今天继续给大家介绍Linux运维相关知识,本文主要内容是Dashboard安装与部署。
一、Dashboard创建
Kubernetes的Dashboard是一个图形化页面,通过该页面,我们也可以管理整个Kubernetes集群,从而可以不用使用命令行的方式来进行配置。
Dashborad的创建资源清单如下所示:
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-certs
namespace: kube-system
type: Opaque
---
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]
verbs: ["get", "update", "delete"]
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
apiVersion: apps/v1beta2
kind: Deployment
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
nodeName: master
containers:
- name: kubernetes-dashboard
image: mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.8.3
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {
}
serviceAccountName: kubernetes-dashboard
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
type: NodePort
ports:
- port: 443
targetPort: 8443
nodePort: 30000
selector:
k8s-app: kubernetes-dashboard
注意,我们在使用该资源清单时,需要将Deployment控制器下的nodeName指定为Kubernetes集群中控制节点的主机名,我这里是master,其他场景下应该根据其配置情况进行不同的修改。
完成后,我们即可执行命令:
kubectl create -f kubernetes-dashboard.yaml
该命令执行后悔按照我们资源清单的配置,分别撞见Secret、ServiceAccount、Role、Rolebinding、Deployment以及Service,该命令执行过程如下所示:

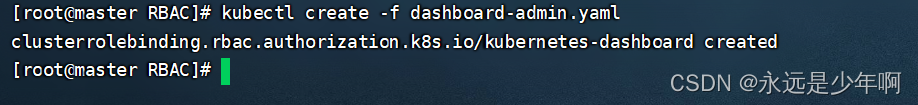
二、ClusterRolebinding创建
之后,我们还需要创建一个ClusterRolebinding,来给我们Dashboard进行授权。该ClusterRolebinding配置命令如下所示:
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: kubernetes-dashboard
labels:
k8s-app: kubernetes-dashboard
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
之后,我们可以执行该命令,执行结果如下所示:
三、效果展示
在上述所有配置结束后,我们就可以来查看我们的配置结果了。首先,我们执行命令:
kubectl get pods --all-namespaces
该命令执行结果如下所示:
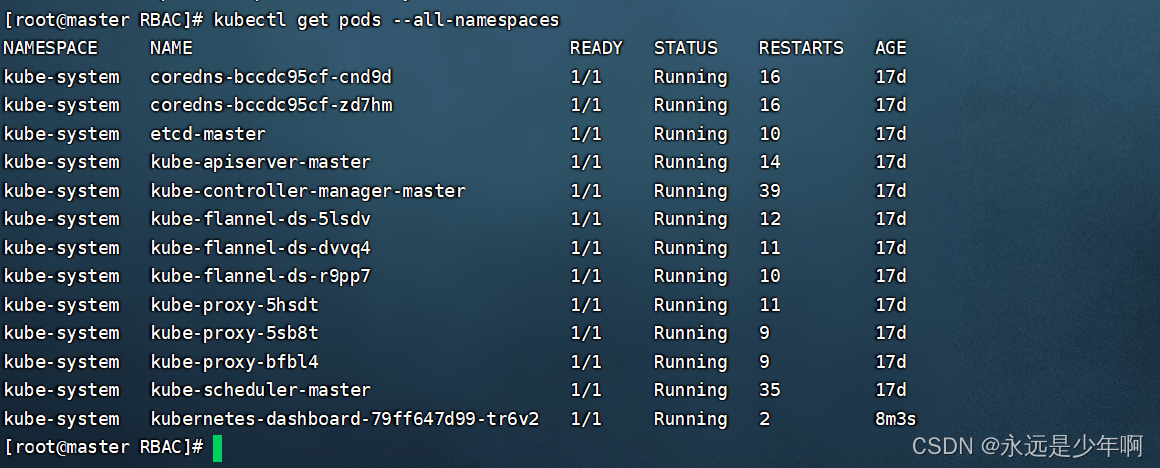
发现我们的dashborad的Pod已经成功运行!
我们查看当前的端口,结果如下所示:
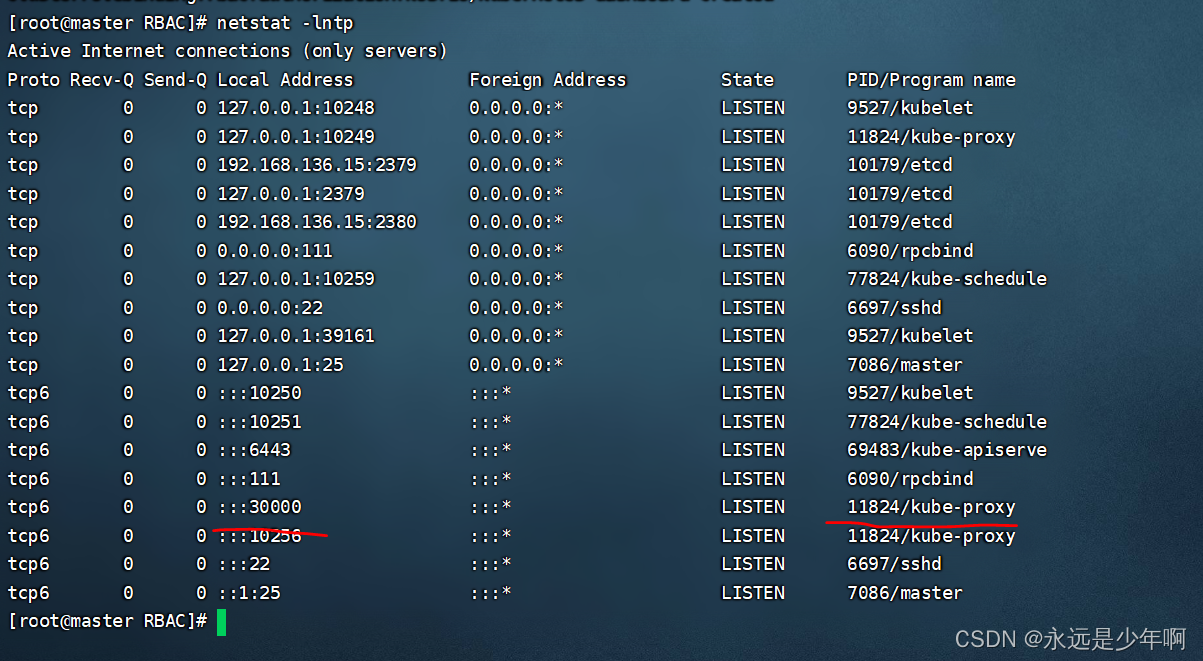
发现我们的系统30000端口已经打开。
之后,我们使用浏览器访问我们Kubernetes集群中的任意一台设备的30000端口,结果如下所示:

从上图中可以看出,我们的Dashboard已经安装并且部署完毕!
注:访问时请采用火狐浏览器,否则其他的浏览器会因为我们访问Dashboard的证书问题而拒绝我们访问。此外,如果您的火狐浏览器级别过高,也可能会出现上述问题。出现上述问题的解决请查看Kubernetes详解(五十九)——Kubernetes Dashboard无法用浏览器访问解决
原创不易,转载请说明出处:https://blog.csdn.net/weixin_40228200