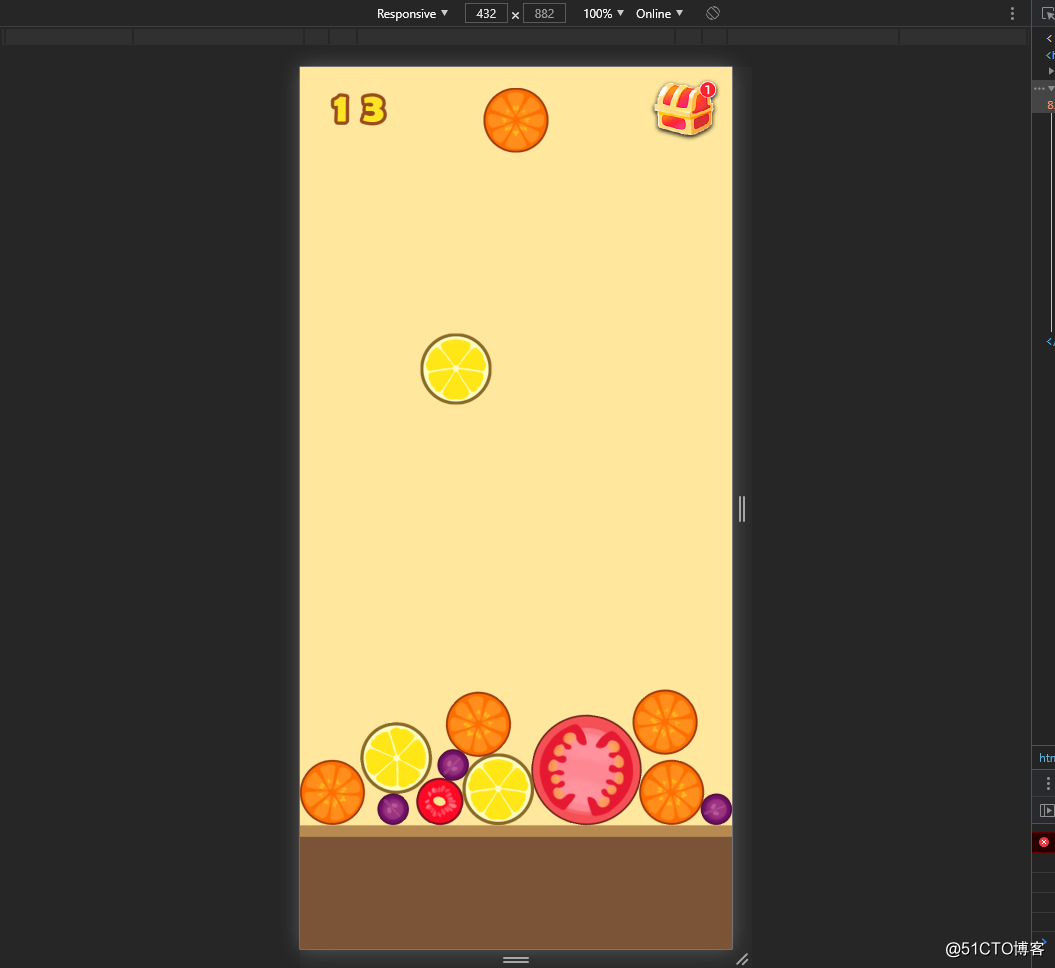
搭建的一个最新比较热门的小游戏合成西瓜
需要安装好k8s集群以及docker,如果还没部署k8s可以看如下文档:我是用的k8s版本为1.16
https://blog.51cto.com/13555423/2503576因为要将制作的镜像上传harbor所以没安装harbor也可以参考:
https://blog.51cto.com/13555423/2621233
将合成西瓜代码下载下来,链接1为github地址,链接2为下载地址:
https://github.com/bullhe4d/bigwatermelon
https://github.com/bullhe4d/bigwatermelon/archive/main.zip
注:1.20版本k8s个别api已经弃用如果你的版本为1.20那将无法部署成功
先yum安装一个nginx,作为反向代理,在不加端口的情况下访问
cat <<EOF > /etc/yum.repos.d/nginx.repo
[nginx-stable]
name=nginx stable repo
baseurl=http://nginx.org/packages/centos/$releasever/$basearch/
gpgcheck=1
enabled=1
gpgkey=https://nginx.org/keys/nginx_signing.key
[nginx-mainline]
name=nginx mainline repo
baseurl=http://nginx.org/packages/mainline/centos/$releasever/$basearch/
gpgcheck=1
enabled=0
gpgkey=https://nginx.org/keys/nginx_signing.key
EOFyum install nginx将下载好的代码放到bigwatermelon目录下解压
mkdir bigwatermelon
cd bigwatermelon
unzip bigwatermelon-main.zip
rm -rf bigwatermelon-main.zip下载好后创建个目录写一个Dockerfile文件,我是用的nginx作为基础镜像
vi Dockerfile
FROM nginx
COPY ./* /usr/share/nginx/html/
WORKDIR /usr/share/nginx/html/
RUN chown -R daemon:daemon /usr/share/nginx/html/ &&\
chmod -R 755 /usr/share/nginx/html/用docker build制作镜像
docker build -t nginx-test:v4 .制作好镜像后上传到harbor上面方便node节点进行pull
镜像做好后用traefik作为负载均衡:
vim nginx-app.yamlapiVersion: apps/v1
kind: Deployment
metadata:
name: test-demo
labels:
app: test-demo
spec:
replicas: 1
selector:
matchLabels:
app: test-demo
template:
metadata:
labels:
app: test-demo
spec:
containers:
- name: test-demo-app
image: nginx-test:v4
imagePullPolicy: Never
ports:
- containerPort: 80
resources:
requests:
cpu: "1000m"
memory: "1Gi"
limits:
cpu: "2000m"
memory: "2Gi"
---
apiVersion: v1
kind: Service
metadata:
name: test-demo-service
spec:
selector:
app: test-demo
# type: NodePort
ports:
- name: web
port: 80
protocol: TCP**kubectl apply -f nginx-app.yaml**启动后查看服务状态
kubectl get pods -o wide创建路由
vim traefik-Route.yamlapiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: ingre***outes.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: Ingre***oute
plural: ingre***outes
singular: ingre***oute
scope: Namespaced
---
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: middlewares.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: Middleware
plural: middlewares
singular: middleware
scope: Namespaced
---
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: ingre***outetcps.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: Ingre***outeTCP
plural: ingre***outetcps
singular: ingre***outetcp
scope: Namespaced
---
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: ingre***outeudps.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: Ingre***outeUDP
plural: ingre***outeudps
singular: ingre***outeudp
scope: Namespaced
---
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: tlsoptions.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: TLSOption
plural: tlsoptions
singular: tlsoption
scope: Namespaced
---
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: tlsstores.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: TLSStore
plural: tlsstores
singular: tlsstore
scope: Namespaced
---
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: traefikservices.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: TraefikService
plural: traefikservices
singular: traefikservice
scope: Namespaced
---
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: serverstransports.traefik.containo.us
spec:
group: traefik.containo.us
version: v1alpha1
names:
kind: ServersTransport
plural: serverstransports
singular: serverstransport
scope: Namespaced
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: traefik-ingress-controller
rules:
- apiGroups:
- ""
resources:
- services
- endpoints
- secrets
verbs:
- get
- list
- watch
- apiGroups:
- extensions
- networking.k8s.io
resources:
- ingresses
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- extensions
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- traefik.containo.us
resources:
- middlewares
- ingre***outes
- traefikservices
- ingre***outetcps
- ingre***outeudps
- tlsoptions
- tlsstores
- serverstransports
verbs:
- get
- list
- watch
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: traefik-ingress-controller
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: traefik-ingress-controller
subjects:
- kind: ServiceAccount
name: traefik-ingress-controller
namespace: defaultkubectl apply -f traefik-Route.yaml创建service
vim traefik-svc.yamlapiVersion: v1
kind: Service
metadata:
name: traefik
spec:
type: NodePort
ports:
- protocol: TCP
name: web
port: 8000
- protocol: TCP
name: admin
port: 8080
- protocol: TCP
name: websecure
port: 4443
selector:
app: traefikkubectl apply -f traefik-svc.yaml创建delployment
vim traefik-delployment.yamlapiVersion: v1
kind: ServiceAccount
metadata:
namespace: default
name: traefik-ingress-controller
---
kind: Deployment
apiVersion: apps/v1
metadata:
namespace: default
name: traefik
labels:
app: traefik
spec:
replicas: 1
selector:
matchLabels:
app: traefik
template:
metadata:
labels:
app: traefik
spec:
serviceAccountName: traefik-ingress-controller
containers:
- name: traefik
image: traefik:v2.4
args:
- --api.insecure
- --accesslog
- --entrypoints.web.Address=:8000
- --entrypoints.websecure.Address=:4443
- --providers.kubernetescrd
- --certificatesresolvers.myresolver.acme.tlschallenge
- [email protected]
- --certificatesresolvers.myresolver.acme.storage=acme.json
# Please note that this is the staging Let's Encrypt server.
# Once you get things working, you should remove that whole line altogether.
- --certificatesresolvers.myresolver.acme.caserver=https://acme-staging-v02.api.letsencrypt.org/directory
ports:
- name: web
containerPort: 8000
- name: websecure
containerPort: 4443
- name: admin
containerPort: 8080kubectl apply -f traefik-delployment.yamltraefik搭建完毕,查看pod是否运行,以及服务
kubectl get pods -o wide
kubectl get svc -o wide看到8080映射的端口也就是traefik的端口,IP加端口即可看到traefik管理界面
将域名和service服务关联
vim traefik-host.yamlapiVersion: traefik.containo.us/v1alpha1
kind: Ingre***oute
metadata:
name: test-demo-service-ingress-route
namespace: default
spec:
entryPoints:
- web
routes:
- match: Host(`test.bigwatermelon.com`)
kind: Rule
services:
- name: test-demo-service
port: 80kubectl apply -f traefik-host.yaml使用nginx代理ingress-controller的8000端口,127.0.0.1:后面的端口是8000通过nodeport映射到本地的端口
vi /etc/nginx/conf.d/test-bitwater.confserver {
listen 80;
server_name test.bigwatermelon.com;
location / {
proxy_pass http://127.0.0.1:31472;
proxy_set_header Host $host;
}
}systemctl start nginx
nginx -s reload在 /etc/hosts中添加
192.168.254.1 test.bigwatermelon.com因为是内网地址所以想要访问还需要在hosts中添加
C:\Windows\System32\drivers\etc\hosts
192.168.254.1 test.bigwatermelon.com
最后访问域名展示如下: