[Computer network] computer network summing up
Article Directory
A computer network architecture
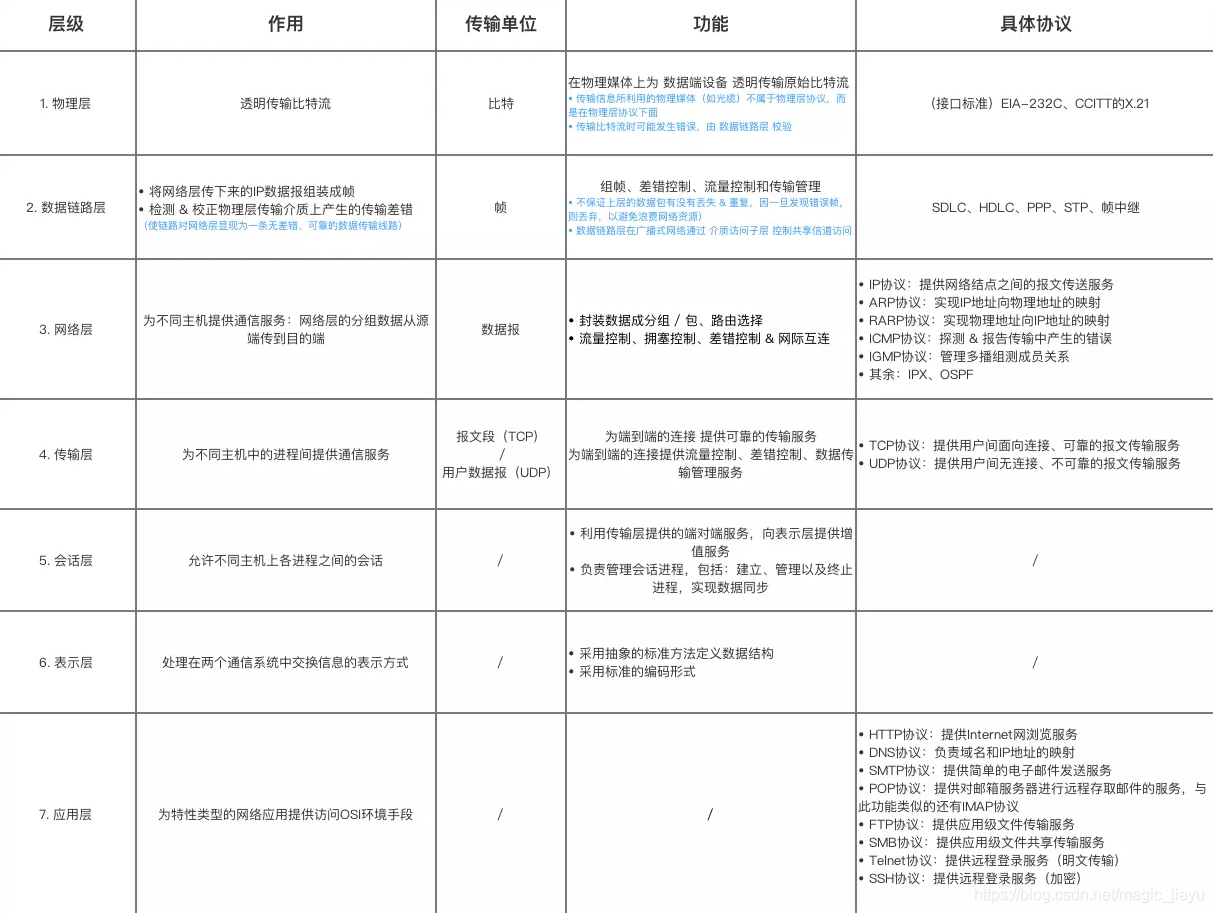
-
Definition: The layers of computer network protocols which set +
-
Action: definition of the computer network functions can be completed
-
Structure Description: Computer network architecture divided into three kinds:
OSIarchitecture,TCP/IParchitecture, five-layer architecture.
OSIArchitecture: Concepts & clear idea of integrity, but not practical complex &TCP / IPArchitecture: with a range of network protocols constitute the foundation of the Internet, isInternetthe core & protocol is widely used in LAN and WAN- Five-layer architecture: the integration of
OSItheTCP / IParchitecture, the purpose is to learn the principles of computer & explain
Lower three layers of subnetworks, for data transmission; high three subnets resource, the computer system corresponds to, for data processing; nexus transport layer.
1. TCP / IP architecture
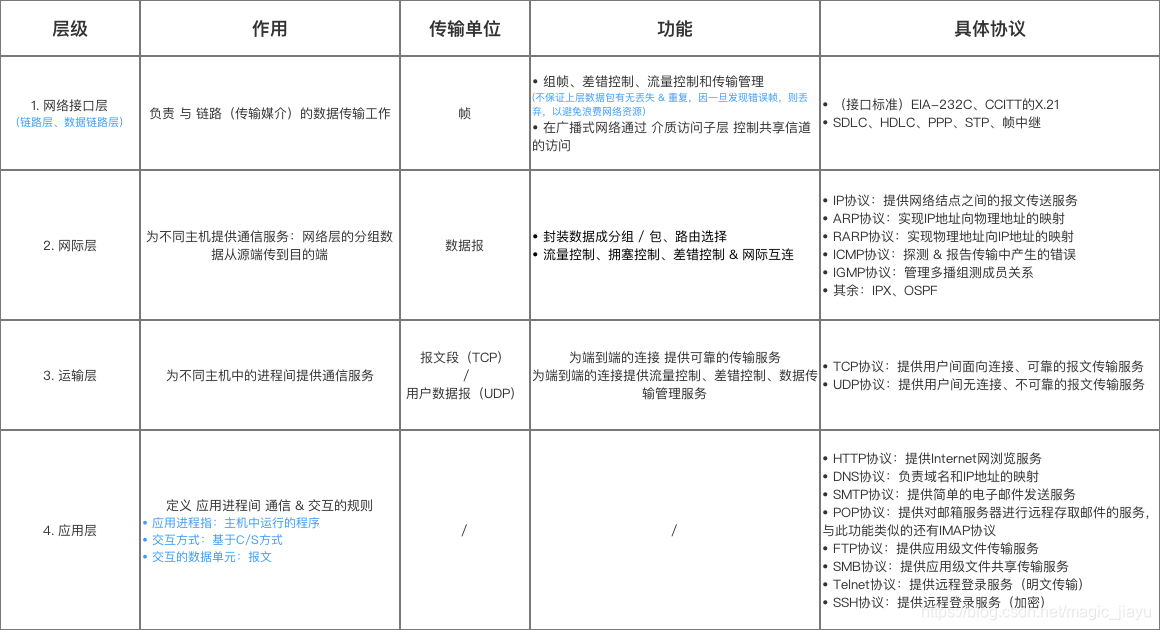
2. OSI architecture
Two, TCP protocol
[Computer network] TCP protocol
Three, UDP protocol
User Datagram Protocol, I.e., User Datagram Protocol, belong to the transport layer protocol
application scenarios: a high speed communication requirements
basedUDPapplication layer protocols areTFTP,SNMP,DNSandNFS
- Domain Name Translation:
DNSProtocol- File Transfer:
TFTPProtocol- Network Management:
SNMPProtocol- Remote file server:
NFSProtocol
1. Features

Advantages and disadvantages: fast but the message is easy to lose (especially if the network is poor)
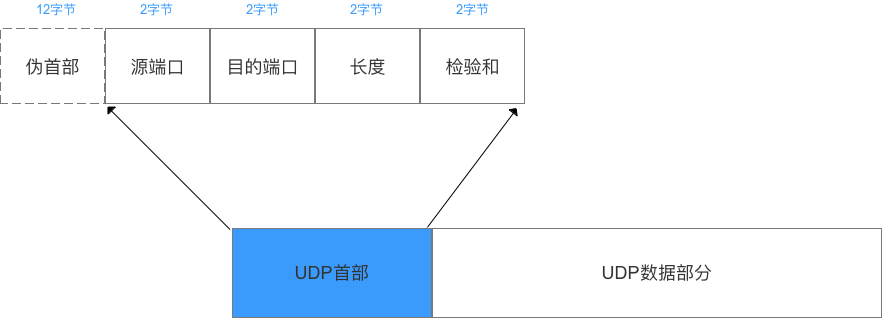
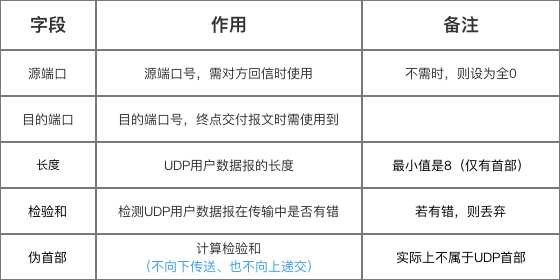
2. segment format
UDP segment shared two fields: a data field & header field is the first key (8 bytes, 4 field).
Four, HTTP protocol
[Computer Network] the HTTP protocol
Five, Socket
- Socket, the application layer and
TCP/IPthe intermediate communication protocol suite software abstraction layer encapsulates the performance of aTCP / IPprotocol family programming interface (API)
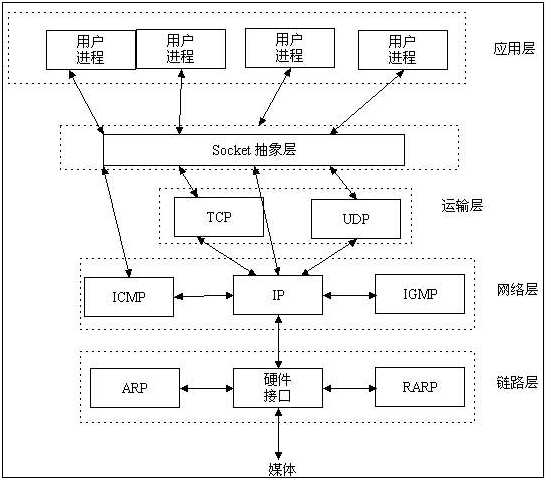
SocketNot a protocol, but a programming call interface (API), belonging to the transport layer (mainly to solve how the data transmission in the network)- Namely: through
Socket, we can through theTCP/IPdevelopment of network communication protocols- For users, simply call
Socketto organize data in order to comply with the specified protocol, to communicate
-
In pairs, a pair of sockets:
Socket ={(IP地址1:PORT端口号),(IP地址2:PORT端口号)} -
A
Socketcommunication link of an application on a host only representative examples
Six additional knowledge
1. Enter the url address in the browser -> Show home page of the process
Open a Web page, the whole process will be which ones to use
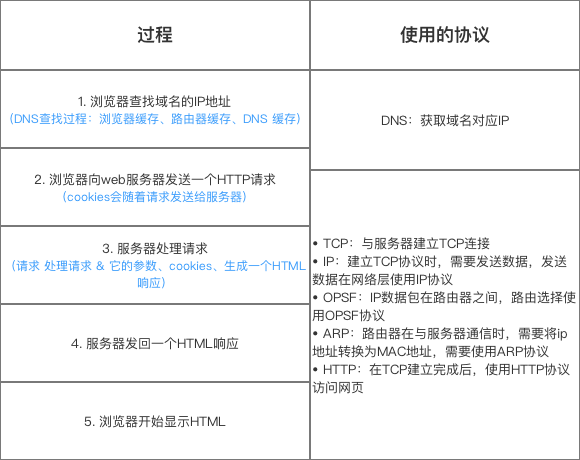
2. IPv4 address
- Definition: Internet connection in each host (or router) a globally unique identifier.
- Composition: IP address of the network number = 32 = + host number; :: = {i.e., IP address <network number> <host number>}
Network Number: flag network host (or router) are connected. A network number must be unique within the scope of the entire Internet.
Host number: Flag of the host (or router). A host number in front of it network-wide network number specified must be unique.
Different types of IP addresses, which is different from the number of bytes occupied by the network number & host number; therefore: An IP address is unique in the entire network
- Classification: The traditional classification of IP address is an address, is divided into A, B, C, D, E five. Difference is the number of bytes of the network number of the account number & host.
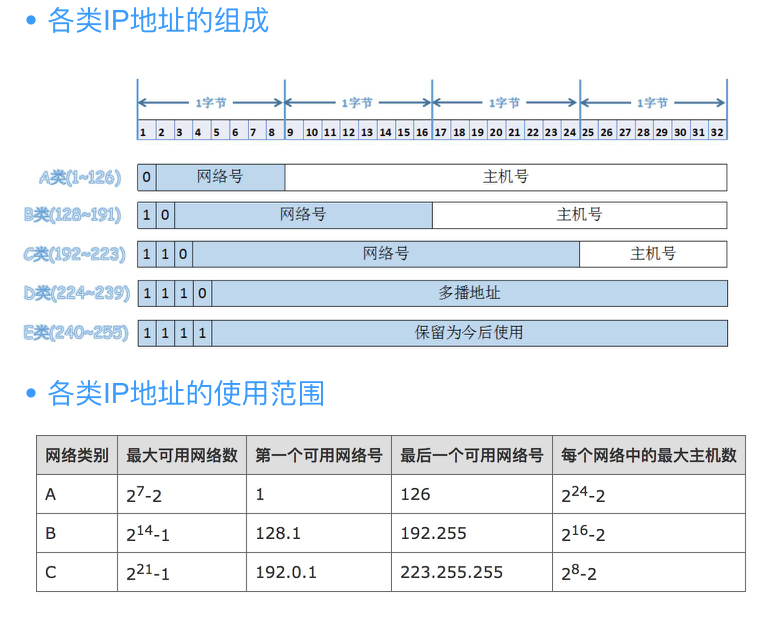
- Note: The IP address of all kinds, some IP addresses are used for special purposes, it can not be used as the host IP address

3. ICMP protocol
Belong to the IP layer protocol
Note: ICMP packet is not a high-level agreement, but as the data layer IP datagram, plus datagram header, consisting of an IP datagram sent out
- Definition:
Internet Control Message Protocolthat the Internet Control Message Protocol - Role: to more effectively forward IP packet delivery & improve the chances of success. While allowing the host / router & report error exceptions
- Category:
ICMPerror report message &ICMPinquiry message - Main applications:
PING(Internetwork Packet detection),Traceroute(track packets from a source to a destination path principle a series = IP datagrams sent from the source host to the destination host)
4. Ping process
ICMP packet is an important application: using the echo request IPCM & echo-reply message
is an example of the direct use of ICMP network layer application layer, a transport layer of non-TCP, UDP
- Definition:
Packet InterNet Groper, i.e., the probe packet network. - Action: Test connectivity two hosts.
- principle:
- A plurality of transmission to the destination host ICMP echo request packets
- The reply from the host ICMP echo reply message timestamp to calculate the round trip time
- Which results are shown: the IP address is sent to the destination host, the number of transmit & receive & missing packet, the minimum round trip time, the maximum average &
- Process :( destination host) PC1: IP = 192.168.1.1; (source host) PC2: IP = 192.168.1.2

- Source host Step 3: transmitting a broadcast ARP packet to obtain the MAC address of the process
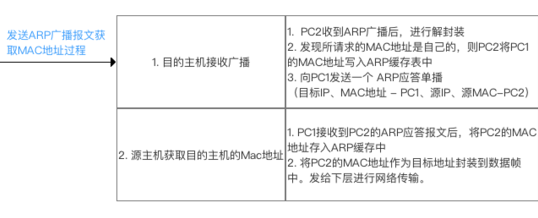
- Source host Step 3: transmitting a broadcast ARP packet to obtain the MAC address of the process
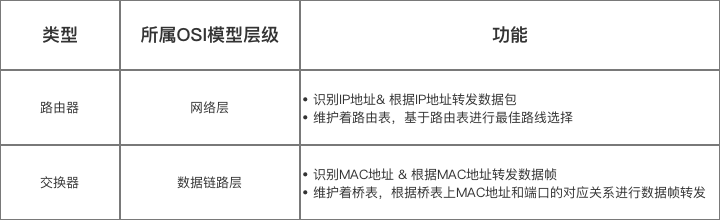
The difference between routers and switches
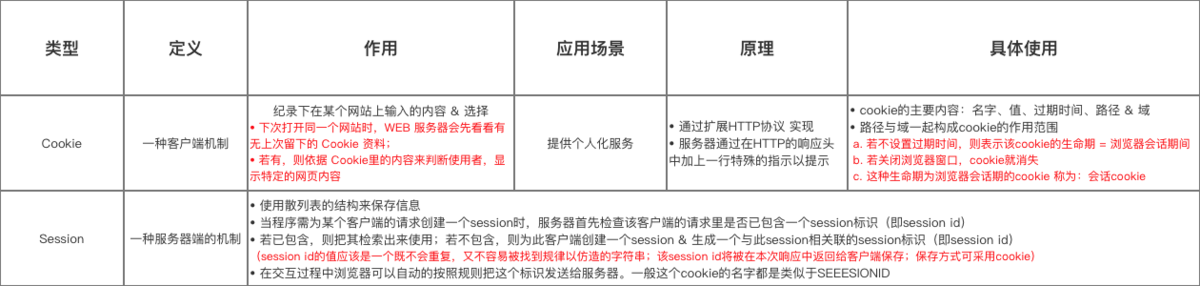
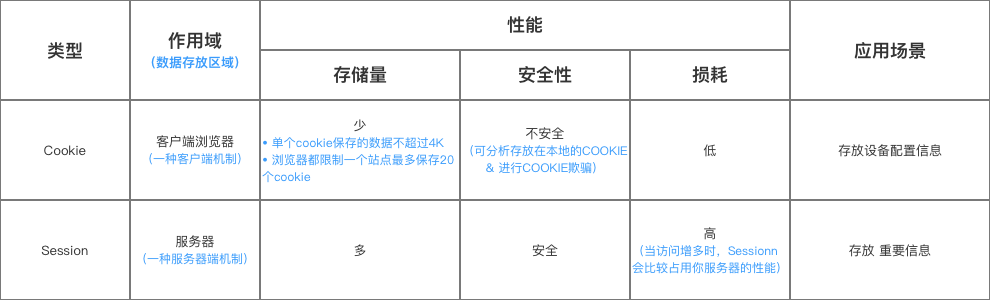
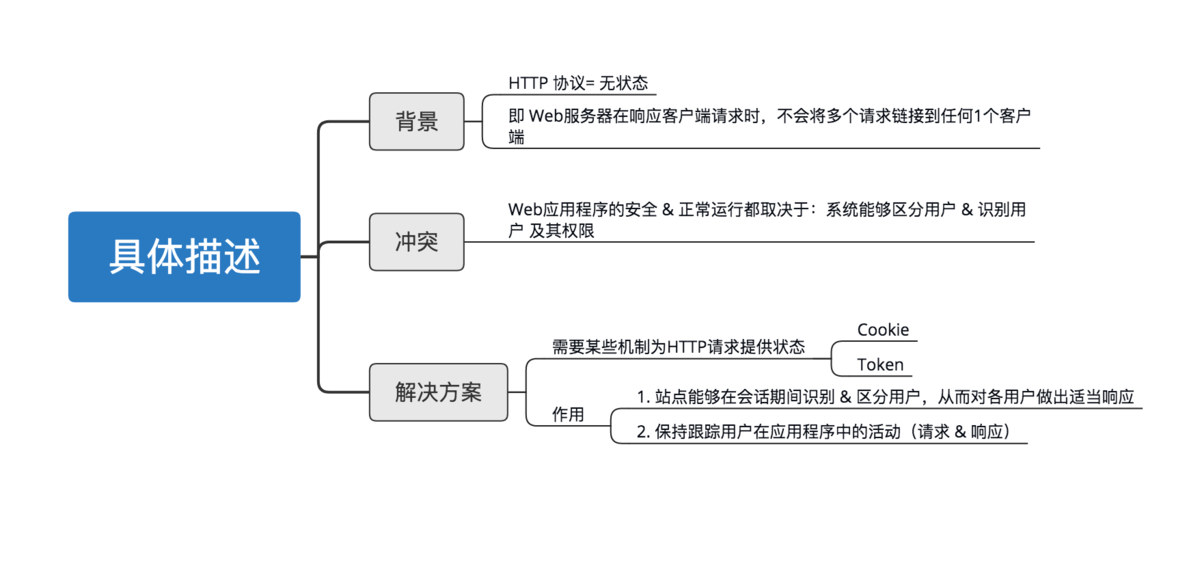
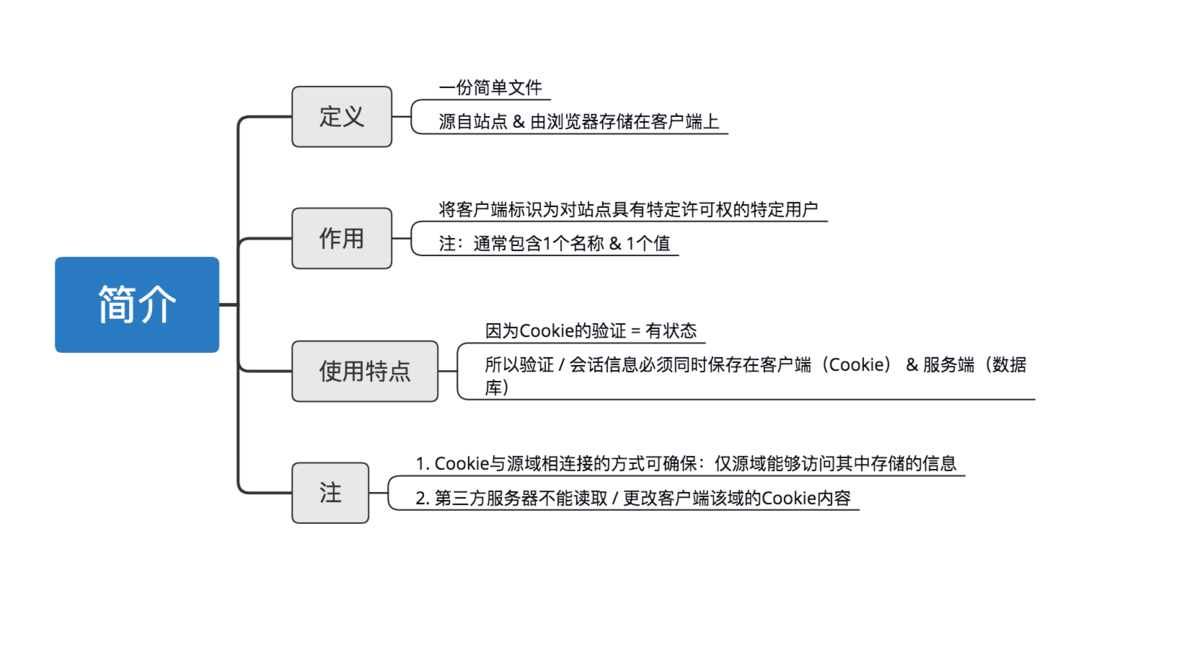
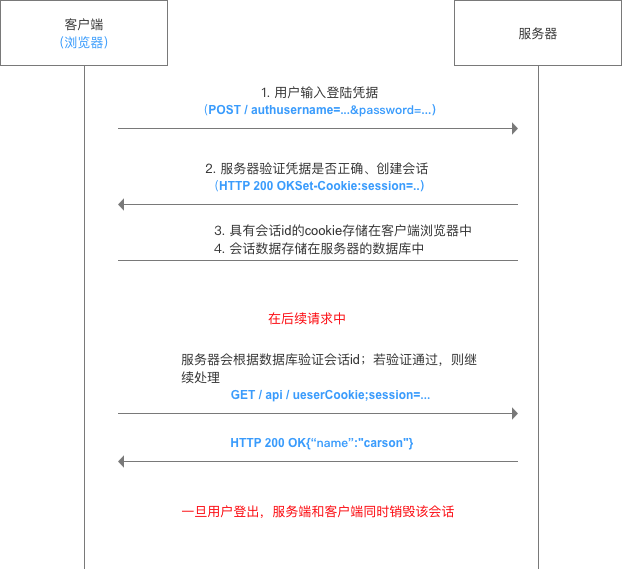
6. Cookie与Session
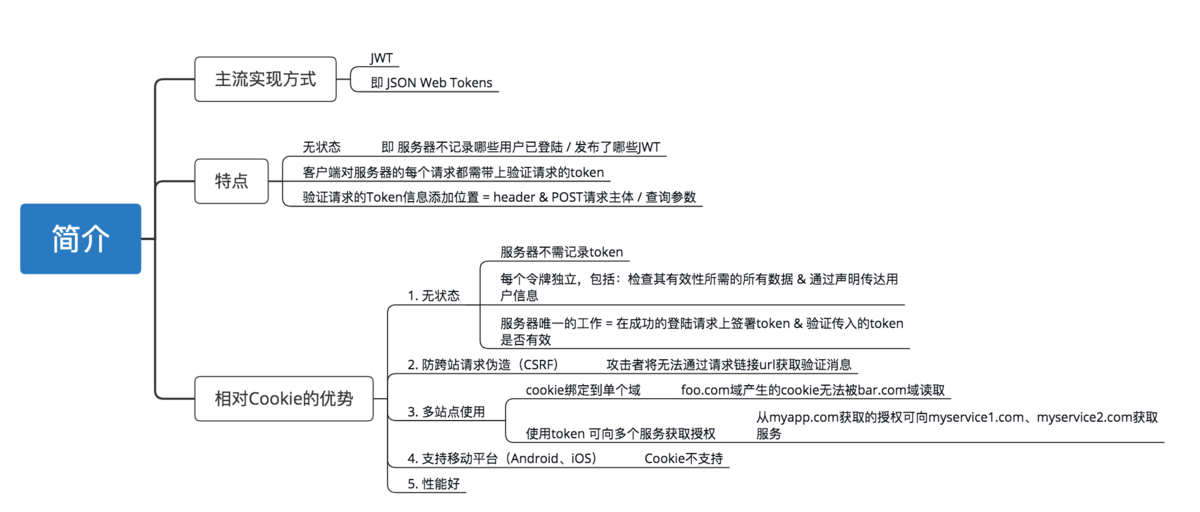
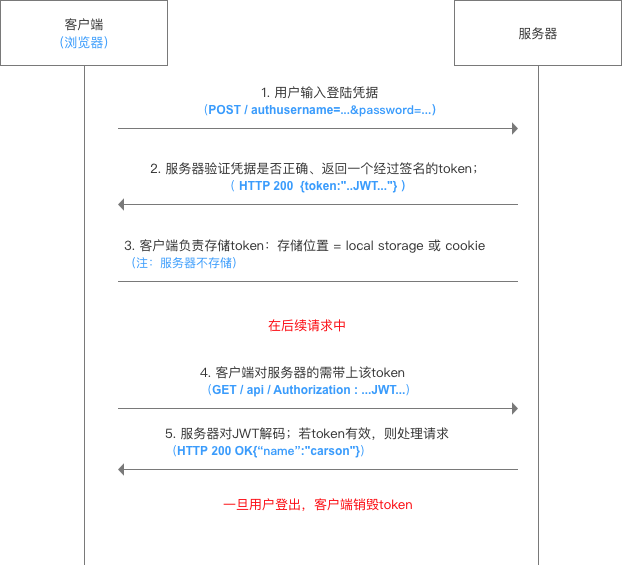
7. Cookie given Token
-
Brief introduction
-
Based
Cookieauthentication & verification process
-
Based
Tokenauthentication & verification process
Reference Links: This is a detailed definition of computer network infrastructure & Study Guide