1. Misunderstandings and pitfalls of self-study network security learning
1. Don’t try to become a programmer [programming-based learning] before you start learning
In my previous answers, I have repeatedly emphasized not to start learning network security based on programming. Generally speaking, learning programming is not only a long learning cycle, but also there are not many key knowledge available after the actual transition to security
If ordinary people want to learn programming well and start learning network security, it often takes a long time, and it is easy to give up halfway. And learning programming is just a tool, not an end. Our goal is not to become a programmer. It is suggested that in the process of learning network security, what will not be filled, which is more purposeful and less time-consuming
2. Don’t take deep learning as the first lesson
Many people are aiming to learn network security well and solidly, so it is easy to use too much force and fall into a misunderstanding: it is to learn all the content in depth, but it is not right to use deep learning as the first lesson of network security. good idea. The reasons are as follows:
[1] The black-box nature of deep learning is more obvious, and it is easy to learn and swallow
【2】Deep learning has high requirements on itself, it is not suitable for self-study, and it is easy to enter a dead end
3. Don’t Collect Too Much Data
There are a lot of learning materials about network security on the Internet, and there are several gigabytes of materials that can be downloaded or watched at every turn. And many friends have "collection addiction", buying more than a dozen books at once, or collecting dozens of videos
Many online learning materials are extremely repetitive and most of the content has not been updated a few years ago. During the introductory period, it is recommended to choose "small but refined" materials. Below I will recommend some learning resources that I think are good for Xiaobai. Read on patiently.
2. Some preliminary preparations for learning network security
1. Hardware selection
I am often asked "Do I need a computer with a high configuration to learn network security?" The answer is no, the computer used by hackers does not need any high configuration, as long as it is stable. Because some programs used by hackers, low-end CPUs are also It can run very well, and it doesn’t take up much memory. There is another one, the hacker is done under the DOS command, so the computer can be used in the best condition! So, don’t re-purchase the machine in the name of learning...
2. Software selection
Many people will be entangled in learning hackers whether to use Linux, Windows or Mac system. Although Linux looks cool, it is not friendly to newbies. The Windows system can also use the virtual machine to install the target machine for learning
As for the programming language, Python is the most recommended because of its good expansion support. Of course, many websites on the market are developed by PHP, so it is also possible to choose PHP. Other languages include C++, Java...
Many friends will ask if they want to learn all languages? the answer is negative! To quote my sentence above: Learning programming is just a tool, not an end, our goal is not to become a programmer
(An extra thing to mention here is that although learning programming cannot get you started, it can determine how far you can go on the road of network security, so I recommend you to learn some basic programming knowledge by yourself)
3. Language ability
We know that computers were first invented in the West, and many nouns or codes are in English. Even some existing tutorials were originally translated from English, and it usually takes a week for a bug to be translated into Chinese. Vulnerabilities may have been patched at this time difference. And if you don’t understand some professional terms, you will have obstacles when communicating technology or experience with other hackers, so you need a certain amount of English and hacker professional terms (you don’t need to be particularly proficient, but you must be able to understand the basics)
For example: broiler, hanging horse, shell, WebShell, etc.
3. Network security learning route

The first stage: getting started with basic operations and learning basic knowledge
The first step to getting started is to learn some current mainstream security tool courses and supporting books on basic principles. Generally speaking, this process takes about 1 month.
At this stage, you already have a basic understanding of cybersecurity. If you have finished the first step, I believe you have theoretically understood the above is sql injection, what is xss attack, and you have also mastered the basic operations of security tools such as burp, msf, and cs. The most important thing at this time is to start laying the foundation!
The so-called "foundation" is actually a systematic study of basic computer knowledge. If you want to learn network security well, you must first have 5 basic knowledge modules:
1. Operating system
2. Protocol/Network
3. Database
4. Development language
5. Principles of Common Vulnerabilities
What is the use of learning these basics?
The level of knowledge in various fields of computer determines the upper limit of your penetration level.
[1] For example: if you have a high level of programming, you will be better than others in code auditing, and the exploit tools you write will be easier to use than others;
[2] For example: if you have a high level of database knowledge, then when you are conducting SQL injection attacks, you can write more and better SQL injection statements, which can bypass WAF that others cannot bypass;
【3】For example: if your network level is high, then you can understand the network structure of the target more easily than others when you infiltrate the internal network. You can get a network topology to know where you are, and get the configuration of a router. file, you will know what routes they have made;
【4】For another example, if your operating system is good, your privilege will be enhanced, your information collection efficiency will be higher, and you can efficiently filter out the information you want.
The second stage: practical operation
1. Mining SRC
The purpose of digging SRC is mainly to put the skills into practice. The biggest illusion of learning network security is to feel that you know everything, but when it comes to digging holes, you can’t do anything. SRC is a very good opportunity to apply skills.
2. Learn from technical sharing posts (vulnerability mining type)
Watch and study all the 0day mining posts in the past ten years, and then build an environment to reproduce the loopholes, think and learn the author's digging thinking, and cultivate your own penetrating thinking
3. Range practice
Build a shooting range by yourself or go to a free shooting range website to practice. If you have the conditions, you can buy it or apply to a reliable training institution. Generally, there are supporting shooting range exercises.
Phase 3: Participate in CTF competitions or HVV operations
Recommended: CTF Competition
CTF has three points:
【1】A chance close to actual combat. Now the network security law is very strict, unlike before, everyone can mess around
[2] Topics keep up with the frontiers of technology, but many books lag behind
【3】If you are a college student, it will be very helpful for finding a job in the future
If you want to play a CTF competition, go directly to the competition questions, if you don’t understand the competition questions, go to the information according to what you don’t understand
Recommended: HVV (network protection)
HVV has four points:
[1] It can also greatly exercise you and improve your own skills. It is best to participate in the HVV action held every year
【2】Be able to meet many bigwigs in the circle and expand your network
【3】The salary of HVV is also very high, so you can earn a lot of money if you participate
[4] Like the CTF competition, if you are a college student, it will also be very helpful for finding a job in the future
Fourth, the recommendation of learning materials
Book list recommendation:
Computer operating system:
[1] Coding: the language hidden behind computer software and hardware
【2】In-depth understanding of the operating system
【3】In-depth understanding of windows operating system
【4】Linux kernel and implementation
Programming development class:
【1】windows programming
【2】windwos core becomes
【3】Linux programming
【4】Unix environment advanced into
【5】IOS becomes
[6] The first line of code Android
【7】C programming language design
【8】C primer plus
[9] C and pointers
[10] C expert programming
[11] C traps and defects
[12] Assembly language (Wang Shuang)
【13】java core technology
【14】java programming ideas
【15】Python core programming
[16] Linux shell script strategy
[17] Introduction to Algorithms
[18] Compilation principle
[19] Compilation and decompilation technology practice
[20] The way to clean code
[21] Code Encyclopedia
[22] TCP/IP Detailed Explanation
【23】Rootkit: Lurkers in the gray area of the system
【24】Hacking Attack and Defense Technology Collection
【25】Encryption and decryption
【26】C++ Disassembly and Reverse Analysis Technique Revealed
[27] web security testing
【28】White hat talks about web security
【29】Proficient in script hacking
【30】Web front-end hacking technology secret
[31] Programmer's application
【32】English Writing Handbook: Elements of Style
Common Internet Security and Forums
Kanxue Forum
Safety Class
Safety Niu
Safety Internal Reference
Green League
Prophet Community
XCTF Alliance
I have also compiled some network security information for you below. If you don’t want to find them one by one, you can refer to these information.
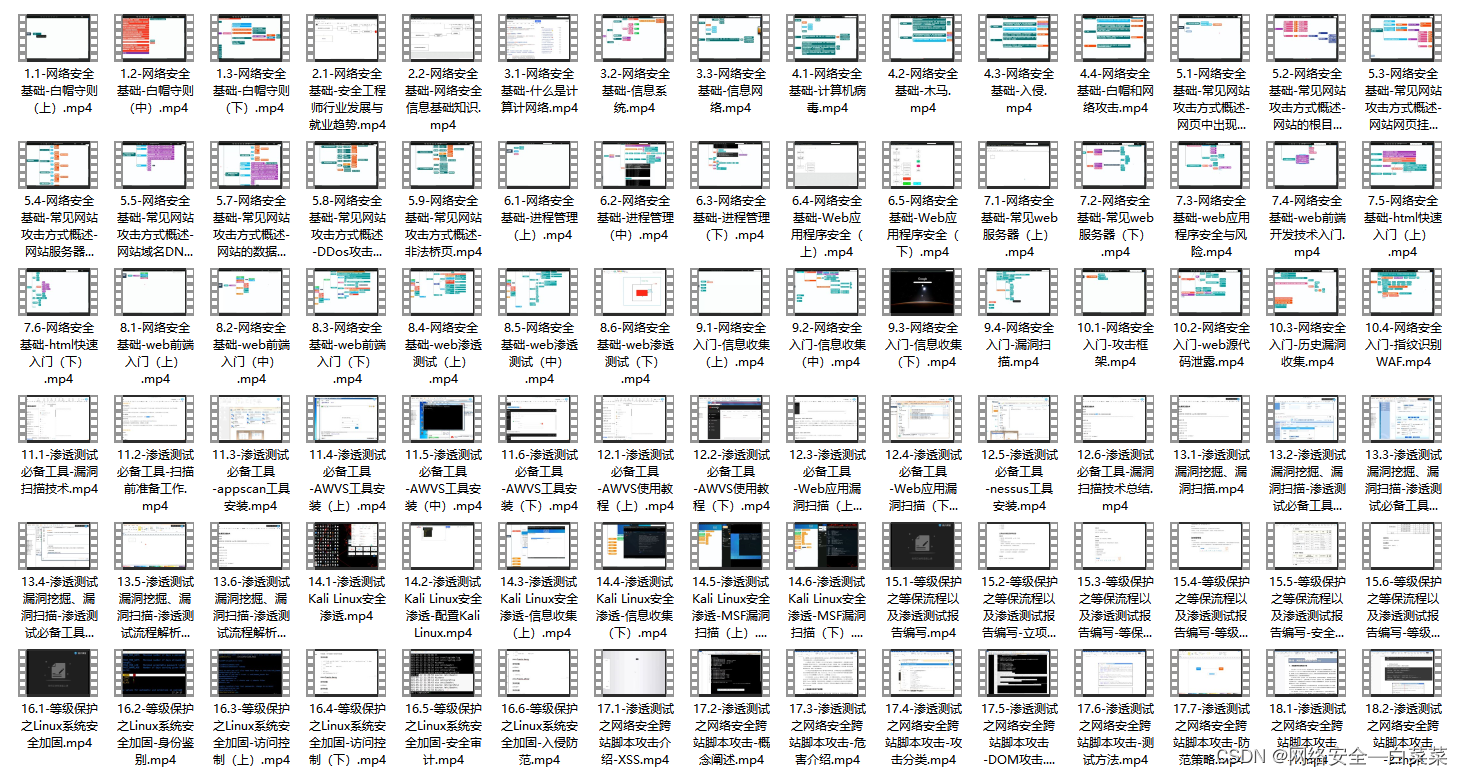
video tutorial
SRC&Hacking Technical Documentation

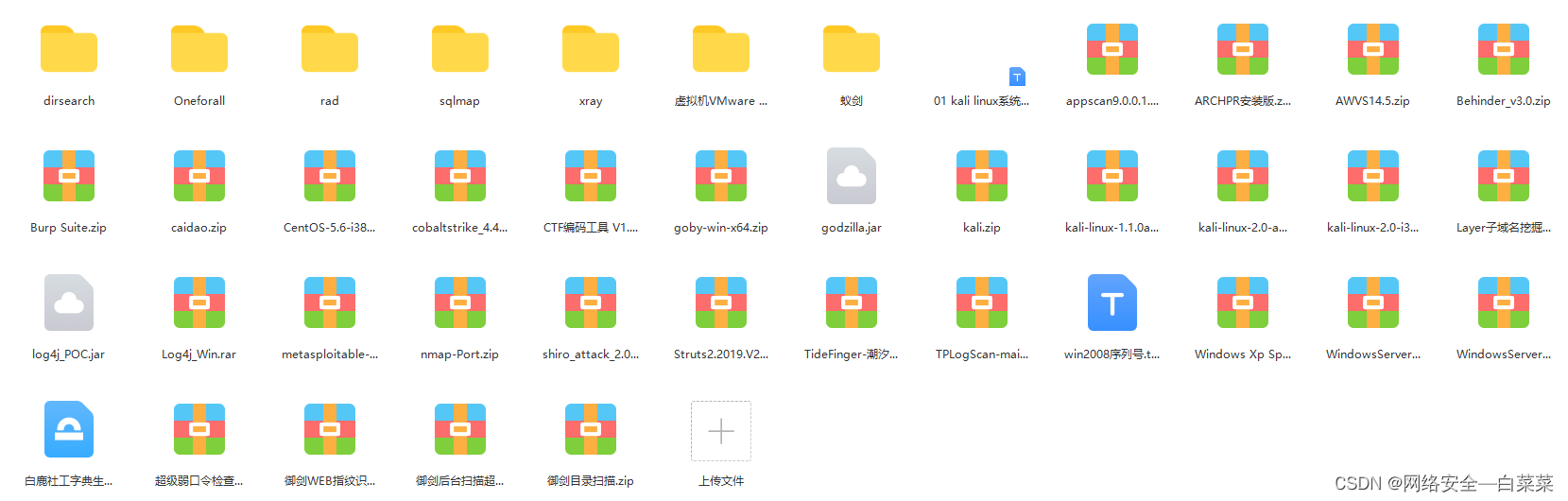
Hacking Tools Collection
The comment area where you need information is waiting for you