Many students learned redhat 7, when using centos will always encounter some problems, because when you install centos enabled by default for some services, we have to change the SSH port under centos 7.0 today.
Steps:
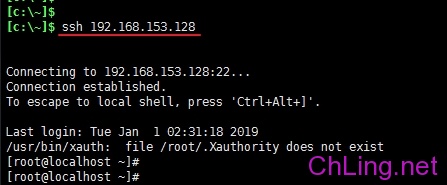
Centos 7.0 log on remotely to the terminal;
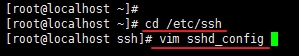
Modify / etc / ssh folder sshd_config file

#Port 22 find this line in the file
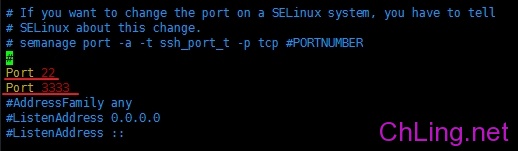
Delete #Port 22 # in front of the number, use the default port 22
to add a line Port 3333, serving to increase the SSH port 3333
(for more ports, line by line in this format can be added, if only to modify the default port 22 3333 port, port 22 would delete this line, you can add port 3333)
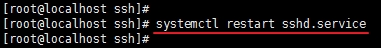
After saving the file, use
systemctl restart sshd.service
Restart sshd service
(Redhat 7.0 then you can call it a day)

Found using port 3333, not connected to the terminal device, and some versions of CentOS (such centos7.4) when there is such a service restart sshd error message
Job for sshd.service failed because the control process exited with error code.
See “systemctl status sshd.service” and “journalctl -xe” for details.
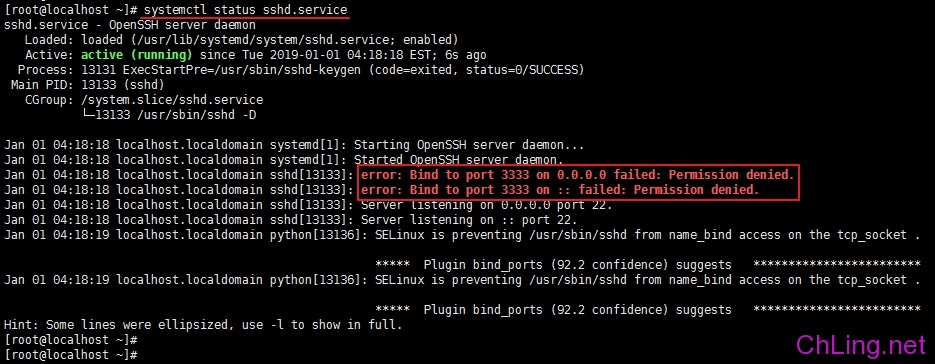
use
systemctl status sshd.service
Sshd command to view the state found that 3333 port bind failure, not in force, suggesting View SELinux Service
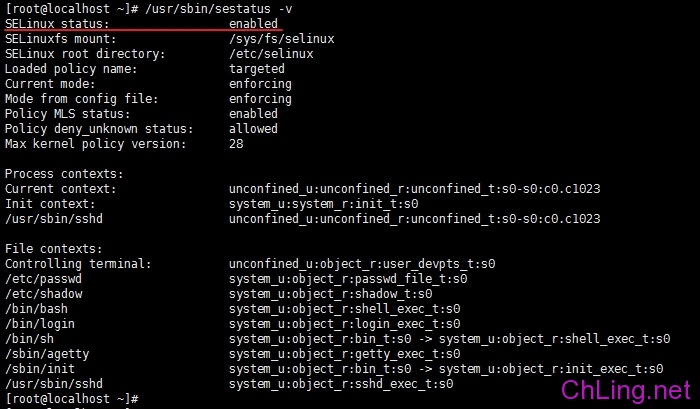
use
/ Usr / sbin / sestatus -v
Command to check the status of SELinux service, found status is turned on
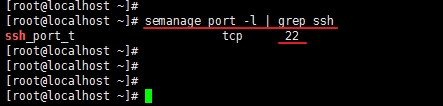
Then we use
semanage port -l | grep ssh
Ssh command to view the current port services, found that only 22 ports and 3333 ports did not we just added
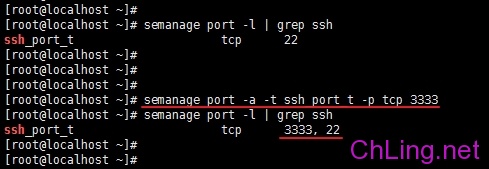
Then we need to use
semanage port -a -t ssh_port_t -p tcp 3333
SELinux in order to add to the ssh port
to use again
semanage port -l | grep ssh
Ssh command to view the current port services, the port has been added successfully found 3333
This time we use
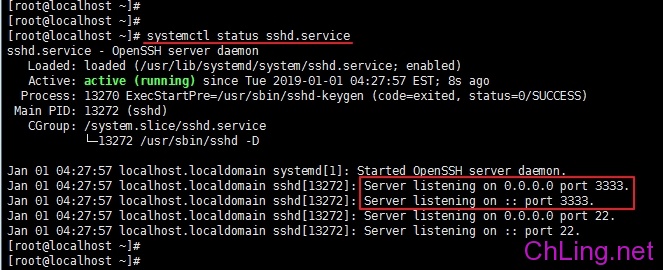
systemctl status sshd.service
Command, this time found that 3333 port is listening state.
By this time our work is not over, some of the students could not help but have to use a remote SSH, found or not connected, because it is enabled by default firwall 3333 blocking the connection port.

use
firewall-cmd –list-all
Command to see, not just in the ports row we add 3333,
this time we need to use
firewall-cmd –zone=public –add-port=3333/tcp –permanent
Command, add the port number to the firewall exception rule
(-permanent permanent, this argument does not fail after the restart)
have added rules to be in effect for the firewall to restart loading it rules,
firewall-cmd –reload
Used again
firewall-cmd –list-all
Command found in the ports has more than one port connection is an exception 3333tcp
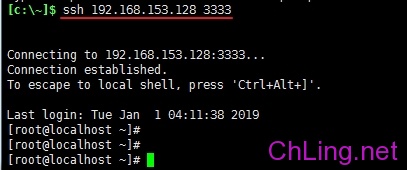
This time to use port 3333 for remote connections, you can successfully landing system.
By this time, the entire process is completed!
Kick call it a day!
Remarks:
/ usr / sbin / sestatus -v // view the SELinux state semanage port -l | grep ssh // query the current service ssh port semanage port -a -t ssh_port_t -p tcp 3333 // add ssh port to SELinux in systemctl restart sshd. service // restart the ssh service firewall-cmd -list-all // Check the list of firewall firewall-cmd -zone = public -list- ports // view all open ports firewall-cmd -zone = public -add- port = 3333 / tcp -permanent // Add the port number (-permanent permanent, this argument does not fail after the restart) firewall-cmd -reload // reload firewall firewall-cmd -zone = public -query- port = 3333 / tcp // View whether the port within the rules firewall-cmd -zone = public -remove- port = 3333 / tcp -permanent // delete the port number