4.4.4 phone system n4
Zygote originally app_system program but there is also a part of java, with the last successful commissioning him as useless, this time with gdb debugger.
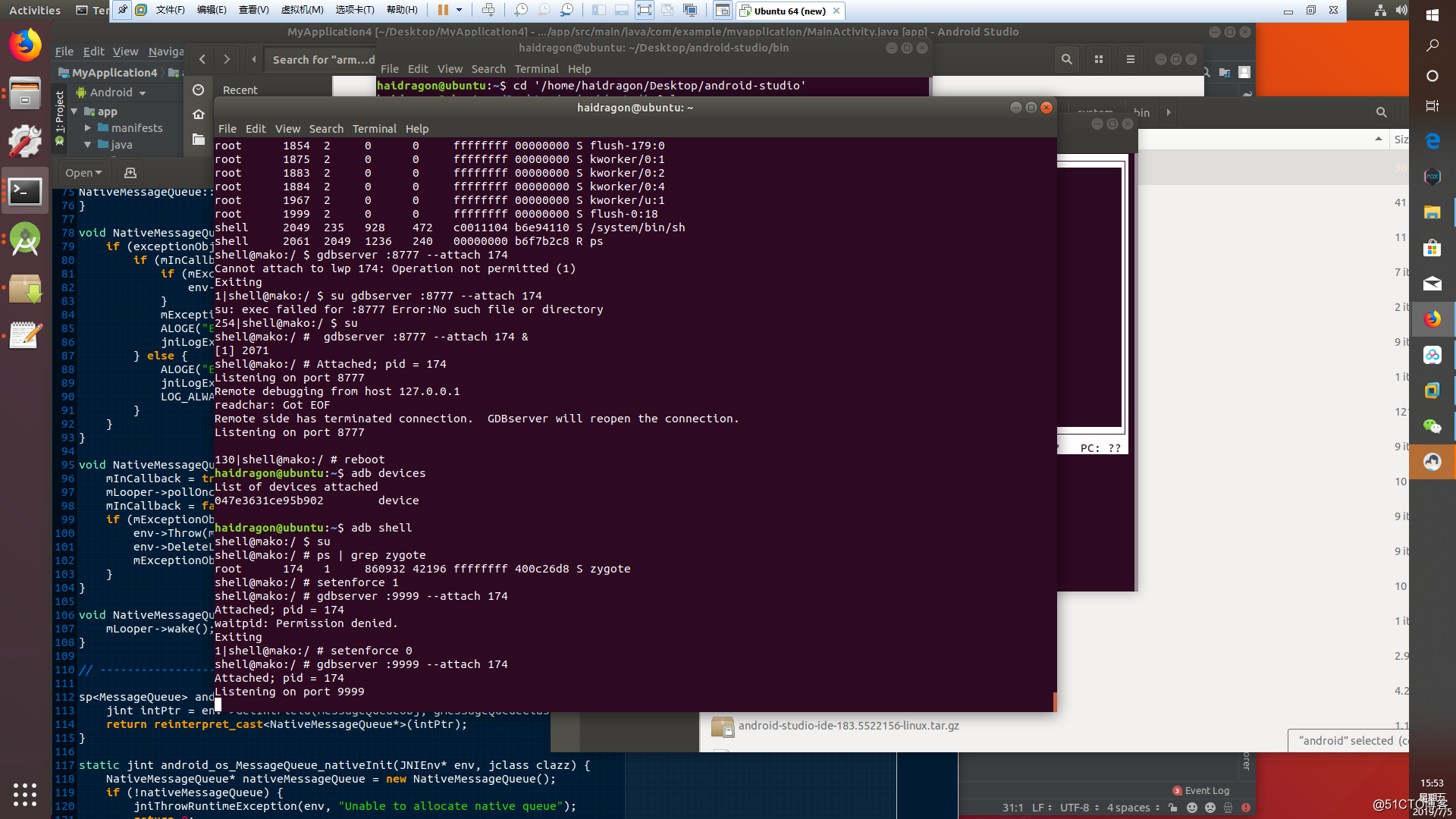
Into the phone directly with adbserver attached. The phone is turned on by default seliunx need to enter setenforce 0
130|shell@mako:/ # reboot
haidragon@ubuntu:~$ adb devices
List of devices attached
047e3631ce95b902 device
haidragon@ubuntu:~$ adb shell
shell@mako:/ $ su
shell@mako:/ # ps | grep zygote
root 174 1 860932 42196 ffffffff 400c26d8 S zygote
shell@mako:/ # setenforce 1
shell@mako:/ # gdbserver :9999 --attach 174
Attached; pid = 174
waitpid: Permission denied.
Exiting
1|shell@mako:/ # setenforce 0
shell@mako:/ # gdbserver :9999 --attach 174
Attached; pid = 174
First port forwarding adb forward tcp: 9999 tcp: 9999
found arm-linux version of gdb on linux must be used to arm-linux is arm-linux-androideabi-gdb (the Internet are looking at me here on the inside ndk it no other all have, and I have both a version that only 4.7 can do) 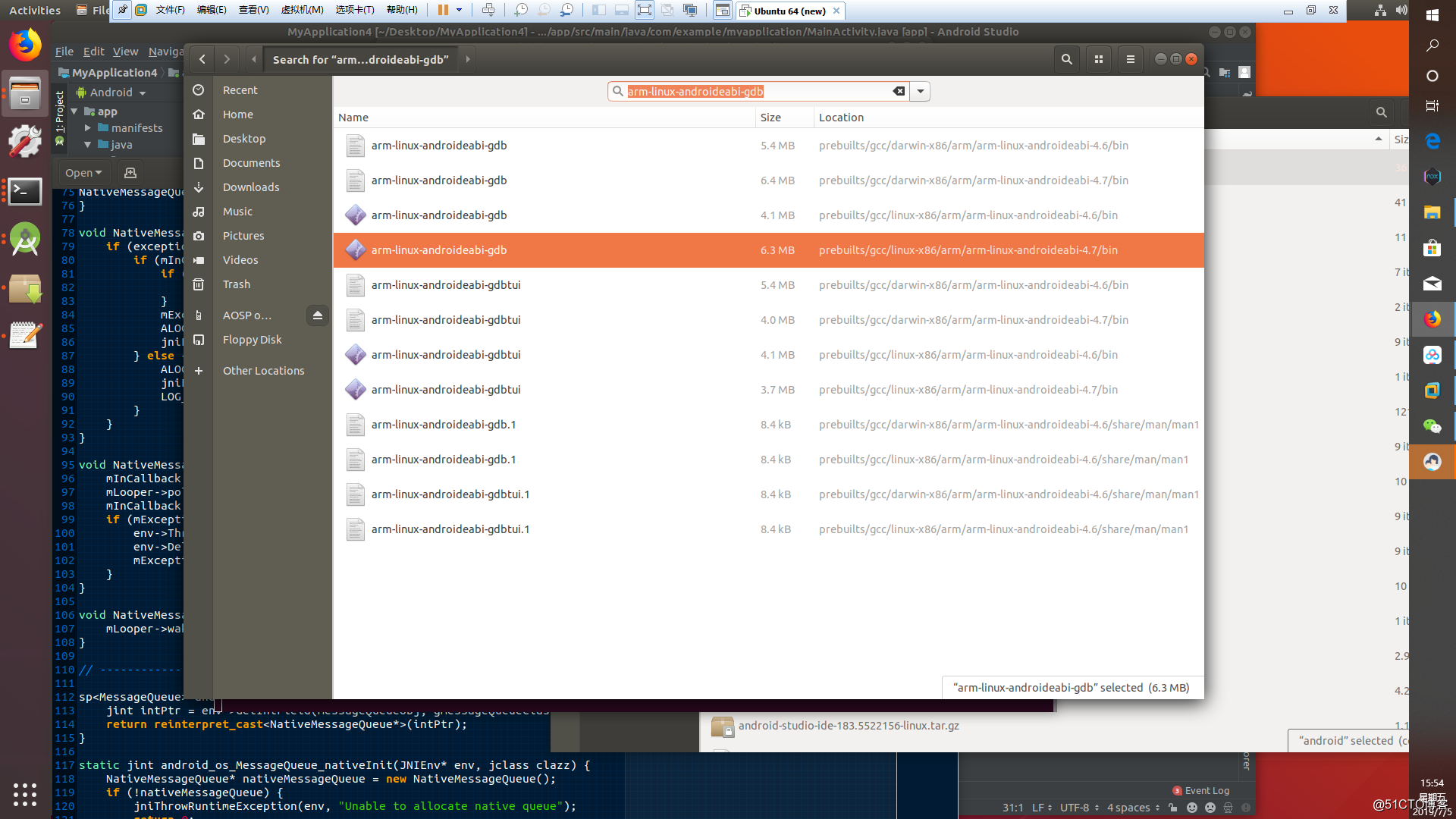
run
'/home/haidragon/Desktop/android/prebuilts/gcc/linux-x86/arm/arm-linux-androideabi-4.7/bin/arm-linux-androideabi-gdb'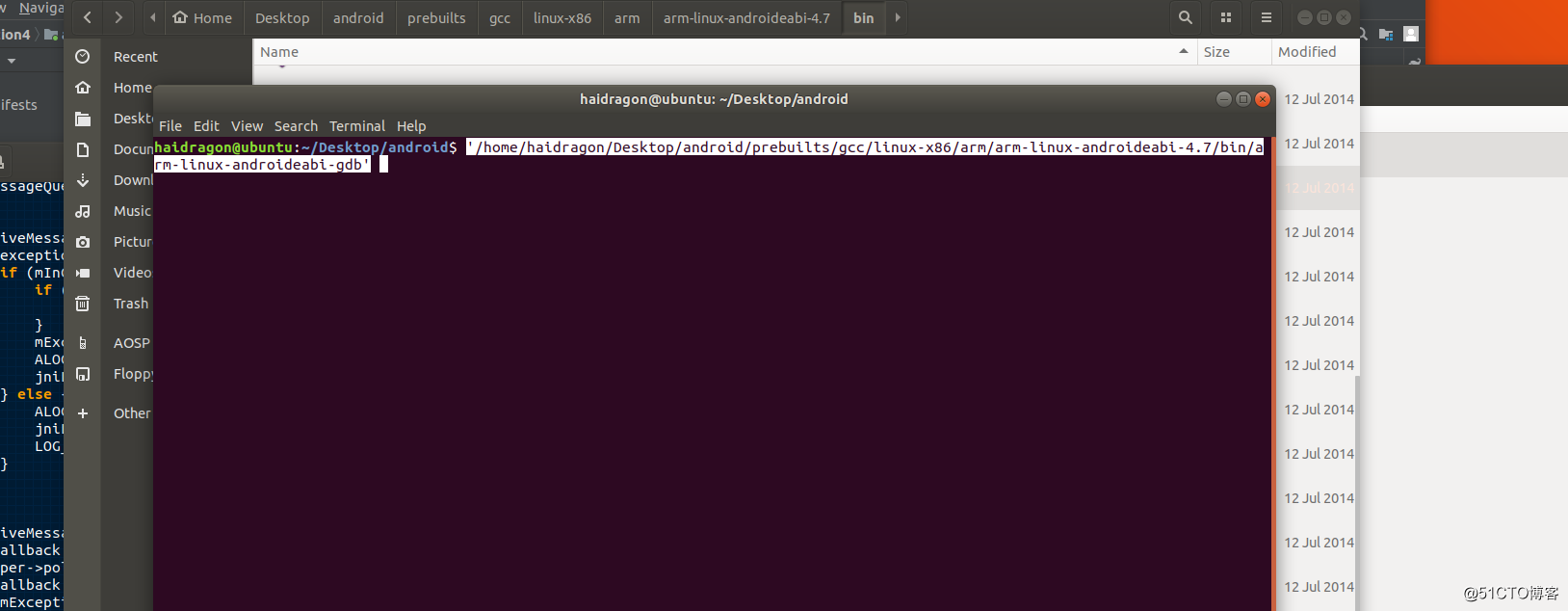
Load binary file, load the symbol root, root-source load path
haidragon@ubuntu:~/Desktop/android$ '/home/haidragon/Desktop/android/prebuilts/gcc/linux-x86/arm/arm-linux-androideabi-4.7/bin/arm-linux-androideabi-gdb'
GNU gdb (GDB) 7.6
Copyright (C) 2013 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law. Type "show copying"
and "show warranty" for details.
This GDB was configured as "--host=x86_64-linux-gnu --target=arm-linux-android".
For bug reporting instructions, please see:
<http://source.android.com/source/report-bugs.html>.
(gdb) file '/home/haidragon/Desktop/android/out/target/product/mako/symbols/system/bin/app_process'
Reading symbols from /home/haidragon/Desktop/android/out/target/product/mako/symbols/system/bin/app_process...done.
(gdb) set sysroot '/home/haidragon/Desktop/android/out/target/product/mako/symbols'
(gdb) set dir '/home/haidragon/Desktop/android'
(gdb) list
130 /*
131 * sets argv0 to as much of newArgv0 as will fit
132 */
133 static void setArgv0(const char *argv0, const char *newArgv0)
134 {
135 strlcpy(const_cast<char *>(argv0), newArgv0, strlen(argv0));
136 }
137
138 int main(int argc, char* const argv[])
139 {
(gdb)
You can choose to enter gdb tui interface, press ctrl-x a
and connect the server target remote: 9999 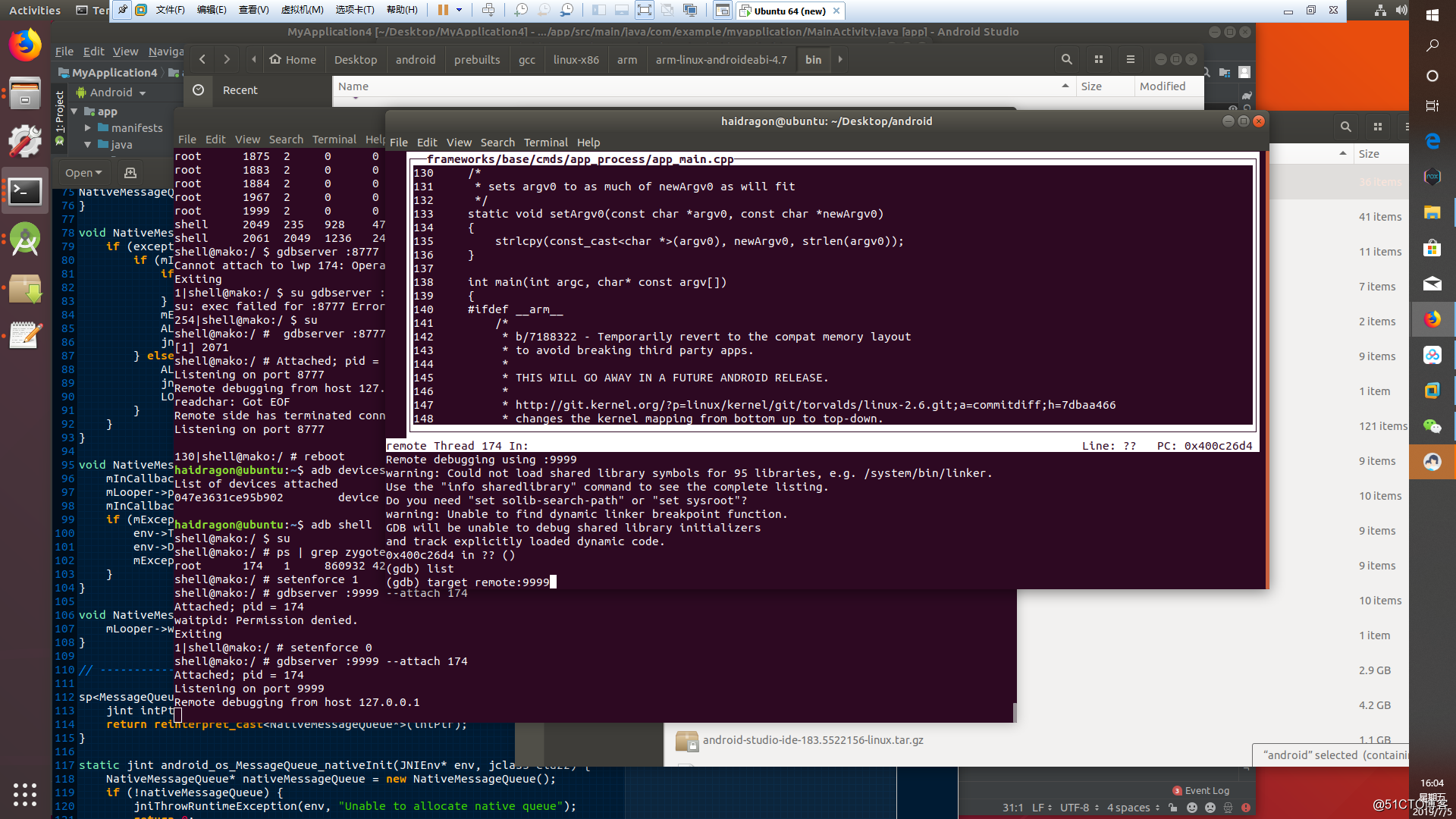
debugger to debug c layer is so, other studies gdb how you can use your own.