CICD Overview
- CI- continuous integration (Continuous Integration): frequent code integrated into the trunk of a development practices, are each integrated automated build (including the compilation, publishing, automated testing) to verify, in order to find as soon as possible through integration errors.
- CD- continuous deployment (Continuous Deployment): submit the code to complete the test automation, build and deploy to the production environment
Do CI / CD in the method Rancher
- With third-party tools, Drone / Travis / Jenkins, with webhook, rancher cli trigger the deployment of updates, etc.
- Use
Rancher pipelinebuild from source to submit an application deployed in the pipeline Rancher
Rancher pipeline deployment
Ranche Pipeline is a new feature Rancher V1.6.13 update release. So if it is not V1.6.13 must first upgrade Rancher's.
Rancher pipeline installation is very simple, search pipeline app store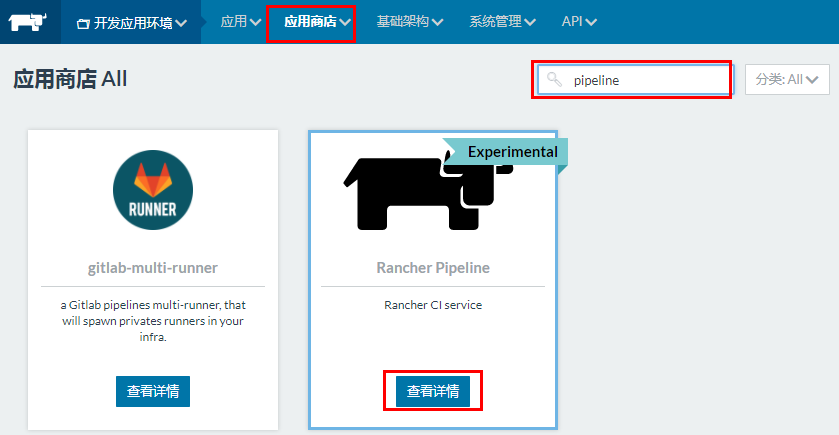
With a default configuration key deployment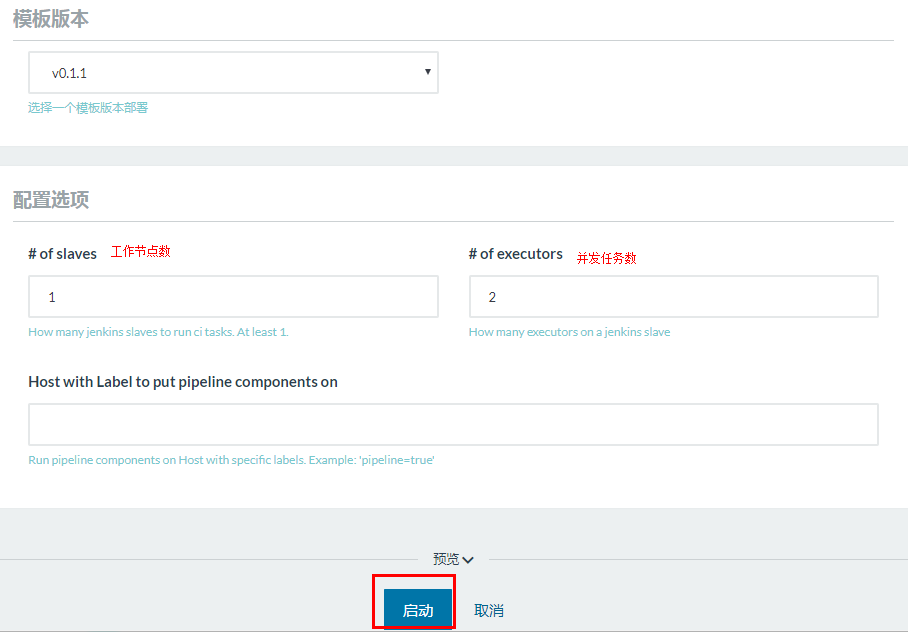
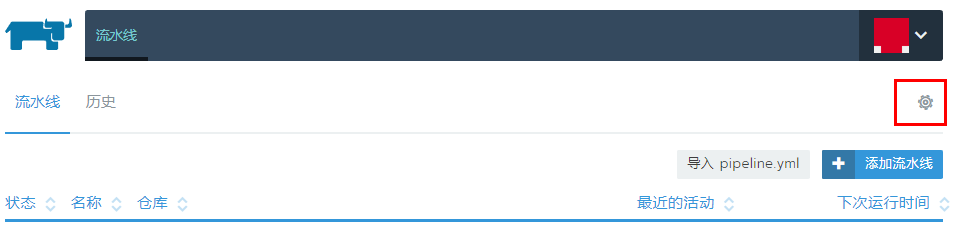
And other infrastructure applications in the pipeline after the services are started, you will see a line at the top of the menu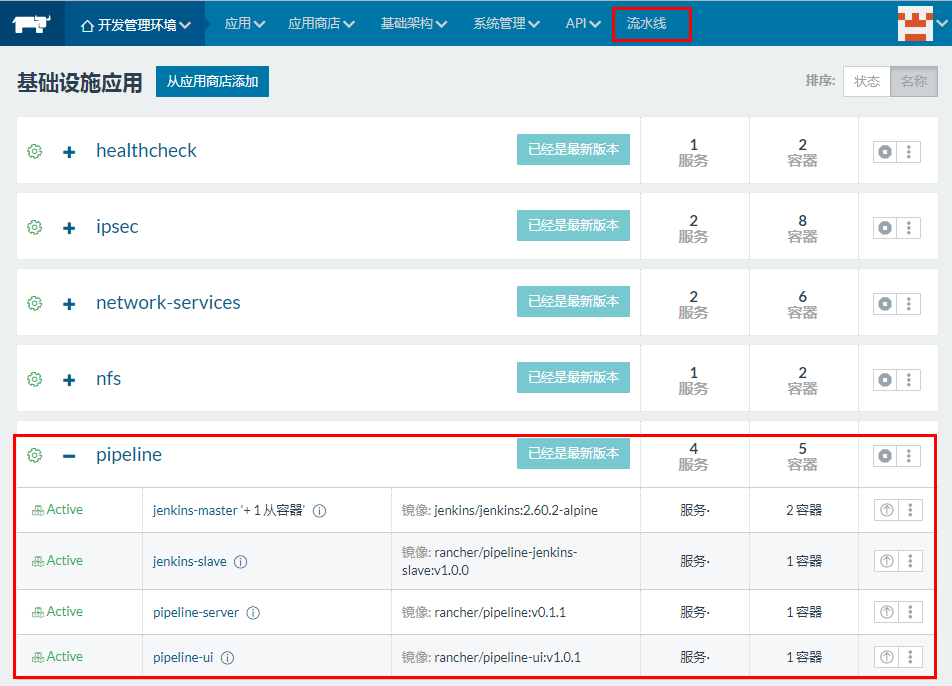
The first may be due to load UI files will be slower when playing lines, the effect after the open as shown below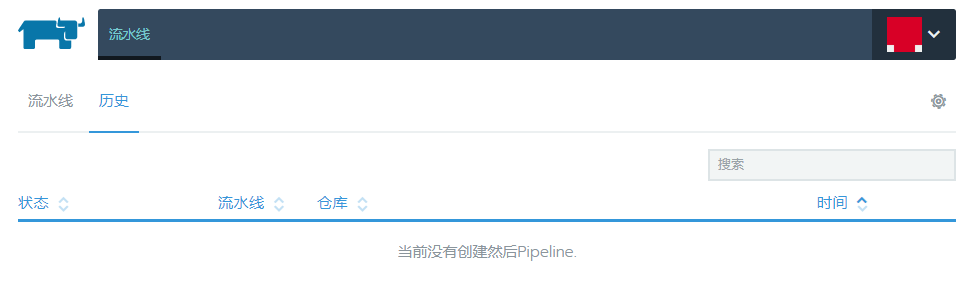
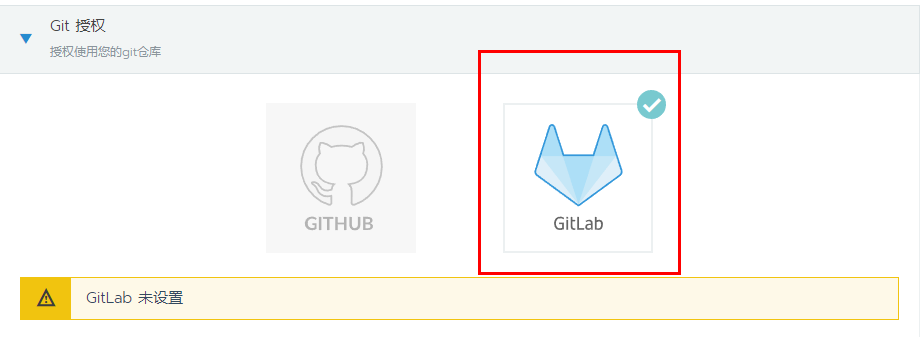
Authorization git repository
Follow the prompts steps to set gitlab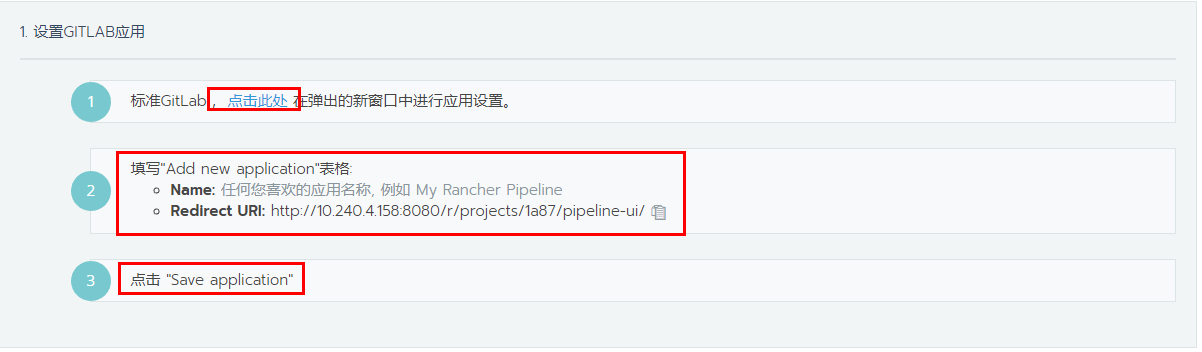
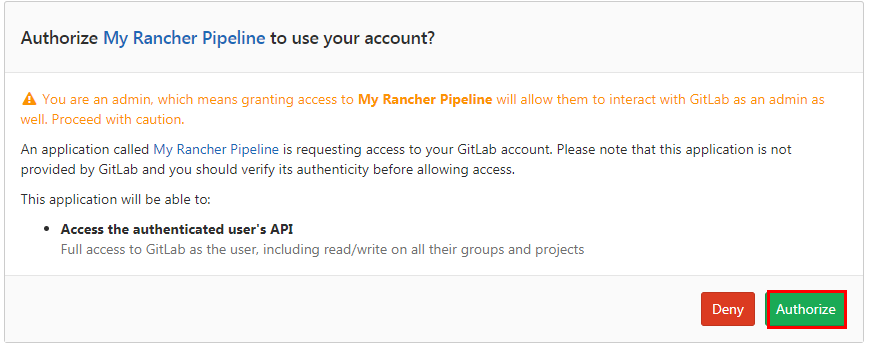
Configuring GitLab of OAuth-based authentication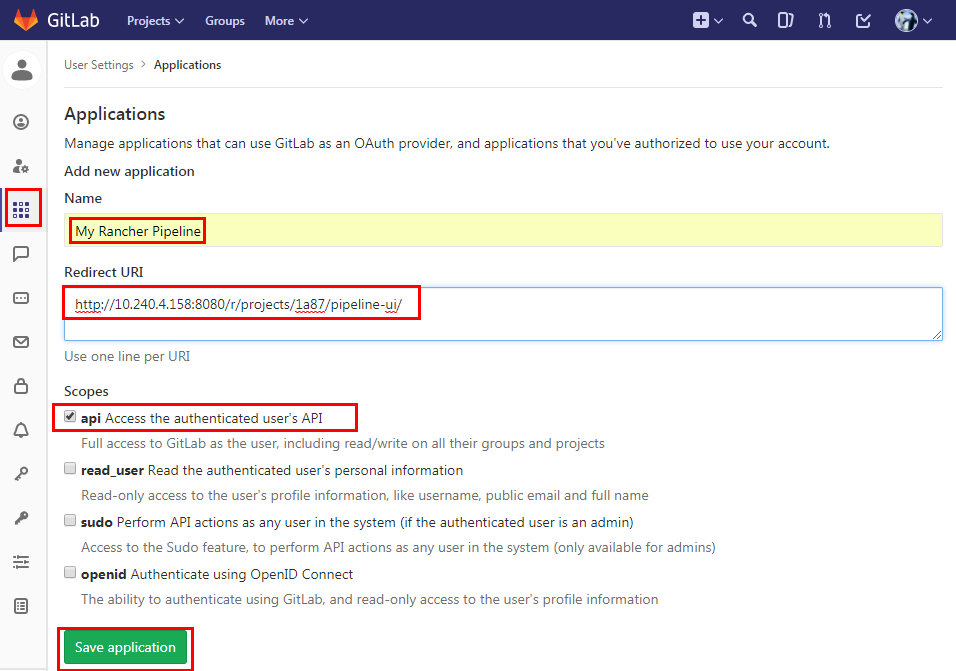
Generating the client ID and secret key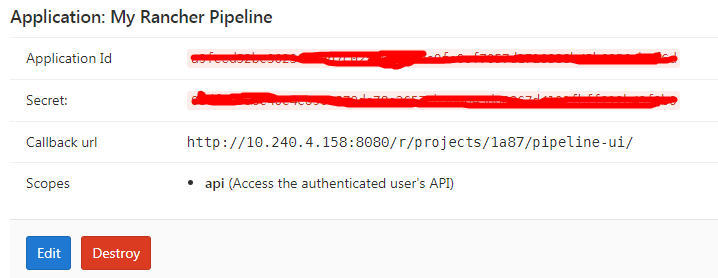
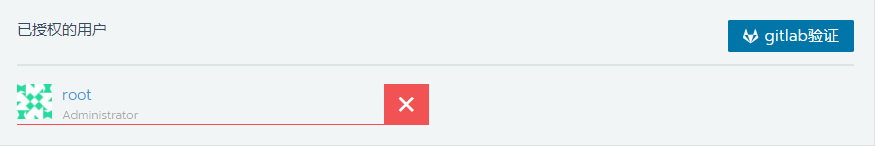
Just fill generated client ID and secret key, and verify the information Tianxie gitlab
You can add many more accounts (gitlab To exit re-login with another account)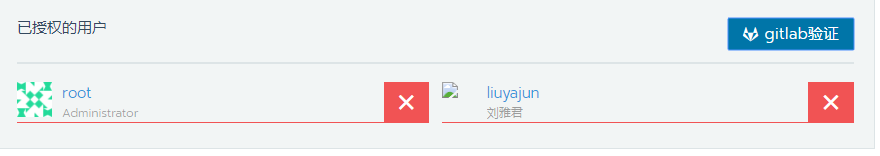
GO DEMO
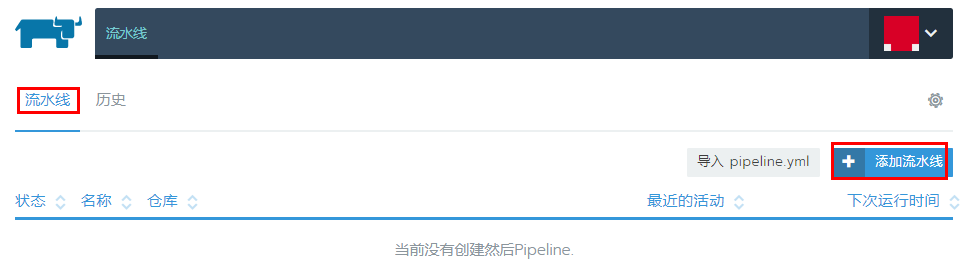
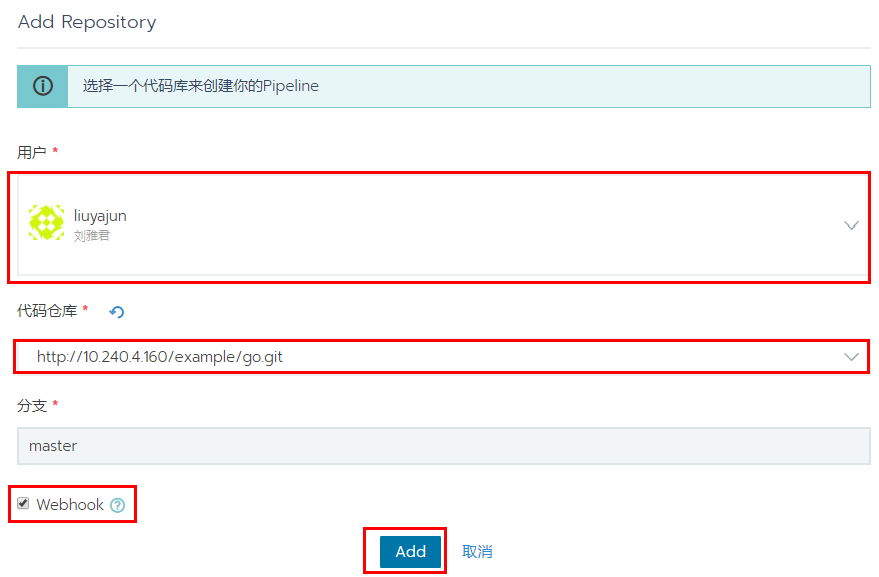
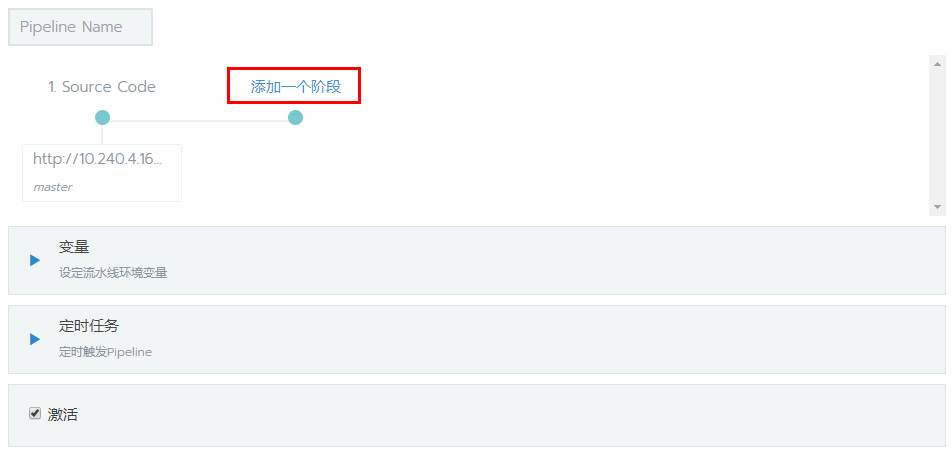
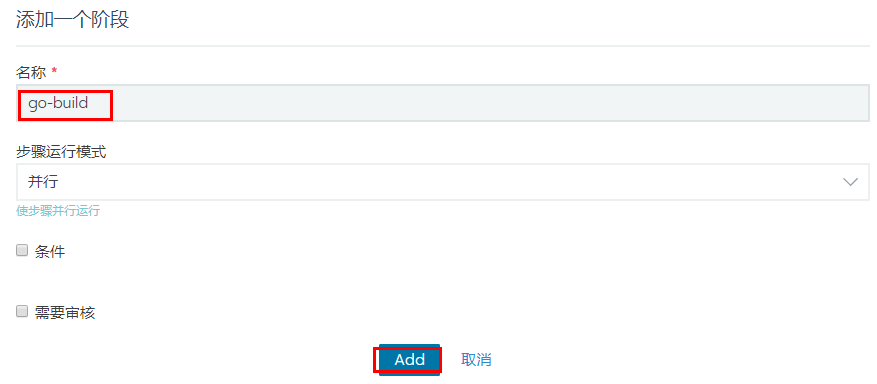
Add lines
mkdir -p /go/src/10.240.4.160/example
ln -s $(pwd) /go/src/10.240.4.160/example/go
cd /go/src/10.240.4.160/example/go/outyet
GOOS=linux GOARCH=amd64 CGO_ENABLED=0 go build -o bin/outyet
docker pull 10.240.4.159/example/outyet:demo
/data/tomcat/webapps:/usr/local/tomcat/webapps
https://github.com/golang/example
创建容器的时候指定启动参数,自动挂载localtime文件到容器内
https://github.com/lawrli
##
参考文档:
将证书拷贝到如10.240.4.158客户机上并信任
scp -P 50022 10.240.4.160.crt 10.240.4.158:/usr/local/share/ca-certificates/
mattermost_external_url ‘https://10.240.4.160‘
mattermost_nginx[‘redirect_http_to_https’] = true
mattermost[‘gitlab_auth_endpoint’] = “https://10.240.4.160/oauth/authorize“
mattermost[‘gitlab_token_endpoint’] = “https://10.240.4.160/oauth/token“
mattermost[‘gitlab_user_api_endpoint’] = “https://10.240.4.160/api/v4/user“
##
openssl req -new -newkey rsa:2048 -nodes -out 10.240.4.160.csr -keyout 10.240.4.160.key -subj "/C=CN/ST=Harbin/L=Harbin/O=ydgw/OU=IT/CN=10.240.4.160" openssl x509 -in 10.240.4.160.crt -text -noout cp 10.240.4.160.crt /usr/local/share/ca-certificates/ /data/dns-etc/resolv.dnsmasq:/etc/resolv.dnsmasq /data/dns-etc/dnsmasqhosts:/etc/dnsmasqhosts /data/dns-etc/dnsmasq.conf:/etc/dnsmasq.conf /etc/localtime:/etc/localtime:ro dns (Expected state running but got error: Error response from daemon: OCI runtime create failed: container_linux.go:296: starting container process caused "process_linux.go:398: container init caused \"rootfs_linux.go:58: mounting \\\"/data/docker-dns/dnsmasq.conf\\\" to rootfs \\\"/var/lib/docker/aufs/mnt/3daf5708bcea4ec8da7108e5c8d6b2d030010e5a1fbe7d86349dc3db1a3fd774\\\" at \\\"/var/lib/docker/aufs/mnt/3daf5708bcea4ec8da7108e5c8d6b2d030010e5a1fbe7d86349dc3db1a3fd774/etc/dnsmasq.conf\\\" caused \\\"not a directory\\\"\"": unknown: Are you trying to mount a directory onto a file (or vice-versa)? Check if the specified host path exists and is the expected type) docker run -d -p 53:53/tcp -p 53:53/udp --cap-add=NET_ADMIN --name dns-server andyshinn/dnsmasq docker pull andyshinn/dnsmasq mkdir -p /data/docker-dns cd /data/docker-dns vi resolv.dnsmasq nameserver 202.97.224.68 nameserver 114.114.114.114 nameserver 8.8.8.8 vi dnsmasqhosts 10.240.4.160 gitlab gitlab.ydgw.cn vi dnsmasq.conf resolv-file=/etc/dnsmasq.d/resolv.dnsmasq addn-hosts=/etc/dnsmasq.d/dnsmasqhosts resolv-file=/etc/dnsmasq.d/resolv.dnsmasq addn-hosts=/etc/dnsmasq.d/dnsmasqhosts docker tag SOURCE_IMAGE[:TAG] 10.240.4.159/app/IMAGE[:TAG] docker-compose -f ./dns.yaml up -d
容器-Docker为什么火?
Google自2004年就开始使用容器技术,目前他们每周要启动超过20亿个容器,每秒种新启动的容器就超过3000个,在容器技术方面有大量的积累。
曾相继开源了Cgroup(Control Groups)和Imctfy(Google开源Linux容器)这两个重量级项目。Google对Docker的支持力度非常大,不仅把imctfy先进之处融入Docker之中,还把自已的容器管理系统(kubernetes)也开源出来。
技术的发展产生了大量优秀的系统和软件。
操作系统:Redhat/Centos、Debian/Ubuntu、FreeBSD、SUSE等
编程语言:Java、Python、Ruby、Golang、C/C++等
WEB服务器:Apache、Nginx、Lighttpd等
数据库:Mysql、Redis、Mongodb等
软件开发人员在这么多种类中自由选择,结果就是维护一个非常庞大的开发、测试和生产环境,开发、测试和运维人员就会被种类繁多的环境折腾的筋疲力尽。即使只选择其中一两种,随着操作系统和软件版本的更新迭代,维护工作还是变得越来越庞大。