We recommend the use of site-to-site *** or point-to-site *** Remote Access Port Access Management (RDP, SQL host, etc.). Security group or the network configuration, the DMZ is divided
Another method is the default port change to a larger range. This is not very good security, because the port is still fully exposed to the Internet, but better than the direct use of 3389.
The following procedure will update the RDP port, create inbound firewall rules and updated Windows Azure Security Group (NSG).
Note: As with any change, this change in production before, make sure you fully understand the contents of changes to be made, and there is a rollback plan.
Windows firewall and registry changes #PS Code:
# Write-host "What Port would you like to set for RDP: " -ForegroundColor Yellow -NoNewline;$RDPPort = Read-Host
# Set-ItemProperty -Path "HKLM:\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-TCP\" -Name PortNumber -Value $RDPPort
New-NetFirewallRule -DisplayName "RDP HighPort" -Direction Inbound –LocalPort $RDPPort -Protocol TCP -Action Allow Write-host "port number is $RDPPORT" -ForegroundColor MagentaWrite-host "Launch RDP with IP:$RDPORT or cmdline MSTSC /V [ip]:$RDPORT"
Steps:
# Using Powershell update VM port
1. The administrator runs the Powershell command line
2. Paste command line, type VM Host will use high-end port
3. Configure Windows Firewall policy
RDP and Windows Firewall with the new port configuration update
4. Restart the VM Host
# GUI graphical interface by updating the network security group (NSG).
1. Select Modify VM Host, click on the network interface name
2. Network security group
3. Click Network Group Name
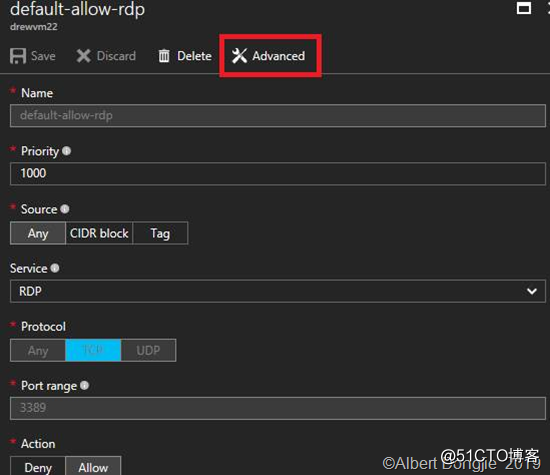
4. Select the default-allow-rdp
5. Click on Advanced
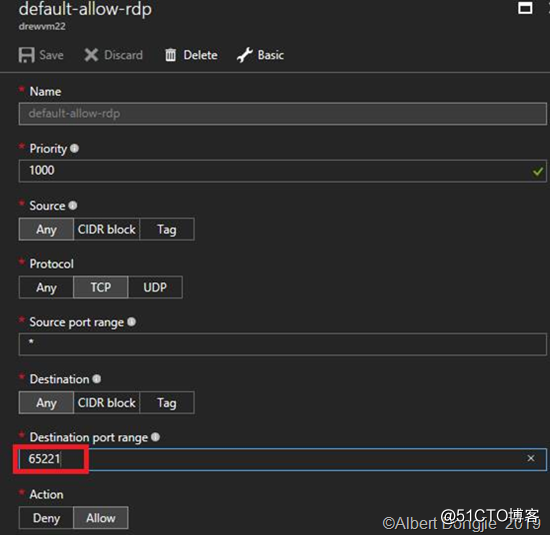
6. Select the port to update the port range we need to customize.
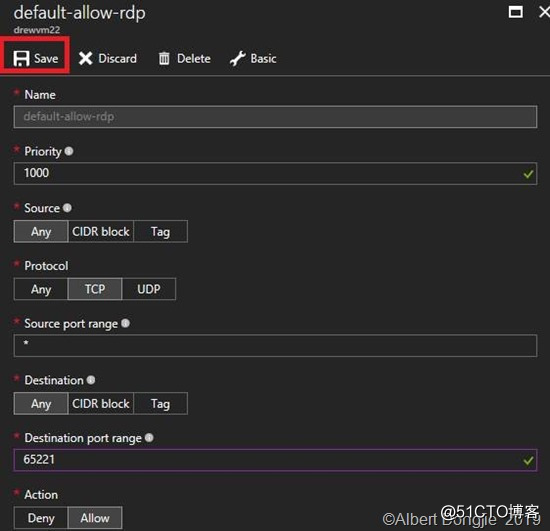
7. Click outside the box, "Save"
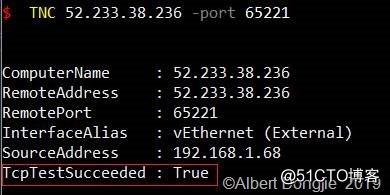
8. Wait NSG updated, it was confirmed that the port is listening by Powershell TNC: {TNC IPAddress -Port PORT} confirmed as true.
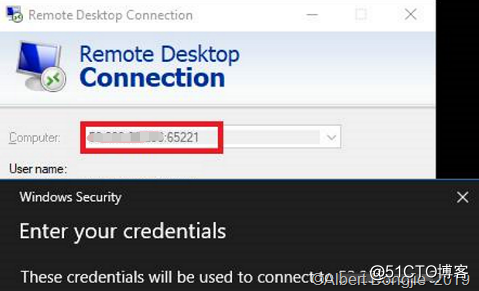
Start RDP, enter {IPAddress: Port}, a new high verify the configuration access port

![clip_image002[7] clip_image002[7]](https://s4.51cto.com/images/blog/202003/17/de0b35dedfd3ee2ded0de3bb5cbccca1.png?x-oss-process=image/watermark,size_16,text_QDUxQ1RP5Y2a5a6i,color_FFFFFF,t_100,g_se,x_10,y_10,shadow_90,type_ZmFuZ3poZW5naGVpdGk=)
![clip_image003[7] clip_image003[7]](https://s4.51cto.com/images/blog/202003/17/87fcae15ebcde3d39410b02ae15fb22f.png?x-oss-process=image/watermark,size_16,text_QDUxQ1RP5Y2a5a6i,color_FFFFFF,t_100,g_se,x_10,y_10,shadow_90,type_ZmFuZ3poZW5naGVpdGk=)
![clip_image004[5] clip_image004[5]](https://s4.51cto.com/images/blog/202003/17/b48caf8adac0e4d2e8eae568ad073b8b.png?x-oss-process=image/watermark,size_16,text_QDUxQ1RP5Y2a5a6i,color_FFFFFF,t_100,g_se,x_10,y_10,shadow_90,type_ZmFuZ3poZW5naGVpdGk=)
![clip_image005[5] clip_image005[5]](https://s4.51cto.com/images/blog/202003/17/1e959e9f7bd18042c6a38f568f22e0f1.png?x-oss-process=image/watermark,size_16,text_QDUxQ1RP5Y2a5a6i,color_FFFFFF,t_100,g_se,x_10,y_10,shadow_90,type_ZmFuZ3poZW5naGVpdGk=)
![clip_image006[5] clip_image006[5]](https://s4.51cto.com/images/blog/202003/17/f60696e8a51a31ec4b4ae7c38aa4837b.png?x-oss-process=image/watermark,size_16,text_QDUxQ1RP5Y2a5a6i,color_FFFFFF,t_100,g_se,x_10,y_10,shadow_90,type_ZmFuZ3poZW5naGVpdGk=)