Sql language basis:
The core idea: We have constructed the code for a query, and then added to the statement, resulting in some of the data you want.
Mysql is an open source database
APP Serv: Apache + php + mysql, equivalent phpstudy (recommended mounted on the machine, installed in the virtual machine is not recommended)
Installation (main): four main pieces to be installed, local web site needs its own name, for example: www.test.com
Then set the Mysql password, select allowed through the firewall.
The default start Apache and mysql
Mysql operation:
Mysql.exe mysqld.exe open the file and the folder where the copy path address;

Log database:

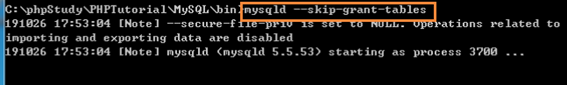
May be unauthorized access, then skip the mysql user authentication. Note Enter this command after the command line can not operate, and then you can then open a new command line.
Note: The first ended before you enter this command in Task Manager mysqld.exe process to ensure mysql server has finished running; then enter the mysql directly, do not need to take any login parameters can directly enter the landing on the database
At this point we can carry out a series of operations
Input select version (); display the current version number

Enter show databases; see what the current database contains (it can be seen from the following six databases)
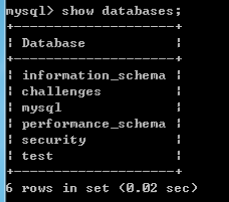
Information_schema, mysql, built-in, no need to do any changes except, test, because the test
Originally used for testing
Open the test database: use test;
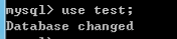
Display the currently open database: select database;

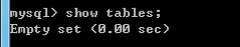
Display table test databases: show tables; (where you can see the test database table is empty)
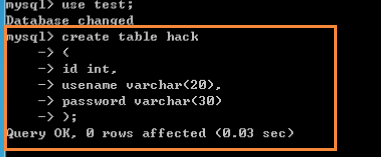
Create a table:
mysql> create table hack to create a table hack;
-> (Table of Contents of the following;
-> id int id field is an integer type
-> usename varchar (20), usename is 20 bytes in length of the variable length type
->password varchar(30)
->);
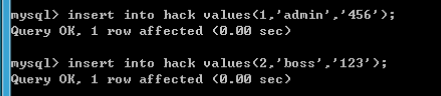
往表里添加记录:
insert into hack values(1,’admin’,’456’);
insert into hack values(2,’boss’,’123’);
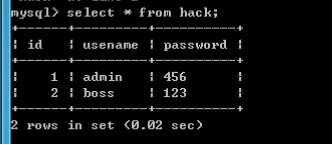
select查询语句:
select * from hack; 显示hack表里所有字段内容;
select usename,password from hack; 只显示usename和password两个字段的内容;

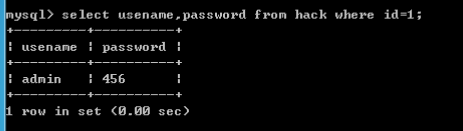
select usename,password from hack where id=1; 从hack表中查找满足条件id=1的记录;
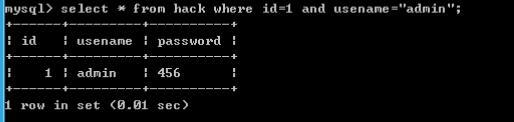
select * from hack where id=1 and usename=’admin’; 从hack表中查找满足id=1且usename=”admin”时的记录;
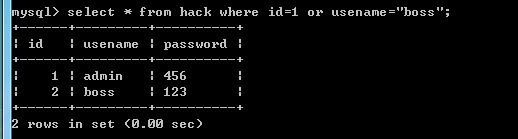
select * from hack where id=1 or usename=”boss”; 从hack表中查找满足id=1或者usename=”admin”时的记录;
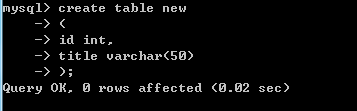
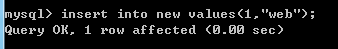
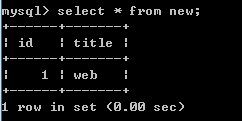
我们再创建个表new
我们还可以删除表(这里以删除表news为例)
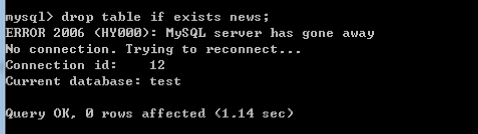
验证删除表news是否成功:

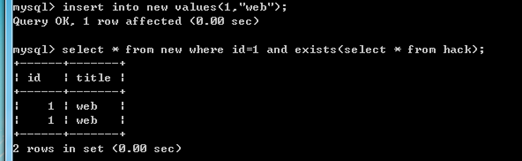
select * from new where id=1 and exists(select * from hack); 判断在hack数据库中查找关于new表中是否存在id=1的字段;
select * from hack order by password; 查询所有字段,按照password来排序(默认升序)

select * from hack order by 4; 查询hack数据库的字段数(这里可以看到不存在4个字段)
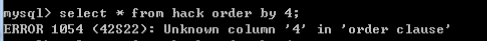
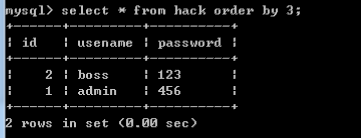
select * from hack order by 3; 判断当前查询显示几个字段,这里用3判断了下,说明是存在3个字段的
Union联合查询:
知道显示的是几个字段显示几个字段有什么用呢?
其实就是为了我们后面的union联合查询,可以使用union查询一次性执行两个或者多个查询,并将它们的结果组合在一起输出显示。必须知道有多少个字段才能执行。
这里需要特别注意的是union联合查询的基本规则就是所有查询中的列数必须相同。意思就是说前面的查询结果的字段数跟后面查询结果的字段数必须是一样的。
具体查询操作如下所示:
查询new表字段数,如下图可以看到,有两个字段

查询hack表字段数,如下图可以看到,有三个字段

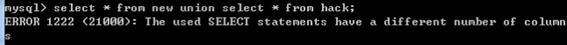
由前面我们知道new表中有两个字段,hack表中有3个字段,当我们输入: select * from new union select * from hack; 时查询是报错的,报错原因说的是字段数不匹配
不匹配怎么办呢?我们保证前后字段数相同不就行啦!
new表有两个字段,我们让hack表也只显示两个字段(usename和password)
我们再输入select * from new union select usename,password from hack;

看到没,成功啦!
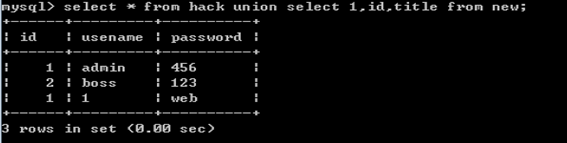
那么我们还可以满足hack表,让new表显示3个字段
输入 select * from hack union select 1,2,3 from new; 其中1,2,3可以替换成new表中的字段名
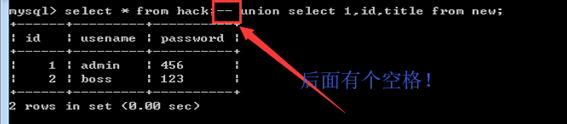
例如我这里要同时输入hack表里所有字段和new表里id和title两个字段如下所示。
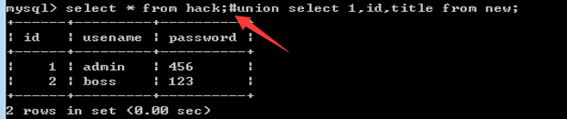
最后说一下mysql中的注释语句,因为有时我们需要屏蔽一下语句的作用,就需要用到注释符。
单行注释:在某一行中插入一个符号,这一行就没有意义了,例如,我们在此处插入#,后面的语句就被注释掉了,输出结果就不会显示。
除了# 还有-- 注释符,注意:这里—后面有一个空格
多行注释:/* */,”/*”用于注释文字的开头,”*/”用于注释文字的结尾。
学到这里我们几乎就可以开始sql注入啦!!