Chinese People's Public Security University
Chinese people’ public security university
Network Warfare Technology
experimental report
| Third experiment |
| Password cracking techniques |
| student name |
Chen Ziwei |
| grade |
2017 |
| District Team |
Four area teams |
| mentor |
Your opinion |
Institute of Technology and Information Network Security
2016 Nian 11 Yue 7 Ri
Master experimental task
2016-2017 school year, Di Yi semester
First, the purpose of the experiment
1 . Deepen and digest this course lectures, review what they have learned through the Internet search techniques, methods and techniques;
2 . Become familiar with commonly used encryption algorithm, encryption and decryption tools, tools and other Internet resources to crack, given the ciphertext, encrypted file system password to crack;
3 . The purpose of the consolidation of curriculum knowledge and practical application.
Second, the experimental requirements
1 . Carefully read the contents of each experiment, we need to capture the title, to be clear screenshots and annotate screenshots and descriptions.
2 . Documentation Requirements clear structure, graphic expression accurate labeling specifications. Reasoning was objective, reasonable and logical.
3 . Software tools can be used john the ripper or Hydra , dictionary generator, pwdump7 like.
4 . After the experiment, to retain electronic documents.
Third, the experimental procedures
1 . ready
Experimental preparation well in advance, should learn more about the purpose of the experiment, test requirements and test content before the experiment, familiar with the software tools and ready with a good experiment, in accordance with the requirements of experimental content and experimental content ready ahead of time.
2 . lab environment
Describes the hardware and software environment used in the experiment (including a variety of software tools);
Boot and start the software office2003 or 2007 , browser, encryption and decryption software.
3 . experiment procedure
1 ) Start the system and start-up tool environment.
2 ) realization of experimental content using software tools.
4 . experimental report
Write lab reports in accordance with the standard requirements of the test report format. The document prepared in accordance with the format template embedded test report document, the document written in accordance with the provisions of the written format, the form must be said that the graphics have a table Illustrated.
Tool here (the school site visits)
http://121.194.212.168/eol/homepage/course/layout/page/index.jsp?courseId=14280
The left teaching materials, tools and sample in
Tasks (a)
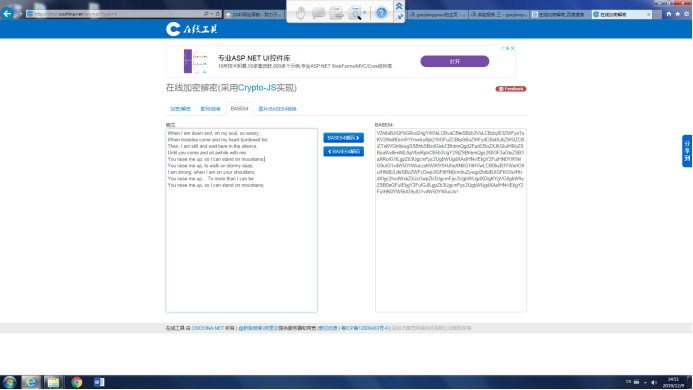
1. Please decrypt the following string 35556C826BF3ADDFA2BB0F86E0819A6C . (Screenshot attached)

2.
This seems to be a lyric, please tell me the song decrypted.
V2hlbiBJIGFtIGRvd24gYW5kLCBvaCBteSBzb3VsLCBzbyB3ZWFyeTsKV2hlbiB0cm91YmxlcyBjb21lIGFuZCBteSBoZWFydCBidXJkZW5lZCBiZTsKVGhlbiwgSSBhbSBzdGlsbCBhbmQgd2FpdCBoZXJlIGluIHRoZSBzaWxlbmNlLApVbnRpbCB5b3UgY29tZSBhbmQgc2l0IGF3aGlsZSB3aXRoIG1lLgpZb3UgcmFpc2UgbWUgdXAsIHNvIEkgY2FuIHN0YW5kIG9uIG1vdW50YWluczsKWW91IHJhaXNlIG1lIHVwLCB0byB3YWxrIG9uIHN0b3JteSBzZWFzOwpJIGFtIHN0cm9uZywgd2hlbiBJIGFtIG9uIHlvdXIgc2hvdWxkZXJzOwpZb3UgcmFpc2UgbWUgdXDigKYgVG8gbW9yZSB0aGFuIEkgY2FuIGJlLgpZb3UgcmFpc2UgbWUgdXAsIHNvIEkgY2FuIHN0YW5kIG9uIG1vdW50YWluczs=
Task (b)
windows system password cracking
1. In the windows xp use system net user gao gao123 / add to add users gao , password gao123 account (user name and password can set their own); and use the net user command to add a user to determine success.

2.使用pwdump软件导出本机的sam文件
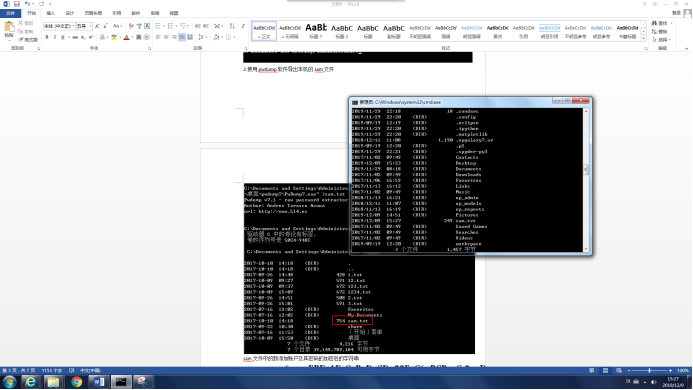
sam文件中的新添加账户及其密码的加密后的字符串
Administrator:500:NO PASSWORD*********************:31D6CFE0D16AE931B73C59D7E0C089C0:::
Guest:501:NO PASSWORD*********************:NO PASSWORD*********************:::
siegz:1003:NO PASSWORD*********************:A13D0272F353A863546EDAD12C3F25A6:::
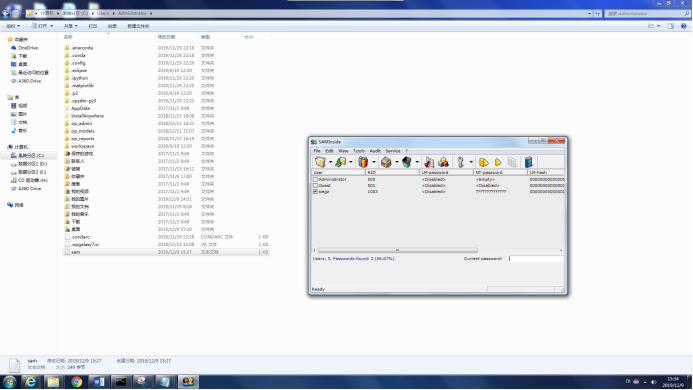
3.使用saminside软件将sam.txt导入,并进行破解,注意配置字典破解和暴力破解
如果遇到复杂密码的LM值破解时间长,可以使用在线破解的方式。
http://www.objectif-securite.ch/ophcrack.php
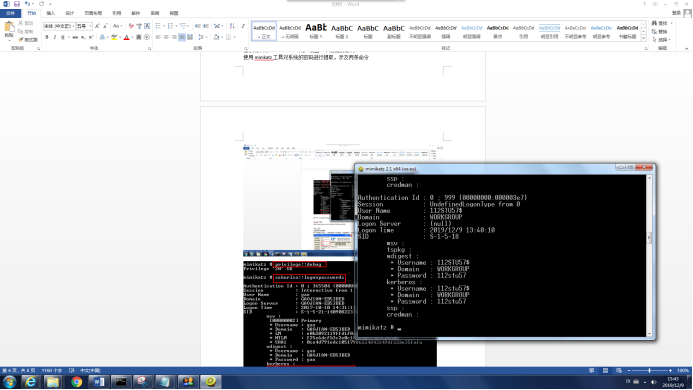
任务(三)
内存密码提取
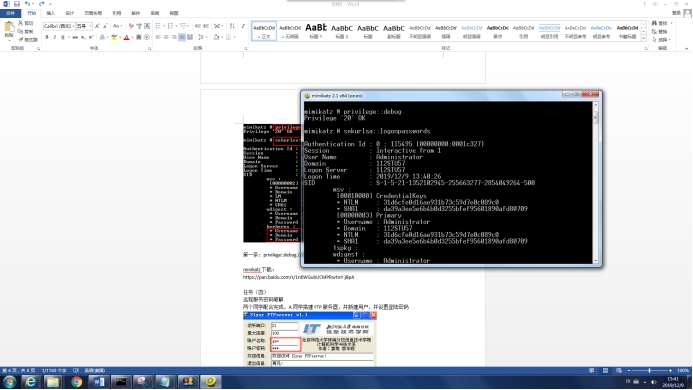
在系统中为Administrator用户设置一个高强度密码。
使用minikatz工具对系统的密码进行提取,涉及两条命令
第一条:privilege::debug //提升权限 第二条:sekurlsa::logonpasswords //抓取密码
minikatz下载:
https://pan.baidu.com/s/1n6WGubUCMPRsvtisY-jBpA
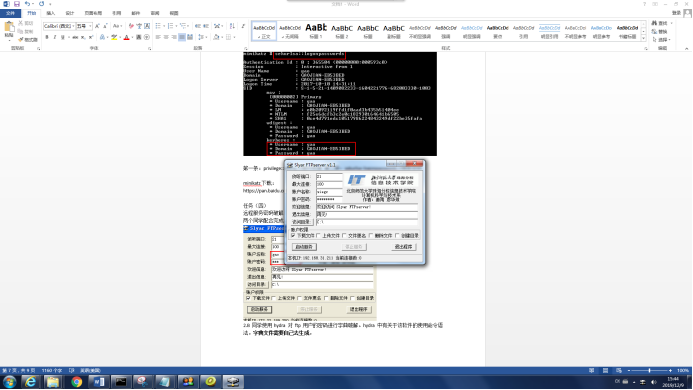
任务(四)
远程服务密码破解
两个同学配合完成,A同学搭建FTP服务器,并新建用户,并设置登陆密码
2.B同学使用hydra 对ftp用户的密码进行字典破解。hydra 中有关于该软件的使用命令语法。字典文件需要自己去生成。

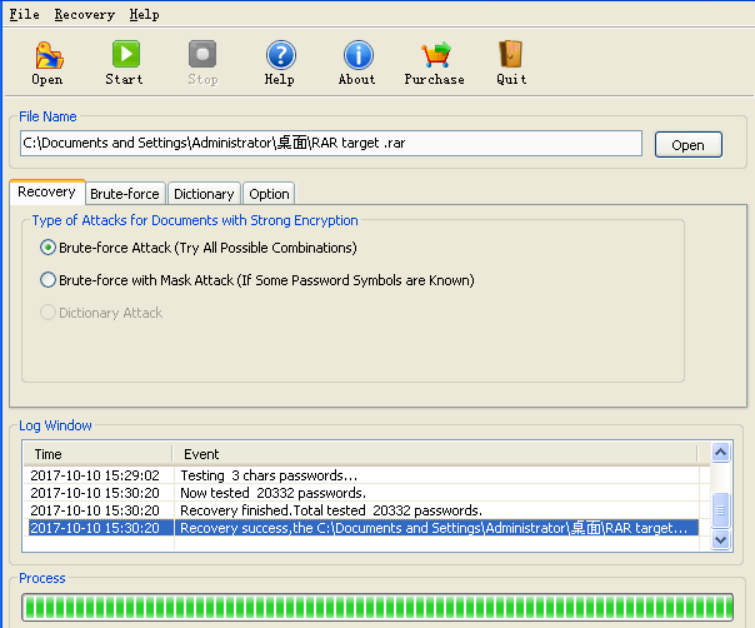
任务(五)
应用程序密码破解
使用Rar crack软件破解,给出的RAR target文件的密码,并查看压缩包中的内容
破解软件和RAR target均在前面给出的链接里。
任务(六)
完成对给定靶机的密码破解,并获取root权限。过程如下:
1.通过对网页的邮箱提取,形成用户表和密码表
2.通过nmap扫描发现其开放端口
3. 通过ssh协议破解获取登陆密码
4. 登陆后查看用户的权限和用户组
5. 提权获取shadow文件内容
6.通过对shadow文件破解获取root密码
相关工具:
john the ripper-windows版
https://pan.baidu.com/s/1mgp7SgvVYY2M_WWjCg-qqg
hydra - windows版
https://pan.baidu.com/s/1LQ1ituR5yGPhaTnT1FTTNg
请参考