In the kernel hook sub :
Since the data of the low 2gb each process is different; kernel hook so because of the sub-code in the high 2gb.
Method 1 (application):
Using the previous example ExAllocatePool (0, size); nonpaged memory and then copied to the non-paged memory shellcode.
Method 2 (steal memory):
Note: when stealing a look at the page attribute is readable and writable executable
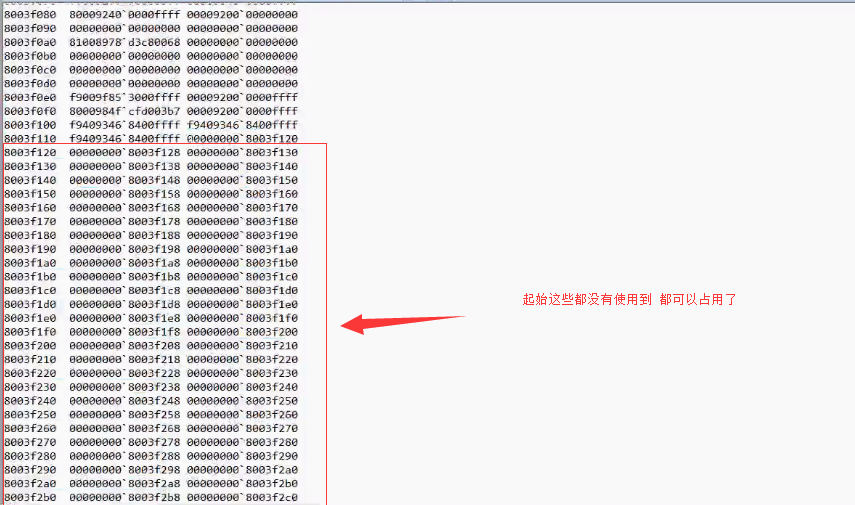
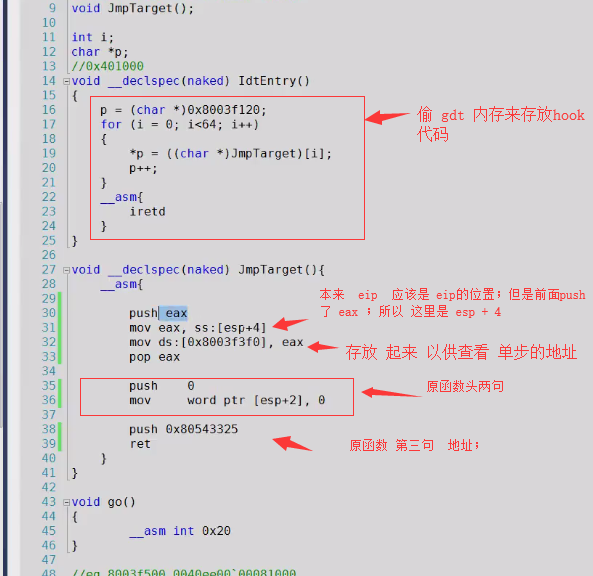
Put our shellcode ;; fixed in the kernel is not used to the place
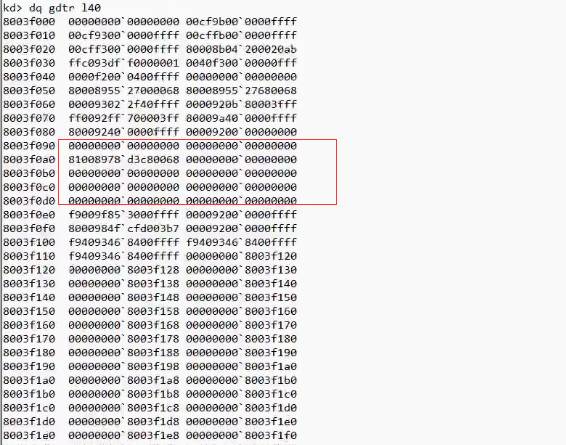
Such as: the empty vector gdtr.
The following are not starting to use, it can be occupied by:
Bare function Note:
Not bare function automatically ebp, esp open flat stack on the stack; so taboo local variable ; can of course manage their stack, local variables used better.
Hook kifastcallentry
Key Conclusions: Note that when
Target address <current address; JMP target offset should be direct - current -5;
Destination address> current address; jmp offset should be the goal - Current -5;
It is the same; base address offset jmp instruction to end the current position .
jmp call registers as registers and what does not need to calculate an offset; register is what jumps.
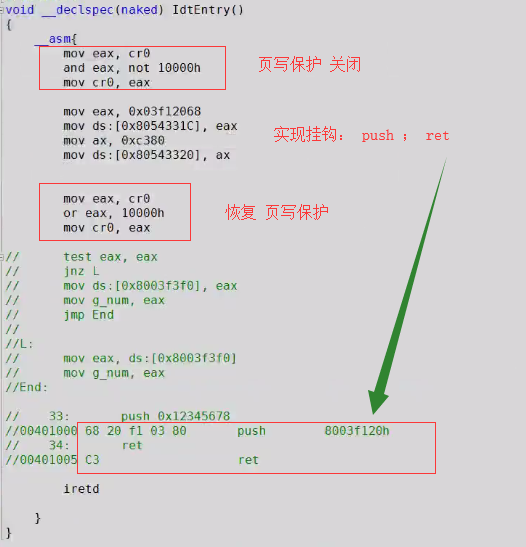
push 0xAddr; ret is not necessary to calculate the offset; but requires 6 bytes; calculation requires five byte offset
Calculating an offset is the most important;
Note the steps of:
-
Calculating a target code offset (or directly register)
-
The opcode for the current position of the modified jump instruction char * [] = {0xe9,0x ..... 0x ..}
-
Then the destination address will be performed well after the stream switching process is preferably performed original stream; recalculated so offset (or register) to jump back;
f7 stepping idt is triggered inside the No. 1 treatment
Use number inside pchunter See idt vector address 1; then use the debugger to view ida;
hook;
As follows:
Program 1: Hook gdt memory address to target function
Program 2: hook logic operation code: