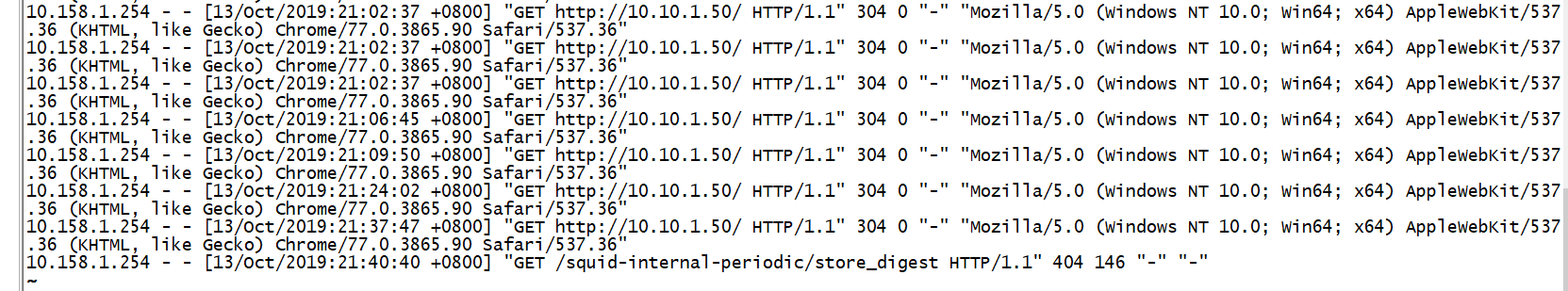
Network topology:
As shown above, the firewall into external / internal / dmz security Zone three, one of which is 10.133.1.100/32 squid cache server dmz zone, 10.158.1.10 / 32,10.158.1.20 / 32 internal to the two internal the web server, firewall external port on the 80-port mapping 10.133.1.100/32 to 10.10.1.50/32, the external client can access through port 80 10.10.1.50/32 of the business.
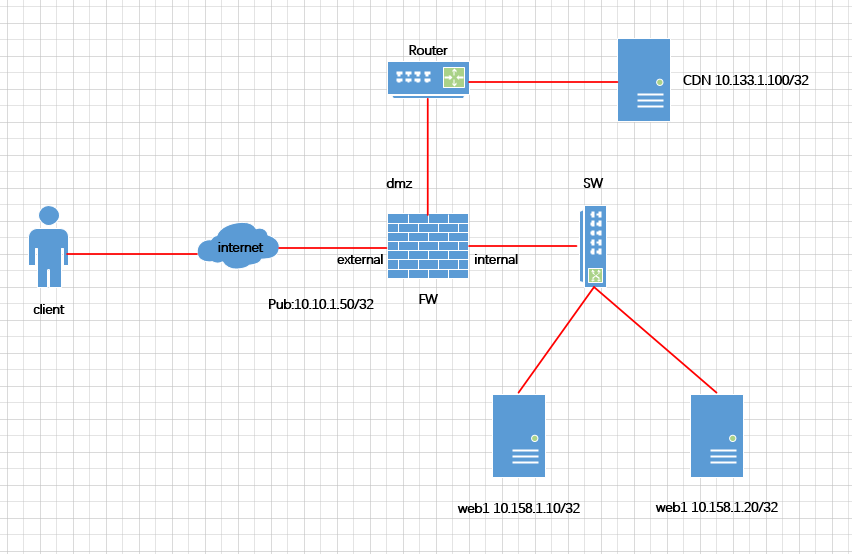
Policy configuration as shown below:
As FIG, 10.133.1.100/32 the squid the DMZ server access port 80 and 10.158.1.20/32 10.158.1.10/32 internal region of the two hosts, but it 10.158.1.10/32 and 10.158.1.20/32 You can not initiate access to the 10.133.1.100/32. Therefore, in the process of configuring firewall policy should be cautious strategy configuration bi-directional exchange of visits, unless there is a demand, one-way access control to avoid some of the internal reverse connection and download like viruses and Trojans to a certain extent.
The client browser access to the following:

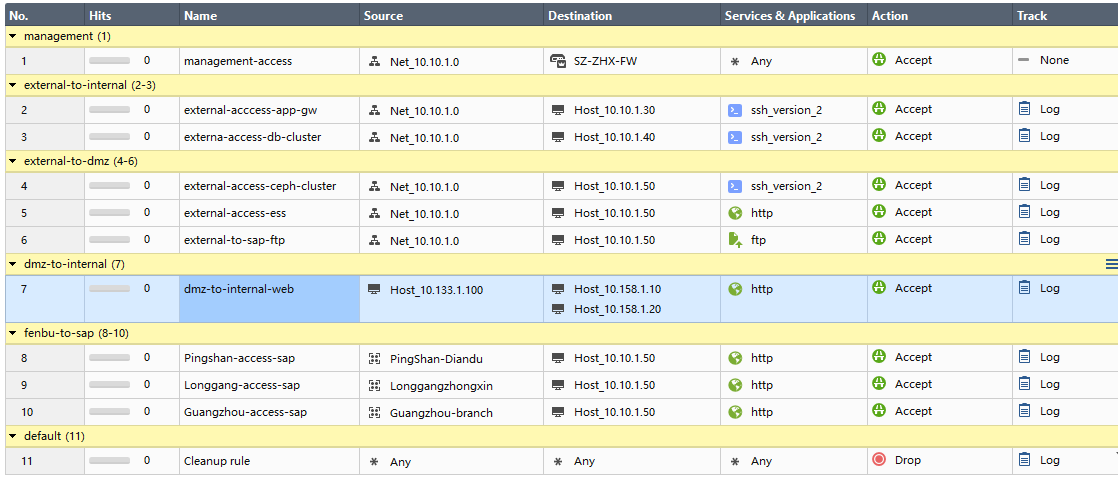
Look squid server access log, as follows:

In the internal server logs to see inside the 10.158.1.10/32: