Single byte character set: All characters are used to indicate a byte, such as ASCII code.
Multi-byte character sets: a multi-byte character sets, a portion of the plurality of bytes represented by byte, another portion (possibly none) are represented by a single byte.
UTF-8 encoding: encoding is an encoding method (multi-byte code), which can be 1 to 4 bytes of one symbol, the symbol changes depending on the byte length.
Common byte width: GB2312, GBK, GB18030, BIG5, Shift_JIS GB2312 byte wide injection does not exist, there is a wide bytes may be collected injected coding.
Prerequisites
Have byte wide injection vulnerability
1, first of all to meet the target program using a two / multi-byte character sets parses
2, followed by a range of different characters are not the same, may not contain lower set of single-byte characters, so no way, so to ensure low byte contains bits set in the range of character types, 0x5C such as (01011100) of character, that is the escape character \.
Byte wide potential safety problem is eating ascll character (one byte) phenomenon
Here we look at an example of use
https://xxxxx?name=hello%27
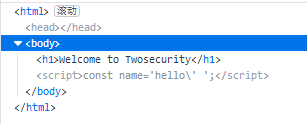
name value in the js, but the input of a single quote is escaped, and no way to escape
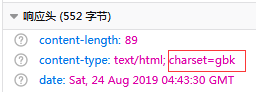
Then look at the page source and request headers, it found that client encoding is gbk
Presumably injected bytes wide, try to enter hello% df% 27

Yes, that is a byte wide, console prompt quotation marks are being given is not closed, and the back is constructed out of js code and comment out the back for the character, so grammatically correct