1. MISC direction
Miscellaneous items are often questions that cannot be classified into other categories, so there are all kinds of questions and the tools are also very complicated.
The main categories are:
1. Video, audio and picture category
- Stegsolve.jar
An image steganography tool that supports the use of different methods to remove image steganography. It is an essential tool for image steganography. Can crack color channel steganography, etc., requires JAVA environment. - QR_Research.exe
is used to scan QR codes. For some questions, you need to prepare the QR code positioning angle map yourself and use the p-map tool to upload it - Audacity.exe
Common audio steganography tool running on windows - outguess (linux)
Open source steganography algorithm, supports files in various formats, written in C language - MP3STEGO.exe
A typical steganography tool for audio. - Invisible Watermark Tool v1.2.exe
is used to add and hide watermarks in pictures. - tweakpng-1.4.6.exe
png image modification and viewing - foremost (linux)
Open source steganography algorithm, supports files in various formats - PotPlayer64
Play the video frame by frame, extract each frame, etc. - wbs43open steganography tool
is suitable for steganography in pdf, bmp image and other formats.
Students who need tools, scan the QR code to get them!
[Click to get them for free]
2. Compressed package and disk forensics
- 010Editor
Aprofessional text editor and hexadecimal editor, its design Designed to quickly and easily edit the contents of any file on your computer. - WinHEX
is a hexadecimal data editing and processing program developed by the German software company X-Ways. - archpr (Advanced Archive Password Recovery)
A compressed package password decompression tool that supports various modes of cracking. - WinRARa64
RAR format decompression tool. - 7zip
Various compression format decompression tools. - Ziperello
ZIP password cracking tool (Ziperello) supports dual mode cracking: brute force/dictionary, and also has advanced features such as breakpoint recovery and mask cracking - Password Dictionary Generator
A dictionary used to generate passwords for blasted compressed packages. - AccessData_FTK_Imager
Disk image forensic tool. You can mount images and create image files. - UltraISO
Virtual optical drive, ISO burning to U disk or CD, compact, free and ad-free - AlternateStreamView
NTFS data stream inspection tool can scan your NTFS drive with one click to find all hidden alternate streams, and then extract the alternate streams to a specified folder . - File format summary.txt
Organization of various compressed package formats - binwalk& foremost
Detection & separation tool, scans files for hidden files and separates them.
3. wifi, bluetooth, data package
- Wireshark
Multifunctional network packet analysis. It is a free and open source network packet analysis software. The function of network packet analysis software is to intercept network data packets and display the most detailed network data packet information as possible. - fiddler2
HTTP packet capture, a proxy server application for HTTP debugging.
4. Environment (important)
The environment is used in all directions
- Kali Linux (or WSL)
Kali Linux is a Debian-based Linux distribution designed for digital forensics and penetration testing.
is a well-known Linux that integrates many tools. - Java environment
There are many tools developed based on the java environment (providing cross-platform support). - python environment
Many topics such as Crypto, Reverse, Pwn, and Mobile require writing py code to implement.
2. WEB direction
1. Penetration tools
- Burp Suite
Integrated platform for web application penetration testing. Integrated platform for attacking web applications. It contains many tools and has many interfaces designed for these tools to facilitate the process of attacking applications faster.
There is a fee in English. There are third-party versions of earlier generations that provide Chinese translation and registration services. - HackBar-v2.3.1
A browser plug-in for security testing, which can be used in Firefox and Chrome browsers. The functions currently provided are: common encoding and decoding , POST/Cookies data submission, SQL/XSS/LFI/XXE vulnerability testing, etc. The latest version starts charging, and you can register with earlier versions. - sqlmap1.1.3 official version
Sqlmap is an open source automated SQL injection tool. Full support for MySQL, Oracle, PostgreSQL, Microsoft SQL Server. Direct connection to the database without going through SQL injection points is supported if conditions such as database certificate, IP address, port, and database name permit. - Pangolin3.2.4
SQL injection, scanning, etc. - DatabaseBrowser
A free database browser, open source visual tool for creating, designing and modifying database files compatible with SQLite. - Chinese Kitchen Knife&Webshell
webshell, one sentence backdoor - Vulnerability Scan:
Yujian Background Scan Collector’s Edition: Directory Scan
nmap-7.40 official version: Powerful website scanning, supports DOS and graphics
DirBuster-0.12 official version: vulnerability scanning, directory scanning, written in java language
AppScan 8.7 cracked version: powerful WEB vulnerability scanning tool
2. Web environment
- phpStudy (Little Pi Panel)
A program integration package for PHP debugging environment. This package integrates the latest Apache+PHP+MySQL+phpMyAdmin+ZendOptimizer, - PuTTY
is used for remote connection of Linux systems. It is compact, free and ad-free.
Supports a variety of network protocols, including SCP, SSH, Telnet, rlogin and raw socket connections.
One-time installation, no configuration required for use. - Termite- Springboard Management Tool
An intranet penetration tool, divided into management side admin and agent side agent. It supports multiple platforms, forward and reverse cascading between springboard machines, built-in shell management, etc. - SecureCRTSecureFX_7.0.0.326Chinese version
A terminal emulation program with a friendly interface that can log in to the Linux server host under Windows. Not only SupportsSSH1, SSH2, and supports Telnet and rlogin protocols. - WinSCP
A free and open source SCP client, running under Windows system, released under GPL. In addition to SCP, WinSCP also supports SFTP, FTP, WebDAV, and Amazon S3 protocols. - phpMyAdmin
phpMyAdmin secret blast - sunny-ngrok
Domestic intranet mapping server, providing free intranet penetration. - IP high-precision positioning
Query the geographical location of the IP address. - IP proxy pool
3. Crypto Tools
1. Cryptozoology synthesis
- CTFCrackTools V4.0
Developed by Mist Security Official Website, it has built-in current mainstream passwords (including but not limited to Vigilia Cipher, Caesar Cipher, Barrier Cipher... ) Users can write their own plug-ins.
The project is based on java and python, and is open source on github. It is free in English, and there are third-party versions of earlier generations that provide Chinese translation. - CyberChef V9.20.3
A new open source web tool released by the British intelligence agency Government Communications Headquarters (GCHQ) provides convenience for security practitioners to analyze and decrypt data. Known as the "Swiss Network Army Knife", it is executed in the browser in the form of a web page.
The project is open source on github. It is free in English, and there are third-party versions of earlier generations that provide Chinese translation. - pyg cryptography comprehensive tool v5.0
Piaoyun Daniel has synthesized various cryptography encryption algorithms and is an essential tool for researching cryptography. - CAP4
CAP4 is a very simple and practical tool for verifying encryption algorithms. It is a password creation and analysis tool specially developed for teaching. It has been widely used in many universities in the United States. use. This tool includes the cracking of some classical encryption algorithms, such as Caesar cipher, affine cipher, etc. - Cipher Machine v1.0
Including barrier cipher, Caesar cipher, Caesar shift (Chinese version), Vigenie cipher, Morse code, MD5 substitution cipher, substitution cipher and so on.
2. Single encryption and decryption
- RSATool v17
can be used to calculate several parameters in RSA, generate keys, and encrypt and decrypt. It can also be used for some less complex cracking work. - yafu
is used for automatic integer factorization. In RSA, when the values of p and q are too different or too close, yafu can be used to quickly factor n The value is decomposed into p and q values. The principle is to use the Fermat method and Pollard rho method. - TextForever V1.78
The original name of the software is FineReader, which includes HTML to text file conversion, file merging, file segmentation, paragraph merging, paragraph segmentation, and internal code conversion (only (Used under Win 2k/XP), text replacement, HTML sorting, text extraction, regular expressions (requires the support of IE 5.5 or above), batch OCR, tcr file compression/decompression and other functions. - Xiaokui multifunctional conversion tool
supports converting common encodings into URL/SQL_En/Hex/Asc/MD5_32/MD5_16/Base64 and other formats, and also supports decrypting base64 encoding. - md5crack3
MD5 crack is magical and supports saving progress and custom cracking. - superdic super dictionary generator
A password dictionary generation tool. The program uses a highly optimized algorithm to create dictionaries very quickly. - ASCII Code Changer v3.0
A tool specially used to convert characters into decimal and hexadecimal ASCII codes. It can also convert decimal and hexadecimal Convert ASCII code back to characters. - RegexTester
Use the tool regex tester to match regular expressions - snow encryption
A decryption tool for a specific encryption algorithm snow - Fence password encryption and decryption 1.10
is used for fence password encryption and decryption - UNICODE2ANSI converter
supports conversion between ascll code and unicode
3. Online tools (many)
- CTF online tool by CTFcode
http://www.hiencode.com/ - CTF tool resource library by HBCTF team (including resource download)
https://www.ctftools.com/down/ - CTF-Wiki (you can go offline with github)
https://ctf-wiki.org/introduction/resources/#ctf_1 - Mengyan Society New Testament Buddhism and Zen
http://hi.pcmoe.net/buddha.html - Wait many
4. Reverse direction tool
1. Decompilation of c family
- Interactive disassembler IDA Pro
The best one at presentStatic decompilation software, cross Windows or Linux WinCE MacOS platform host to analyze the program, is recognized as the best reverse engineering tool money can buy. Cross-platform. Supports all programs of the C family. - Exeinfo PE
A new generation of universal shell checking software that is short and concise and has functions similar to the PEiD shell checking program. It has a built-in massive PEiD signature library and integrates nearly 50 plug-ins and is more complete. Chinese language pack. - OllyDBG second generation
A newdynamic tracking tool that combines IDA with SoftICE Product, Ring 3 level debugger. - C32Asm
Quickly statically decompile PE format files (Exe, Dll, etc.).
Provides memory dump, memory editing, PE file dump, PE memory ImageSize correction and other practical functions; provides memory disassembly function, provides assembly statement direct modification function, eliminating the need for direct operation of OPCode Cumbersome;
2. python decompilation
- pyinstxtractor
is a script used to decompile the exe packaged by PyInstaller. Written based on python and open source on github. - Uncompyle6
can decompilepyc to produce a py file. Written based on python and open source on github. - Online pyc decompilation tool
https://tool.lu/pyc/
5. Pwn direction tool
1. Python-based library
- pwn
is a CTF (Capture The Flag) framework, and is an exploit development library written in Python. It is mainly designed for rapid prototyping and development, and is dedicated to making Users write exploits that are as brief as possible. - gmpy2
The GNU high-precision arithmetic operation library not only provides high-precision operations for ordinary integers, real numbers, and floating-point numbers, but also generates random numbers. In particular, it provides a very complete Operational interfaces in number theory, such as Miller-Rabin prime number testing algorithm, large prime number generation, Euclidean algorithm, finding the inverse of elements in a field, Jacobi symbols, legendre symbols, etc. - base64
py's built-in library supports various processing of base64. base64 is an encoding method from arbitrary binary to text strings, often used to transmit small amounts of binary data in URLs, cookies, and web pages. - requests
is a Python HTTP library that can easily send http requests and process response results. - Pillow
is the de facto image processing standard library for the Python platform.
2. Tools based on kali linux
- checksec
Check the file protection mechanism and check executable file attributes, such as PIE, RELRO, PaX, Canaries, ASLR, Fortify Source and other attributes. - gdb
GNU symbolic debugger, a powerful command line debugging tool. Supports debugging such as breakpoints, single-step execution, printing variables, observing variables, viewing registers, viewing stacks, etc. - file
The Linux file command is used to identify file types. Through the file command, we can identify the type of the file. Can view 32/64-bit information. - nc
The abbreviation of netcat is known as the Swiss Army Knife of the Internet industry. Because it is short, concise and practical, it is designed to be a simple and reliable network tool. Supports testing linux tcp and udp ports, and is often used for port scanning. - objdump
is used to display information about binary files in a readable format to let you know more about additional information that binary files may contain. - ROPgadget
helps you find suitable gadgets, which is very useful when writing your ROP exp.
6. Mobile Direction Tool
1.java decompilation
- JEB Decompiler
A powerful decompilation tool for Android applications designed for security professionals . Used for reverse engineering or auditing APK files. - jd-gui-1.6.6
A Java decompilation tool developed using C++, It is an independent graphical interfaceJava source code ".class" file decompilationtool. Only 3mb, open source on github, based on jd. JD is a decompiler for the Java programming language. JD is provided as a GUI tool and as a plug-in for the Eclipse and IntelliJ IDEA integrated development environments. - jadx
jadx is a powerful decompilation tool that supports graphical interface and drag-and-drop operation. Open source on github. Can be used across platforms. - ApkIDE_v3.3
A visual, easy-to-use, fast and integrated toolAndroid APK modification tool< a i=3>, integrates Apk modification tools such as ApkTool, Dex2jar, JD-GUI, etc., integrates Apk decompilation, Apk shell checking, encryption and decryption, Apk debugging analysis, Apk packaging, Apk signature, and supports syntax highlighting code editor. - AndroidKiller_v1.3.1
A decompilation software with a visual interface that eliminates the tedious steps of using compilation tools to decompile. - GDA3.97
A simple, lightweight and fast interactive Android decompilation analysis tool
2. ARM assembly modification
- SO Helper 1.2
SH, referred to as SH, is a visual ARM assembly modification tool. It can quickly help you modify the assembly code of SO files, and SH also supports modifying hexadecimal. . - Arm Assembly Converter
A green and compact assembly conversion tool that does not require installation. Using this Arm assembly conversion assistant can easily help users convert assembly into C language.
3. Android unpacking tool
- abe.jar
Extract the Android backup file and unpack the .bak file into an apk. - apktool.jar
Conversion of apk format files and smali files - dex2jar.jar
Conversion of dex format files and jar files - smali.jar
Conversion of dex format files and smali files
4. Android running tools
- NetEase MUMU Android emulator
Produced by NetEase, the interface is brief, about 300M, no lag, relatively few functions, and occasional advertisements. - BlueStacks simulator
is developed by an Indian company. One of the most famous and oldest Android emulators. The principle is to translate the Android underlying API interface into Windows API, which has no requirements on the PC hardware itself and has certain advantages in terms of hardware compatibility. Suitable for playing big games. - Virtualbox
Virtualbox is an open source project under the database giant Oracle. By directly inserting the driver module into the bottom layer of the Windows kernel, it creates a complete virtual computer environment to run the Android system, plus CPU VT Hardware acceleration, performance and compatibility are better, but it has certain requirements for the computer CPU. It is more difficult to use computers that are more than five years old. - Yeshen Emulator
An Android emulator customized based on Virtualbox. Direct integration with NOVA desktop is a major feature of it. However, multi-opening efficiency needs to be improved. Stuttering, delays, and occasional system crashes.
As long as you like my article today, my private network security learning materials will be shared with you for free. Come and see what is available.
Network security learning resource sharing:
Finally, I would like to share with you a complete set of network security learning materials that I have studied myself. I hope it will be helpful to friends who want to learn network security!
Getting Started with Zero Basics
For students who have never been exposed to network security, we have prepared a detailed learning and growth roadmap for you. It can be said to be the most scientific and systematic learning route. It will be no problem for everyone to follow this general direction.
1. Learning roadmap

There are a lot of things to learn about attack and defense. I have written down the specific things you need to learn in the road map above. If you can learn them all, you will have no problem taking on private work.
2. Video tutorial
Although there are many learning resources on the Internet, they are basically incomplete. This is a video tutorial on network security that I recorded myself. I have accompanying video explanations for every knowledge point in the roadmap above. [Click to receive the video tutorial]

I also compiled the technical documents myself, including my experience and technical points in participating in large-scale network security operations, CTF and digging SRC vulnerabilities. There are also more than 200 e-books[Click to receive it Technical Documentation]

(They are all packaged into one piece and cannot be expanded one by one. There are more than 300 episodes in total)
3. Technical documents and e-books
I also compiled the technical documents myself, including my experience and technical points in participating in large-scale network security operations, CTF and digging SRC vulnerabilities. There are also more than 200 e-books[Click to receive it Books]

4. Toolkit, interview questions and source code
"If you want to do your job well, you must first sharpen your tools." I have summarized dozens of the most popular hacking tools for everyone. The scope of coverage mainly focuses on information collection, Android hacking tools, automation tools, phishing, etc. Interested students should not miss it.

Finally, here are the interview questions about network security that I have compiled over the past few years. If you are looking for a job in network security, they will definitely help you a lot.
These questions are often encountered when interviewing Sangfor, Qi Anxin, Tencent or other major companies. If you have good questions or good insights, please share them.
Reference analysis: Sangfor official website, Qi’anxin official website, Freebuf, csdn, etc.
Content features: Clear organization and graphical representation to make it easier to understand.
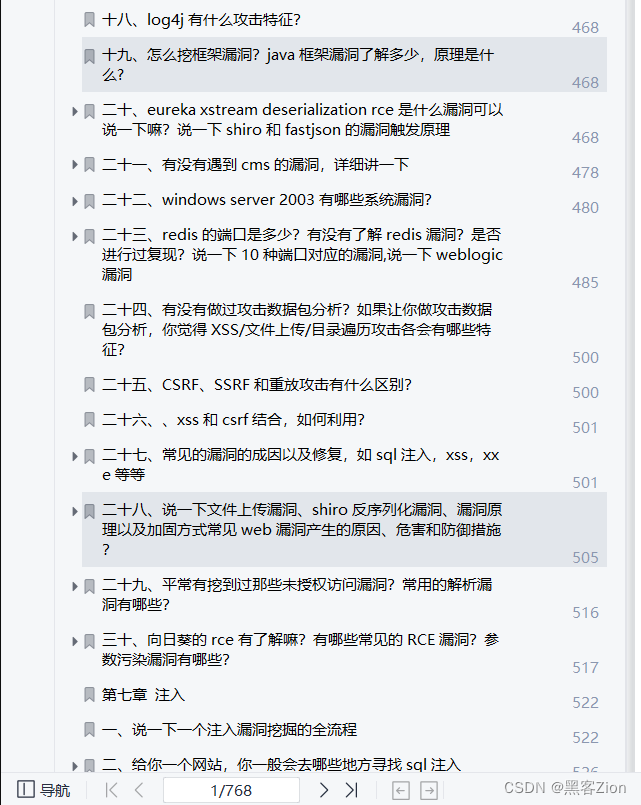
Summary of content: Including intranet, operating system, protocol, penetration testing, security service, vulnerability, injection, XSS, CSRF, SSRF, file upload, file download, file inclusion, XXE, logical vulnerability, tools, SQLmap, NMAP, BP, MSF…
Due to limited space, only part of the information is displayed. You need to click the link below to obtain it
CSDN gift package: "Hacker & Network Security Introduction & Advanced Learning Resource Package" Share for free