Install and use wireshark on mac
1 Introduction
In our daily development process, when we encounter difficult problems, we inevitably check the specific network request situation. At this time, we need to use packet capture tools. The more famous packet capture tools are: wireshark and fildder. I mainly introduce wireshark here.
2 installation
Take mac installation as an example.
- Go to the official website to download the corresponding mac version. (Pay attention to whether your chip is Intel or Apple)
https://www.wireshark.org/download.html- After downloading, just double-click the .dmg and drag to install.
- After successful installation, go to the application and double-click the wireshark icon.
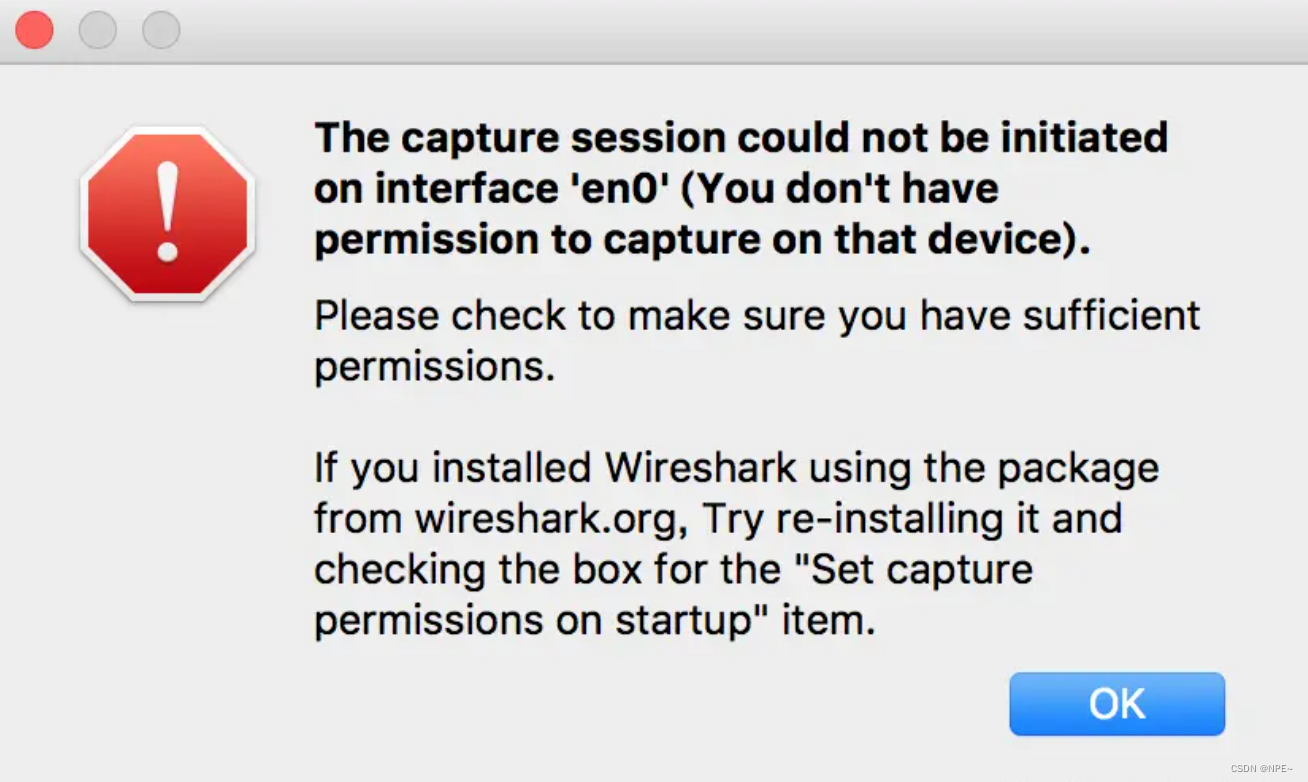
- If you find that wireshark reports an error after double-clicking:
It means that wireshark does not have the corresponding network card permissions to capture the traffic corresponding to the network card.
Execute the following command, and then reopen wireshark.sudo chmod 777 /dev/bpf*
3 use
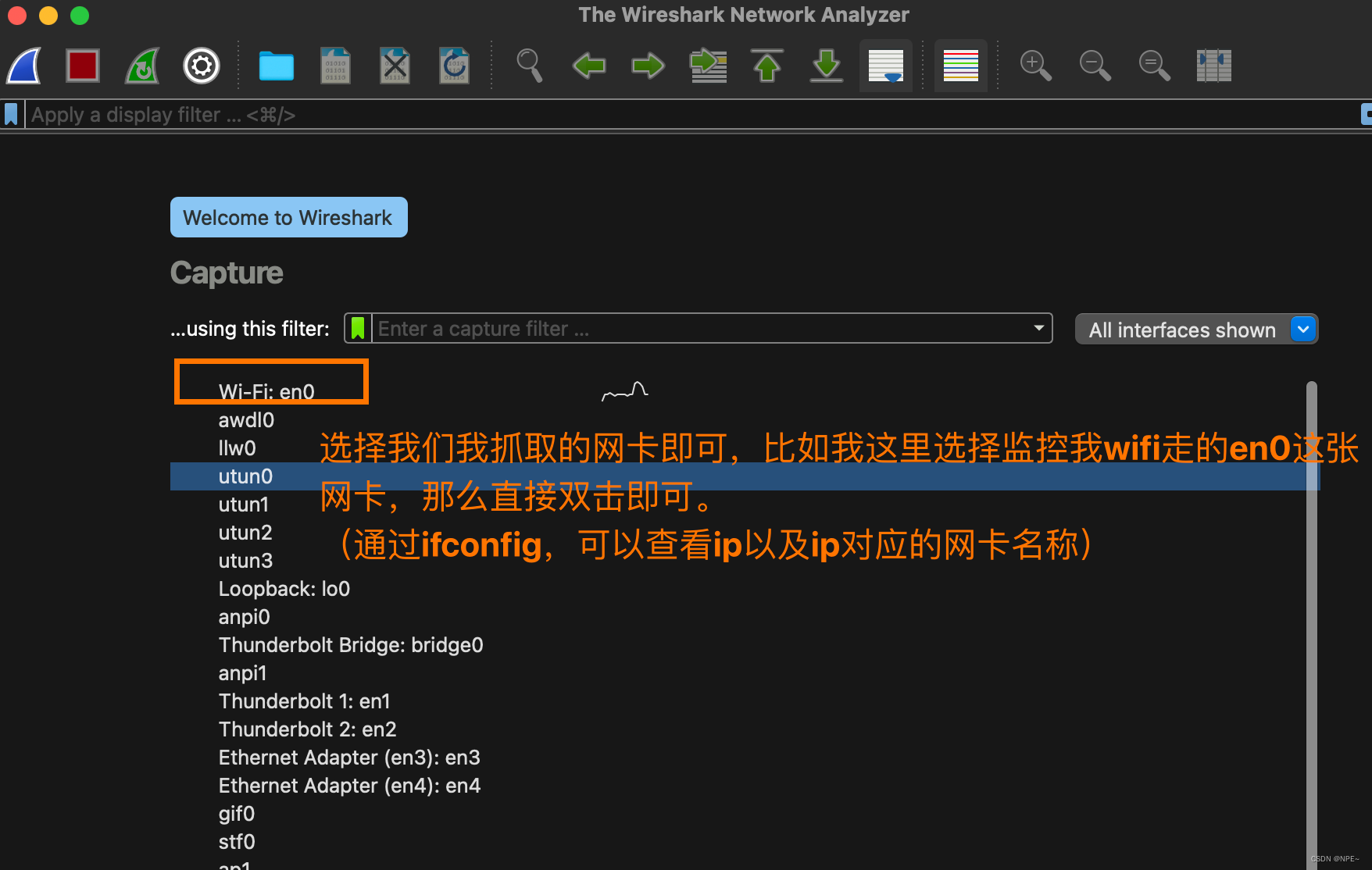
3.1 Determine the network card
If our computer has multiple network cards, how do we determine which network card we should monitor?
- Method 1: Use ifconfig to check the network card name to which the IP belongs, and then click Monitor on wireshark.
- Method 2: Move the mouse to the network card name displayed on the wireshark page. Wireshark will automatically display the ip address, and then select the network card where the ip we want to monitor is located.
3.2 Filter IP (source or destination)
①ip.src eq 192.168.1.145 or ip.dst eq 192.168.1.145
Or ip.addr eq 192.168.1.145
- You can also use ip.addr == 192.168.1.145 directly
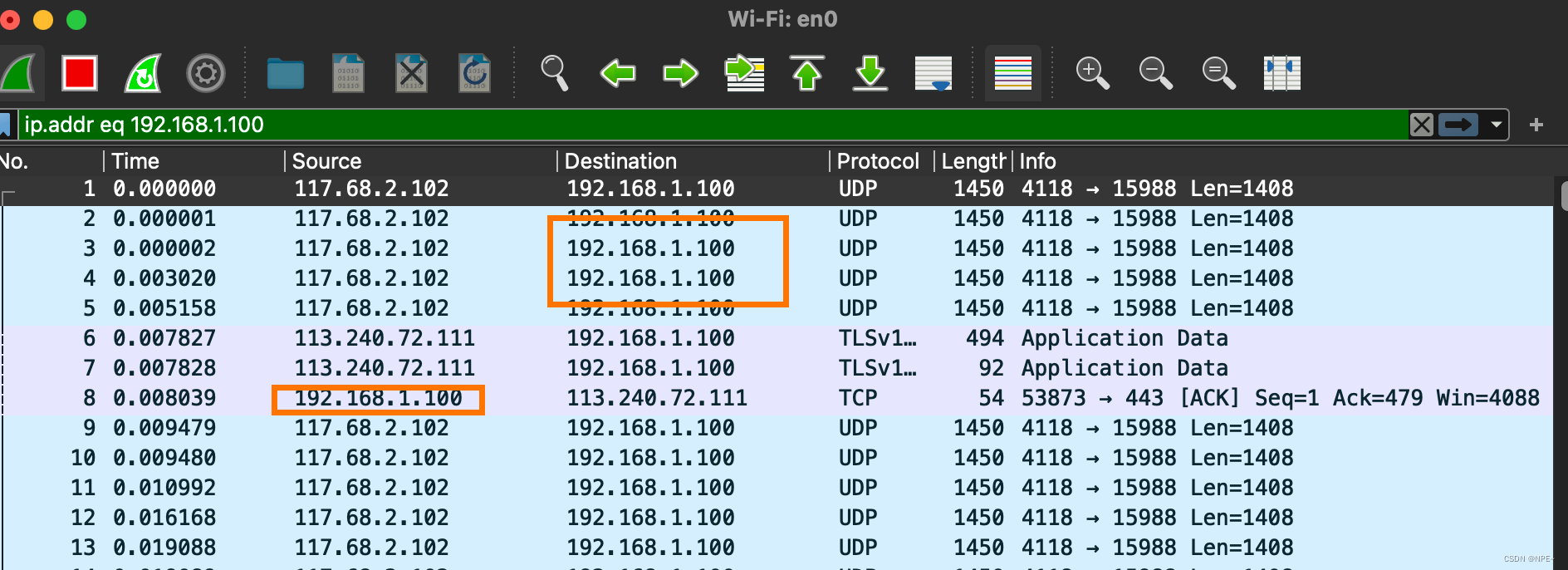
Tip: In the Filter edit box, when entering filtering rules, if the syntax is incorrect, the box will be red, and if it is correct, it will be green.
②ip.src == 192.168.1.145
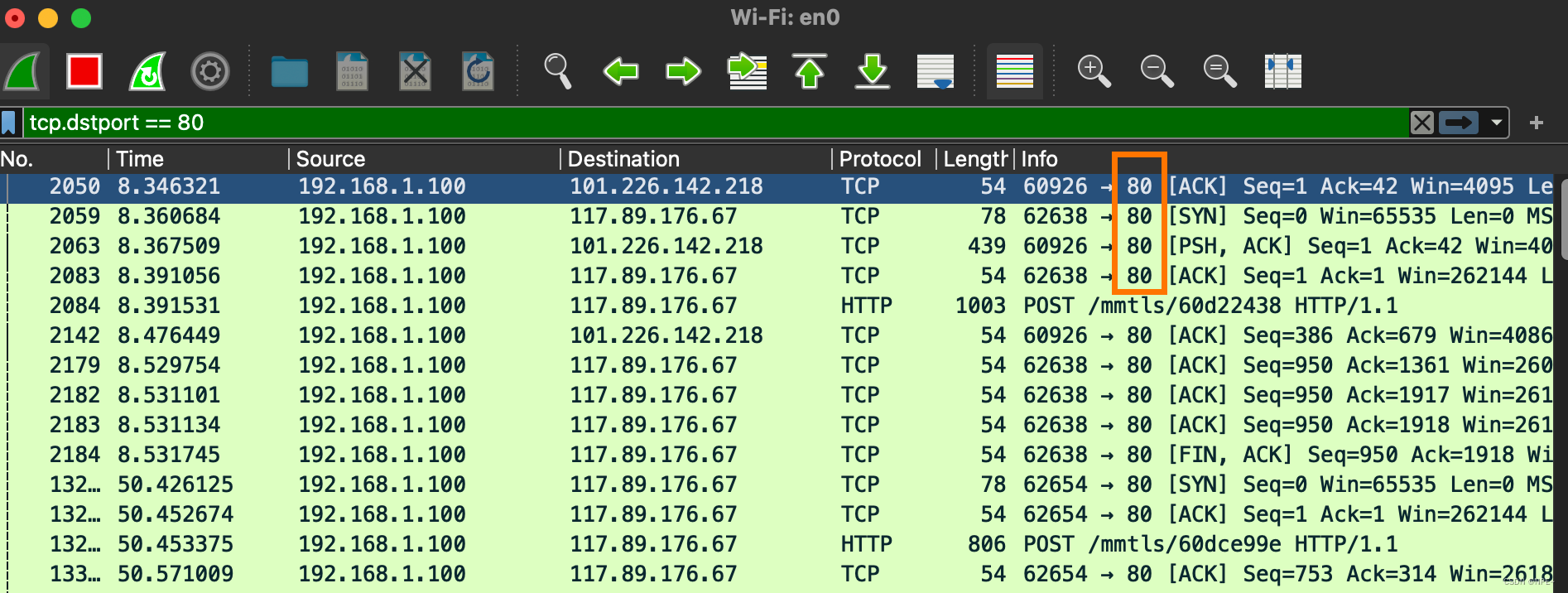
3.3 Filter port
①tcp.port == 80 (regardless of source or destination)
tcp.port eq 80 // Display regardless of whether the port is source or destination
tcp.port == 80
tcp.port eq 2722
tcp.port eq 80 or udp.port eq 80
tcp.dstport == 80 // Only display the target port 80 of the tcp protocol
tcp.srcport == 80 // Only display the source port 80 of the tcp protocol
②tcp.dstport == 80 (only displays the target port of the tcp protocol is 80)
③udp.port == 1500
④tcp.port >= 1 and tcp.port <= 80
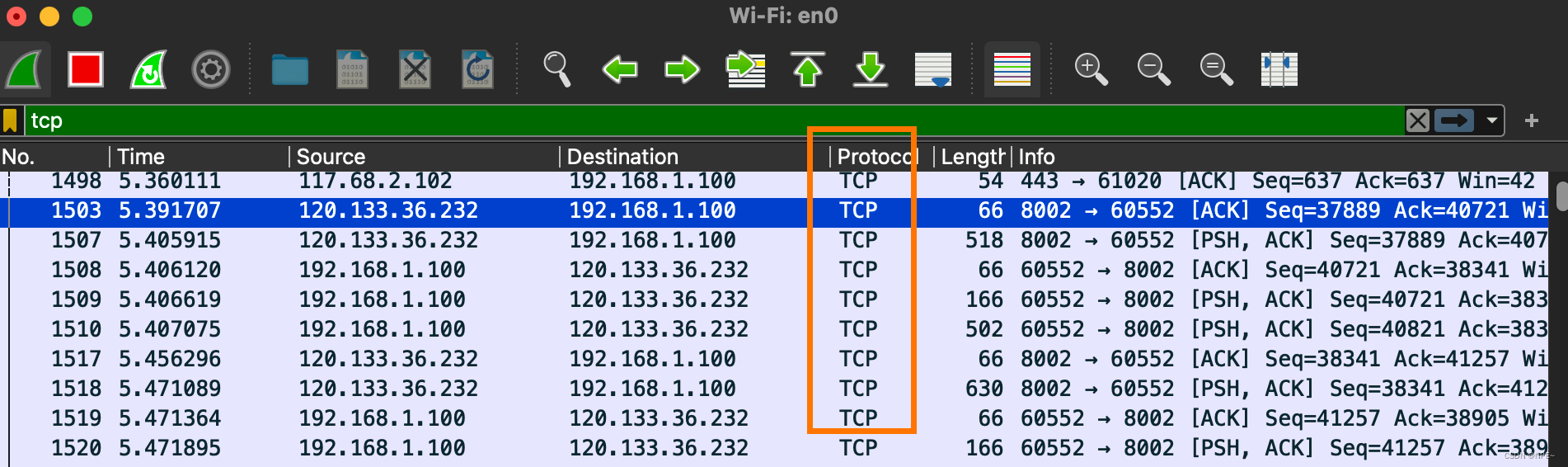
3.4 Filtering protocols
例子:
tcp
udp
smb
arp
icmp
http
smtp
ftp
dns
msnms
ip
ssl
oicq
bootp
等等
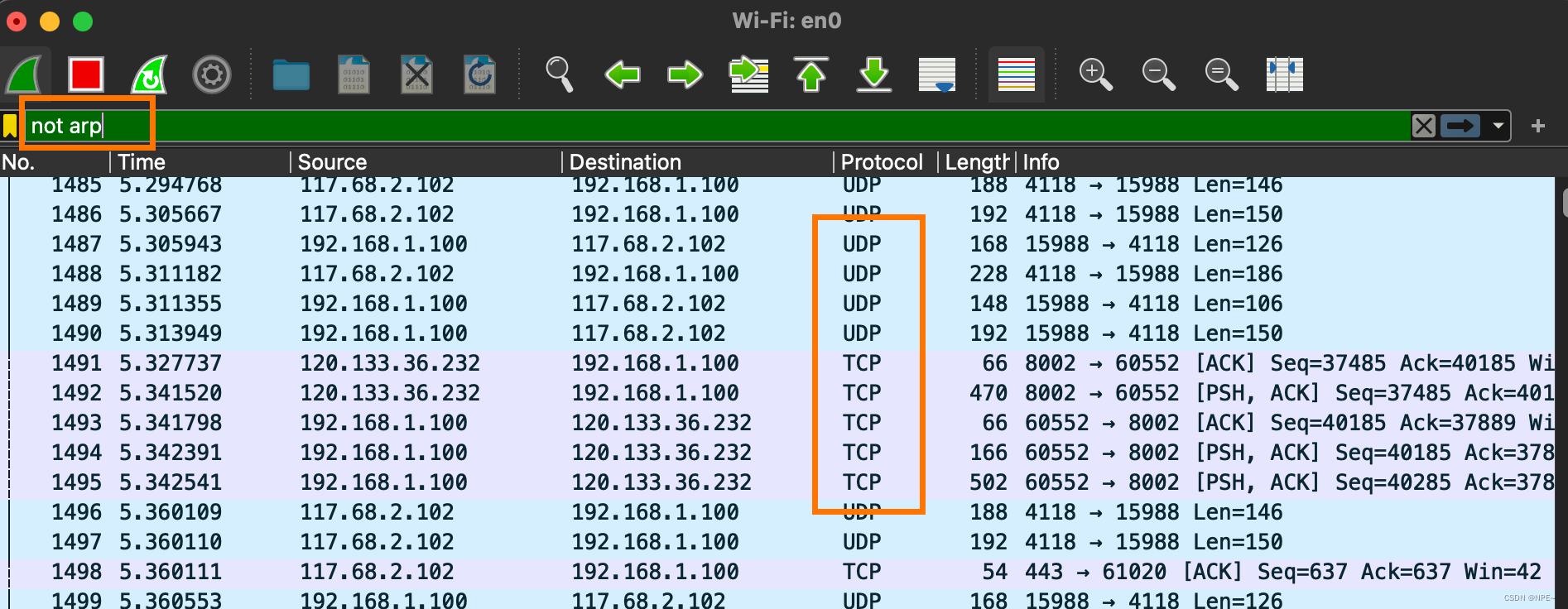
①tcp (screening tcp protocol)
②not arp (exclude arp protocol)
or
!arp
3.5 Filter MAC
①eth.dst == A0:00:00:04:C5:84 filter target mac
②eth.src == A0:00:00:04:C5:84 filter source mac
eth.src eq A0:00:00:04:C5:84 // Filter source mac
eth.dst == A0:00:00:04:C5:84
eth.dst == A0-00-00-04-C5-84
eth.addr eq A0:00:00:04:C5:84 / / Filter source MAC and destination MAC are both equal to A0:00:00:04:C5:84
less than less than< lt
less than or equal to le is not equal to ne is greater than or equal to ge is greater than gt
is equal to eq
3.6 Packet length filtering
①udp.length == 26 (udp itself has a fixed length of 8 + 26 after the data packet)
This length refers to the fixed length of udp itself (8) plus the sum of the data packets below udp
②tcp.len >= 7 refers to the ip data packet (not including tcp itself)
③ip.len == 94 Except for Ethernet fixed length 14, everything else is considered ip.len
That is: from the ip itself to the end
④frame.len == 119 The entire data packet length, from the beginning to the end of eth
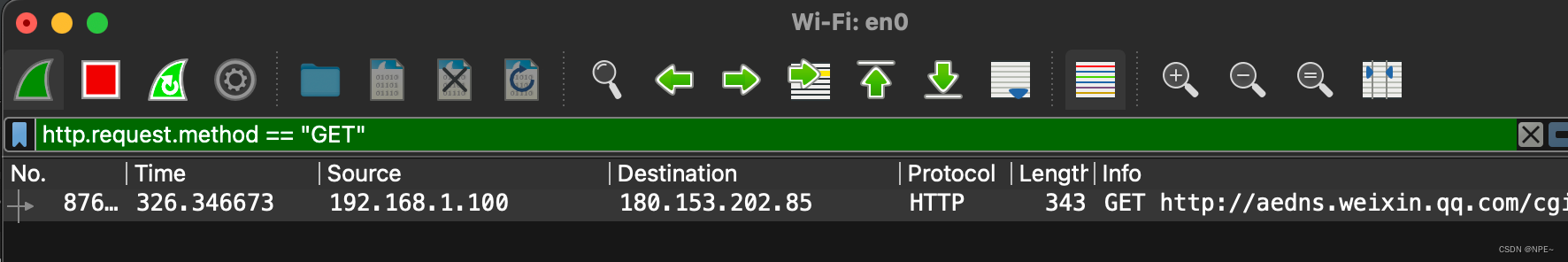
3.7 http mode filtering
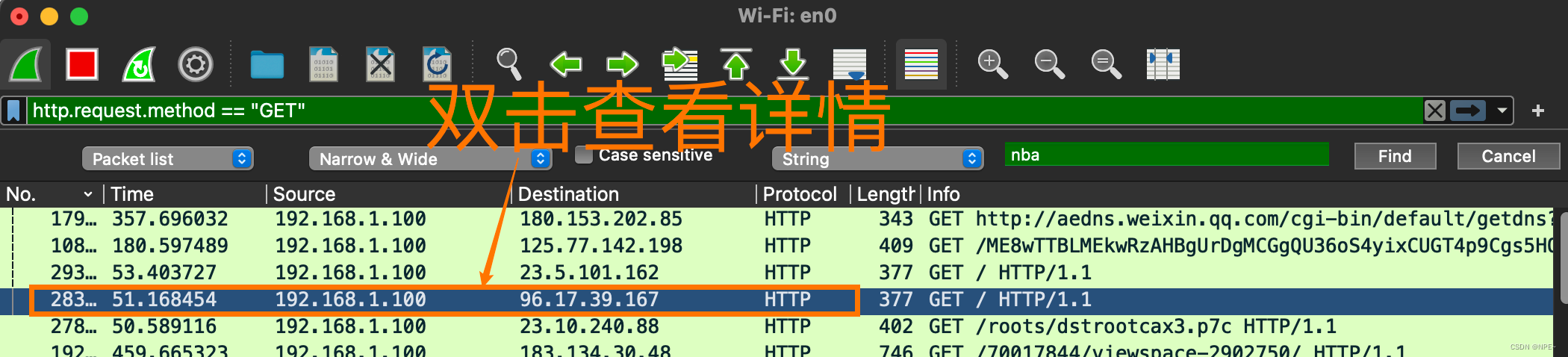
①http.request.method == “GET”
http.request.method == “POST”
②http.request.uri == “/img/demo.png”
③http contains “GET”
④http contains “HTTP/1.” (case sensitive)
Note: case sensitive
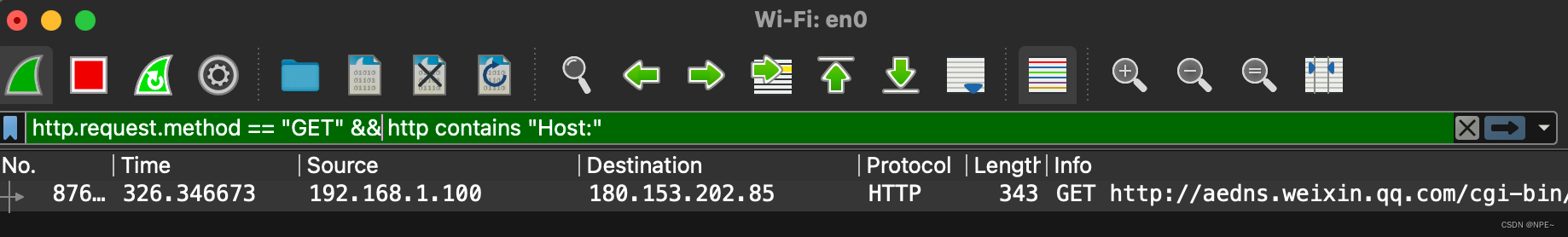
⑤GET package
http.request.method == “GET” && http contains "Host: "
http.request.method == “GET” && http contains "User-Agent: "
⑥POST package
http.request.method == “POST” && http contains "Host: "
http.request.method == "POST" and http contains "Host: " can also be used
http.request.method == “POST” && http contains "User-Agent: "
⑦Response package
http contains “HTTP/1.1 200 OK” && http contains "Content-Type: "
http contains “HTTP/1.0 200 OK” && http contains "Content-Type: "
3.8 TCP parameter filtering
①tcp.flags displays packets containing TCP flags
②tcp.flags.syn == 0x02 displays packets containing the TCP SYN flag
③tcp.window_size == 0 && tcp.flags.reset != 1
3.9 Packet content filtering
①tcp[20:8] means starting from 20, taking 8 characters
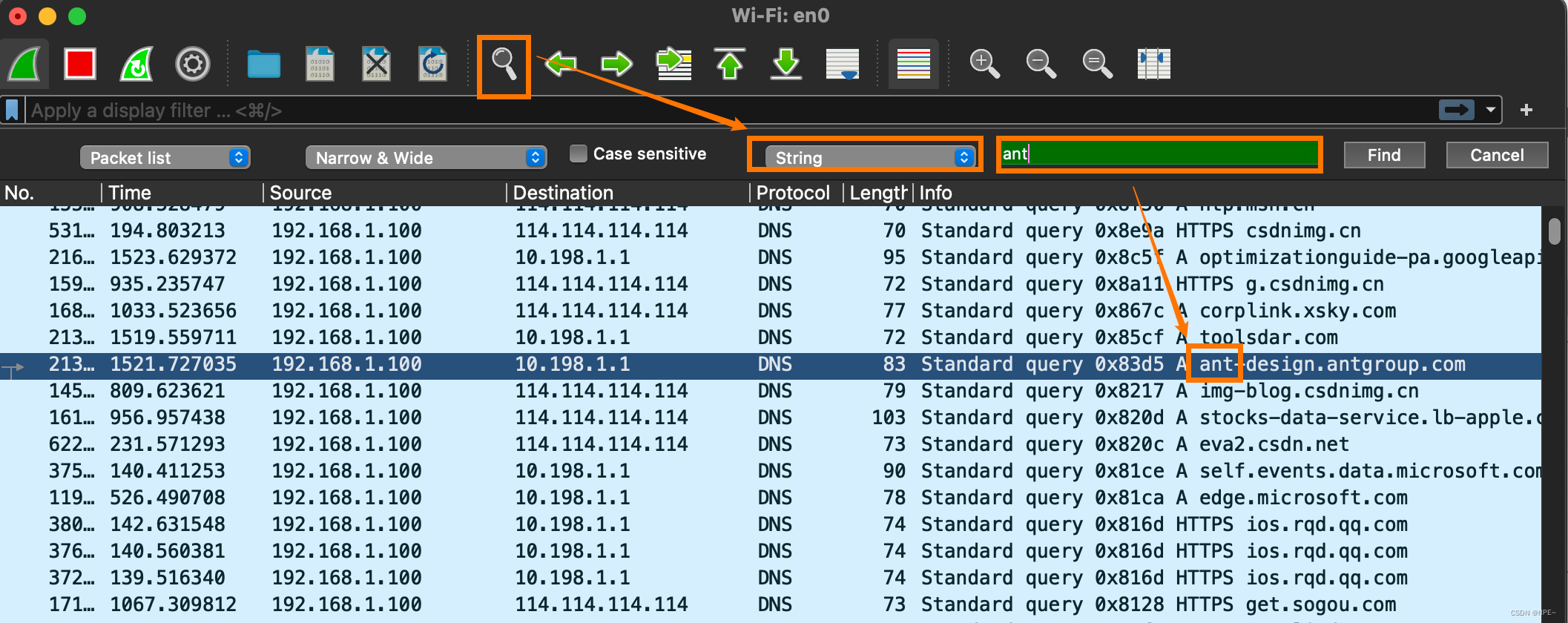
②Operation through the page
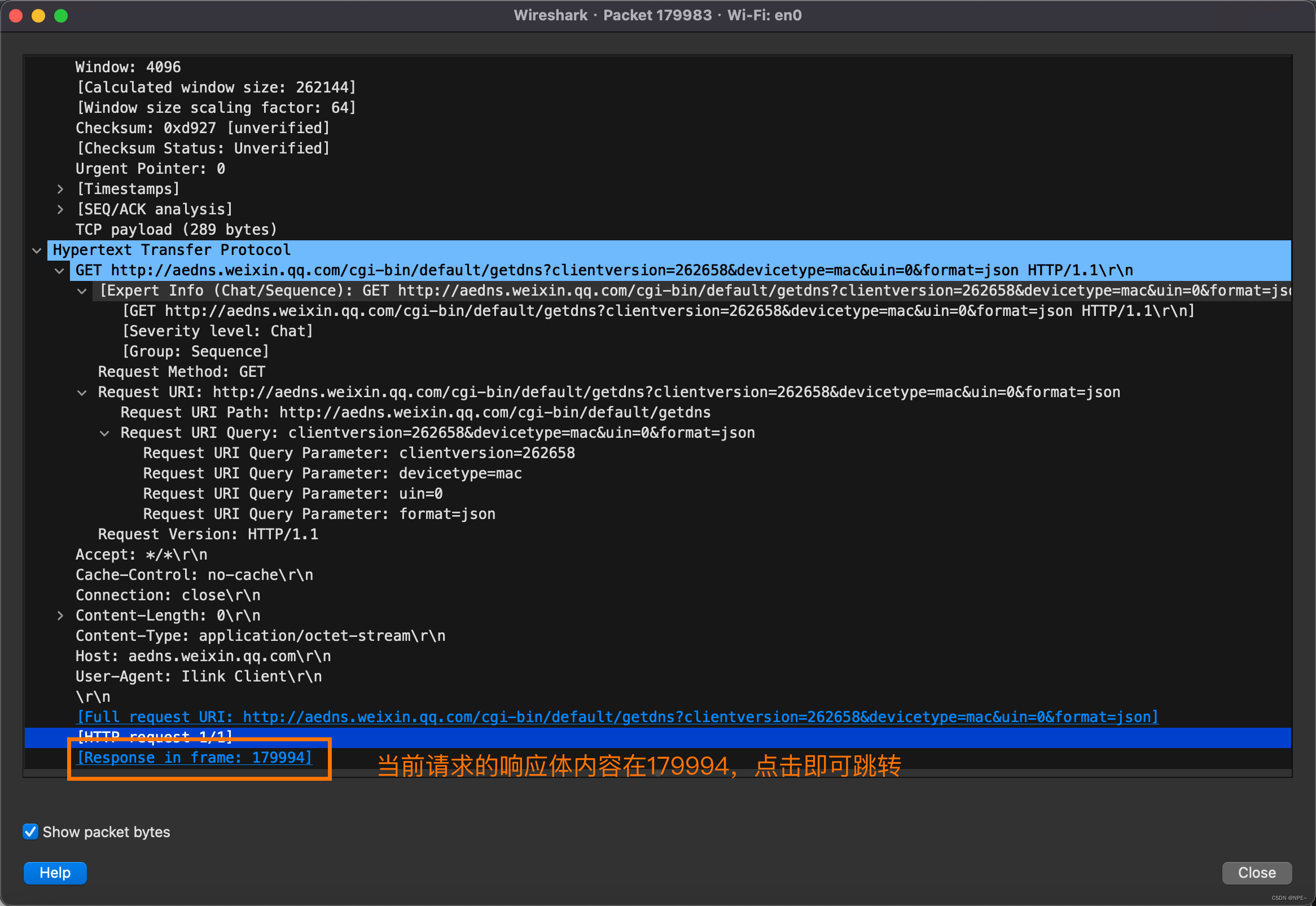
4 View details
Double-click to view details:
The details will display the request body, request headers, etc., including the response link address of the request.
Reference text:
https://blog.csdn.net/wojiaopanpan/article/details/69944970