foreword
The author was once very confused. After I chose to get started with network security, I picked up and picked up everywhere. I learned a little about the front-end and back-end communication protocols, but in the end I found that I didn’t learn anything well... I finally didn’t know how to go further.
I believe this is also a common problem encountered by many people who are beginners in network security. In this article, the author wants to share some routes that have been sorted out to help friends who are beginners in network security avoid detours.
This article will mention study notes, roadmap and interview materials. If you are still in the beginner stage, don’t be too anxious. You can use this article as a roadmap for learning and move in this direction in the future Just work hard.
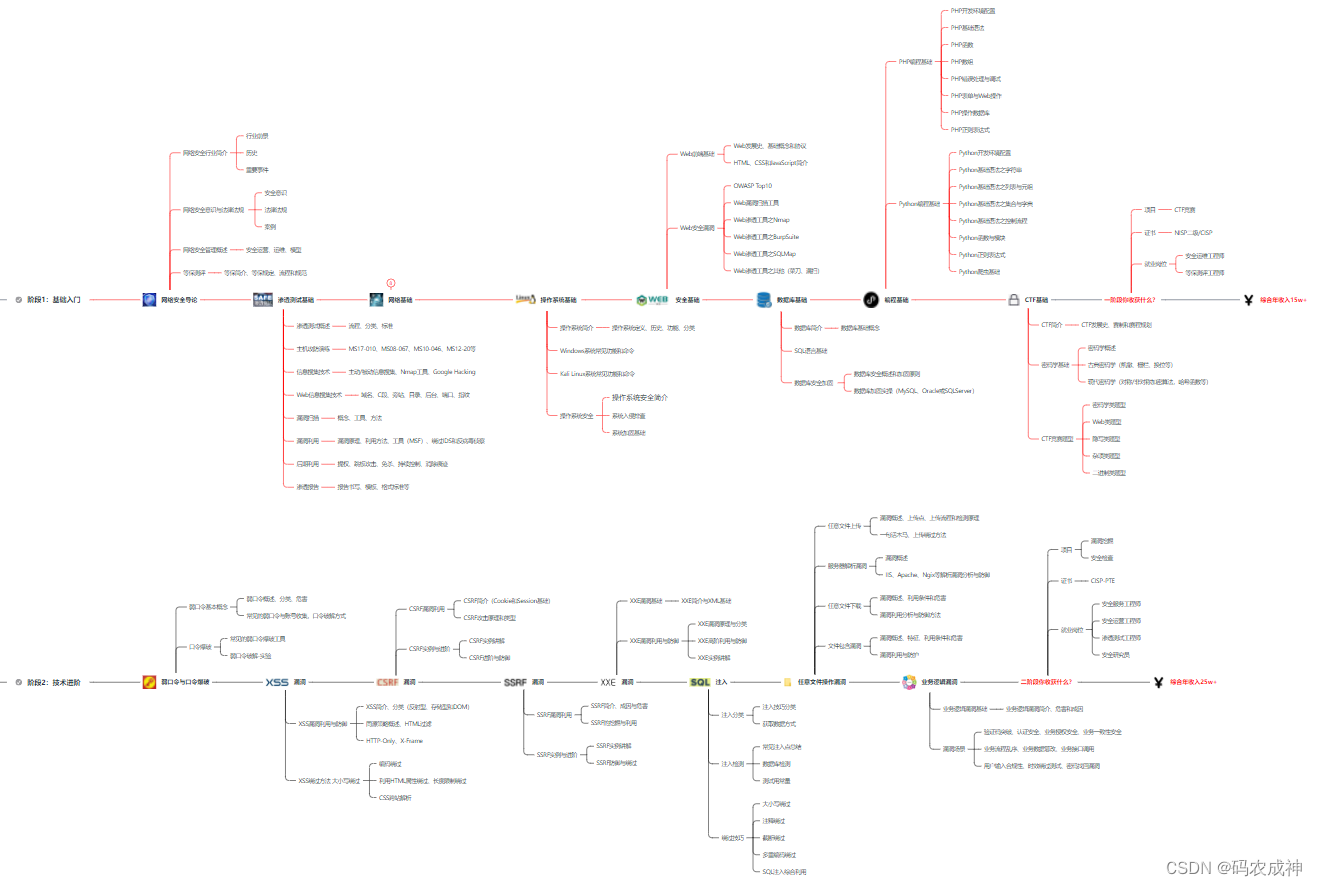
Cyber Security Learning Path
Before learning, we need to have an efficient network security learning plan, which can help us avoid many detours, get started and get employed quickly!
The following summarizes a set of learning routes suitable for zero-basic cybersecurity. It is suitable for both fresh graduates and career changers. After completing the study, the minimum guarantee is 6k! Even if you have a poor background, if you can take advantage of the good development momentum of Internet security and continue to learn, it is not impossible to switch to a big company in the future and get a million annual salary!
【Click here to get the information first and then watch~】
Junior Network Worker
1. Theoretical knowledge of network security (2 days)
① Understand the relevant background and prospects of the industry, and determine the development direction.
②Learn laws and regulations related to network security.
③The concept of network security operation.
④Multiple guarantee introduction, guarantee regulations, procedures and norms. (Very important)
2. Penetration testing basics (one week)
①Penetration testing process, classification, standard
②Information collection technology: active/passive information collection, Nmap tool, Google Hacking
③Vulnerability scanning, vulnerability utilization, principle, utilization method, tool (MSF), bypassing IDS and anti-virus
reconnaissance④ Host attack and defense drills: MS17-010, MS08-067, MS10-046, MS12-20, etc.
3. Basic operating system (one week)
① Common functions and commands of Windows system
② Common functions and commands of Kali Linux system
③ Operating system security (system intrusion troubleshooting/system reinforcement basis)
4. Basics of computer network (one week)
①Computer network foundation, protocol and architecture
②Network communication principle, OSI model, data forwarding process
③Common protocol analysis (HTTP, TCP/IP, ARP, etc.)
④Network attack technology and network security defense technology
⑤Web vulnerability principle and defense: active/ Passive attack, DDOS attack, CVE vulnerability recurrence
5. Basic database operations (2 days)
①Database foundation
②SQL language foundation
③Database security reinforcement
6. Web penetration (1 week)
①Introduction to HTML, CSS and JavaScript
②OWASP Top10
③Web vulnerability scanning tools
④Web penetration tools: Nmap, BurpSuite, SQLMap, others (chopper, missed scan, etc.)

Congratulations, if you learn this, you can basically work in a network security-related job, such as penetration testing, web penetration, security services, security analysis and other positions; if you learn the security module well, you can also work as a security engineer. Salary range 6k-15k
So far, about a month. You've become a "script kiddie". So do you still want to explore further?
[ "Script Kiddie" growth and advanced resource collection ]
7. Script programming (beginner/intermediate/advanced)
In the field of network security. Programming ability is the essential difference between "script kiddies" and real hackers . In the actual penetration testing process, in the face of a complex and changeable network environment, when the common tools cannot meet the actual needs, it is often necessary to expand the existing tools, or write tools and automated scripts that meet our requirements. Some programming ability is required. In the CTF competition where every second counts, if you want to efficiently use self-made scripting tools to achieve various purposes, you need to have programming skills.
For a zero-based entry, it is recommended to choose one of the scripting languages Python/PHP/Go/Java, and learn programming for common libraries; build a development environment and choose an IDE, Wamp and XAMPP are recommended for the PHP environment, and Sublime is strongly recommended for the IDE; Python programming learning , the learning content includes: common libraries such as grammar, regularization, files, network, multi-threading, etc., "Python Core Programming" is recommended, do not read it; ·Use Python to write vulnerability exploits, and then write a simple web crawler; ·PHP basic syntax Learn and write a simple blog system; Familiar with MVC architecture, and try to learn a PHP framework or Python framework (optional); Understand Bootstrap layout or CSS.
8. Super Network Worker
This part of the content is still relatively far away for students with zero foundation, so I won’t go into details, and post a general route. Interested children's shoes can be studied, and if you don't know where to go, you can [click here] add me to fuel consumption, and learn and communicate with me.
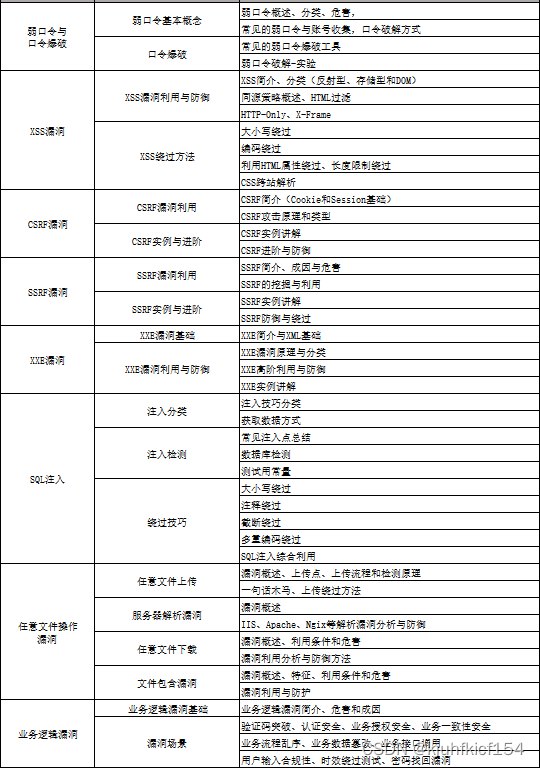
Network security engineer enterprise-level learning route
If the picture is too large and cannot be seen clearly due to the compression of the platform, you can [click here] add me to send it to you, and everyone can learn and communicate together.
Some video tutorials that I bought myself, and other platforms can’t get free prostitutes:

If you need it, you can scan the card below and add me to send it to you (all are shared for free), and everyone can learn and communicate together.

epilogue
The network security industry is like a river and lake, where people of all colors gather. Compared with many decent families with solid foundations in European and American countries (understand encryption, know how to protect, can dig holes, and are good at engineering), our talents are more heretics (many white hats may not be convinced), so in the future Talent training and In terms of construction, it is necessary to adjust the structure and encourage more people to do "positive" "system and construction" that combines "business" and "data" and "automation" in order to quench the thirst for talents and truly serve the society in an all-round way. Internet provides security.
Special statement:
This tutorial is purely technical sharing! The purpose of this book is by no means to provide and technical support for those with bad motives! Nor does it assume joint and several liability arising from the misuse of technology! The purpose of this book is to maximize everyone's attention to network security and take corresponding security measures to reduce economic losses caused by network security! ! !