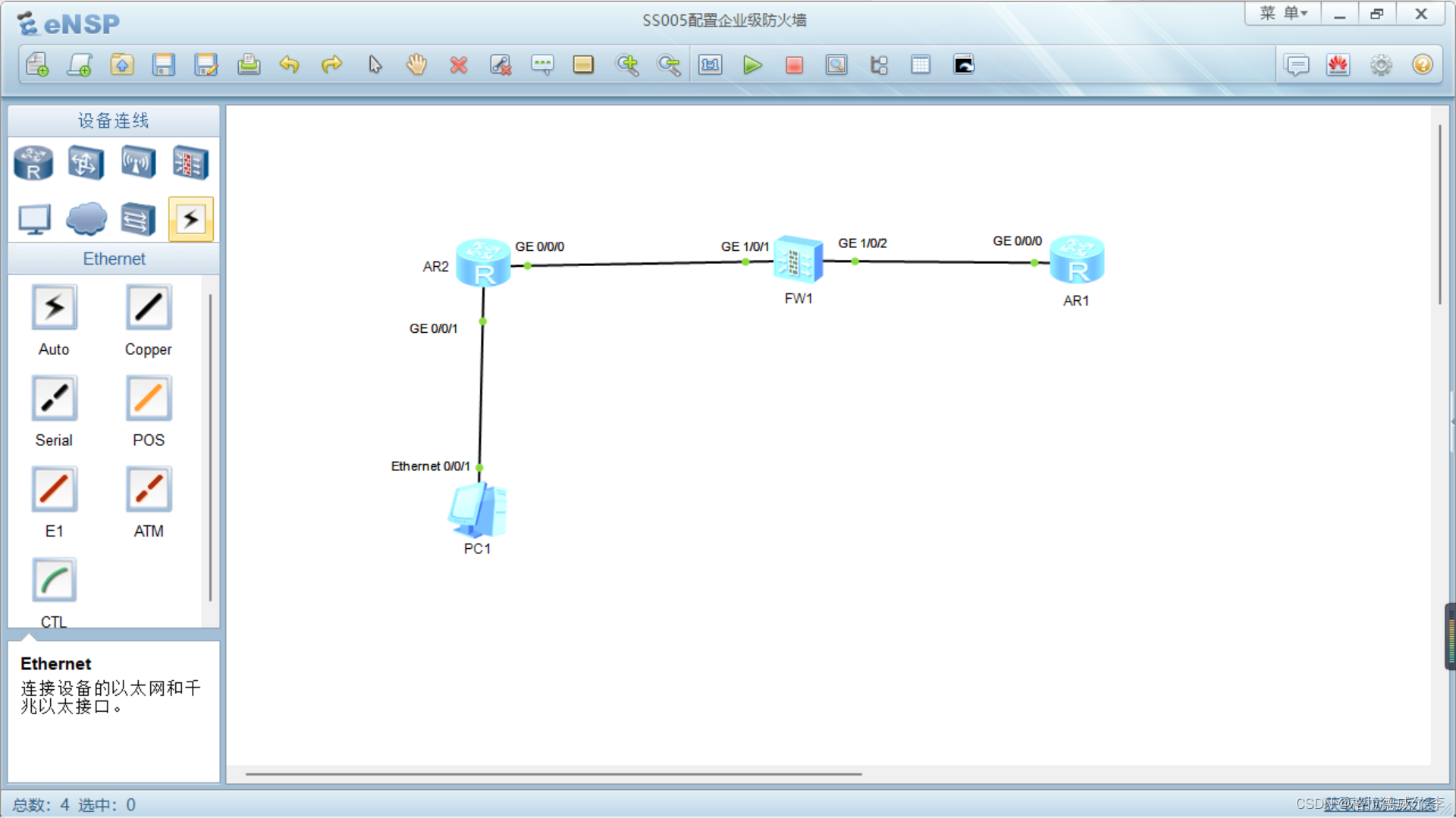
Topology
Equipment: a terminal PC, two routers, and a firewall
Except for the firewall, the operation of other equipment has been done before.
Firewall related configuration
Firewall Security Policy
Add the interface to the security zone
Several security domains of the firewall:
trust zone: intranet, own people.
Untrusted area: external network, outsider
DMZ area: intermediate area, between the trusted area and the untrusted area.
Trust zone:
fairwall zone trust
add int g1/0/1
Command explanation:
firewall zone trust
enters the trust zone
add int g1/0/1
adds interface g1/0/1 to the trust zone
untrusted zone
firewall zone untrust
add int g1/0/2
Command explanation:
firewall zone untrust
enters the untrusted zone
add int g1/0/2
adds the interface to the untrusted zone
Do release strategy
security-policy
rule name shangwang
course-zone trust
destination-zone untrust
action permit
security-policy
Enter the security policy
rule name shangwang
Create a new security policy called shangwang
source-zone trust
from the trusted zone
destination-zone untrust
go to the untrusted zone
action permit
to allow action
The internal network host is a private network ip, and the private network ip cannot access the external network
Use nat network address translation, network address translation technology, to convert private network ip to public network ip
nat-policy
rule name shangwang
course-zone trust
destination-zone untrust
action course-nat easy-ip
Command explanation:
nat-policy
enters nat policy
rule name shangwang
to create a new nat policy called shangwang
source-zone trust
from trusted zone
destination-zone untrust
to untrusted zone
action source-nat easy-ip
to do address translation and convert to export ip , easy-ip can automatically convert to the address of the outgoing interface of the device when performing address translation.
backhaul routing
return journey
In actual work, it is particularly easy to overlook this point
ip route-static 192.168.1.0 24 10.10.10.1