The transport layer is located in the fourth layer of the five-layer protocol. The transport layer provides general services to the upper application layer. The general purpose means that multiple application processes can use the same transport layer protocol. The transport layer is responsible for providing general data transmission services for the communication between two hosts. The transport layer has the functions of demultiplexing and multiplexing. Multiplexing means that multiple applications use the same transport layer service. Deliver information from the network layer to different applications
There are mainly two protocols at the transport layer:
- TCP: Transmission Control Protocol, which provides a connection-oriented and reliable data transmission protocol
- UDP: User Datagram Protocol, which provides a connectionless, best-effort data transmission service, but does not guarantee reliability
This article focuses on the two protocols UDP and TCP
One, UDP
The full name of 用户数据包协议(User Datagram Protocol)UDP is , UDP provides a way for applications to send encapsulated IP data packets without establishing a connection. UDP only adds a few functions to IP datagrams, namely demultiplexing, multiplexing, and errors. The detection function, although it has error detection, it has no recovery capability and retransmission mechanism, so it is unreliable
1.1 Features of UDP
UDP是无连接的, That is, there is no need to establish a connection before sending data, and there is no connection release after sending data, which reduces the overhead of establishing and releasing the connectionUDP尽最大努力交付,是没有连接状态的, That is, reliable delivery is not guaranteed, so the host does not need to maintain a complex stateUDP是面向报文的, UDP is message-oriented, that is, it directly encapsulates the messages from the application layer, and the packet header overhead is small速度快Based on the above characteristics, the speed of UDP is very fast, and the purpose is to ensure real-time
Two, TCP
As a transport layer protocol, TCP is considered more than UDP. TCP is a connection-oriented protocol that provides reliable transmission, while connection-oriented TCP requires three handshake and four waves to confirm and release the connection. To provide reliable transmission, there must be sliding The window mechanism is guaranteed by the serial number confirmation number, capable of flow control and congestion control, etc.
2.1 Features of TCP
TCP是面向连接的, Which means that the connection is established and released every time you communicateTCP提供可靠传输, Data transmitted via TCP, no error, no loss, no duplicationTCP提供全双工通信, TCP allows the application processes of both parties to communicate at any time. Both the receiver and sender of TCP are set up with a buffer to temporarily store the received or sent data.面向字节流Although the data from the application layer is a data block, TCP only treats these data as a series of unstructured byte streams
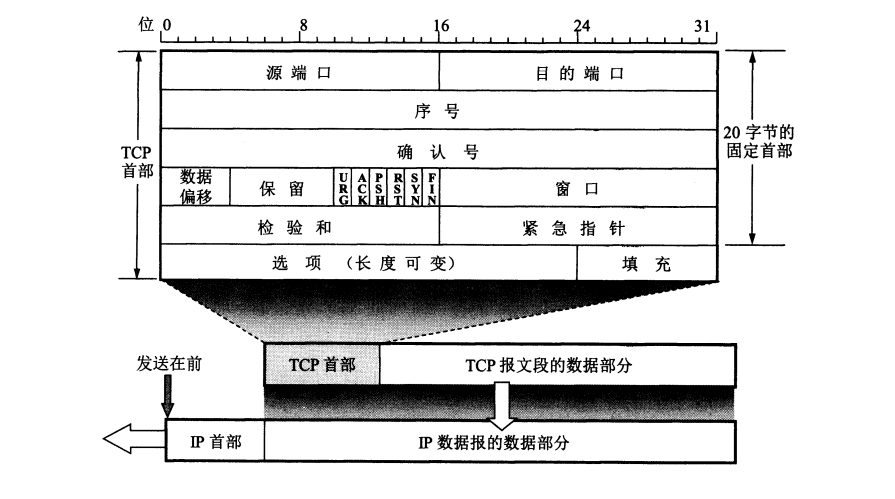
2.2 The first message format of TCP
TCP is byte-oriented, but the specific data sent is still a message segment, and the role of each field in the header of the message segment reflects all the functions of TCP. The following introduces some of the more commonly used message data segments
-
Source port and destination port: The source port and the destination port each occupies 2 bytes. These two fields are used for demultiplexing and multiplexing to mark the port number of the process, which can be packaged and unpackaged when receiving or sending
-
Sequence number: The sequence number occupies 4 bytes, a total of 2^32 sequence numbers. When the sequence number is used up, it can be numbered from 0. The byte stream sent in each TCP connection must be numbered in sequence. The entire byte stream is The starting number must be determined when the connection is established
-
Confirmation number: The confirmation number occupies 4 bytes. It is the sequence number of the first data byte expected to receive the next message segment from the other party. That is to say, if the confirmation number is N, it means that the data before N-1 is all Confirmed receipt
-
Acknowledge ACK: The field is valid only when ACK=1. TCP stipulates that ACK=1 must be set after the connection is established
-
Synchronous SYN: Used for synchronization when the connection is established. When SYN=1 and ACK=0, it indicates that this is a connection request segment. If the other party agrees to establish a connection, it will send SYN=1 and ACK in the response datagram. =1
-
Terminate FIN: used to release a connection, when FIN=1, it indicates that the connection needs to be released
-
Window: occupies 2 bytes and refers to the receiving window of the receiver. The window value tells the sender: the maximum amount of data that can be sent this time, so the window is used as the basis for the sender's sending window
2.3 Principle of Reliable Transmission-ARQ Protocol
自动重传请求(ARQ)It is the error correction protocol of the data link layer and the transport layer in the OSI model. Through the two mechanisms of acknowledgment and timeout, reliable information transmission can be realized on the basis of unreliable services. ARQ includes stop-waiting ARQ and continuous ARQ protocols
Stop waiting for ARQ protocol
1) No errors
Send and send the data packet, the receiver receives it within the specified time, and replies to the confirmation, and sends and sends the next data packet again
2) Something went wrong
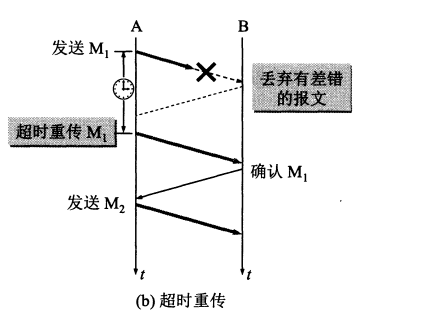
When B encounters an error when receiving M1, B does not notify A that it has received an error message. It is also possible that M1 is lost during transmission, and B will not send any messages. This is ARQ stipulates that as long as A does not receive the confirmation message from B within a certain period of time, a timeout retransmission is required.
To achieve timeout retransmission, the sender needs to set a timeout retransmission timer, and the time of the timeout retransmission timer should be longer than the round-trip time of the data packet. The sender also needs to back up the sent packets. In order to retransmit, and each data packet needs to be numbered, so as to confirm which segment is not sent correctly
3) Confirm lost and confirmed late
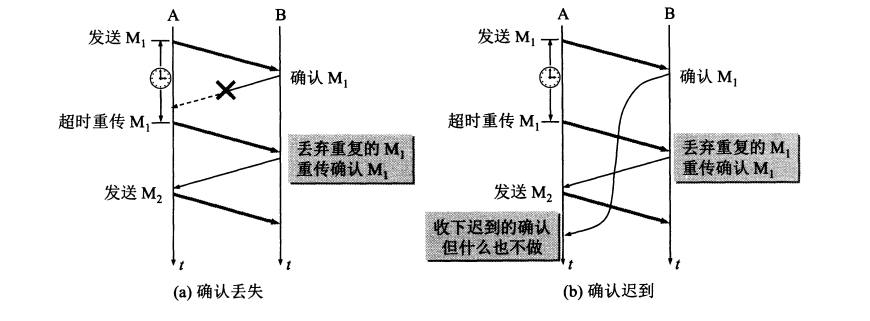
- Confirmation lost: The confirmation message was lost during transmission. When A sends M1 to B, B receives M1 and sends an acknowledgment message, but the acknowledgment message is lost during the transmission. When the timeout of the retransmission timer expires, A resends M1, and B should receive it Do: ①Receive but discard M1, do not deliver to the upper layer ②Resend the confirmation message, not because the confirmation of M1 has been sent will not be sent
- Confirmation is late: the confirmation message is stuck during transmission. Similarly, when A does not receive the confirmation message from B within the time allowed by the timeout retransmission timer, it needs to retransmit to M1. After the same B received Need to discard M1 and resend the confirmation message, and A may receive the stranded confirmation message at this time, and then discard it directly
Continuous ARQ protocol
The continuous ARQ protocol can provide channel utilization, and the sending and sending maintains a sending window of 5, for example, which means that the sender can send 5 consecutive datagrams at once without waiting for the other party's confirmation. The receiver adopts the method of accumulative confirmation, and only needs to send the last sequence of confirmation messages, then the sender thinks that the receiver has received all the messages before the sequence number, such as sending and sending a message with a sequence number of 1-5 , And the receiver only needs to send an acknowledgment message with sequence number 5, and the sender thinks that the receiver correctly received the segment 1-5
The advantage of using the above method is that the channel utilization rate is high and it is easy to realize. The disadvantage is that it cannot reflect to the sender all the packet information that the receiver has correctly received. For example, the sender has sent 5 packets, and the receiver has lost the third packet. , Only the first two packets can be confirmed, and the sender has to retransmit all the next three packets. This is called Go-Back-N (back N)
2.4 Flow control and sliding window
To achieve a fast transmission speed, the joint efforts of the sender and the receiver should be required, but if the sender is too fast and the receiver is too late to receive, flow control is required, and flow control is achieved by sliding windows. It is the window field in the message format. The window field in the confirmation message sent by the receiver can be used to control the size of the sender's window, thereby affecting the sender's sending rate.
Join the sender and send an acknowledgment message with a window of 0 to the receiver, which tells the sender that no more data can be sent. Here we consider a situation. If the receiver's buffer can receive new data after a period of time has passed The sender sends a message with a window value of rwnd=100, but this message is lost, which causes the sender to wait for the receiver, causing a deadlock phenomenon. In order to solve this problem, TCP for each connection A continuous timer is set. As long as the sender receives a zero window notification, the timer will be started. When the timer expires, a probe message will be sent. Then the receiver will confirm and give the current window value. Caused a stalemate
2.5 Congestion control
Congestion control is to prevent excessive data from being injected into the network, so that routers or links in the network will not be overloaded. Congestion control is a global process involving all hosts, routers, and so on. On the contrary, what flow control needs to do is point-to-point control, and what flow control needs to do is to suppress the sending rate of the sender so that the receiver can come and receive
In order to control congestion, the TCP sender maintains a window variable of the congestion window (cwnd). The size of the congestion control window depends on the degree of network congestion and changes dynamically. The sender makes its own sending window the congestion window and the receiver. The smaller one of the receiving window
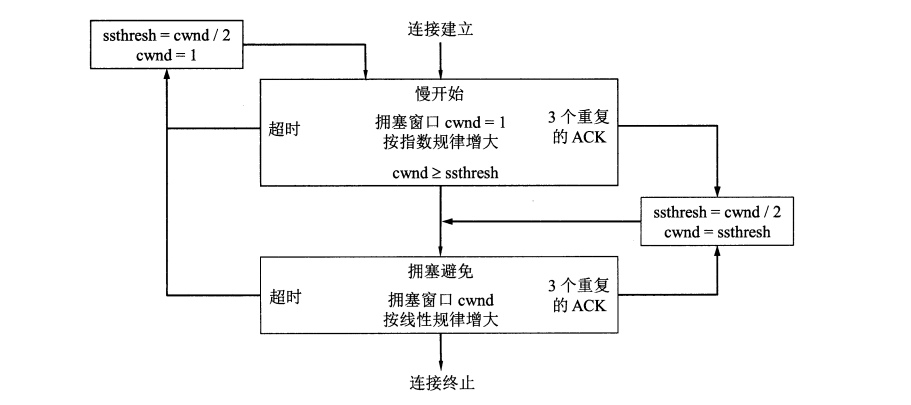
There are four algorithms for TCP congestion control, slow start, congestion avoidance, fast recovery and fast retransmission, which are introduced below in conjunction with the following figure
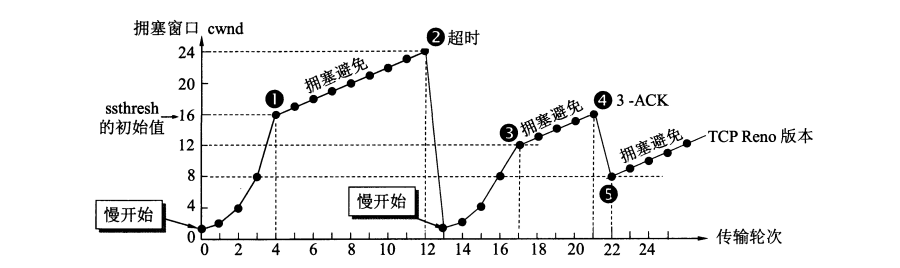
- Slow start: When the host starts to send data, it is not clear about the degree of congestion in the network. If a large amount of data is injected into the network at this time, it may cause congestion, so a slow start algorithm is adopted, from small to small. Largely increase the size of the window value. And set a ssthresh slow start threshold, and the window value will be doubled after each propagation round in the slow start phase
- Congestion avoidance: When the current window value reaches the slow start threshold, start to use the congestion avoidance algorithm. The idea of the congestion avoidance algorithm is to slowly increase the window value, and increase by 1 after each RTT time window, which is to increase according to a linear law. . According to the figure, when the window value reaches 24, a new situation occurs, and it has timed out. At this time, the sender judges that there is congestion, so the current window value cwnd=1, the full start threshold ssthresh=24/2=12, and the slow start is restarted. Algorithms and congestion control algorithms
- Fast retransmission and fast recovery: The fast retransmission algorithm requires the receiver not to carry out piggyback confirmation, but to confirm immediately. When the sender receives three confirmation messages in a row, the sender knows that a certain message is not sent If successful, the fast retransmission is used immediately to resend the lost data packet, and the fast recovery algorithm is performed at the same time to change the current window cwnd to half of the previous one.
The above flow chart is as follows:
2.6 Connection management-three-way handshake
It has been mentioned many times that TCP is connection-oriented, so connection establishment and release are needed. Let’s talk about the process of TCP connection establishment.
In the life cycle of a TCP connection establishment, there are a total of the following states:
LISTEN: Waiting for a connection from any remote TCPSYN-SEND: Waiting for a matching connection request after sending a connection requestSYN-RECEIVED: Indicates that the connection request has been received and it is waiting for the connection confirmation, which is the state of the second handshakeESTAB-LISHED: Indicates that the connection has been successfully created and data can be transferred
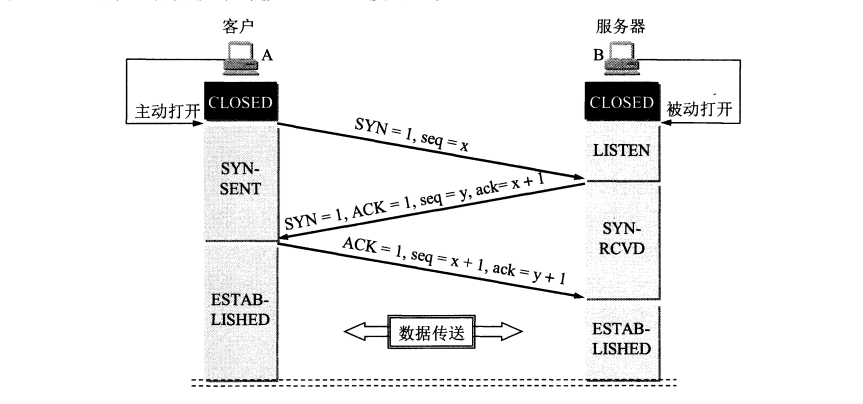
The above figure is a schematic diagram of a three-way handshake connection. TCP stipulates that when a client initiates a request for a connection, it cannot send data but consumes a serial number. Let's analyze the above process:
-
The client actively sends a connection request to the server. The header of the request is SYN=1 in the same part, and an initial sequence number seq is selected. The SYN segment is not allowed to carry data, and only consumes one sequence number. The client enters the
SYN-SENDstate -
After the server receives the client's request to initiate a connection, it needs to confirm the client's message. In the confirmation message segment, both SYN and ACK need to be set. At the same time, it sends a confirmation number and also chooses an initial sequence number for itself. The text segment also cannot carry data, it needs to consume a serial number, and the server enters at the same time
SYN-RECEIVED -
After the client receives the confirmation message, it also needs to give a confirmation connection message. The confirmation connection message finds the ACK=1 and the sequence number is x+1. This message can carry data and the client enters
ESTAB-LISHED -
The server also enters after receiving the confirmation message
ESTAB-LISHED
Analyze the process of the three-way handshake again. In fact, the process of establishing a connection request is to let the other party know their status first, that is, to make sure that the other party's sending and receiving are normal:
- The first handshake: the client can't confirm anything, the server confirms: the other party sends normally, and the receiver is normal
- The second handshake: the client confirms: receiving and sending are normal, the other sending and receiving are also normal, the server confirming: the other sending is normal, and the receiving is normal
- The third handshake: the client confirms: receiving and sending are normal, the other sending and receiving are also normal, the server confirming: receiving and sending are normal, the other sending and receiving are also normal
So it needs three handshake
Why send back SYN and ACK?
The SYN is sent back in the second handshake. The purpose is to tell the client that the message I received is indeed the message you sent and not someone else. The correctness of the communication parties must be that the messages sent to each other are correct, so the purpose of sending back ACK is also to prove that the channel between the two is correct.
2.7 Connection Management-Four Waves
There are the following states in a TCP connection close life cycle:
FIN-WAIT-1: Means to wait for the connection termination request from the remote TCP, or wait for the connection termination request sent previouslyFIN-WAIT-2:Indicate waiting for connection termination request from remote TCPCLOSE-WAIT: Indicates waiting for the connection termination request of the local userCLOSING: Represents waiting for the connection termination request confirmation from the remote TCPLAST-ACK: Indicates that it is waiting for the confirmation of the connection termination request previously sent to the remote TCPTIME-WAIT: Means to wait for enough time to ensure that the remote TCP receives its connection termination confirmation requestCLOSE: Indicates that the connection has been closed, no connection status

- The client application sends a request message segment to release the connection, and actively closes the connection. The header of the message segment FIN=1, does not contain data, where seq=u, and the client enters
FIN-WAIT-1 - After the server receives the connection release message from the client, it sends an acknowledgement response message, where ACK=1, generates its own serial number, and then the server host enters
CLOSE-WAIT - After the client receives the confirmation message from the server, it enters the
FIN-WAIT-2state and waits for the server to send a message segment for connection release. At this time, the connection from the client to the server has been released. - When the server host has no data to send, the server host sends a disconnect request segment where ACK=1, FIN=1, where seq is not necessarily v because data may be sent in the middle. After sending the request, the server will Into
LAST-ACK - After the client receives the connection disconnect request sent by the server, the client needs to make a response, and then enter the
TIME-WAITstate. At this time, the connection has not been closed, and the client will enter after the time 2MSL has passed.CLOSE
The reason for the need to wave four times is that either party can send a request to release the connection after the end of the data transmission. When the other party confirms, it enters the semi-closed state. When the other party has no data to send, the connection release request is issued again. Therefore, it is necessary Four times
The client needs to make a response, and then enter the TIME-WAITstate. At this time, the connection has not been closed. The client will enter after the time 2MSL has elapsed.CLOSE
The reason for the need to wave four times is that either party can send a request to release the connection after the end of the data transmission. When the other party confirms, it enters the semi-closed state. When the other party has no data to send, the connection release request is issued again. Therefore, it is necessary Four times
The reason why the client needs to wait for 2MSL above is: ①In order to ensure that the last response can reach the server, ②to prevent invalid message segments, after waiting for the 2MSL time, it can ensure that all message segments within the duration of this connection are from the network disappear