installation
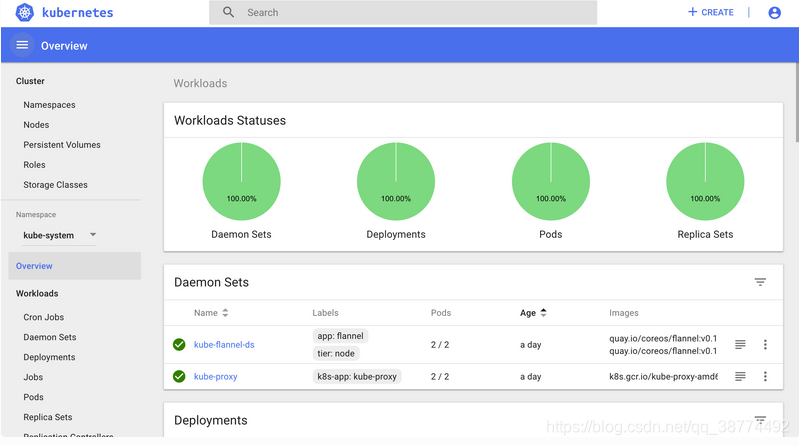
1. Kubernetes Dashboard is a WEB UI management tool for k8s cluster, the code is hosted on github,
address: https://github.com/kubernetes/dashboard
2. Installation
wget https://raw.githubusercontent.com/kubernetes/dashboard/v1.10.1/src/deploy/recommended/kubernetes-dashboard.yaml
There are three ways to access:
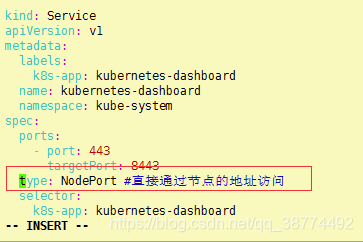
①Access via node address
Add the following fields in the configuration file
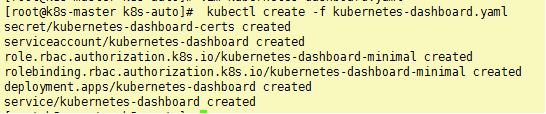
3. Deployment
kubectl create -f kubernetes-dashboard.yaml
4. View its external network access port
kubectl get svc kubernetes-dashboard -n kube-system
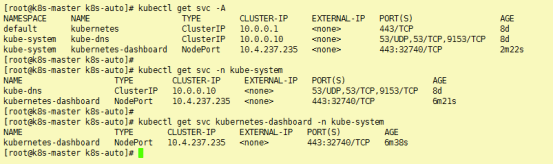
Access url:
https://13x.1xx.48.xxx:32740/

②Use Kube-proxy API proxy form to access
kubectl proxy --address="0.0.0.0" --accept-hosts='^localhost$,^127\.0\.0\.1$,^172\.24\.4'
http://172.24.4.15:8001/api/v1/namespaces/kubernetes-dashboard/services/https:kubernetes-dashboard:/proxy/#/login
If you want to connect to the service through proxy, you must use a specific format of Proxy URL :
http://<apiserver-address>/api/v1/namespaces/<service-namespace>/services/[https:]<service-name>:[<port-name>]/proxy
- apiserver-address is the address of the machine you entered the kubectl proxy command
- port-name is optional, if you do not specify the name of the port
- The protocol is optional. If you are using http,
there is a pit, pay attention to the colon between service-name and port-name, even if port-name is not used, and the colon after service-name can not be less refer to the official website documentation incorrect
proxy address Please modify your Master node IP
③ access through port forwarding
kubectl port-forward -n kubernetes-dashboard service / kubernetes-dashboard 8080: 443 --address = 0.0.0.0
Then directly access any node IP in the cluster and add port 31694 above to open the dashboard page.
Here I choose the second method

Authentication
When logging in to the dashboard, two authentication methods are supported: Kubeconfig and token. Kubeconfig also relies on the token field, so the step of generating token is essential.
Generate token
We create an admin user and grant the admin role binding, use the following yaml file to create the admin user and give him administrator privileges, and then we can log in to dashbaord through the token. This authentication method is actually through the identity authentication of the Service Account plus The above Bearer token request API server is implemented, refer to the authentication in Kubernetes.
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: admin
annotations:
rbac.authorization.kubernetes.io/autoupdate: "true"
roleRef:
kind: ClusterRole
name: cluster-admin
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: ServiceAccount
name: admin
namespace: kube-system
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin
namespace: kube-system
labels:
kubernetes.io/cluster-service: "true"
addonmanager.kubernetes.io/mode: Reconcile
[root@k8s-master k8s-auto]# kubectl apply -f kubernetes_token.yaml
clusterrolebinding.rbac.authorization.k8s.io/admin created
serviceaccount/admin created
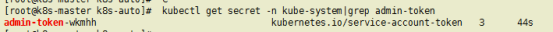
kubectl get secret admin-token-wkmhh -o jsonpath={
.data.token} -n kube-system |base64 -d;
Take the token generated by the above command to log in.

This is because the secret key is incorrect. Check and retry after modification

. This is because the requested resource cannot be found. I am here because there is only one master node and there are no other services on it. Normally, it should be as follows