Unauthorized access, in the usual tests, should be relatively easy of a loophole, you only need to be scanned by software Sword, etc., it is possible to get an unauthorized access vulnerabilities.
However, what causes it, please listen to me Wei (xia) Wei (bi) Road (bi) to.
All of the following code is I wrote it myself, there may be unsightly, coding errors and so on, I hope you can correct me.
Vulnerability to explain
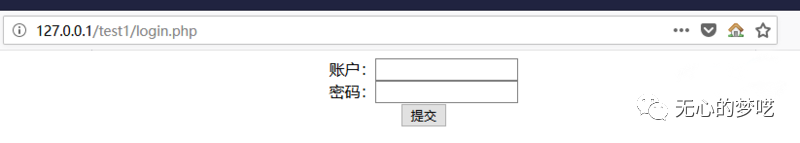
Below, this is a login box, login.php
In the usual test, we often try to directly access some of the key file, if it's validation code in question, we will be able to have direct access to normally inaccessible content
Here we have direct access to the index.php page
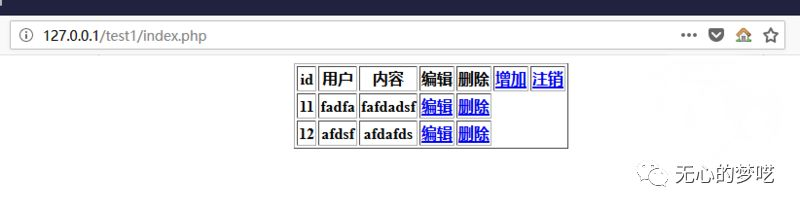
We can directly access to content only in the case of landing, to access to the
Next, we look at how the code is written
PS: In a normal project, may not be written like this, but here in order to facilitate understanding, it will be all code shorthand, the principle is the same
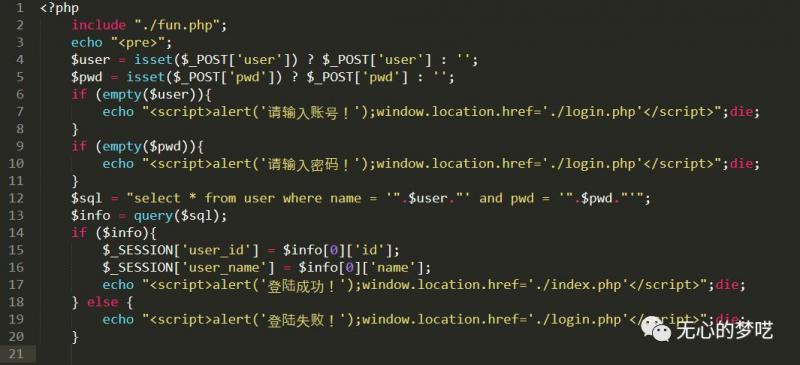
login.php

logins.php
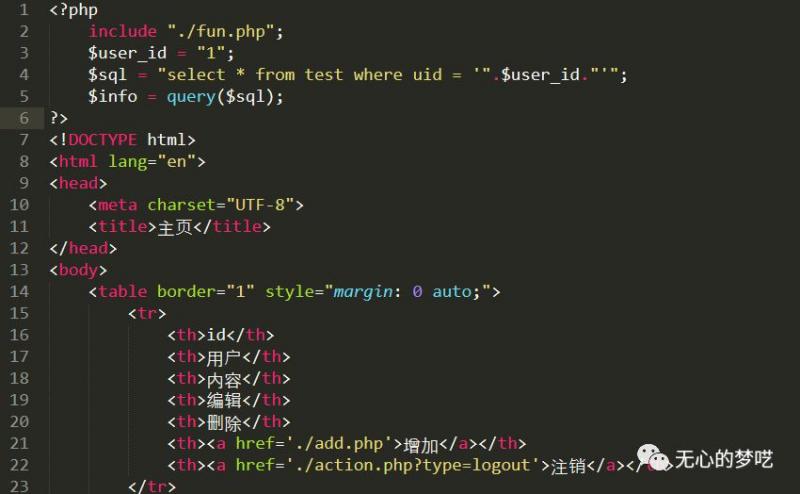
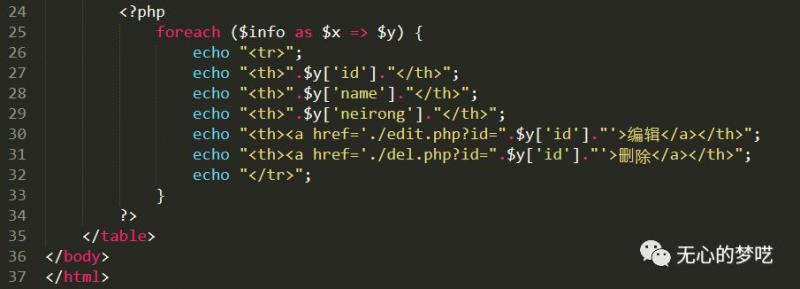
index.php
PS: fun.php for the database manipulation functions comprising
I believe we can understand this part of the code
login.php landing page for the code, only one form form, where we can see that it is the content passed logins.php
logins.php content to receive a pass over the account password, first determine whether the account passwords are filled out, and then into a database query, if present, set the session and return to the successful landing, and jump to the session page; otherwise, it returns failed on landing .
Next, the main concern is the code of index.php file, here is our most important part caused by unauthorized access
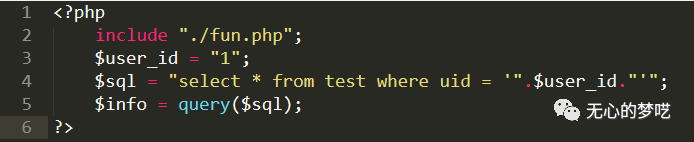
Here I will uid when the query is set to 1 by default, facilitate our operations
Here we can clearly know that it did not conduct any testing, direct the sql query, and then you can view the contents of the page
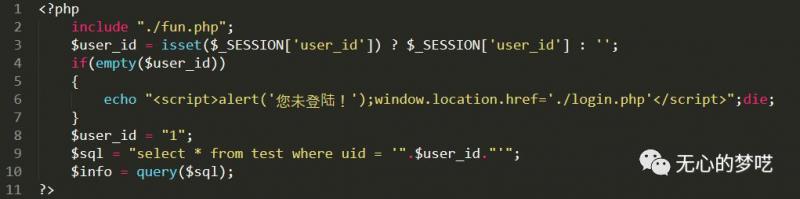
Simple repair
Because when landing successfully, we set the session, where we can directly increase at the beginning of a session to determine the value, if the session does not exist, directly out, without sql query.
After the code is modified as follows
In this case the effect is
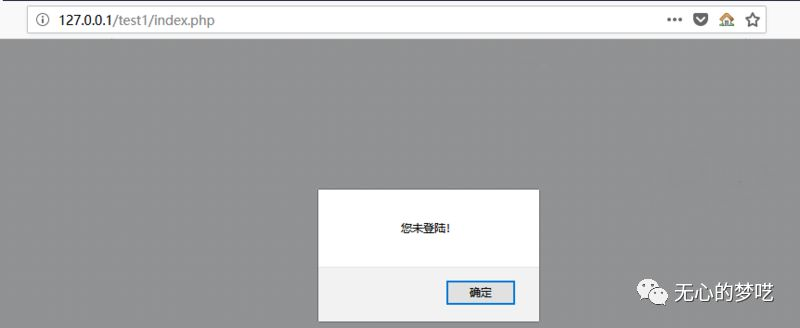
It can prevent unauthorized access
expand
Here is to mention, when writing code must determine the value of session, but can not determine the cookie, the cookie value is stored in a well-known client, it can be forged.
Classic case, please read - "classic case of MLM station tamper cookie into the background
No public debut article: unintentional balderdash (wuxinmengyi)
This is a record red team learning, Principal notes, personal growth number of public
Concern to scan code
