Environment Configuration:
Pyhton
the Java
dex2jar (the apk decompile java source code)
jd_gui (Source view)
jadx
have root Android phone or emulator
fiddler
analysis:
First, we use fiddler packet capture tool to be landed app capture, grab this app global agent package needs to open, or you'll catch data.
If you will not use the global proxy capture of friends, you can look at previous article, there are detailed packet capture tutorial.
Data capture follows:
<ignore_js_op>
We can see a token parameter, experienced friends know that this is a server-generated background, and before sending the login verification code requests and no other data exchange! <ignore_js_op>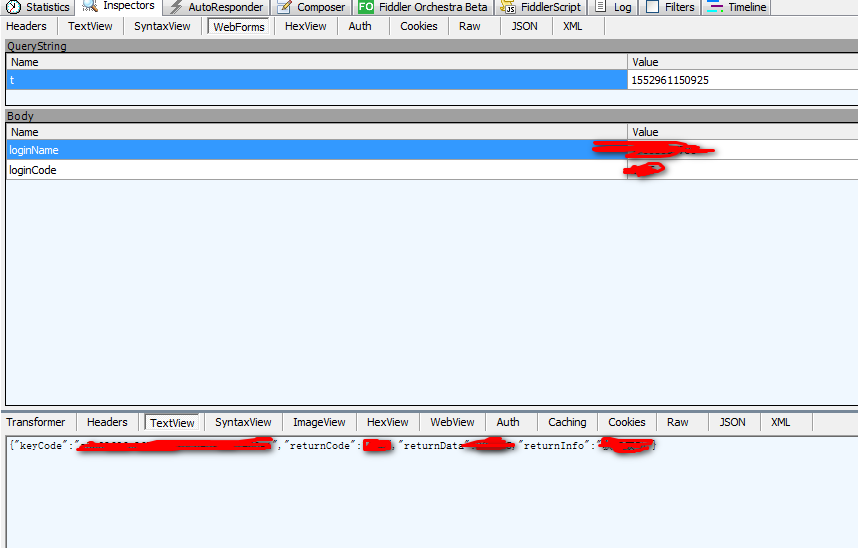
Crack process:
There are two options for ways to decompile, reverse compile process is as follows:
1.将安卓app的后缀更改为可解密的包,并解压
<ignore_js_op>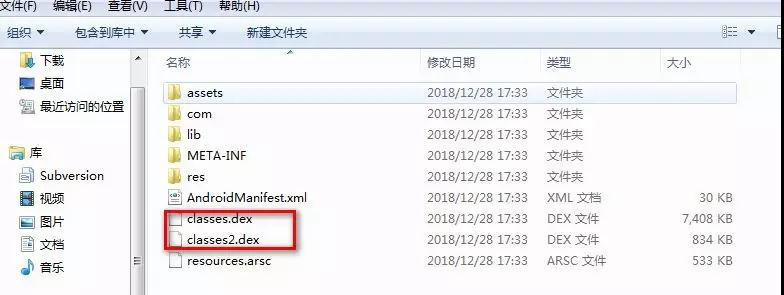
2.将解压后生成的后缀为 .dex 复制到 dex2jar 安装目录中
<ignore_js_op>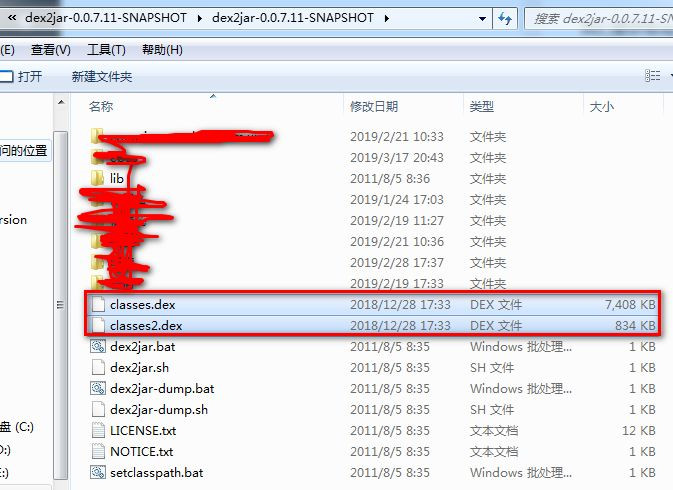
3.DOS命令行进入此文件夹,然后执行命令:dex2jar.bat classes.dex
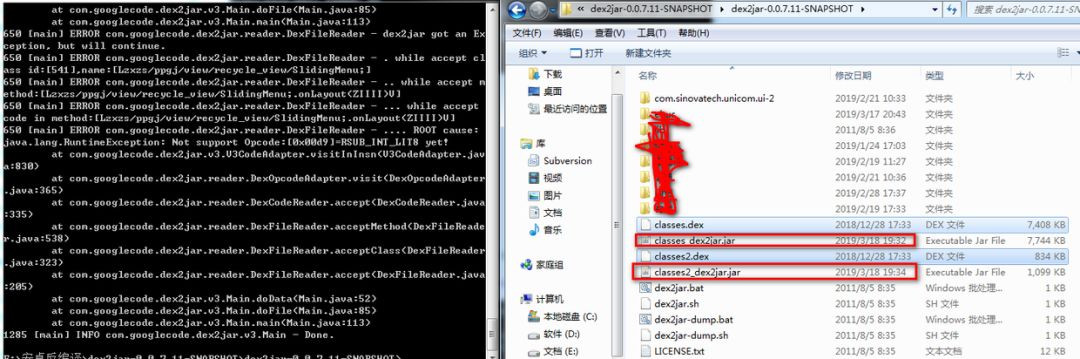
4. 生成.jar文件就是apk的源码了,我们使用 jd_gui 来查看源码 <ignore_js_op>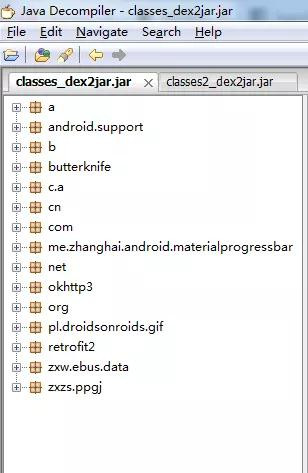
幸运的是这个app并没有加固,有app进行了加固,像腾讯乐固,360加固等等
<ignore_js_op>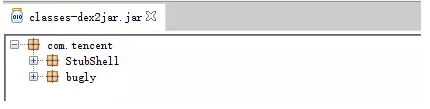
<ignore_js_op>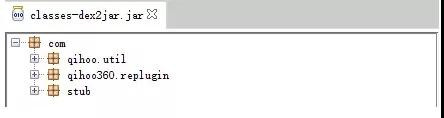
5.第二种反编译的方法是直接使用工具 jadx 打开 .apk 文件
6.根据请求或响应的参数去源码中搜索加密方式
根据前面请求、响应参数去搜索,或者请求的 url 地址去搜索,而且经验很重要
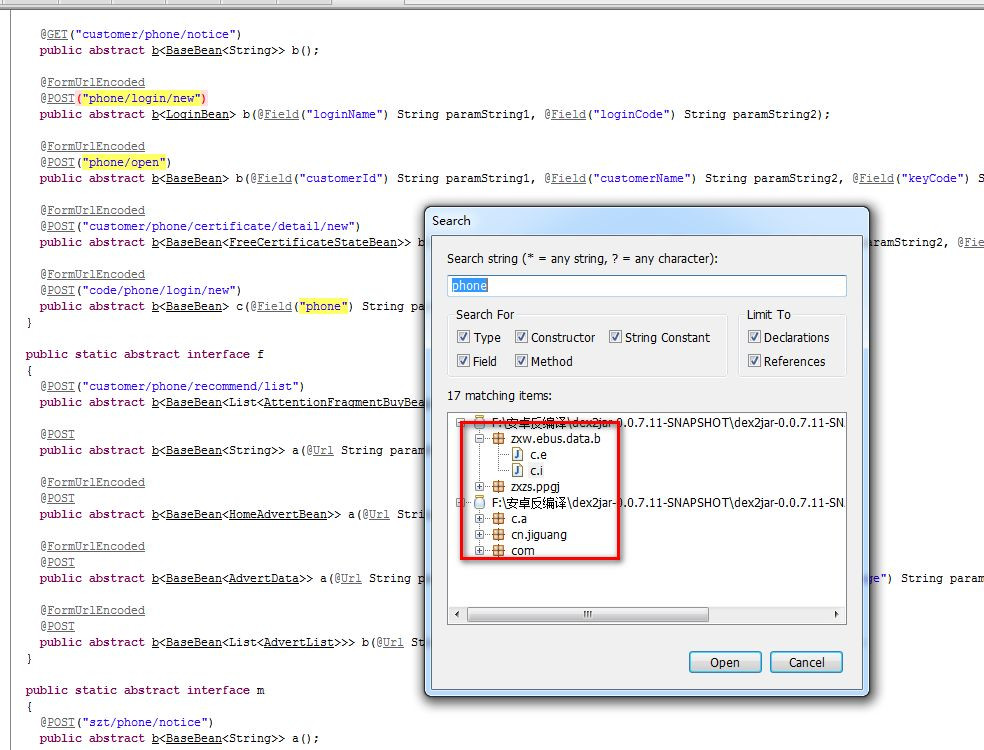
在查找的过程中要尽可能的多尝试,大胆猜测
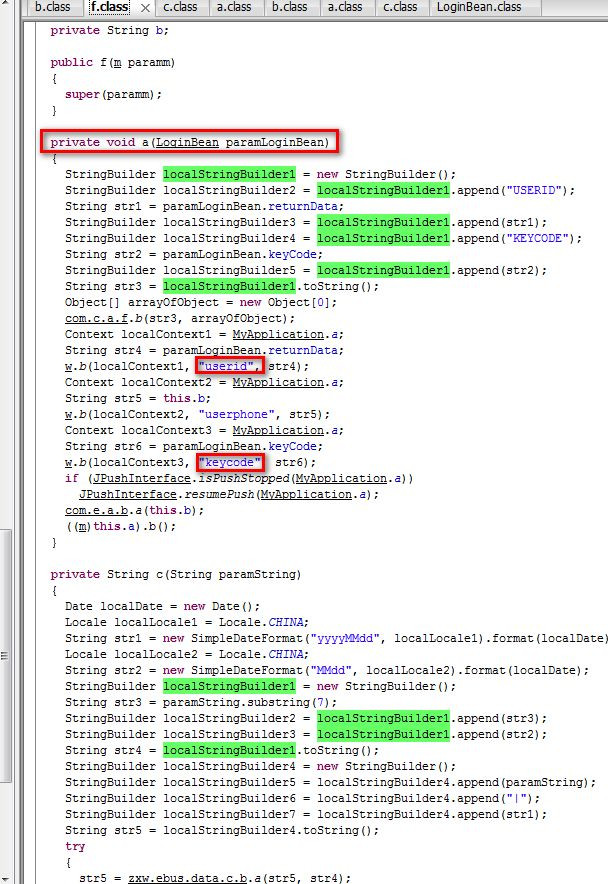
验证我们把源码拷贝出来,分析加密参数
private String c(String paramString)
{
Date localDate = new Date();
Locale localLocale1 = Locale.CHINA;
String str1 = new SimpleDateFormat("yyyyMMdd", localLocale1).format(localDate);
Locale localLocale2 = Locale.CHINA;
String str2 = new SimpleDateFormat("MMdd", localLocale2).format(localDate);
StringBuilder localStringBuilder1 = new StringBuilder();
String str3 = paramString.substring(7);
StringBuilder localStringBuilder2 = localStringBuilder1.append(str3);
StringBuilder localStringBuilder3 = localStringBuilder1.append(str2);
String str4 = localStringBuilder1.toString();
StringBuilder localStringBuilder4 = new StringBuilder();
StringBuilder localStringBuilder5 = localStringBuilder4.append(paramString);
StringBuilder localStringBuilder6 = localStringBuilder4.append("|");
StringBuilder localStringBuilder7 = localStringBuilder4.append(str1);
String str5 = localStringBuilder4.toString();
try
{
str5 = zxw.data.c.b.a(str5, str4);
}
catch (Exception localException)
{
localException.printStackTrace();
str5 = null;
}
return c.a(str5);
}
其中生成了两个参数 str5, str4 传到加密函数。
下面是 str5 的生成代码
String str1 = new SimpleDateFormat("yyyyMMdd", localLocale1).format(localDate);
StringBuilder localStringBuilder4 = new StringBuilder();
StringBuilder localStringBuilder5 = localStringBuilder4.append(paramString);
StringBuilder localStringBuilder6 = localStringBuilder4.append("|");
StringBuilder localStringBuilder7 = localStringBuilder4.append(str1);
String str5 = localStringBuilder4.toString();
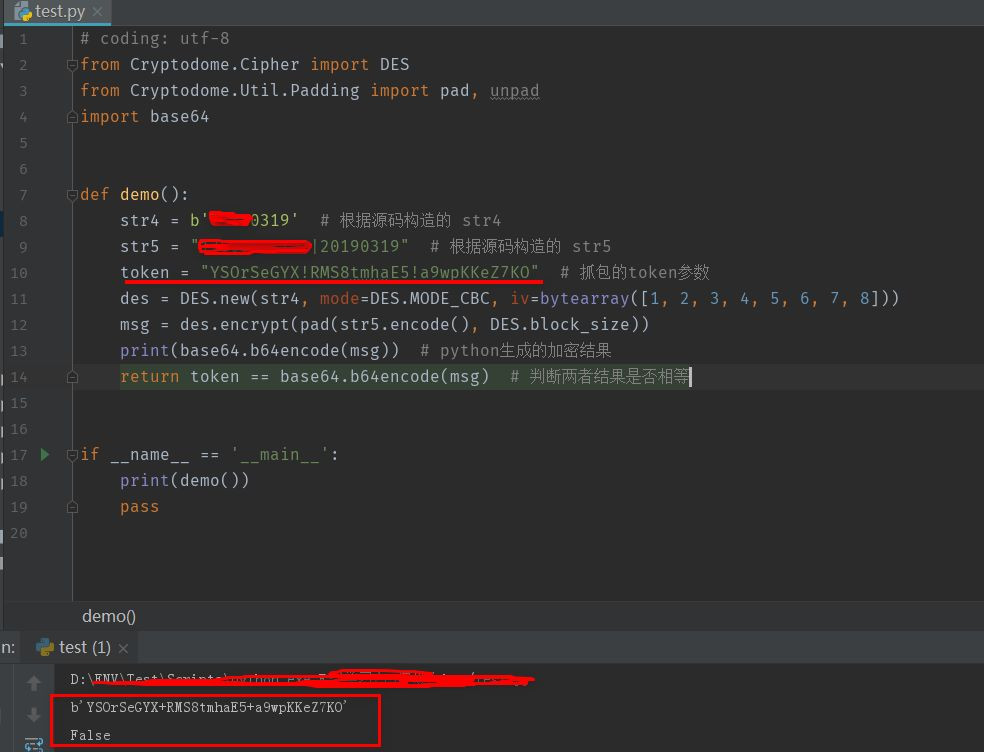
str1 = 20190319,也就是今天的日期
str5 = 传过来的参数 + '|' + '20190319'
那么 str4 呢
String str2 = new SimpleDateFormat("MMdd", localLocale2).format(localDate);
StringBuilder localStringBuilder1 = new StringBuilder();
String str3 = paramString.substring(7);
StringBuilder localStringBuilder2 = localStringBuilder1.append(str3);
StringBuilder localStringBuilder3 = localStringBuilder1.append(str2);
String str4 = localStringBuilder1.toString();
如果不知道生成的方式,就用 java运行一波,将这两个参数打印出来,是最方便快捷的方法~~
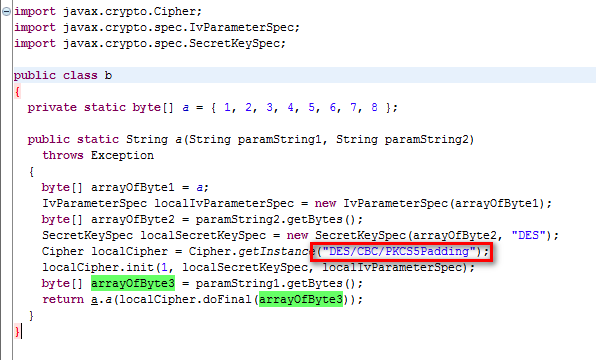
源码加密的方法如下:
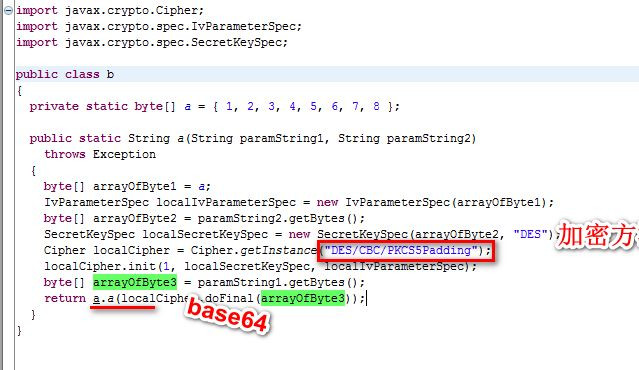
再返回去看看源码,源码中最后将生成的加密数据再传给了某个函数再返回
return c.a(str5);
public class c
{
public static String a(String paramString)
{
return paramString.replaceAll("\\+", "!");
}
}
所以我们将之前运行出来的结果中的 "+" 替换成 "!" 就是完全正确了!
so, 我们就将这个 token 参数给破解了!
总结
2.善于利用搜索引擎,碰到看不懂的方法,就去网上多搜索。
3.如果认识大佬,当然是要抱紧大佬的大腿啊,多问问大佬,会让你事半功倍!