About oauth2.0
OAuth 2.0 authorization framework supports third-party support limited access to HTTP service, approved by the interaction between a resource owner and resource persons to represent the HTTP service to access these resources, or gain access by allowing third-party applications on their own behalf authority.
To facilitate understanding, it is conceivable OAuth2.0 is in an intermediate layer between the user resources and third-party applications, it is the resources and third-party applications spaced so that third-party applications can not directly access resources, which play a role in protecting resources .
To access this protected resource, third-party applications (clients) in the time of the visit need to provide credentials. That is, the need to tell you who OAuth2.0 what you do.
OAuth defines four roles:
- resource owner (resource owner)
- resource server (resource server)
- client (Client): On behalf of the resource owner and the owner's authorization to access a protected resource applications
- authorization server (authorization server): access token issued to the client after successful authentication and authorization resource owner
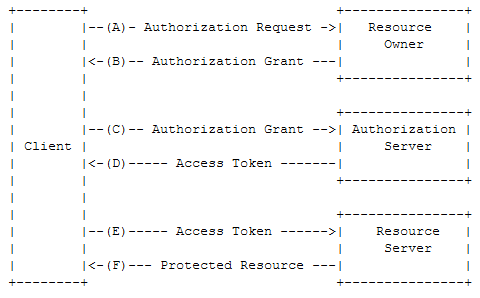
Abstract OAuth2.0 process shown in Figure:
- (A) client requests its authorization to the resource owner
- (B) the client receives the license of the owner of the resource, this is a license authorized on behalf of the resource owner credentials
- (C) The client requests access token to the authorization server, and produce license
- (D) authorization server to authenticate the identity of the client, and license check, if we are all valid, the access token issuance
- (E) client requests a protected resource to the resource server, and produce an access token
- (F) resource servers check the access token, if the token is valid, the provision of services
Think about the micro-channel public platform, in the micro-channel public platform development process when we visit a page, the page may pop up a message box applications that require access to our personal information asked whether to allow the point to confirm in fact authorize a third party app to get us in the micro-letter personal information public platform. Here is authorized to micro-letter web OAuth2.0 use.

Examples of micro-channel authorization page
[Micro-channel public platform | development document] http://mp.weixin.qq.com/wiki/home/ .
Implementation steps:
Step 1: The user consent, access code
Step 2: The code page in exchange for authorization access_token
3 The third step: pulling the user information (as required scope snsapi_userinfo)
The first step: user consent, access code
Splicing the following address, replacing the parameters of the micro-channel open at
https://open.weixin.qq.com/connect/oauth2/authorize?appid=APPID&redirect_uri=REDIRECT_URI&response_type=code&scope=SCOPE&state=STATE#wechat_redirect
If the user agrees authorization, the page will jump to redirect_uri /? Code = CODE & state = STATE.
The sample code to obtain code
/ **
* @explain
* acquisition code, used to get openid and the access_token
* @remark
* code can only be used once, after acquiring the code fails to get again need to re-enter the
* authorization page does not pop up for public concern No. after the custom menu jumps, etc., if you do not focus, you can only get openid
** /
public function getCode ()
{
IF (isset ($ _ gET [ "code"])) {
return $ _GET [ "code"];
} {the else
$ = STR. "LOCATION: https://open.weixin.qq.com/connect/oauth2/authorize?appid=" $ this-> AppID "the redirect_uri = &" $ this-> index_url "& response_type =... & scope = & snsapi_userinfo code State = # wechat_redirect. 1 ";
header (STR $);
Exit;
}
}
Step Two: The code page in exchange for authorization access_token
Alternatively the link parameters, the server requests the address curl
https://api.weixin.qq.com/sns/oauth2/access_token?appid=APPID&secret=SECRET&code=CODE&grant_type=authorization_code
Return data as follows
{
"access_token":"ACCESS_TOKEN",
"expires_in":7200,
"refresh_token":"REFRESH_TOKEN",
"openid":"OPENID",
"scope":"SCOPE"
}
Code Example:
/**
* @explain
* 用于获取access_token,返回的<span style="font-family: Arial, Helvetica, sans-serif;">$access_token_array中也包含有用户的openid信息。</span>
**/
public function getOpenId()
{
$access_token_url = "https://api.weixin.qq.com/sns/oauth2/access_token?appid=" . $this->appid . "&secret=" . $this->appsecret . "&code=" . $this->code . "&grant_type=authorization_code";
$access_token_json = $this->https_request($access_token_url);
$access_token_array = json_decode($access_token_json, TRUE);
return $access_token_array;
}
The third step: pulling the user information (as required scope snsapi_userinfo)
http: GET (using the https protocol) https://api.weixin.qq.com/sns/userinfo?access_token=ACCESS_TOKEN&openid=OPENID&lang=zh_CN
Return data as follows:
{
"openid":" OPENID",
" nickname": NICKNAME,
"sex":"1",
"province":"PROVINCE"
"city":"CITY",
"country":"COUNTRY",
"headimgurl": "http://thirdwx.qlogo.cn/mmopen/g3MonUZtNHkdmzicIlibx6iaFqAc56vxLSUfpb6n5WKSYVY0ChQKkiaJSgQ1dZuTOgvLLrhJbERQQ4eMsv84eavHiaiceqxibJxCfHe/46",
"privilege":[ "PRIVILEGE1" "PRIVILEGE2" ],
"unionid": "o6_bmasdasdsad6_2sgVt7hMZOPfL"
}
The sample code
/ **
* @explain
* After openid acquired user may determine whether there is user data to be acquired skip the access_token, can continue to obtain the access_token
** /
public getUserInfo function ()
{
$ userinfo_url = "HTTPS: // API .weixin.qq.com / SNS / UserInfo the access_token = "$ this-> the access_token [ 'the access_token'].." OpenID = & "$ this-> the access_token [ 'OpenID'].." & lang = zh_CN ";?
$ userinfo_json $ this- => https_request ($ userinfo_url);
$ = userinfo_array of json_decode ($ userinfo_json, TRUE);
return $ userinfo_array;
}