NGINX evolves to cloud native, All in OpenNJet
.need
Currently, only auth_basic_user_file is supported. You need to manually modify the contents of the file to add new users and change passwords. Need to add a type: auth_basic_kv, use kv to store username/password
•Key is "auth_basic":{prefix}:{user_name}, value is password. prefix supports variables so that server_name, etc. can be used for easy configuration.
•Provide HTTP interface to dynamically add entries, change passwords, and also support deletion
2.auth_basic_kv instruction design
This directive can be configured in the main, server, location, limit_conf blocks. Taking api_limit_except as an example, the auth_basic_kv directive is placed in the njt_http_auth_basic_module module. It can be configured with the auth_basic_user_file directive. It cannot be configured at the same time.
| Syntax | auth_basic_kv {prefix} |
| Default | - |
| Context | main,server,location,limit_conf |
prefix can be a variable or an ordinary string. The actual password format stored by kv is: Key: auth_basic:{prefix}:{user_name} Value: Password (using SHA algorithm)
Eg:
•Assume the user name is njet, use the variable $server_name format, (if the actual server_name is www.baidu.com), the actual storage in kv memory is: Key: auth_basic:www.baidu.com:njet
•Assuming that the user name is njet and the fixed string test_prefix format is used, the actual storage in kv memory is: Key: auth_basic:test_prefix:njet
#变量格式
api_limit_except GET {
auth_basic "OpenNJet AUTH API";
auth_basic_kv $server_name;
}
#字符串格式
api_limit_except GET {
auth_basic "OpenNJet AUTH API";
auth_basic_kv test_prefix;
}
NOTE:
When the Http request comes, if it is a variable, the variable will be converted into an actual value, and then searched in kv db. Therefore, all the actual variable values stored in kv db are not variables.
3. Password http api interface design
Add a new njt_http_auth_api_module. Like other imperative api modules (the control plane is configured through the /api entrance), it provides an http api interface and provides password addition, deletion and modification functions. Unified prefix: /api/v1/auth_kv/{type} type: [password| role|login] is reserved. Currently, the password type is used to operate the password. In the future, the role role and login can be operated.
3.1 Set password interface:
PUT:/api/v1/auth_kv/password body has the following format:
{
"prefix": "www.baidu.com", #对应上面$server_name变量,此处是实际的变量取值
"user_name": "njet",
"password": "123456"
}
或者
{
"prefix": "test_prefix", #此处是明确的字符串前缀
"user_name": "njet",
"password": "123456"
}
| error code | Error message | |
|---|---|---|
| increase success | 0 | success |
| User already exists | 4 | user existed |
| increase failure | 4 | add password error |
| Parameter has null value | 3 | prefix,user_name and password should not be empty |
| Parameter is illegal | 3 | There will be specific json errors |
| Password encryption failed | 4 | password encrypt error |
3.2 Password modification interface:
PATCH:/api/v1/auth_kv/password/{prefix}/{user_name}
#变量取值
/api/v1/auth_kv/password/www.baidu.com/njet
或者
#明确字符串前缀
/api/v1/auth_kv/password/test_prefix/njet
The body has the following format:
{
"password": "123456"
}
| error code | Error message | |
|---|---|---|
| Successfully modified | 0 | success |
| User does not exist | 4 | user is not existed |
| fail to edit | 4 | modify password error |
| Parameter has null value | 3 | prefix,user_name and password should not be empty |
| Parameter is illegal | 3 | There will be specific json errors |
| Password encryption failed | 4 | password encrypt error |
3.3 Delete password interface:
DELETE:/api/v1/auth_kv/password/{prefix}/{user_name}
#变量取值
/api/v1/auth_kv/password/www.baidu.com/njet
或者
#明确字符串前缀
/api/v1/auth_kv/password/test_prefix/njet
return value
| error code | Error message | |
|---|---|---|
| User deleted successfully | 0 | success |
| User does not exist | 4 | user is not exist |
| User deletion failed | 4 | delete error |
4. Test
4.1 Test configuration (taking the control plane configuration api_limit_except block test as an example):
Add permission verification for the range api interface as an example for testing (fixed string prefix) Add permission verification for the ssl api interface as an example for testing (use variable prefix)
ctrl.conf
...
load_module modules/njt_http_range_api_module.so; #以range api 设置权限验证普通字符串前缀为例测试
load_module modules/njt_http_ssl_api_module.so; #以range api 设置权限验证变量前缀为例测试
load_module modules/njt_http_auth_api_module.so; #auth kv 模块加载
...
http {
server {
listen 8081;
server_name www.test.com; #下面使用$server_name变量测试
location /api {
dyn_module_api;
api_limit_except /v1/range PUT {
auth_basic "OpenNJet range API";
auth_basic_kv test_kv; #range 使用固定前缀字符串测试
}
api_limit_except /v1/ssl PUT {
auth_basic "OpenNJet ssl API";
auth_basic_kv $server_name; #ssl 使用变量前缀测试
}
}
location /doc {
doc_api;
}
}
}
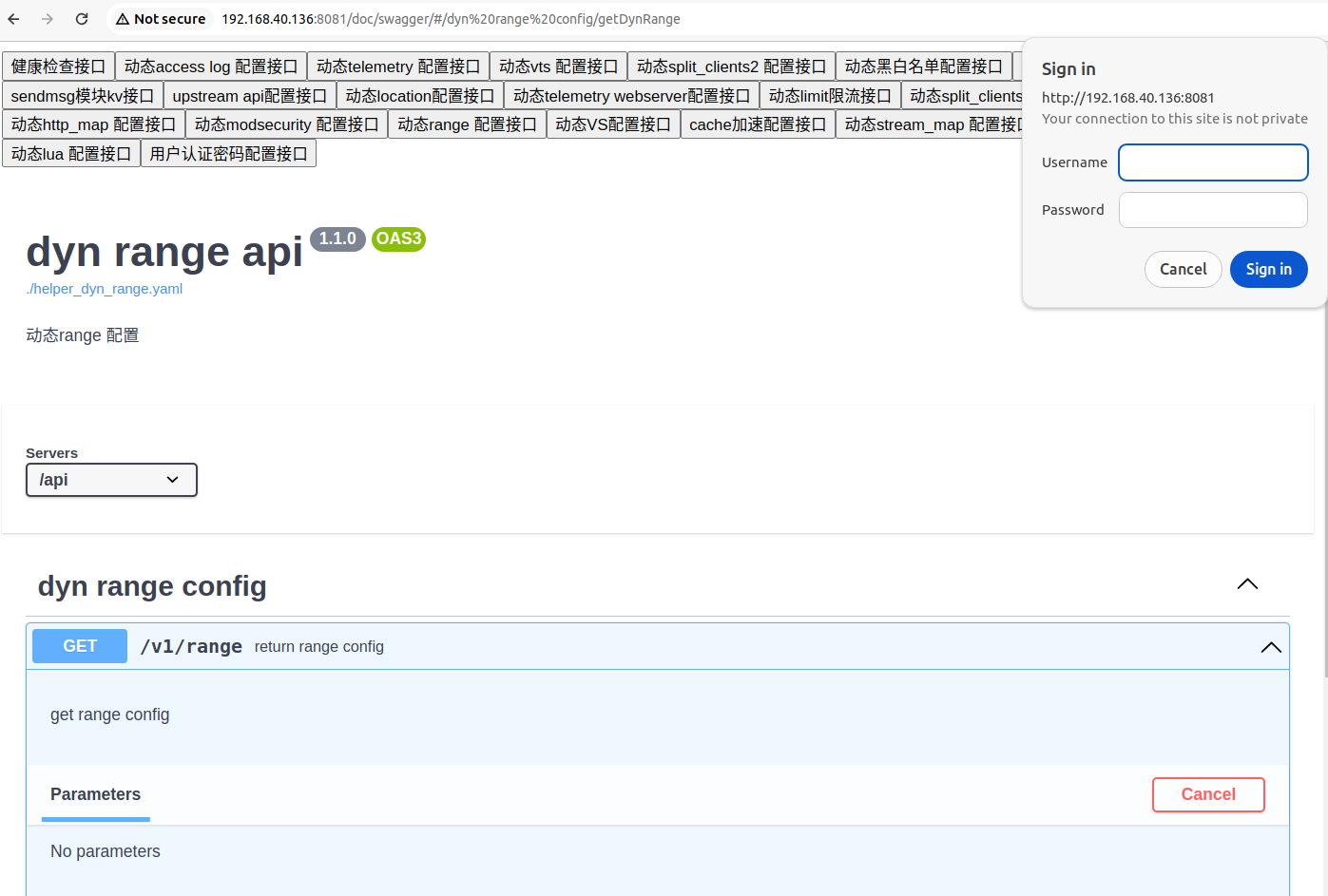
4.2 range fixed string prefix test (username: njet password 123456)
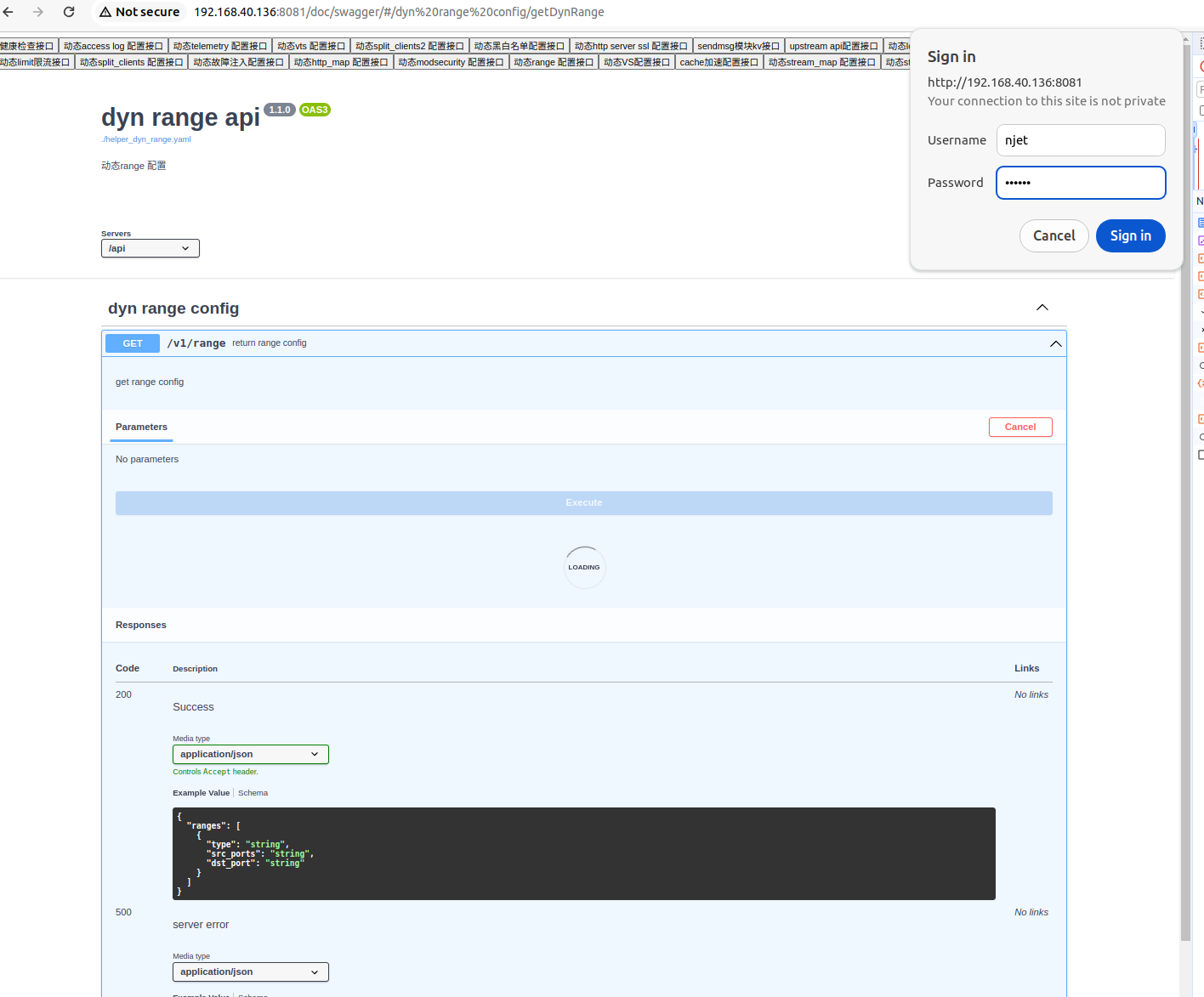
PUT Add user name and password. The initial test does not exist njet user and password 123456. Access the range api get interface, prompt to enter the password, enter njet/123456, the verification fails.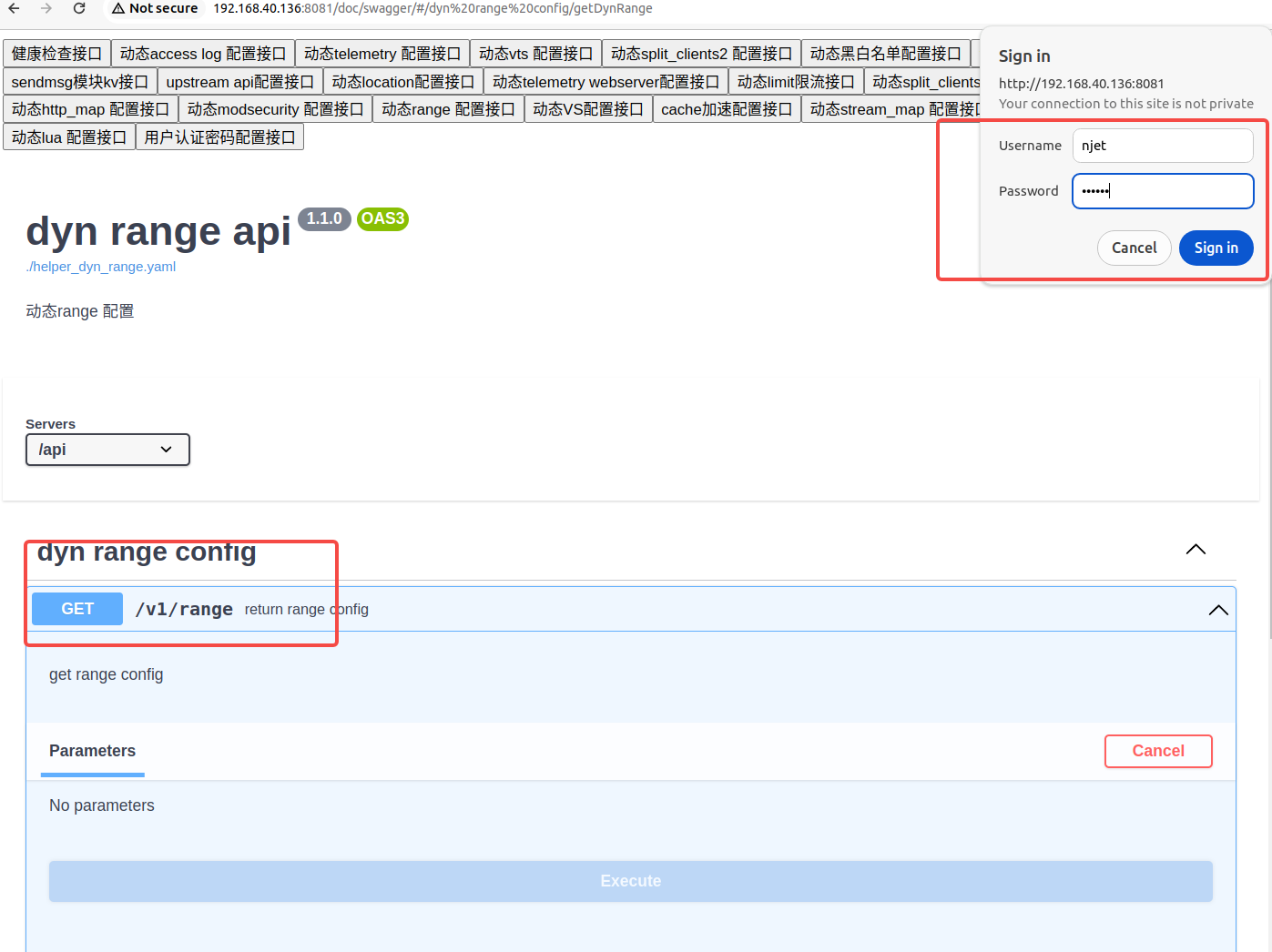
Configure username and password through auth configuration, njet/123456
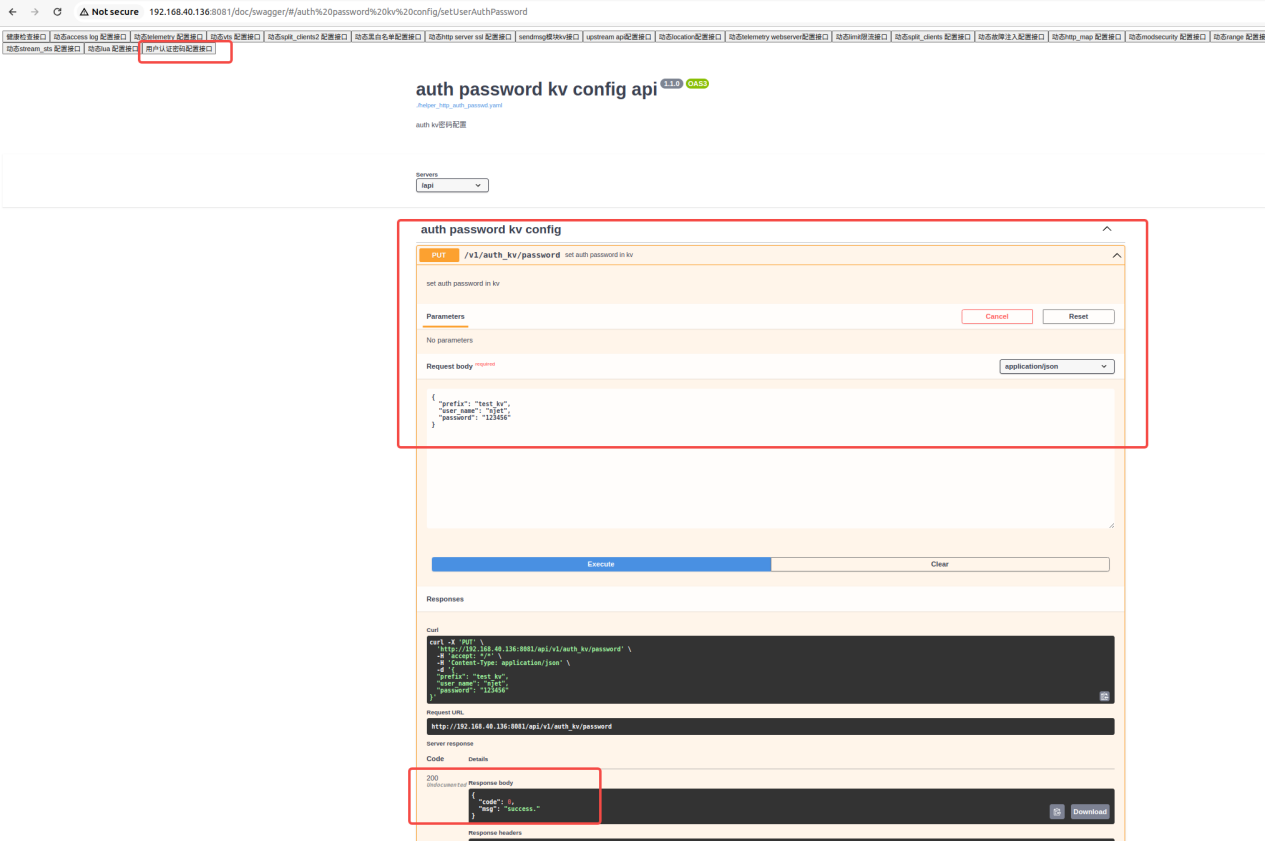
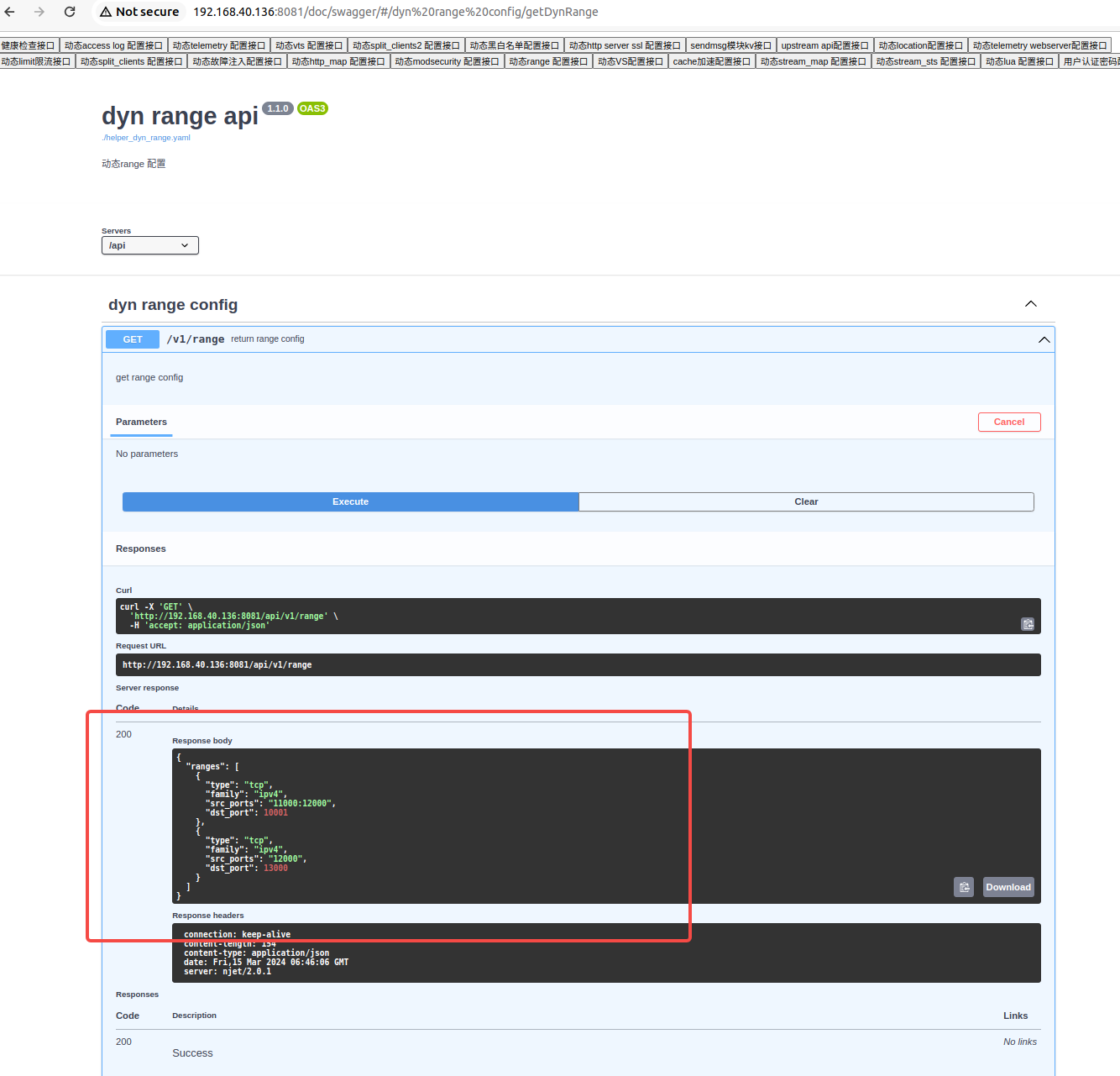
Visit the range get interface again, enter njet/123456, and the verification is passed successfully.

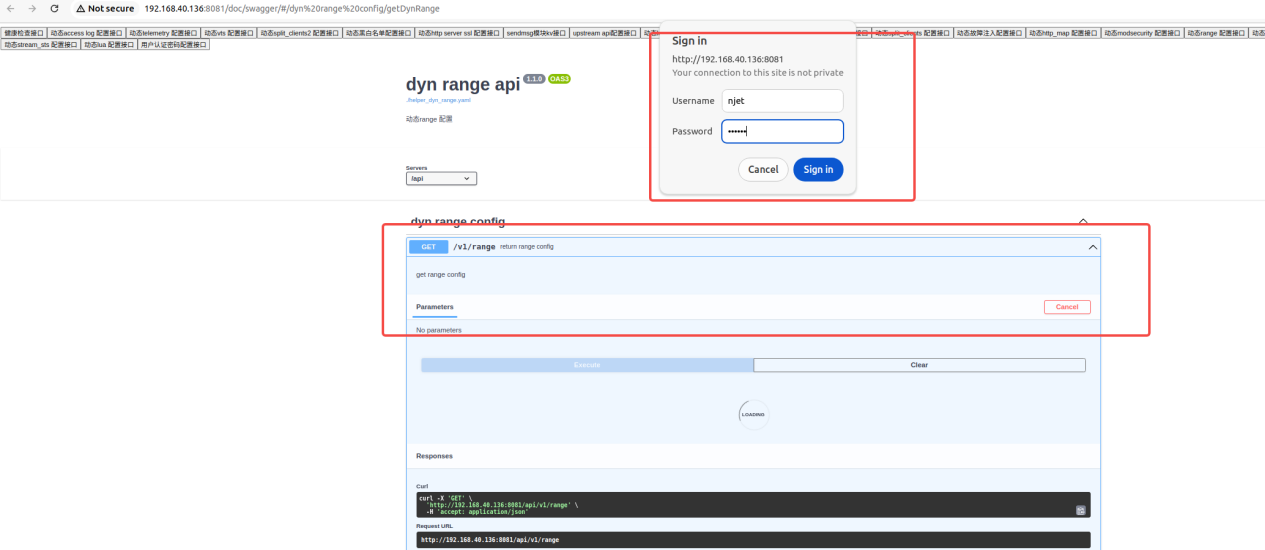
PATCH change password test

Revisit the range get interface and use njet/12345 to fail.
Use njet/654321, verification passed
DELETE delete password test delete password

Access the range again and fail
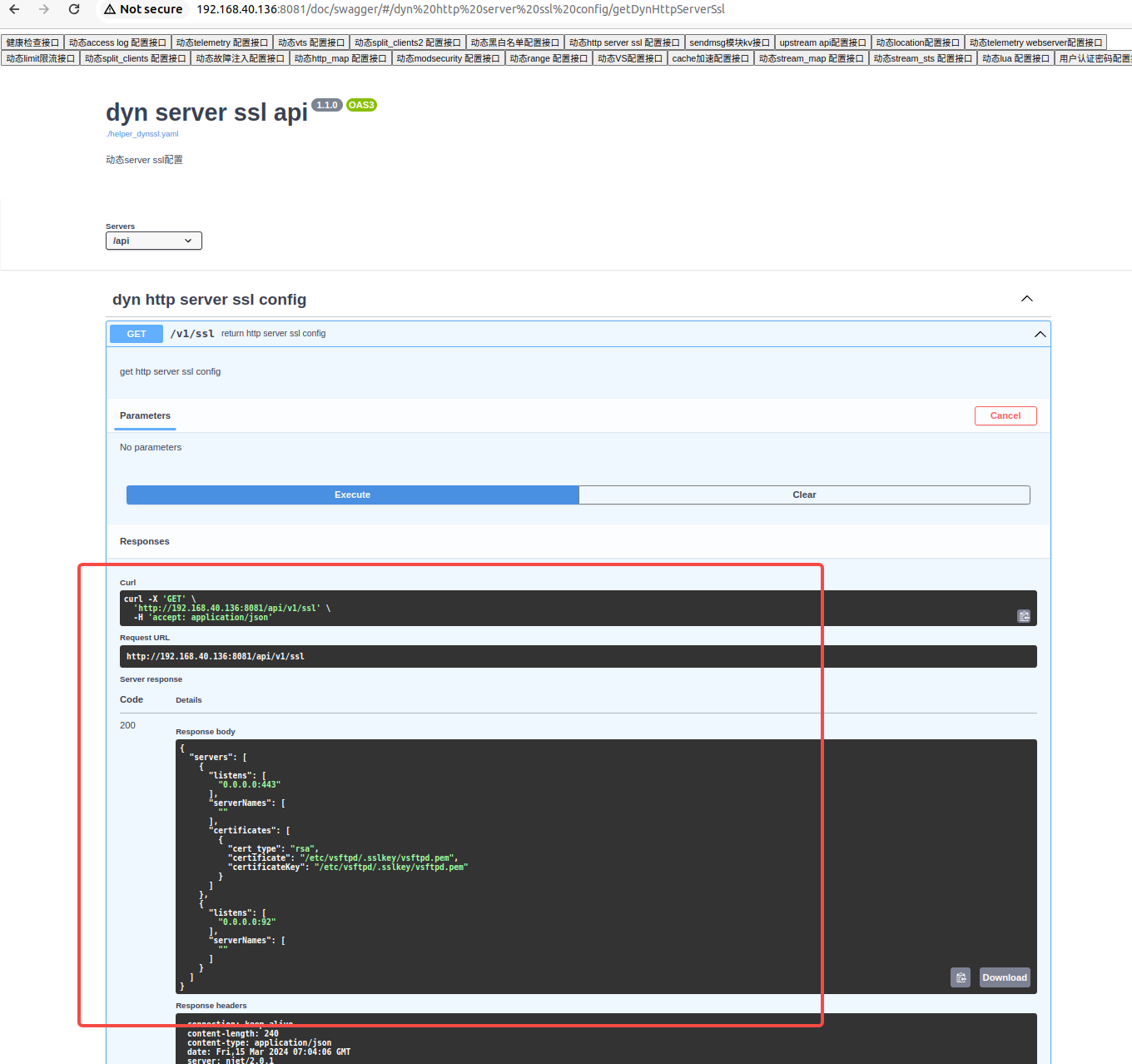
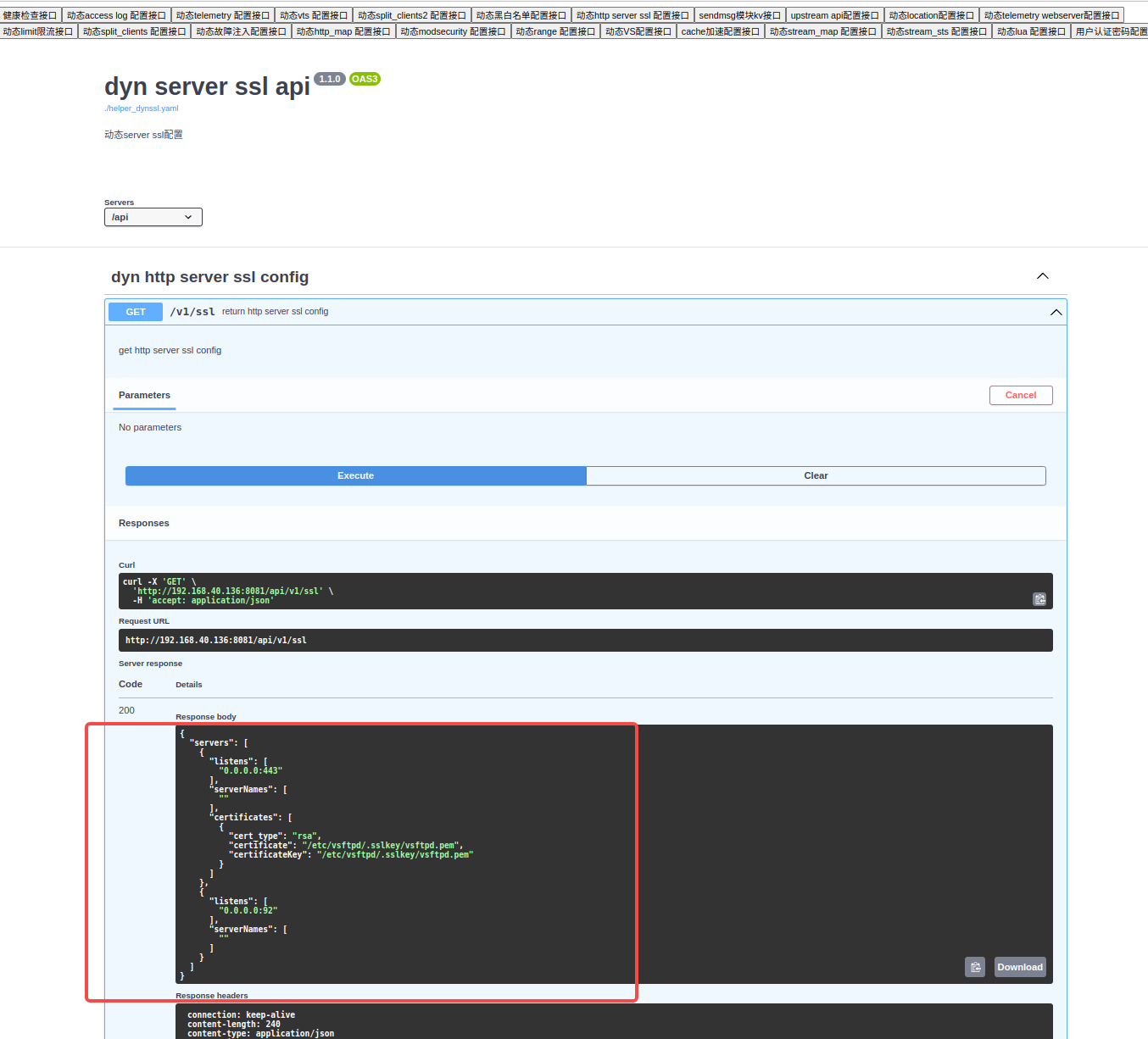
4.3 ssl test using variable prefix (username: ssl password 123456)
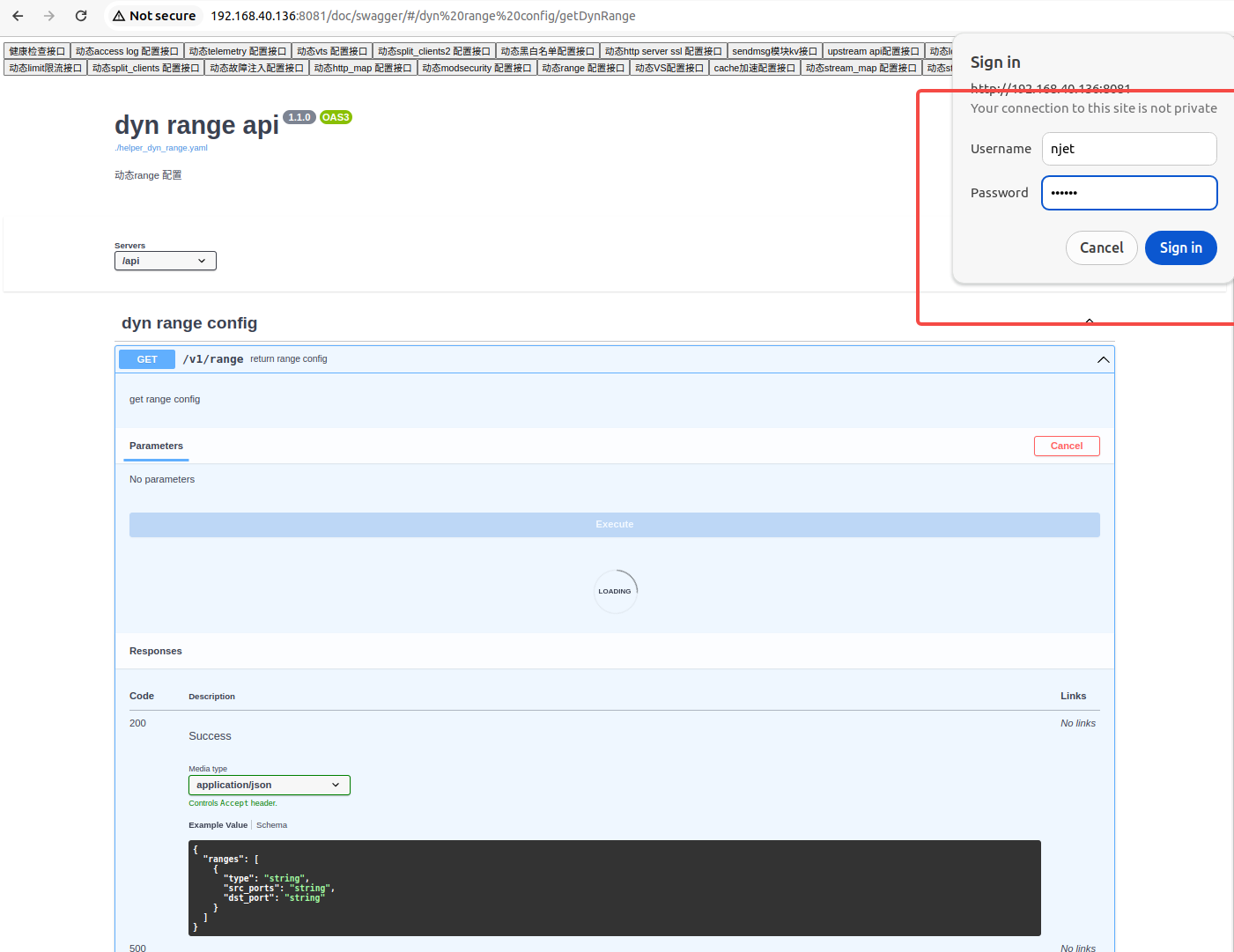
PUT Add username and password. Test that there is no ssl user and password 123456 initially. Access the range ssl get interface and prompt for password. Enter ssl/123456. The verification fails.

Configure the username and password through auth configuration, ssl/123456, use www.test.com as the prefix.
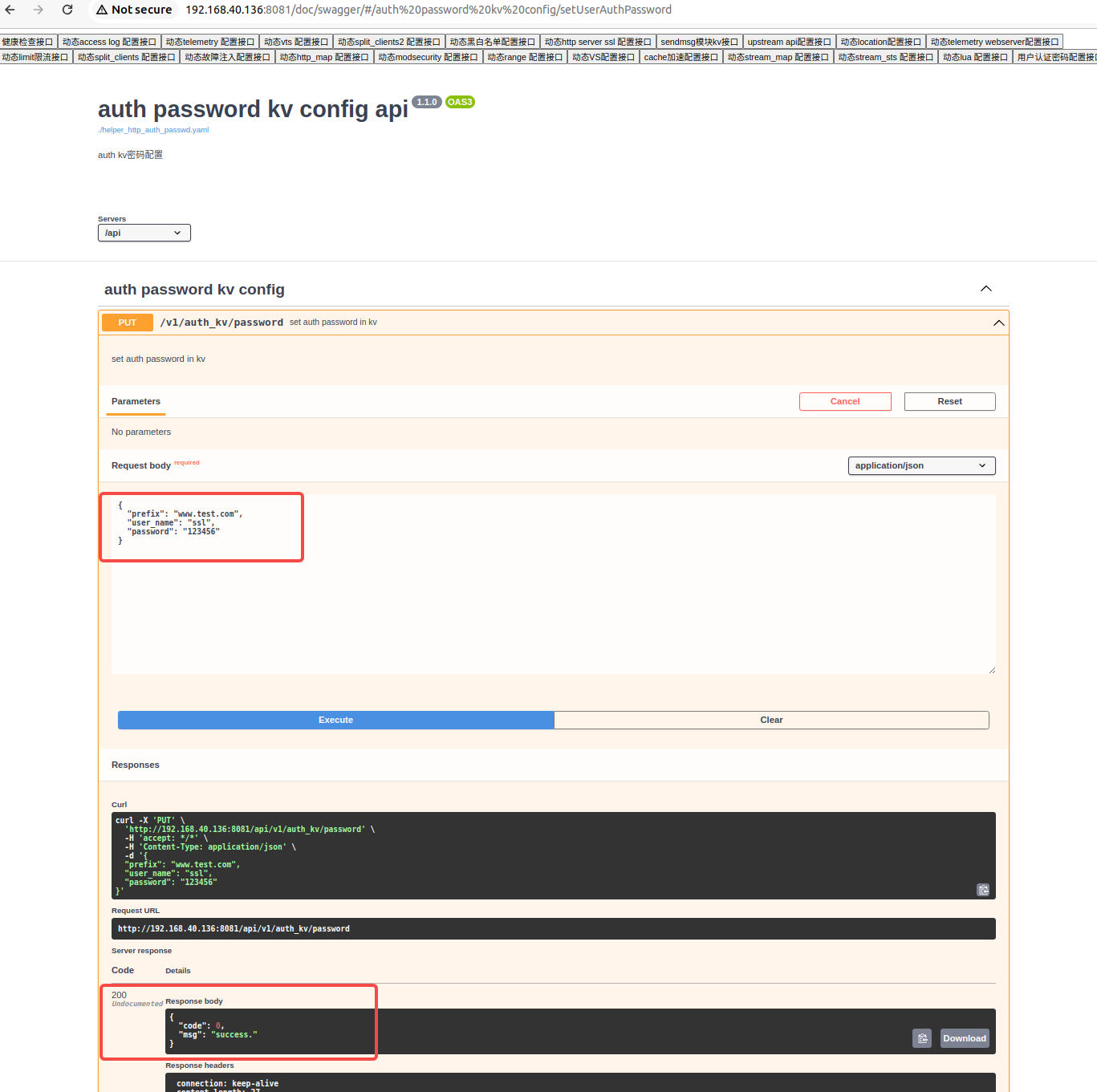
Access the ssl get interface again, enter ssl/123456, and the verification is passed successfully.

PATCH change password test

Re-access the ssl get interface and use ssl/12345 to fail.

Use ssl/654321, verification passed
DELETE delete password test delete password
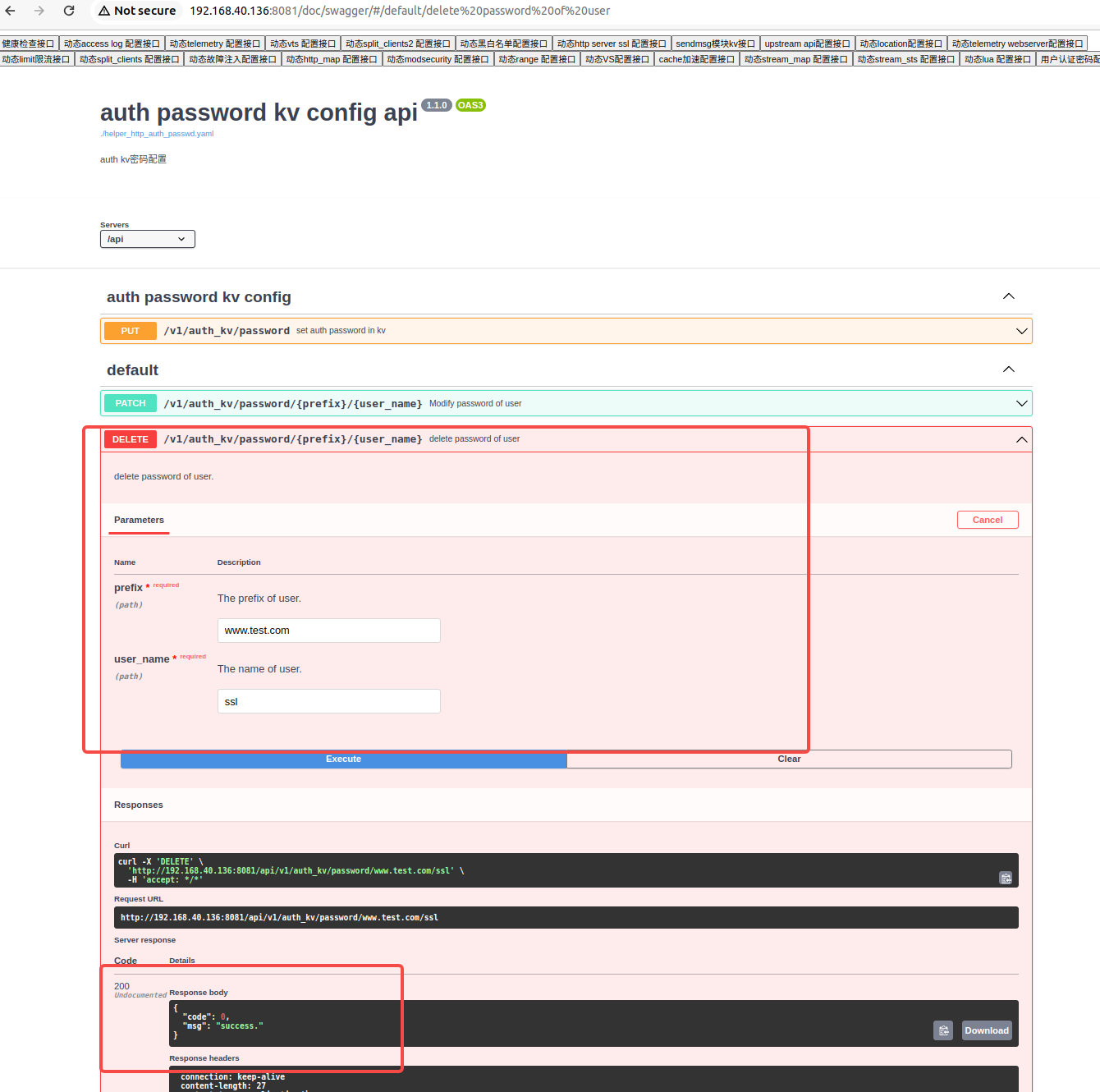
Access ssl again, failed

The NJet application engine achieves unique runtime dynamic configuration loading capabilities through kernel reconstruction and is a new generation of high-performance Web application engine . NJet has high-performance data plane processing capabilities and schedules multiple auxiliary functions such as clustering, high availability, active health checks, and declarative APIs through NJet's unique co-pilot CoPilot service framework to facilitate function expansion and isolate management/control function pairs. Due to the impact on the data plane, the performance of the NJet application engine exceeds three times that of the Envoy application engine recommended by CNCF. Mail group official website
