Vulnerability description
Airflow is an open source workflow automation platform that allows users to define, schedule and monitor the execution of workflow tasks. Run Tasks are run through Airflow's web interface or command-line tool.
In affected versions of Airflow, the Run Task feature allows users to manually trigger the execution of specific tasks without being restricted by normal task scheduling and dependencies. When a user does not have permission to perform a specific task, the execution of the task can be manually triggered through the Run Task function, thereby bypassing the access control and dependencies that should be implemented. Attackers can use the Run Task function to execute arbitrary code on the target server. Since DAG defines the dependencies and execution order between tasks, attackers can bypass certain DAG restrictions through Run Task.
| Vulnerability name | Apache Airflow Run Task Permission Bypass Vulnerability |
|---|---|
| Vulnerability type | Improper access control |
| Discovery time | 2023-08-05 |
| Vulnerability Breadth | generally |
| MPS number | MPS-2vhe-kp7q |
| CVE number | CVE-2023-39508 |
| CNVD number | - |
Sphere of influence
apache-airflow@(-∞, 2.6.0)
Repair plan
Upgrade the component apache-airflow to 2.6.0 or higher
reference link
https://www.oscs1024.com/hd/MPS-2vhe-kp7q
https://nvd.nist.gov/vuln/detail/CVE-2023-39508
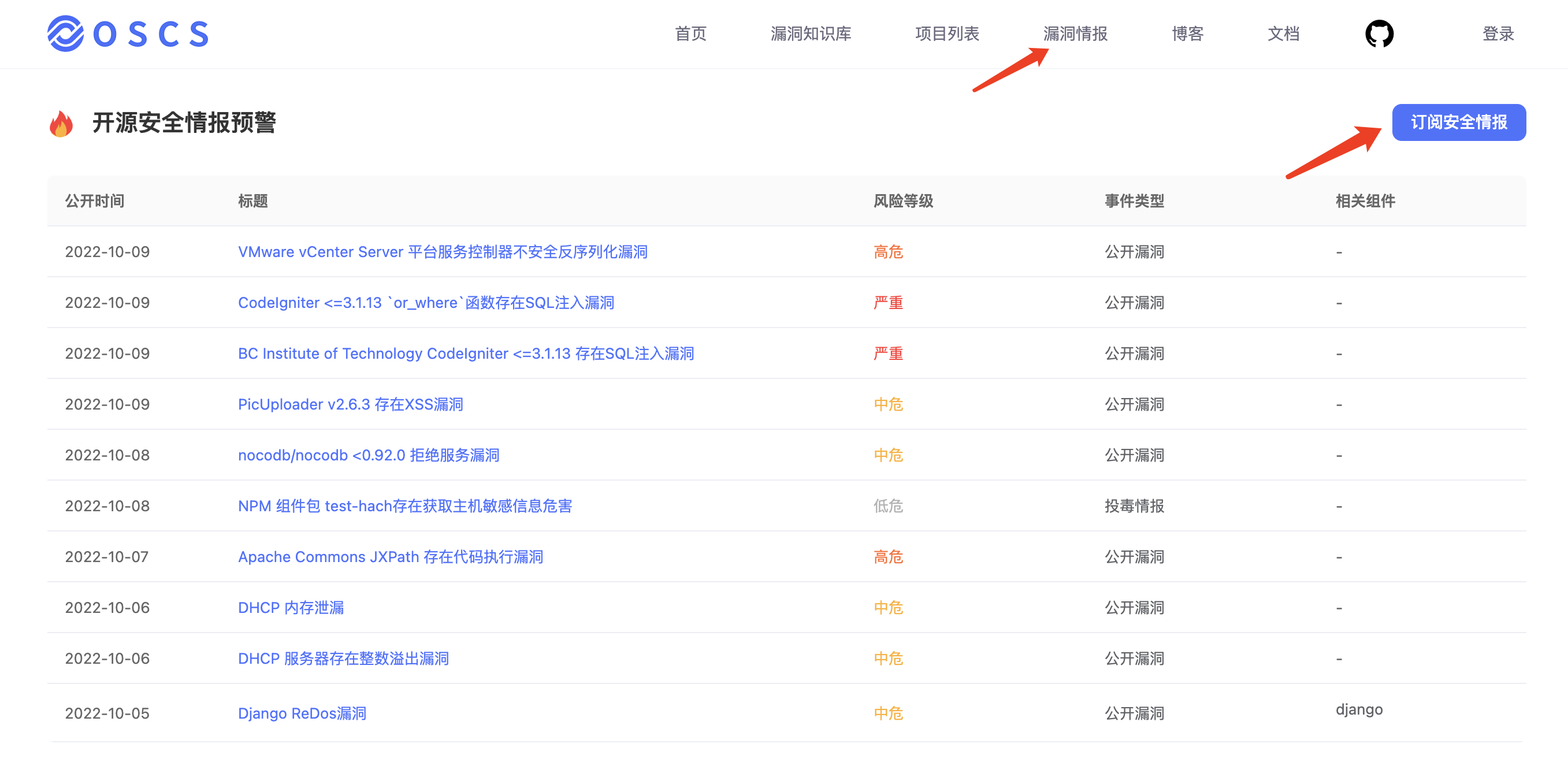
Free intelligence subscription & code security detection
OSCS is the first open source software supply chain security community in China. The community cooperates with developers to help the world's top open source projects solve security problems, and provides real-time security vulnerability intelligence. It also provides professional code security detection tools for developers to use for free. Community developers can obtain first-hand intelligence by configuring Feishu, DingTalk, and WeChat bots.
Free Code Security Detection Tool: https://www.murphysec.com/?src=osc
Free information subscription: https://www.oscs1024.com/cm/?src=osc
For details on how to subscribe, see: https://www.oscs1024.com/docs/vuln-warning/intro/?src=osc