ss
1. Command introduction
First use the manual to view the command introduction information
NAME
ss - another utility to investigate sockets
DESCRIPTION
ss is used to dump socket statistics. It allows showing information similar
to netstat. It can display more TCP and state informations than other tools.
The main function of the ss (Socket Statistics) command is to display socket information . Very similar to the use of the netstat command, it is used to display socket information, and the advantage of the ss command is that it can display more detailed information about TCP and connection status, and it is faster and more efficient.
2. Grammatical format
The grammatical format of ss is: ss [parameter] [filter]
SYNOPSIS
ss [options] [ FILTER ]
3. Basic parameters
The basic parameters of the command are as follows, and there will be more parameters. Of course, it can also show that the usage of this command will be quite rich.
| -n | Do not resolve domain names |
| -a | show all sockets |
| -l | Show sockets in listening state |
| -o | Show Timer Information |
| -e | Show detailed socket information |
| -m | Display the memory status of the socket |
| -p | Show process using socket |
| -i | Display internal TCP information |
| -s | Show socket usage |
| -4 | Display ipv4 socket information |
| -6 | Display ipv6 socket information |
| -0 | Display PACKET socket information |
| -t | Display TCP socket information |
| -u | Display UDP socket information |
| -d | Display DCCP socket information |
| -w | Display RAW socket information |
| -D | Dump raw TCP socket information to a file |
| -r | Parse IP and port number |
4. The meanings represented by each column
| Nets | network identifier |
| State | Connection status for each service |
| Recv-Q | The amount of data in the receive socket (socket) queue, in bytes |
| Send-Q | The amount of data in the send socket (socket) queue, in bytes |
| Local Address | run local computer address |
| Port | service port |
| Peer Address | peer port |
V. Reference examples
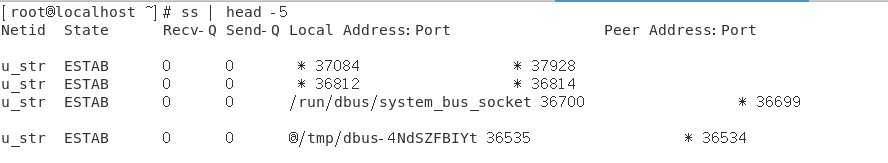
1. List established connections
By default, only ssthe command is used, without any parameters, it will display the socket list information of all established connections
[root@localhost ~]# ss |wc -l
716
[root@localhost ~]# ss | head -n 3
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port
u_str ESTAB 0 0 * 37084 * 37928
u_str ESTAB 0 0 * 36812 * 36814
2. Listen to the socket information of the TCP protocol
-lSocket content of all tcpprotocols can be listened to with parameters
<pre>[root@localhost ~]# ss -lt
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 100 127.0.0.1:smtp *:*
LISTEN 0 128 *:sunrpc *:*
LISTEN 0 5 192.168.122.1:domain *:*
LISTEN 0 128 *:ssh *:*
LISTEN 0 128 127.0.0.1:ipp *:*
LISTEN 0 100 [::1]:smtp [::]:*
LISTEN 0 128 [::]:sunrpc [::]:*
LISTEN 0 128 [::]:ssh [::]:*
LISTEN 0 128 [::1]:ipp [::]:*
</pre>
3. View the port the host listens on
-nIndicates that the domain name is not resolved, and the format of IP+port is displayed
[root@localhost ~]# ss -tnl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 *:111 *:*
LISTEN 0 5 192.168.122.1:53 *:*
LISTEN 0 128 *:22 *:*
LISTEN 0 128 127.0.0.1:631 *:*
4. Display information about running processes
-pThe parameters that need to be used , combined -tlwith the information that shows the service of the tcp protocol and is in the listening state
[root@localhost ~]# ss -tlp |head -10
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 100 127.0.0.1:smtp *:* users:(("master",pid=1284,fd=13))
LISTEN 0 128 *:sunrpc *:* users:(("rpcbind",pid=704,fd=8))
LISTEN 0 5 192.168.122.1:domain *:* users:(("dnsmasq",pid=1533,fd=6))
LISTEN 0 128 *:ssh *:* users:(("sshd",pid=1176,fd=3))
LISTEN 0 128 127.0.0.1:ipp *:* users:(("cupsd",pid=1168,fd=11))
LISTEN 0 100 [::1]:smtp [::]:* users:(("master",pid=1284,fd=14))
You can see that the last column will display the process name, PID, fd file descriptor and other information.
You can also grepobtain the service information you want to know by filtering the information
[root@localhost ~]# ss -ltp | grep ssh
LISTEN 0 128 *:ssh *:* users:(("sshd",pid=1176,fd=3))
LISTEN 0 128 [::]:ssh [::]:* users:(("sshd",pid=1176,fd=4))
5. Display all established information
Parameters are required -ato display all connection information
[root@localhost ~]# ss -a | wc -l
963
[root@localhost ~]# ss | wc -l
716
Because there is too much information, it will not be listed here. You can see that there will be more lines of information when displaying all and the default.
You can also add -t -nparameters to use
[root@localhost ~]# ss -ant
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 *:111 *:*
LISTEN 0 5 192.168.122.1:53 *:*
LISTEN 0 128 *:22 *:*
LISTEN 0 128 127.0.0.1:631 *:*
ESTAB 0 0 192.168.157.166:22 192.168.157.213:65011
LISTEN 0 100 [::1]:25 [::]:*
LISTEN 0 128 [::]:111 [::]:*
LISTEN 0 128 [::]:22 [::]:*
LISTEN 0 128 [::1]:631 [::]:*
[root@localhost ~]# ss -nt
State Recv-Q Send-Q Local Address:Port Peer Address:Port
ESTAB 0 0 192.168.157.166:22 192.168.157.213:65011
6. Display more information about the service
Such as displaying -otime information, -mdisplaying content used by sockets, -idisplaying internal tcp information
[root@localhost ~]# ss -imo | head -2
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port
u_str ESTAB 0 0 * 37084 * 37928 skmem:(r0,rb212992,t0,tb212992,f0,w0,o0,bl0,d0)
7. Display socket usage information
-sParameters needed to display usage information
[root@localhost ~]# ss -s
Total: 1711 (kernel 2055)
TCP: 11 (estab 1, closed 1, orphaned 0, synrecv 0, timewait 0/0), ports 0
Transport Total IP IPv6
* 2055 - -
RAW 1 0 1
UDP 11 8 3
TCP 10 6 4
INET 22 14 8
FRAG 0 0 0
8. Display IPv4 information
The parameters that need to be used -4are followed by the information to be filtered. Only the services that are being monitored are displayed here.
[root@localhost ~]# ss -4 state listening
Netid Recv-Q Send-Q Local Address:Port Peer Address:Port
tcp 0 100 127.0.0.1:smtp *:*
tcp 0 128 *:sunrpc *:*
tcp 0 5 192.168.122.1:domain *:*
tcp 0 128 *:ssh *:*
tcp 0 128 127.0.0.1:ipp *:*
-6To display the available parameters for IPv6
[root@localhost ~]# ss -6 state listening
Netid Recv-Q Send-Q Local Address:Port Peer Address:Port
tcp 0 100 [::1]:smtp [::]:*
tcp 0 128 [::]:sunrpc [::]:*
tcp 0 128 [::]:ssh [::]:*
tcp 0 128 [::1]:ipp [::]:*
9. Match remote and local addresses and port numbers
Several parameter formats need to be used here
They are:
dst: the destination address of the filtered connection
src: the local address of the filtered connection
dport: the destination port
sport: the source port
Match remote addresses and port numbers
ss dst 192.168.157.33
ss dst 192.168.157.33:443
ss dst 192.168.157.33:http
Match local port and port number
ss src 192.168.157.166
ss src 192.168.157.166:22
ss src 192.168.157.166:ssh
9.1 Of course, you can also compare the local and remote ports with a number.
How to use:
ss dport OP num
ss sport OP num
The OP in the above text could have used these
| <= | the | less than or equal to |
| == | eq | equal |
| != | it is | not equal to |
| > | gt | more than the |
| < | lt | less than |
Do you suddenly feel that the symbols in the table are so familiar? If you have studied shell scripts, you should be able to see what the symbols represent at a glance.
Let's continue to demonstrate how to use:
display the content of the port number whose source port is less than 50
[root@localhost ~]# ss -ntul sport lt 50
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port
tcp LISTEN 0 100 127.0.0.1:25 *:*
tcp LISTEN 0 128 *:22 *:*
tcp LISTEN 0 100 [::1]:25 [::]:*
tcp LISTEN 0 128 [::]:22 [::]:*
If you want to use a symbol, you need to add an escape character in front of the symbol.
[root@localhost ~]# ss -ntul sport \< 50
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port
tcp LISTEN 0 100 127.0.0.1:25 *:*
tcp LISTEN 0 128 *:22 *:*
tcp LISTEN 0 100 [::1]:25 [::]:*
tcp LISTEN 0 128 [::]:22 [::]:*
Summarize
The above content is only a part of the ss command, because the ss command has a lot of parameters, and there are countless usages. Regarding viewing network status information, it is also necessary to know how to use ss and netstat. If you think the above content is okay, you can like it and support it!
