@ TOC
Reverse an autumn aviation algorithm
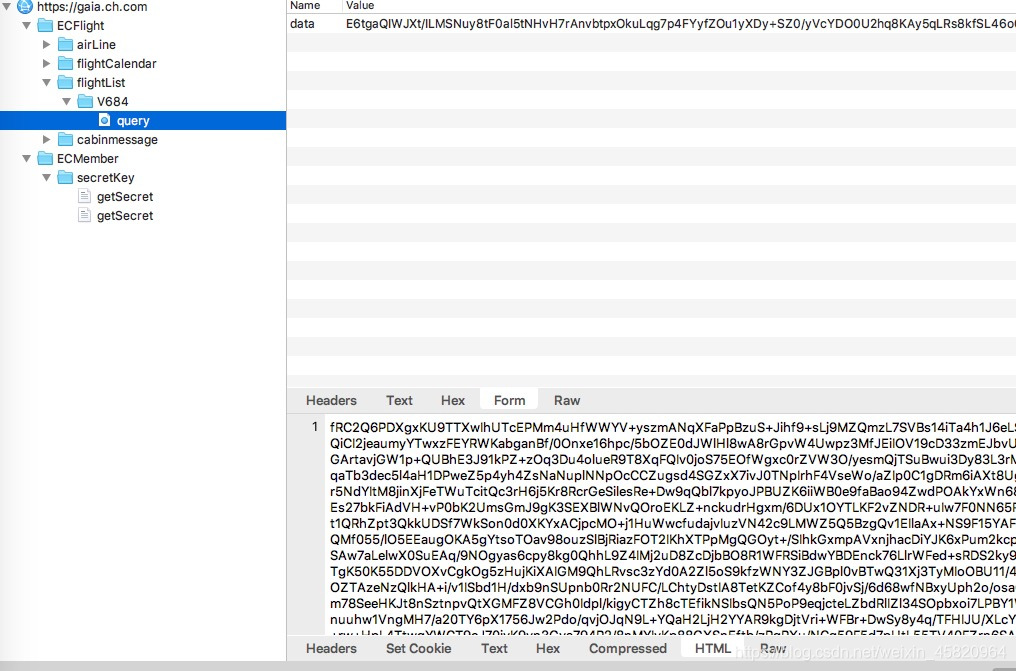
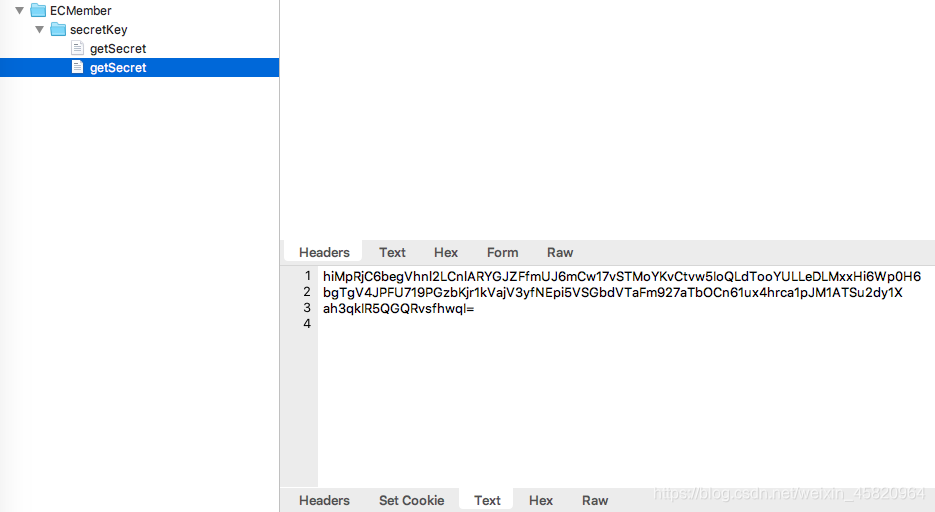
Packet capture by that, every time a page request app autumn, will first / ECMember / secretKey / getSecret send a request, a key is likely to be acquired, the request and response are base64 encoded ciphertext.
Packet capture analysis
Decompile
Here we open with jeb 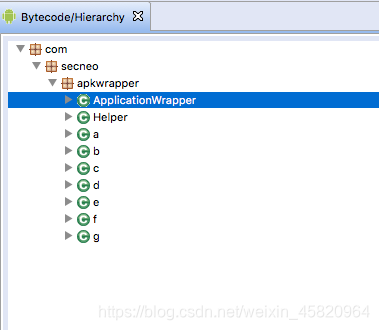 seen from the figure, add a shell, you can see from the package name is Bang Bang shell, we use IDA call and dump out the dex way off from memory about the case, and opened with jadx and export source code, with the idea to open
seen from the figure, add a shell, you can see from the package name is Bang Bang shell, we use IDA call and dump out the dex way off from memory about the case, and opened with jadx and export source code, with the idea to open
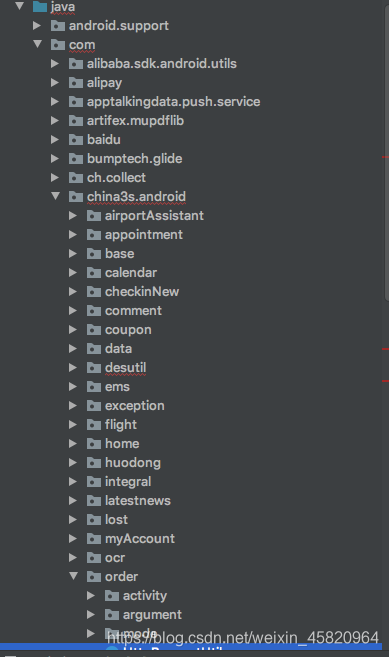
Looking data processing logic and response packets
Open search directly in the idea and enter the "data" 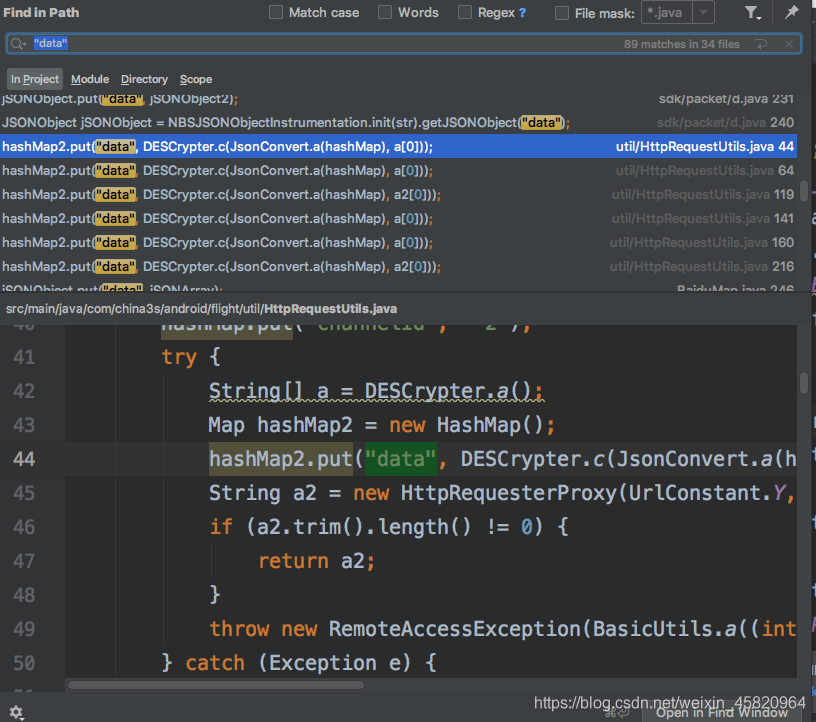 we chose HttpRequestUtils of a method and go in, see something like this
we chose HttpRequestUtils of a method and go in, see something like this
public static String a(ReselectSeatArg reselectSeatArg) throws RemoteAccessException {
...
try {
String[] a = DESCrypter.a();
Map hashMap2 = new HashMap();
hashMap2.put("data", DESCrypter.c(JsonConvert.a(hashMap), a[0]));
String a2 = new HttpRequesterProxy(UrlConstant.Y, hashMap2, 30).a();
if (a2.trim().length() != 0) {
return a2;
}
throw new RemoteAccessException(BasicUtils.a((int) R.string.ERR001));
} catch (Exception e) {
throw new RemoteAccessException(BasicUtils.a((int) R.string.ERR001));
}
}
Is a DES algorithm, enter DESCrypter.a ()
public static String[] a() throws Exception {
return a.getSecrets(new HttpRequesterProxy(UrlConstant.N, 30).a());
}
Here we have to get caught analysis as before, it is to take the keys. DescrypterUtil method of re-entering the getSecrets
public java.lang.String[] getSecrets(java.lang.String r1) {
....
}
Reduction algorithm
public static String recvData(String str) throws IOException {
...
}
public static String decode(String arg10) throws Exception {
...
byte[] decode = Base64.decodeBase64(arg10);
return new String(v0.doFinal(decode), "utf-8");
}
public static String encode(String arg9) throws Exception {
SecretKey v1 = SecretKeyFactory.getInstance("desede")
.generateSecret(new DESedeKeySpec("**************)".getBytes()));
Cipher v0 = Cipher.getInstance("***/***/****");
v0.init(1, ((Key) v1), new IvParameterSpec("***".getBytes()));
return Base64.encodeBase64String(v0.doFinal(arg9.getBytes("utf-8")));
}
Verify the correctness of the algorithm
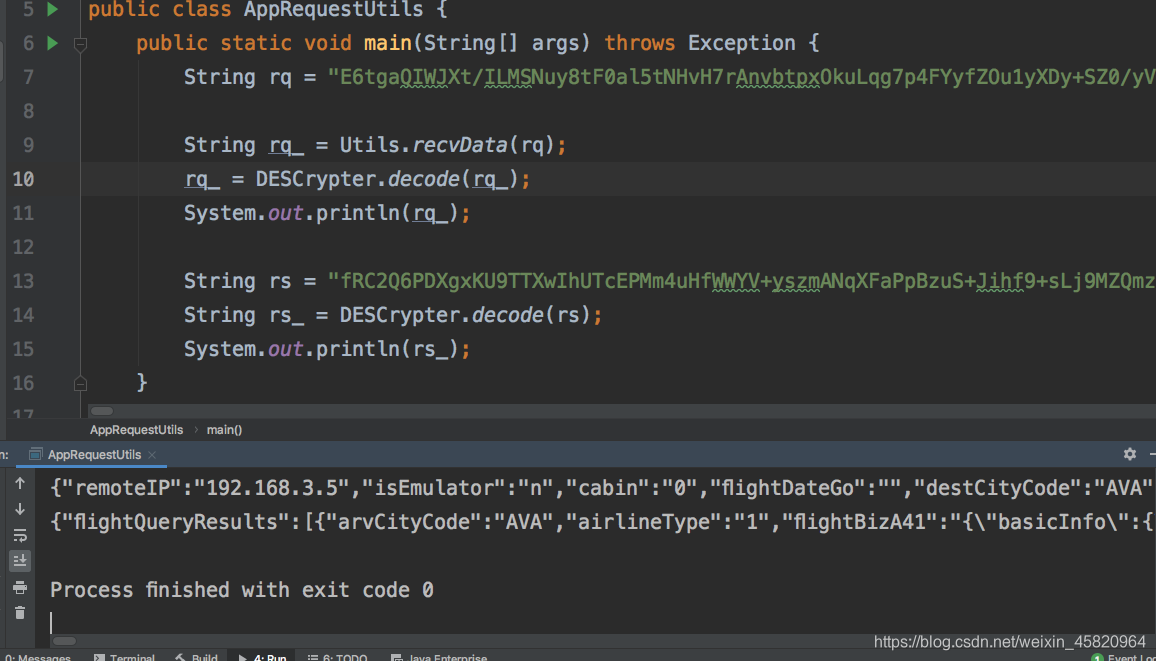 The capture data acquisition request parameters and the decrypted response packet are restored json a readable string that has been completely successful decryption Minga.
The capture data acquisition request parameters and the decrypted response packet are restored json a readable string that has been completely successful decryption Minga.
To have friends who are interested in Andrews reverse, can enter the group: 912 146 030 and share their progress.