网站被恶意请求,拉黑IP是重要的手段,如果每次拉黑都要到nginx上配置,未免太low了;我们需要更方便的控制nginx IP黑名单。
1.方案
黑名单持久化到mysql (常见的方案是redis,但不利于控制,如:不同的IP设置不同的有效期、IP的CRUD、统计等等);
通过lua-nginx-module,在nginx中开辟一块内存(lua_shared_dict),lua将黑名单定期从mysql全量刷新至lua_shared_dict;
所有请求,都要到与lua_shared_dict中的IP check一下。
2.安装
2.1 安装luajit
cd LuaJIT-2.0.5
make
make install PREFIX=/usr/local/luajit2.2.安装nginx时,将lua模块编译进去
export LUAJIT_LIB=/usr/local/luajit/lib
export LUAJIT_INC=/usr/local/luajit/include/luajit-2.1
./configure --prefix=/nginx \
--with-ld-opt="-Wl,-rpath,/usr/local/luajit/lib" \
--add-module=/opt/ngx_devel_kit-0.3.1rc1 \
--add-module=/opt/lua-nginx-module-0.10.14rc3
make -j2
make install
ln -s /nginx/sbin/nginx /usr/sbin/nginx3.配置
3.1 nginx配置
http {
server_tokens off;
lua_package_path "/usr/local/lib/lua/?.lua;;";
lua_shared_dict ip_blacklist 4m;
}
server {
set $real_ip $remote_addr;
if ( $http_x_forwarded_for ~ "^(\d+\.\d+\.\d+\.\d+)" ) {
set $real_ip $1;
}
# 管理信息,访问该URL可以查看nginx中的IP黑名单信息
location /get-ipblacklist-info {
access_by_lua_file conf/lua/get_ipblacklist_info.lua;
}
# 同步URL,通过定时任务调用该URL,实现IP黑名单从mysql到nginx的定时刷新
location /sync-ipblacklist {
access_by_lua_file conf/lua/sync_ipblacklist.lua;
}
# 生产域名配置,所有需要IP黑名单控制的location,都要包含以下语句
location / {
access_by_lua_file conf/lua/check_realip.lua;
}
}nginx服务器配置以下crrontab
* * * * * /usr/bin/curl -o /dev/null -s http://127.0.0.1/sync-ipblacklist > /dev/null 2>&13.2 lua脚本
sync_ipblacklist.lua
local mysql_host = "ip of mysql server"
local mysql_port = 3306
local database = "dbname"
local username = "user"
local password = "password"
-- update ip_blacklist from mysql once every cache_ttl seconds
local cache_ttl = 1
local mysql_connection_timeout = 1000
local client_ip = ngx.var.real_ip
local ip_blacklist = ngx.shared.ip_blacklist
local last_update_time = ip_blacklist:get("last_update_time");
if last_update_time == nil or last_update_time < ( ngx.now() - cache_ttl ) then
local mysql = require "resty.mysql";
local red = mysql:new();
red:set_timeout(mysql_connect_timeout);
local ok, err, errcode, sqlstate = red:connect{
host = mysql_host,
port = mysql_port,
database = database,
user = username,
password = password,
charset = "utf8",
max_packet_size = 1024 * 1024,
}
if not ok then
ngx.log(ngx.ERR, "mysql connection error while retrieving ip_blacklist: " .. err);
else
new_ip_blacklist, err, errcode, sqlstate = red:query("select ip_addr from ip_blacklist where status = 0 order by create_time desc limit 10000", 100)
if not new_ip_blacklist then
ngx.log(ngx.ERR, "bad result. errcode: " .. errcode .. " sqlstate: " .. sqlstate .. " err: " .. err);
return
end
ip_blacklist:flush_all();
for k1, v1 in pairs(new_ip_blacklist) do
for k2, v2 in pairs(v1) do
ip_blacklist:set(v2,true);
end
end
ip_blacklist:set("last_update_time", ngx.now());
end
end
ngx.say("sync successful");
get_ipblacklist_info.lua
-- 调用URL查看黑名单信息
-- 1万IP消耗不到1.5M ngx.shared内存
-- 获取所有KEY会堵塞别的正常请求对ngx.shared内存的访问,因此只能取少数key展示
require "resty.core.shdict"
ngx.say("total space: " .. ngx.shared.ip_blacklist:capacity() .. "<br/>");
ngx.say("free space: " .. ngx.shared.ip_blacklist:free_space() .. "<br/>");
ngx.say("last update time: " .. os.date("%Y%m%d_%H:%M:%S",ngx.shared.ip_blacklist:get("last_update_time")) .. "<br/>");
ngx.say("first 100 keys: <br/>");
ngx.say("--------------------------<br/>");
ip_blacklist = ngx.shared.ip_blacklist:get_keys(100);
for key, value in pairs(ip_blacklist) do
ngx.say(key .. ": " .. value .. "<br/>");
endcheck_realip.lua
if ngx.shared.ip_blacklist:get(ngx.var.real_ip) then
return ngx.exit(ngx.HTTP_FORBIDDEN);
end3.3 数据库设计
CREATE TABLE `ip_blacklist` (
`id` int(11) NOT NULL AUTO_INCREMENT,
`ip_addr` varchar(15) COLLATE utf8mb4_bin DEFAULT NULL,
`status` int(11) DEFAULT '0' COMMENT '0: valid 有效, 1: invalid 失效',
`effective_hour` decimal(11,2) DEFAULT '24' COMMENT '有效期,单位:小时',
`ip_source` varchar(255) COLLATE utf8mb4_bin DEFAULT NULL COMMENT '黑名单来源',
`create_time` datetime DEFAULT CURRENT_TIMESTAMP,
`modify_time` datetime DEFAULT CURRENT_TIMESTAMP ON UPDATE CURRENT_TIMESTAMP,
`remark` varchar(255) COLLATE utf8mb4_bin DEFAULT NULL COMMENT '备注',
PRIMARY KEY (`id`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8mb4 COLLATE=utf8mb4_bin;
CREATE PROCEDURE proc_ip_blacklist_status_update()
-- 将过期的IP状态改为失效
begin
update ip_blacklist
set status=1
where date_add(create_time,INTERVAL effective_hour hour) < now();
commit;
end;
CREATE EVENT job_ip_blacklist_status_update
ON SCHEDULE EVERY 1 MINUTE
ON COMPLETION PRESERVE
ENABLE
DO
call proc_ip_blacklist_status_update();
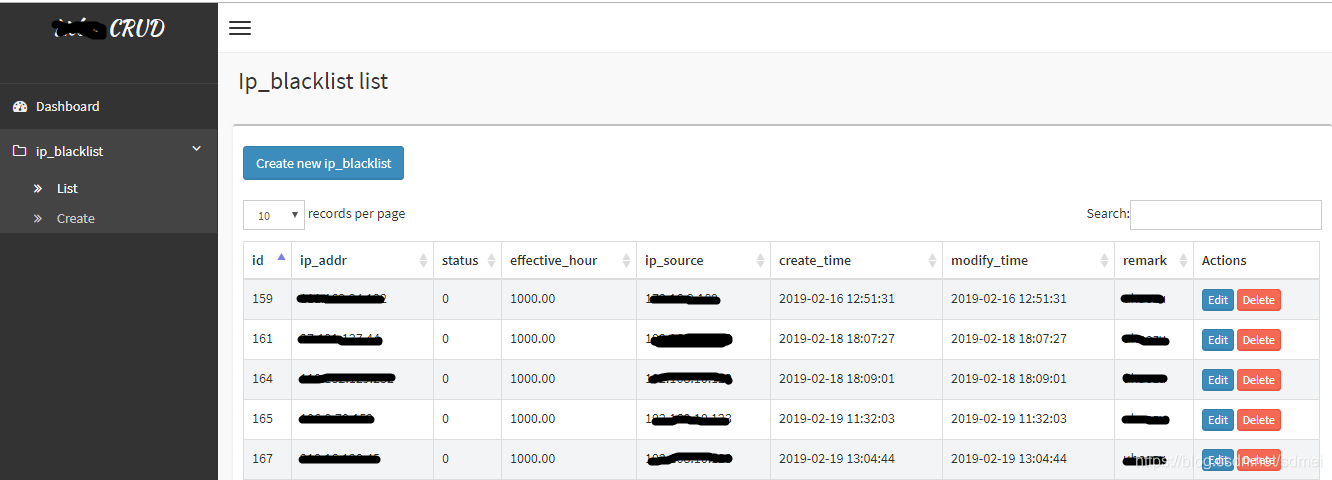
4 CRUD
黑名单产生有手工的方式,也有自动的方式,或者两者兼有。
自动的方式有通过python分析elk日志,将恶意IP自动写入mysql,这是个大话题,这里不涉及。
手工的方式可以人肉查看elk请求日志,发现恶意IP,手工填入mysql,这里推荐一个开源的CRUD工具,用户体验很nice(比直接navicat好多了),当然也可以自己写……
项目地址:https://github.com/jonseg/crud-admin-generator
项目的强大之处在于,所有表都帮你生成菜单,然后这些表的CRUD就直接用了。
具体操作见官方说明,就不赘述了。
==over==
