版权声明:本文为博主原创文章,未经博主允许不得转载。 https://blog.csdn.net/tjjingpan/article/details/85248759
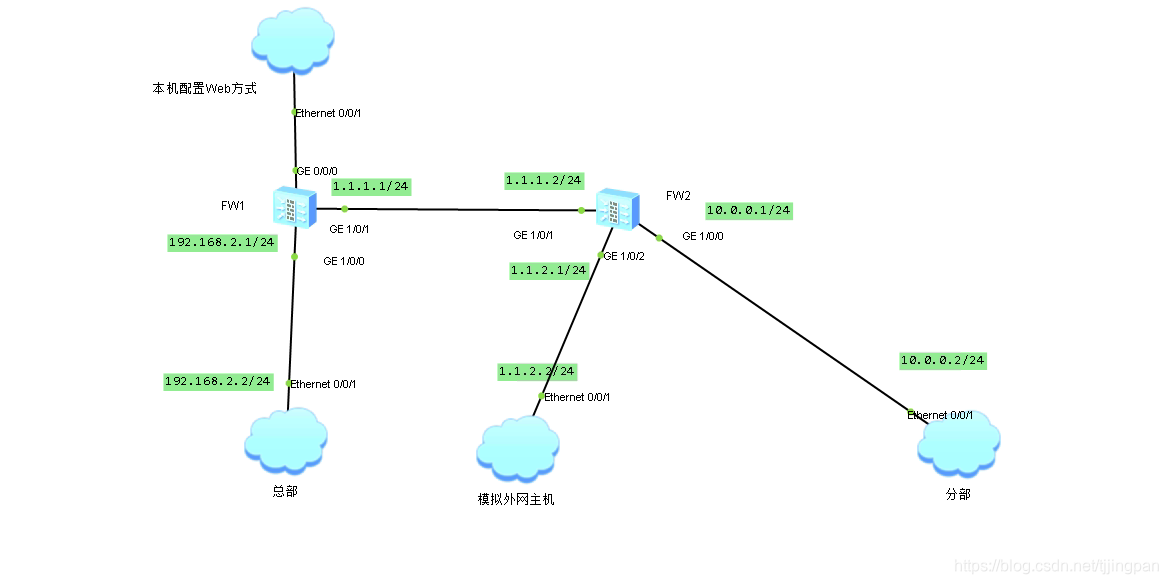
拓扑结构
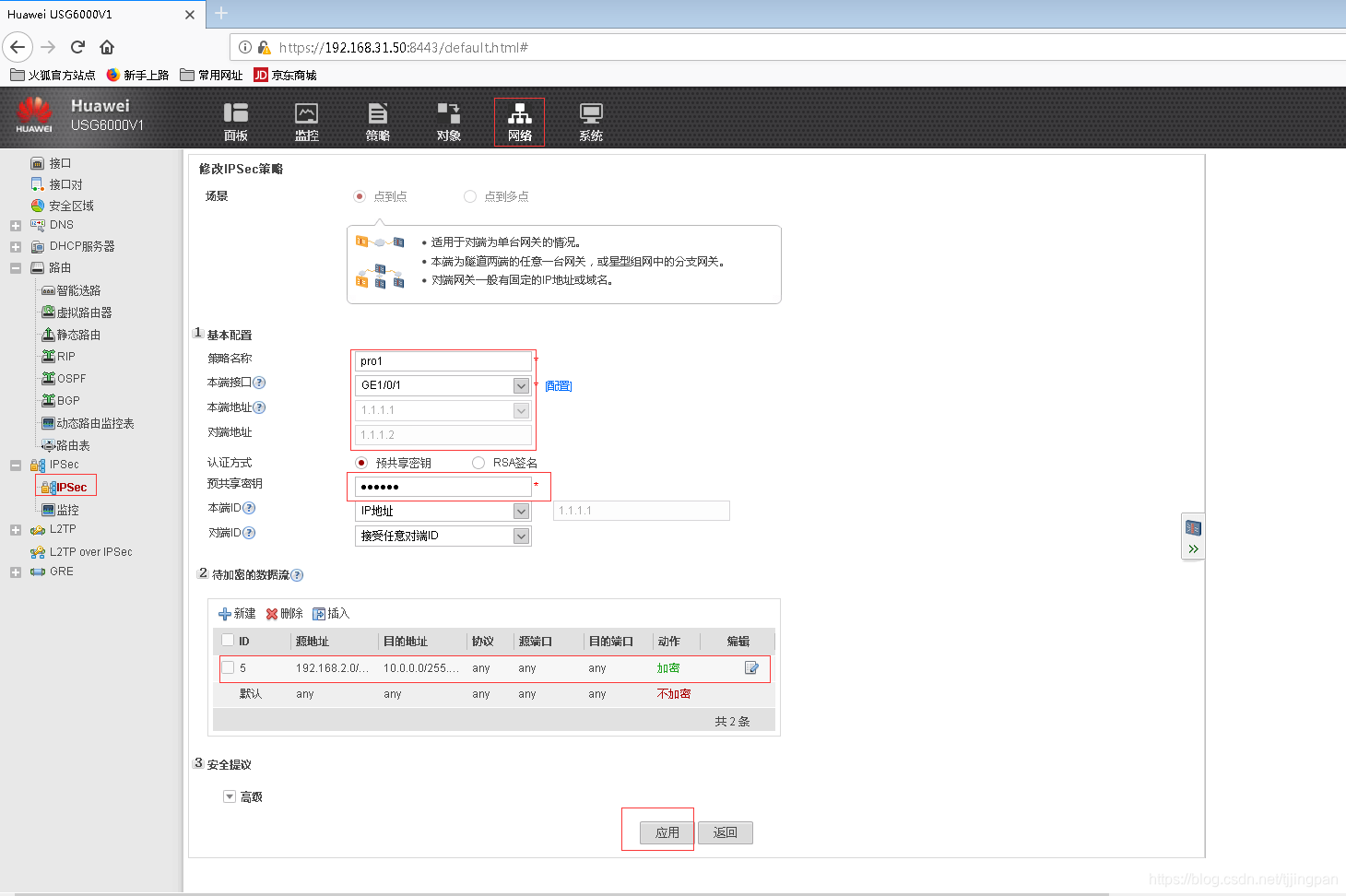
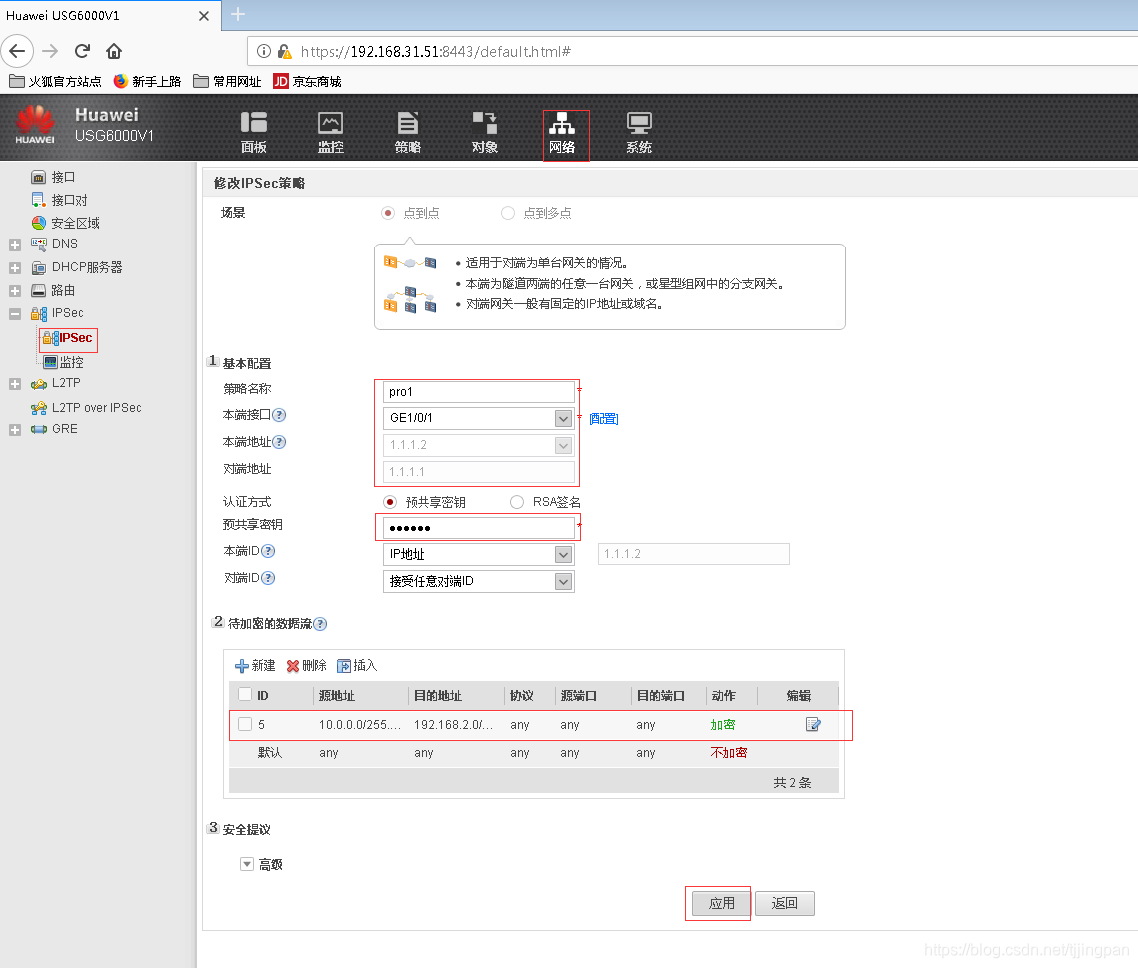
1,VPN配置
采用web方式配置。
FW1配置
FW2配置
Vpn 协商策略
security-policy
rule name untrust2local_vpn
source-zone untrust
destination-zone local
source-address 1.1.1.2 32
destination-address 1.1.1.1 32
service protocol udp destination-port 500
service protocol udp source-port 500
action permit
rule name local2untrust_vpn
source-zone local
destination-zone untrust
source-address 1.1.1.1 32
destination-address 1.1.1.2 32
service protocol udp destination-port 500
service protocol udp source-port 500
action permitNat Server
一正一反,出入自如
[FW1]nat server web protocol tcp global 1.1.1.1 9980 inside 192.168.2.2 80
[FW1]display firewall server-map
Current Total Server-map : 2
Type: Nat Server, ANY -> 1.1.1.1:9980[192.168.2.2:80], Zone:---, protocol:tcp
Vpn: public -> public
Type: Nat Server Reverse, 192.168.2.2[1.1.1.1] -> ANY, Zone:---, protocol:tcp
Vpn: public -> public, counter: 1先关闭默认安全策略,用互联网访问内网主机,查看会话表
tcp VPN: public --> public ID: c487f663b50b23061df5c21e60d
Zone: untrust --> trust TTL: 00:20:00 Left: 00:19:45
Interface: GigabitEthernet1/0/0 NextHop: 192.168.2.2 MAC: 000c-2924-9304
<--packets: 1 bytes: 48 --> packets: 254 bytes: 10,176
1.1.2.2:1047 --> 1.1.1.1:9980[192.168.2.2:80] PolicyName: default配置untrust到trust的安全策略
rule name accesswebserver
source-zone untrust
destination-zone trust
destination-address 192.168.2.2 32
service protocol tcp destination-port 80
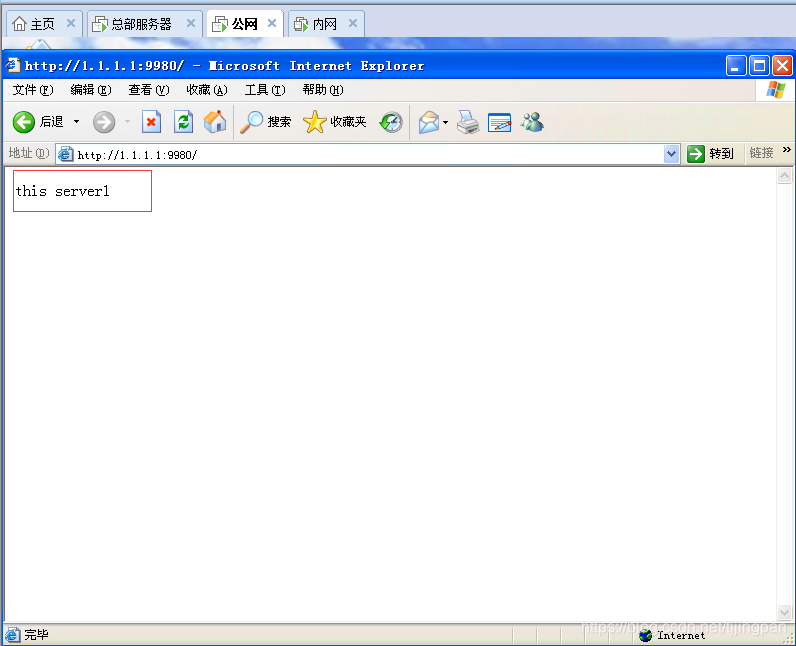
action permit外网主机可以访问内网服务器
内网主机访问internet,NAT策略
rule name internet
source-zone trust
egress-interface GigabitEthernet1/0/1
source-address 192.168.2.0 24
action nat easy-ip——————————————————————————————+++
主机还不能访问internet,还需要配置trust到untrust安全策略
先关闭默认安全策略,用内网主机访问外网web服务,查看会话表
http VPN: public --> public ID: c487f663b5125f028635c21e99d
Zone: trust --> untrust TTL: 00:20:00 Left: 00:19:50
Interface: GigabitEthernet1/0/1 NextHop: 1.1.1.2 MAC: 00e0-fc04-1b46
<--packets: 1256 bytes: 50,624 --> packets: 8 bytes: 1,112
192.168.2.2:53677[1.1.1.1:2049] --> 1.1.2.2:80 PolicyName: default配置trust到untrust安全策略,只允许访问web服务。
rule name trut2untrust
source-zone trust
destination-zone untrust
source-address 192.168.2.0 24
service http
action permit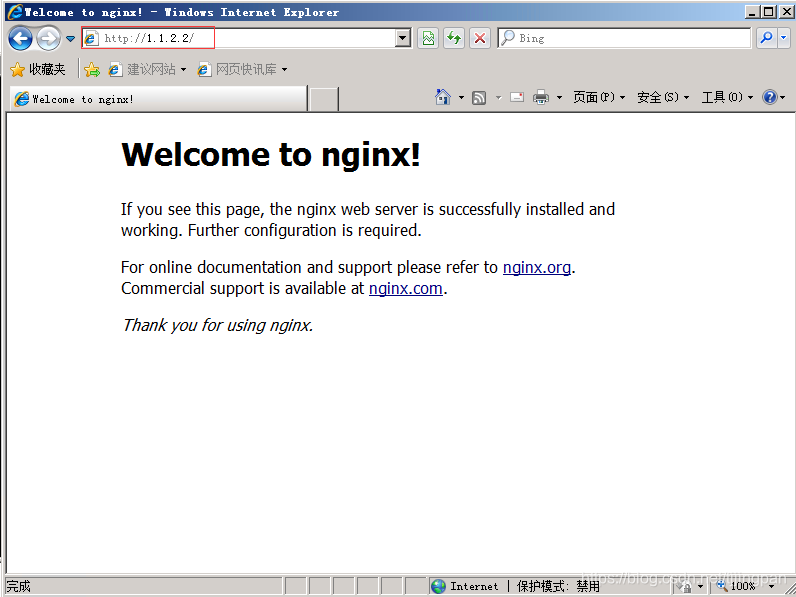
————————————————————————
服务器访问分部的web服务器
查看会话表
esp VPN: public --> public ID: c487f663b4be750539b5c21ec47
Zone: untrust --> local TTL: 00:10:00 Left: 00:09:55
Interface: InLoopBack0 NextHop: 127.0.0.1 MAC: 0000-0000-0000
<--packets: 0 bytes: 0 --> packets: 1 bytes: 124
1.1.1.2:0 --> 1.1.1.1:0 PolicyName: default添加untrust 到local安全策略,允许esp报文通过
rule name untrust2local
source-zone untrust
destination-zone local
source-address 1.1.1.2 32
destination-address 1.1.1.1 32
action permit
[FW1]nat server web protocol tcp global 1.1.1.1 9980 inside 192.168.2.2 80 no-reverse
[FW1]dis firewall session table
Current Total Sessions : 13
http VPN: public --> public 192.168.2.2:53521[1.1.1.1:53521] --> 10.0.0.2:80