部署Flannel网络
Overlay Network: 覆盖网络,在基础网络上叠加的一种虚拟网络技术模式,该网络中的主机通过虚拟链路连接起来.
VXLAN: 将源数据包封装到UDP中,并使用基础网络的IP/MAC作为外层报文头进行封装,然后在以太网传输,到达目的后由隧道端点解封装并将数据发送给目标地址。
Flannel:是Overlay网络的一种,也是将源数据包封装在另一种网络包里面进行路由转发和通信,目前已经支持UDP,VXLAN,AWS,VPC,GCE路由等级传输
下载Flannel网络包:
wget https://github.com/coreos/flannel/releases/download/v0.9.1/flannel-v0.9.1-linux-amd64.tar.gz
解压flannel包:
[root@master ~]# tar xf flannel-v0.9.1-linux-amd64.tar.gz
分别把二进制包flanneld和mk-docker-opts.sh脚本文件传到两台node节点的bin下
[root@master ~]# scp flanneld mk-docker-opts.sh root@192.168.1.102:/opt/kubernetes/bin/ [root@master ~]# scp flanneld mk-docker-opts.sh root@192.168.1.103:/opt/kubernetes/bin/
node1节点操作:
在cfg目录建立文件,添加以下信息
FLANNEL_OPTIONS="--etcd-endpoints=https://192.168.1.101:2379,https://192.168.1.102:2379,https://192.168.1.103:2379 -etcd-cafile=/opt/kubernetes/ssl/ca.pem -etcd-certfile=/opt/kubernetes/server.pem -etcd-keyfile=/opt/kubernetes/server-key.pem"
添加flanneld启动命令:
cat <<EOF >/usr/lib/systemd/system/flanneld.service [Unit] Description=Flanneld overlay address etcd agent After=network-online.target network.target Before=docker.service [Service] Type=notify EnvironmentFile=/opt/kubernetes/cfg/flanneld ExecStart=/opt/kubernetes/bin/flanneld --ip-masq \$FLANNEL_OPTIONS ExecStartPost=/opt/kubernetes/bin/mk-docker-opts.sh -k DOCKER_NETWORK_OPTIONS -d /run/flannel/subnet.env Restart=on-failure [Install] WantedBy=multi-user.target EOF
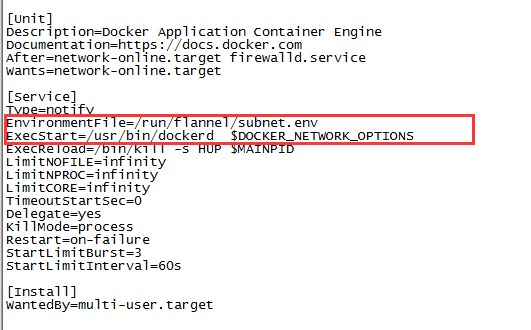
添加docker启动命令:
cat <<EOF >/usr/lib/systemd/system/docker.service [Unit] Description=Docker Application Container Engine Documentation=https://docs.docker.com After=network-online.target firewalld.service Wants=network-online.target [Service] Type=notify EnvironmentFile=/run/flannel/subnet.env ExecStart=/usr/bin/dockerd \$DOCKER_NETWORK_OPTIONS ExecReload=/bin/kill -s HUP \$MAINPID LimitNOFILE=infinity LimitNPROC=infinity LimitCORE=infinity TimeoutStartSec=0 Delegate=yes KillMode=process Restart=on-failure StartLimitBurst=3 StartLimitInterval=60s [Install] WantedBy=multi-user.target EOF
在master端添加flannel网络信息分配给节点,
分配的网段为172.17.0.0网段,封装类型为vxlan,更高效,更稳定
/opt/kubernetes/bin/etcdctl \ --ca-file=/opt/kubernetes/ssl/ca.pem --cert-file=/opt/kubernetes/ssl/server.pem --key-file=/opt/kubernetes/ssl/server-key.pem \ --endpoints="https://192.168.1.101:2379,https://192.168.1.102:2379,https://192.168.1.103:2379" \ set /coreos.com/network/config '{ "Network": "172.17.0.0/16", "Backend": {"Type": "vxlan"}}'
在master端获取是否分配成功:
[root@master ~]# etcdctl --ca-file=/opt/kubernetes/ssl/ca.pem --cert-file=/opt/kubernetes/ssl/server.pem --key-file=/opt/kubernetes/ssl/server-key.pem --endpoints="https://192.168.1.101:2379,https://192.168.1.102:2379,https://192.168.1.103:2379" get /coreos.com/network/config 2018-08-07 17:20:20.214528 I | warning: ignoring ServerName for user-provided CA for backwards compatibility is deprecated { "Network": "172.17.0.0/16", "Backend": {"Type": "vxlan"}}
node1节点启动flanned
[root@node1 cfg]# systemctl restart flanneld
查看ip信息
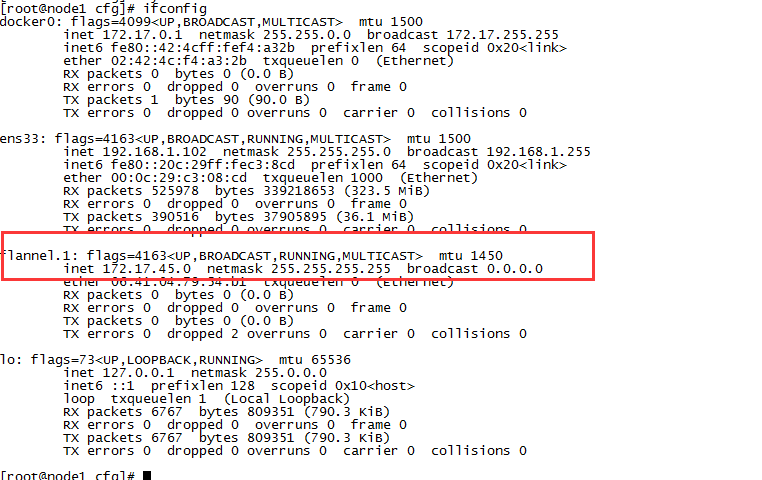
查看flannel生成的文件,分配了一个子网,
[root@node1 cfg]# cat /run/flannel/subnet.env DOCKER_OPT_BIP="--bip=172.17.45.1/24" DOCKER_OPT_IPMASQ="--ip-masq=false" DOCKER_OPT_MTU="--mtu=1450" DOCKER_NETWORK_OPTIONS=" --bip=172.17.45.1/24 --ip-masq=false --mtu=1450"
查看docker启动文件变化,引用了flannel网络文件变量
重启docker
systemctl daemon-reload
systemctl restart docker
再次查看网络变化,两个网段一样
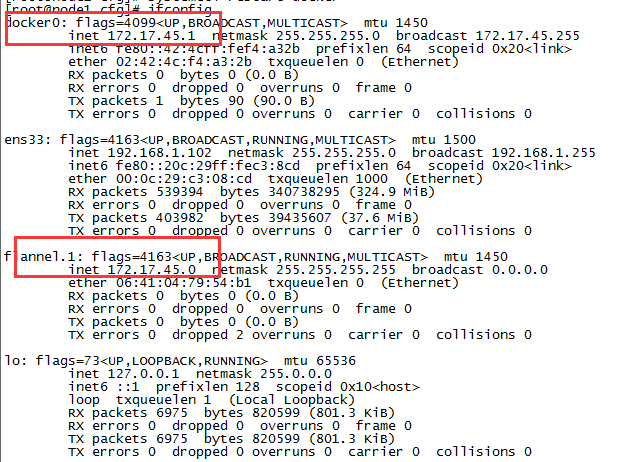
node2节点布署同上node1部署步骤
分别在两个节点上查看 路由信息

[root@node1 cfg]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.1.1 0.0.0.0 UG 100 0 0 ens33 172.17.45.0 0.0.0.0 255.255.255.0 U 0 0 0 docker0 172.17.47.0 172.17.47.0 255.255.255.0 UG 0 0 0 flannel.1 192.168.1.0 0.0.0.0 255.255.255.0 U 100 0 0 ens33

root@node2 cfg]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.1.1 0.0.0.0 UG 100 0 0 ens33 172.17.45.0 172.17.45.0 255.255.255.0 UG 0 0 0 flannel.1 172.17.47.0 0.0.0.0 255.255.255.0 U 0 0 0 docker0 192.168.1.0 0.0.0.0 255.255.255.0 U 100 0 0 ens33
